Weekly Threat Briefing: 70% of Presidential Campaigns Fail to Provide Adequate Online Privacy and Security Protections
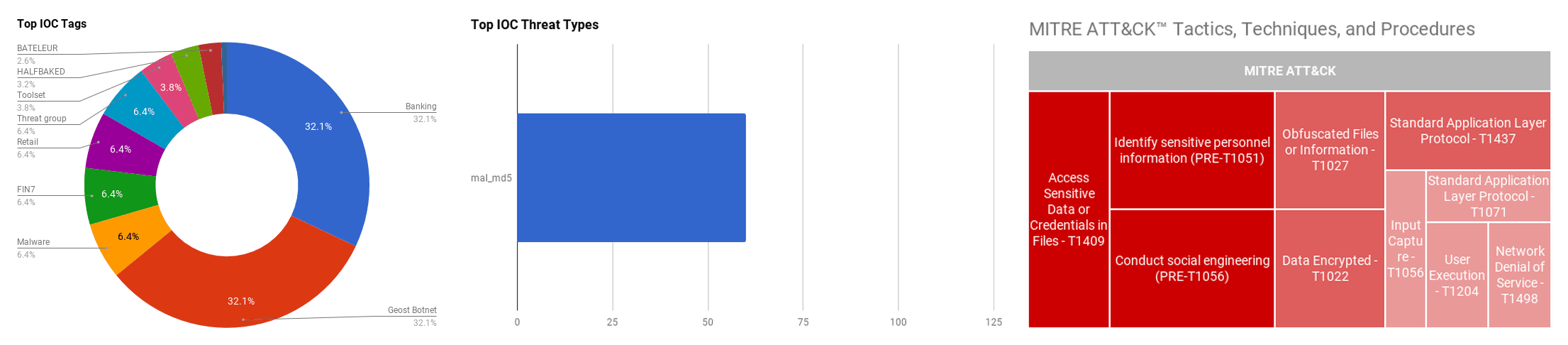

The intelligence in this week’s iteration discuss the following threats: BEC, Botnet, Data breach, Data leak, FIN7, Phishing, Ransomware, Vulnerability, and Zero-day. The IOCs related to these stories are attached to the Community Threat Briefing and can be used to check your logs for potential malicious activity.
Trending Threats
70% of Presidential Campaigns Fail to Provide Adequate Online Privacy and Security Protections (October 14, 2019)
The Online Trust Alliance (OTA) has recently announced in its reviewal of all 2020 U.S presidential campaigns that 70% of the candidate websites failed to meet OTA’s privacy and security standards. This leaves visitors are potentially at risk. Candidates are assessed on three main areas regarding privacy. This includes data retention, data sharing, and language in campaign website privacy statements. 70% is a concerningly high percentage for a failure rate in a presidential analysis due to the increased pressure for privacy even before the implementation of the General Data Protection Regulation (GDPR). The large amount of publicity that is directed at these candidates gives more reason for them to handle the privacy of information of visitors more seriously or be at risk of potential data leak or other forms of malicious activity.
Click here for Anomali recommendation
#SecTorCa: Millions of Phones Leaking Information Via Tor (October 11, 2019)
It was recently announced at the SecTor security conference in Toronto, Canada that millions of Android users are potentially having their personal data leaked via the Tor network. Researchers found that by setting up exit nodes forcing browsers to use unencrypted versions, it allowed them to view user data including GPS coordinates, web addresses, keystrokes and other Personally Identifiable Information (PII). This indicates that actors are potentially tracking and profiling users as a result of leaked personal data via Tor networks even for those that never installed Tor themselves which raises a dangerous scenario for many. This doesn’t just apply to those that installed Tor but also includes those who have not installed Tor, which raises a dangerous scenario for many as to how many android users as unknowingly transmitting data over Tor.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Identify sensitive personnel information (PRE-T1051) | [MITRE MOBILE-ATT&CK] Access Sensitive Data or Credentials in Files - T1409 | [MITRE MOBILE-ATT&CK] Standard Application Layer Protocol - T1437
Apple iTunes and iCloud for Windows 0-Day Exploited in Ransomware Attacks (October 10, 2019)
Threat actors are exploiting a zero-day vulnerability component within Apple’s iTunes and iCloud software in order to evade detection. The vulnerability itself relates to the Bonjour updater which performs low-level network tasks including such as automatically downloading updates for Apple software once they become available. The updater was exploited due it the fact that it used the “unquoted service path vulnerability” which allows actors to implant malicious files within the parent path. This allows the file to maintain persistence and evade detection from genuine applications. The actors were using this unquoted path vulnerability to run the BitPaymer ransomware as it was named “Program”. The Bonjour vulnerability didn’t enable to gain system rights on the infected machine but allows it to evade detection since Bonjour masquerades itself as a genuine process.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Masquerading - T1036
Moroccan Human Rights Defenders Targeted Using Malicious NSO Israeli Spyware (October 10, 2019)
Two Moroccan human rights defenders have been the targets of surveillance, with the technology coming from the NSO Group, an Israeli-based technology firm known for selling spyware to government intelligence and law enforcement agencies. This may indicate that the Moroccan government, or security agencies within Morocco, are behind the surveillance of Maati Monjib and Abdessadak El Bouchattaoui. Maati is an academic and human rights activist and Abdessadak is a human rights lawyer that has been the representative for the social justice movement Hirak El-Rif. Both have been targeted via the use of malicious links from SMS messages that would advertently install Pegasus software to gain control over their phones. Pegasus works by scanning the affected device and installs the necessary modules to capture screenshots, exfiltrate browser history and contacts, listen to calls, log pressed keys, read user’s messages and their mail. It will terminate itself if it cannot communicate with its Command-and-Control (C2) within 60 days if instigation on the infected device.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Conduct social engineering (PRE-T1056) | [MITRE MOBILE-ATT&CK] Access Sensitive Data or Credentials in Files - T1409
Mahalo FIN7: Responding to the Criminal Operators’ New Tools and Techniques (October 10, 2019)
