Weekly Threat Briefing: Google Researchers Discover Malicious Websites Hacking iPhones for Years
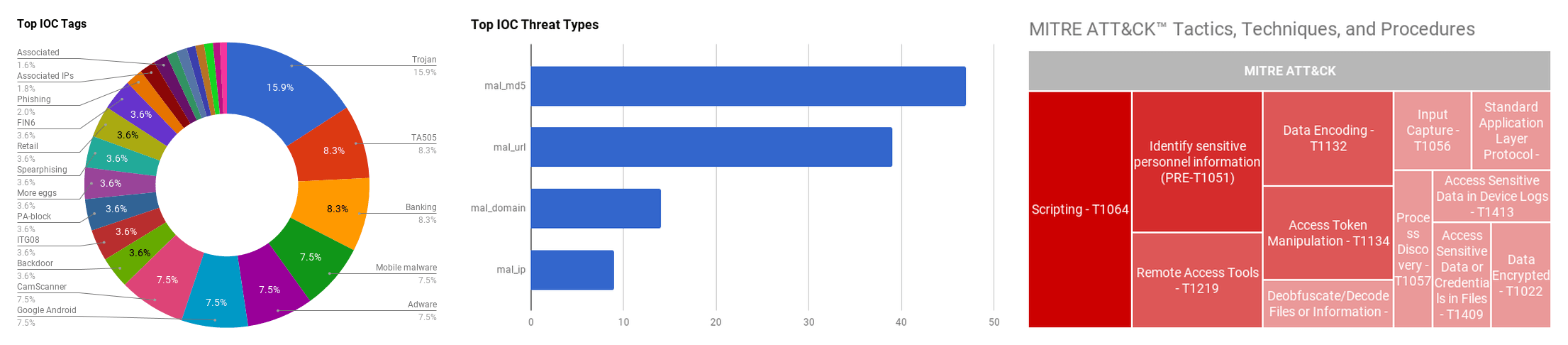

The intelligence in this week’s iteration discuss the following threats: CamScanner, Data Breaches, FIN6, iPhone Hacking, Quasar RAT, Retadup Botnet, REvil Ransomware, TA505, and TrickBot. The IOCs related to these stories are attached to the Community Threat Briefing and can be used to check your logs for potential malicious activity.
Trending Threats
U.S. Jury Indicts Suspected Capital One Hacker on Wire Fraud, Data Theft Charges (August 29, 2019)
Following the conclusion of a federal grand jury investigation, formal charges have been filed against Paige Thompson, the suspected threat actor who obtained personal information of over 100 million people in a Capital One data breach between March and July 2019. Thompson, a former Amazon Web Services (AWS) software engineer, is charged with wire fraud and computer data theft. In late March 2019, Thompson created a program that scanned cloud customers for a specific web application firewall misconfiguration, ultimately exploiting the misconfiguration to extract account credentials for more than 30 victim databases, one of which was Capital One. The Department of Justice has not identified the other companies or agencies breached by Thompson. According to Capital One, approximately 140,000 Social Security numbers and 80,000 associated bank account numbers were compromised in the data breach.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Identify sensitive personnel information (PRE-T1051)
Google Researchers Discover Malicious Websites Hacking iPhones for Years (August 29, 2019)
Researchers at Google’s Treat Analyst Group (TAG) and Project Zero have discovered a series of hacked websites that have been delivering attacks to iPhones for a period of at least two years. “Simply visiting the hacked site was enough for the exploit server to attack your device, and if it was successful, install a monitoring implant,” said Ian Beer, a security researcher at Project Zero. TAG was able to collect five distinct iPhone exploit chains based on 14 vulnerabilities. These exploit chains covered versions from iOS 10 up to the latest iteration of iOS 12. The attack chains allowed a threat actor to gain root access to the device, and gain access to the victim’s keychain, as well as steal files and upload live location data. The implant does not have persistence on a device, but the potentially stolen authentication tokens from user keychains could allow the actor to gain access to various accounts.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE MOBILE-ATT&CK] Access Sensitive Data or Credentials in Files - T1409 | [MITRE MOBILE-ATT&CK] Access Sensitive Data in Device Logs - T1413 | [MITRE ATT&CK] Access Token Manipulation - T1134 | [MITRE ATT&CK] Spearphishing Link - T1192
REvil Ransomware Impacts Hundred of Dental Practices Across US. (August 29, 2019)
An unidentified threat group breached the infrastructure of the medical records software “DDS Safe” to deploy ransomware in hundreds of dental offices across the United States. The breach was discovered on August 26, 2019, when dental staff at impacted offices could not access patient information. The software providers, The Digital Dental Record and PerCSoft, appear to have opted to pay the ransom, and have begun to distribute a decypher to dental offices. The variety of ransomware, known as “REvil,” is considered one of the most active and widespread ransomware strains of 2019, according to a Fidelis Security report.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Data Encrypted - T1022
Threat Actor FIN6 Targeting E-Commerce Using More_eggs Backdoor (August 29, 2019)
Researchers at IBM have identified a series of attacks targeting e-commerce websites as being perpetrated by the threat group dubbed ”ITG08,” or more commonly known as FIN6. The group has been observed injecting malicious code into online checkout pages of compromised websites, thereby stealing payment card data of customers attempting to make a purchase. This new FIN6 activity demonstrates many of the same established tactics, techniques and procedures (TTPs) of the group, but in this new e-commerce environment. FIN6 is targeting multinational organizations via spearphising emails, advertising fake job advertisements to targeted employees. The emails contain a link that leads the targeted individual to download a ZIP file containing a malicious Windows Script File (WSF) that initiates the infection routine of the “More_eggs” JScript backdoor malware. Threat actors can then use the More_eggs backdoor to gain a foothold and infect additional devices.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] PowerShell - T1086 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Scripting - T1064
Retadup Botnet Defeated by Design Flaw (August 28, 2019)
Over 850,000 unique infections of the Retadup cryptojacking botnet have been neutralized after a Command and Control (C2) server was taken down in Paris, France. Bringing down the Redatup infrastructure was possible due to a design flaw that researchers found in the botnet's communication protocol. The Cybercrime Fighting Center (C3N) of the French National Gendarmerie replaced the malicious C2 server with a version that made connected instances of Retadup self-destruct. The botnet was used primarily for Monero cryptojacking, and according to officials at C3N, Retadup operators have earned an estimated “several million” euros every year starting in 2016.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Screen Capture - T1113 | [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Process Discovery - T1057
CamScanner Advertising Dropper in Google Play (August 27, 2019)
Security researchers at Kaspersky have discovered malicious code in an Android application that has over 100 million downloads on Google Play. The app, a mobile PDF creator application called CamScanner, contains within the advertising library a malicious dropper component. Detected as Trojan-Dropper.AndroidOS.Necro.n, the module functions to download and launch a payload of malicious servers. According to researchers at Kaspersky, owners of the module can manipulate an infected device to show intrusive advertisements and to steal money by charging mobile accounts for paid subscriptions. These findings were reported to Google, and the app was removed from the Google Play marketplace.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Deobfuscate/Decode Files or Information - T1140 | [MITRE ATT&CK] User Execution - T1204
Imperva Firewall Breach Exposes Customer API Keys, SSL Certificates (August 27, 2019)
Cybersecurity firm Imperva has announced a security breach, impacting customers of Imperva’s Cloud Web Application Firewall (WAF) product previously known as ‘Incapsula’. The company learned of the incident from a third party, and has verified that the affected customer database contained old Incapsula records that go up to September 15, 2017 only. The exposed information from the database includes email addresses, hashed, and salted passwords, as well as some customer API keys and SSL certificates. Imperva has informed customers affected by the incident regarding the breach, and has implemented password resets and 90-day password expiration for the product in the wake of the incident.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE PRE-ATT&CK] Identify sensitive personnel information (PRE-T1051) | [MITRE ATT&CK] Third-party Software - T1072
TrickBot Modifications to Target U.S. Mobile Users (August 27, 2019)
In August 2019, researchers observed “TrickBot” malware using dynamic web injection attacks on legitimate websites for U.S.-based mobile carriers Sprint, T-Mobile, and Verizon Wireless. The malware leverages a new module that manipulates web sessions for already-infected systems. When a victim navigates to one of the sites on the infected system, the modified website requests the account PIN, which is normally not required by the legitimate site’s login procedure. TrickBot’s record functionality allows the PIN, as well as the victim’s username and password, to be transmitted to the TrickBot Command and Control (C2) server. Threat actors utilizing TrickBot can use the PIN and associated account information to take over the victim account via SIM swapping attacks, allowing the actor to assume control of the telephone number, including text and voice communications.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Scripting - T1064
TA505 Active: Updates to ServHelper and FlawedAmmyy Malware (August 27, 2019)
According to researchers at TrendMicro, threat actor “TA505” is actively targeting banks in Turkey, Serbia, Romania, Korea, Canada, the Czech Republic, and Hungary, utilizing phishing techniques to compromise systems. The group is targeting the banks with emails that have ISO file attachments as an initial infection vector. As in previous operations, TA505 is using either “FlawedAmmy” remote access trojan (RAT) or ServHelper as payloads, and continues to make a combination of small adjustments to their deployment techniques. According to researchers at TrendMicro, the adjustments and updates made to the FlawedAmmyy RAT and ServHelper may indicate that the group is evaluating which forms of obfuscation can bypass detections and yield more financial returns.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Remote Access Tools - T1219 | [MITRE ATT&CK] Scripting - T1064 | [MITRE ATT&CK] Standard Application Layer Protocol - T1071 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] DLL Side-Loading - T1073