FireEye Mandiant analysts have discovered new tools being used within the financially motivated threat actor group FIN7 that allows them to further their evasive tactics. The tools to be of focus are called BOOSTWRITE and RDFSNIFFER. BOOSTWRITE works by decrypting embedded payloads and it uses various methods to get around antivirus detection including a sample which has a genuine Certificate Authority. RDFSNIFFER is actually a payload of a BOOSTWRITE sample which is used to observe and damage connections made by the National Cash Register (NCR) Corporations “Aloha Command Center Client” (RDFClient) which is used to manage payment card processing systems.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Data Encrypted - T1022 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] DLL Search Order Hijacking - T1038 | [MITRE ATT&CK] Code Signing - T1116 | [MITRE ATT&CK] File Deletion - T1107
NSA Is Latest Intelligence Agency to Sound VPN Patch Alarm (October 9, 2019)
The National Security Agency (NSA) recently made an announcement that nation-state threat actors are taking advantage of and exploiting vulnerabilities in three main types VPN servers build Fortinet, Palo Alto Networks and Pulse. This report comes soon after similar reports were made by the UK’s Government Communications Headquarters (GCHQ) and Canada’s Center for Cyber Security (CCCS). Actors are exploiting vulnerabilities “CVE-2019-11510”, “CVE-2019-11539”, “CVE-2018-13379”, among others, to access vulnerable VPN devices produced by the three companies. Frequently, cyberattack investigations occur only when there have been multiple people affected, hence the NSA is pushing individuals and companies to rectify vulnerabilities before they become a problem in the future.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Standard Application Layer Protocol - T1071 | [MITRE ATT&CK] System Information Discovery - T1082
October Patch Tuesday: Microsoft Fixes Critical Remote Desktop Bug (October 9, 2019)
In this month’s Patch Tuesday Microsoft fixed 59 vulnerabilities, one in particular, “CVE-2019-1033”, a vulnerability in their Remote Desktop Client (RDC) that would enable actors to use malicious servers gain control of a Windows computer that was connected to it. Actors could have exploited this via the use of a man-in-the-middle (MITM) attack, compromising genuine servers, DNS poisoning or social engineering. The patch also fixed vulnerabilities relating to Remote Code Execution (RCE) vulnerabilities in Microsoft’s XML parser and RCE bugs in VBScript which enable actors to take control of the individual’s system and corrupts memory.Click here for Anomali recommendation
BEC Explodes As Attackers Exploit Email's Identity Crisis (October 9, 2019)
There are over 800,000 domains which have Domain-based Message Authentication, Reporting and Conformance (DMARC) records as of 2019, however less than 17% of DMARC records are enforced. This indicates that phishing emails are still being received by people in their inboxes, as DMARC protects against direct domain spoofing. Business Email Compromise (BEC) attacks have resulted in more than $26 billion in losses in just the past three years. This raises the question as to why the enforcement rates are so low with such high costs for companies, and why companies are not doing everything in their power to ensure that it can be avoided is curious.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Conduct social engineering (PRE-T1056) | [MITRE ATT&CK] Spearphishing Attachment - T1193 | [MITRE ATT&CK] Spearphishing Link - T1192 | [MITRE ATT&CK] Spearphishing via Service - T1194
Hackers Breach Volusion and Start Collecting Card details from Thousands of Sites (October 8, 2019)
Actors have recently infected the infrastructure of Volusion, a cloud ecommerce service. The infection has enabled actors to modify a JavaScript file and inject malicious code that records payment card details from online forms. Volusion has potentially more than 20,000 customers, one in particular being the Sesame Street Live store. The attack acts as a Magecart attack where actors focus more on stealing payment card details from online sources rather than from physical sources such as ATMs.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Input Capture - T1056
Geost Botnet. The Story of the Discovery of a New Android Banking Trojan from an Opsec Error (October 8, 2019)
The botnet called, Geost, was discovered by members from the Czech Technical University, Argentina’s UNCUYO University, and security firm Avast that has infected an estimated 800,000 individuals in Russia. The botnet worked by taking genuine apps from the Google Play store and implanting malicious code before the apps were made available to download from third-party sites. The botnet also has likely access to large quantities of Euros in multiple bank accounts because . The infection was discovered as a result of the weakness in its operational security. The threat group forgot to encrypt their data which allowed for their activities to be identified as well as trusting the illegal networks that were already being monitored. In addition, the botmasters did not encrypt their communication channels, with most chat conducted on Skype. With all of this going on, taking into regard the mistakes made by the threat group, it is unclear how the threat actors were able to infect approximately 800,000 machines, as of this writing.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE MOBILE-ATT&CK] Access Sensitive Data or Credentials in Files - T1409 | [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Data Obfuscation - T1001 | [MITRE MOBILE-ATT&CK] Standard Application Layer Protocol - T1437