Advanced Phishing Campaign Delivers Quasar RAT (August 26, 2019)
A new phishing campaign has been identified by researchers at Cofense Intelligence that delivers the “Quasar” Remote Access Tool (RAT) while employing multiple measures to deter detection. The phishing email, written to appear as though sent from a job seeker, includes an attached “resume” document file that delivers the malware. The document is password protected to bypass automated phishing software, loaded with more than 1200 lines of garbage code strings to overload and crash analysis systems, and the payload URL is hidden as metadata for embedded images. Finally, to avoid discovery, a Microsoft Self Extracting executable is downloaded that unpacks the RAT that is 401MB, an artificially-large file size that can crash an automated-detection system. These sophisticated techniques are used to delay detection and can provide the threat actor with enough time to gather information and additional malware before being detected or removed.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Remote Access Tools - T1219 | [MITRE ATT&CK] Spearphishing Attachment - T1193 | [MITRE ATT&CK] Scripting - T1064
Hostinger Data Breach Impacts 14 Million Customers (August 26, 2019)
Hostinger, a popular web hosting provider, has announced that an unauthorized third party has breached one of their servers, impacting about 14 million Hostinger users. According to Hostinger, “This server contained an authorization token, which was used to obtain further access and escalate privileges to our system RESTful API server.” The unauthorized third party had access to emails, first names, hashed passwords, IP addresses, and usernames. Hostinger client financial data was not impacted in the breach. Following the incident, all Hostinger user passwords have been reset using SHA-256 hashing algorithm to increase security for customers.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Access Token Manipulation - T1134 | [MITRE PRE-ATT&CK] Identify sensitive personnel information (PRE-T1051)
Observed Threats
This section includes the top threats observed from the Anomali Community user base as well as sensors deployed by Anomali Labs. A ThreatStream account is required to view this section. Click here to request a trial.
TA505 The financially-motivated threat group called, “TA505,” was first reported on by Proofpoint researchers in December 2017. Malicious activity attributed to the Russian-speaking group dates back to at least 2014, and the campaigns conducted by TA505 have targeted entities and individuals around the world. The group distributes a variety of malware, both well-known strains (Dridex banking trojan, Locky ransomware), custom-created (Jaff ransomware, tRAT), and variants of legitimate remote access tools (Remote Manipulator System). The group primarily distributes malware and tools via large scale and indiscriminately-distributed malspam campaigns, often through the “Necurs” botnet, with malicious attachments or links. Incorporation of new malware, creating custom malware and the use of advanced tactics, such as the removal of malware artifacts, indicate that this group is a sophisticated threat and likely well-funded. The group is innovative and shows the flexibility to pivot to other techniques and malware trends on a global scale.
FIN6 FIN6 is a financially motivated threat actor shown active as early as 2014. Public information on this group is limited, but reports from FireEye contend that FIN6 is focused on theft of credit card data that is then offered for sale on underground marketplaces. Researchers report that the group has successfully stolen payment data from more than 10 million credit cards. Public visibility of FIN6 intrusions is limited, thus the group’s initial attack vectors are largely unknown. FireEye researchers believe that the group purchases previously stolen account credentials and access to compromised victim systems on underground forums. Otherwise, like many other threat actors, the group may employ typical phishing schemes to harvest credentials and deploy malware.
FEATURED RESOURCES

Iran's Cyber Offensive Enters a Dangerous New Phase: What CISOs Must Know on Day 98