Tu Ora Data Breach Exposed Medical and Personal Data of up to 1 Million People (October 8, 2019)
In August 2019, Tu Ora Compass Health, a Primary Health Organisation (PHO), confirmed it was compromised by an actor who was able to gain illicit access to their website by exploiting a vulnerability in their system. The exploit itself was first noted in early July 2019 which raises the question why it was not mitigated when the patch was first released. The breach allowed the actor to potentially obtain patient data including addresses, DOB, ethnicity, medical center enrolled, names, and National Health Index Number. As well as personal information, health and medical information may have been obtained during the breach of the website. Those at risk are those enrolled with a medical center in the Greater Wellington, Manawatu and Wairarapa regions of New Zealand since 2002. The database included the data of nearly one million people including deceased patients.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Identify sensitive personnel information (PRE-T1051)
A Year After Patch, Drupalgeddon2 Is Still Being Employed In Cybercriminal Attacks (October 7, 2019)
Drupalgeddon2, a zero-day exploit that is a Remote Code Execution (RCE) vulnerability has been patched for over a year and half is still being against websites in attacks, according to researchers from Akamai. The vulnerability, registered as “CVE-2018-7600” targets Drupal systems that are used to manage websites, and actors are exploiting Drupal systems using malicious .GIF files. When the patch was released owners were encouraged to patch their systems and many did, however many still have not done so and are at risk of data theft and website hijacking.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Identify vulnerabilities in third-party software libraries - T1389 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Network Denial of Service - T1498 | [MITRE ATT&CK] Data Encoding - T1132
RobbinHood Ransomware Using Street Cred to Make Victims Pay (October 7, 2019)
The threat actors behind the RobbinHood ransomware have made adjustments in the content of their ransom note. The note, identified by security researcher Joakim Kennedy, attempts to enforce the mentality upon the individuals that there is no hope of decrypting the files without paying for the recovery. The operators refer to earlier attacks on systems in Baltimore, Maryland (MD), and Greenville, North Carolina (NC), along with the lack of decryption tool available for the ransomware. In other variants of RobbinHood discovered, the threat actors let itself be known to the individual to emphasize a loss of control for them and that the ransom must be paid.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Conduct social engineering (PRE-T1056) | [MITRE ATT&CK] Data Encrypted - T1022
Credit Info Exposed in TransUnion Credential Stuffing Attack (October 7, 2019)
An unknown threat actor was able to gain access to TransUnion Canada web portal via a customer’s stolen credentials and used it to pull consumer credit files from approximately between June 28th and July 11th, 2019. The actor was able to collect addresses, DOBs, names, and Social Insurance Number’s (SINs) from the TransUnion portal by using the login details stolen from a customer’s account. As well as gaining personal information about consumers from reports, the actor may also have collected information related to the consumer’s credit, such as amounts, loan obligations and payment history. The reports, however does not contain account numbers of consumers.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Identify sensitive personnel information (PRE-T1051)
Observed Threats
This section includes the top threats observed from the Anomali Community user base as well as sensors deployed by Anomali Labs. A ThreatStream account is required to view this section. https://www.anomali.com/products
The financially-motivated threat group “FIN7” has been active since at least mid-2015 and has targeted various industries around the world with the objective of stealing financial data, primarily credit and debit card data. The group is Russian-speaking and operates on a global level. FIN7 is one of the most notorious financial groups that has been attributed to the theft of over 15 million payment card records and causing organizations around the world approximately one billion dollars (USD) in losses. In the United States (US) alone, the group has targeted over 100 companies and compromised the network of organizations in 47 states and the District of Columbia. The group primarily targets Point-of-Sale (POS) terminals that have a high usage to steal payment card data and utilizes a mix of custom and open-source malware and tools to attack its targets. FIN7 also created a fake computer security company called “Combi Security” to serve as a front of legitimacy and to recruit members to participate in their malicious activities. Combi Security is purported to be based in Russia and Israel. The group engages in social engineering techniques ranging from custom phishing emails and documents, to phone calls with store managers. The group will sell the financial data on various underground carding forums, or utilize the information themselves for fraudulent activities.
FEATURED RESOURCES




