
The intelligence in this week’s iteration discuss the following threats: Botnet, Cryptocurrency miner, Cyber espionage, Ransomware, Targeted attacks, and Vulnerabilities. The IOCs related to these stories are attached to the WTB and can be used to check your logs for potential malicious activity.
Trending Threats
Android Devices Targeted by New Monero-Mining Botnet (February 5, 2018)
Android devices such as smartphones, smart televisions, and television are being targeted by a new Monero cryptocurrency mining botnet that first appeared on February 3, 2018, according to Qihoo 360 researchers. The botnet, dubbed “ADB.miner,” is targeting port 5555, Android’s Debug Bridge (ADB), and appears to have infected approximately 7,400 devices at the time of this writing. Researchers have not stated specifically how the botnet is utilizing an ADB vulnerability to infect Android devices. Android devices come with port 5555 disabled by default, so the devices that have been infected and are being targeted are those in which individuals have manually enabled port 5555.
Click here for Anomali recommendation
Attackers Exploiting Unpatched Flaw in Flash (February 2, 2018)
Adobe has issued a security advisory regarding a vulnerability, registered as “CVE-2018-4878,” that affects Adobe Flash Player version 28.0.0.137 and all earlier versions. Threat actors have been observed exploiting this vulnerability in the wild via Microsoft Office documents with embedded malicious Flash content. Additional information on this vulnerability has not yet been made available because a patch has not yet been issued.
Click here for Anomali recommendation
DDG, The Second Largest Mining Botnet Targets Redis and OrientDB Servers (February 2, 2018)
Qihoo 360 Netlabs researchers have published information regarding a new cryptocurrency-mining campaign driven by the “DDG” botnet. DDG was first discovered in 2016 and is currently believed to be the second largest mining botnet behind only the “Smominru” botnet. Researchers state that DDG has infected approximately 4,000 “OrientDB” and “Redis” servers. To compromise the servers, the actors behind the botnet are exploiting the remote code execution vulnerability registered as “CVE-2017-11467” to compromise OrientDB servers, and brute force attacks to compromise Redis servers. Researchers identified three wallets that appear to be associated with DDG mining operations. It is unclear how much cryptocurrency was mined because of inconsistencies in some of the wallets, but the amount of Monero that has been mined is either 3,395 ($748,359.85 USD) or 5,760 ($1,269,676.80 USD).
Click here for Anomali recommendation
Meltdown/Specter-based Malware Coming Soon to Devices Near You, Are You Ready? (February 1, 2018)
Security researchers have discovered that threat actors are creating malware designed to exploit the recently discovered vulnerabilities located in processors used in millions of devices around the world. The vulnerabilities, dubbed “Meltdown” and “Specter,” affect processors from AMD, ARM, and Intel, and are located in various devices such as computers, servers, and smartphones, among others. If exploited, the vulnerabilities could allow an actor to “bypass memory isolation mechanisms and access everything, including memory allocated for the kernel containing sensitive data like passwords, encryption keys and other private information.”
Click here for Anomali recommendation
Malicious Chrome Extensions Found in Chrome Web Store, Form Droidclub Botnet (February 1, 2018)
A new botnet, dubbed “Droidclub,” is infecting browsers via malicious extensions in the Google Chrome Web Store, according to Trend Micro researchers. At the time of this writing, approximately 500,000 downloads of malicious extensions associated with Droidclub have taken place. The extensions are capable of injecting advertisements and cryptocurrency mining code into websites that an infected machine visits. The threat actors behind this campaign use malvertisements to promote downloads of the malicious extensions.
Click here for Anomali recommendation
Smominru Monero Mining Botnet Making Millions for Operators (January 31, 2018)
A “Monero” cryptocurrency mining botnet called “Smominru” has been using the “EternalBlue Exploit” to infect machines around the globe since May 2017, according to Proofpoint researchers. The botnet is using the combined computing power to mine Monero on a significant scale. Overall, researchers believe that this botnet has mined approximately 8,900 Monero worth approximately $2.4 million USD at the time of this writing. Proofpoint worked with abuse[.]ch and the ShadowServer Foundation. Together they discovered that at least 25 actor-controlled hosts were actively attempting to use EternalBlue to infect new nodes. Researchers identified that the botnet consists of approximately 526,000 Windows hosts, of which are believed to consist primarily of servers.
Click here for Anomali recommendation
Image Previewer: First Firefox Addon that Injects an In-Browser Miner? (January 31, 2018)
Bleeping Computer researchers have identified a malicious extension for the FireFox web browser called “Image Previewer.” The extension was found to display popups and injecting in-browser cryptocurrency miners into Firefox. Image Previewer is distributed via web sites that promote it as a “Firefox manual update”. If a user installs the extension, it will inject a script tag referencing a remote JavaScript file that will monetize visited sites via popups ; the extension is also capable of link click hijacking and advertisement injection. Additionally, Image Preview will open a webpage within an iframe that contains a setup script for an in-browser Monero cryptocurrency miner.
Click here for Anomali recommendation
Critical Oracle Micros POS Flaw Affects Over 300,000 Payment Systems (January 31, 2018)
The Oracle Corporation has released its January 2018 update that addresses 238 vulnerabilities in multiple products. One of the vulnerabilities, registered as “CVE-2018-2636,” affects the company’s “MICROS” Point-of-Sale (POS) systems used by over 300,000 entities around the globe. If exploited, the vulnerability could allow threat actors access to read sensitive information and receive data from other services without authentication from affected MICROS systems. Researchers note that two of the files actors could access after exploitation contain usernames and encrypted passwords which could then be brute force attack them to “gain access to the DB with all business data.” This would result in an entire MICROS system being compromised.
Click here for Anomali recommendation
Dridex Gang Follows Trends, Also Created FriedEx Ransomware (January 30, 2018)
The threat group behind the “Dridex” banking trojan is responsible for creating a new ransomware family dubbed “FriedEx,” according to ESET researchers. The researchers point to multiple forms of evidence behind their assessment. Their evidence consists of similarities between Dridex and FriedEx that include the following: same malware packer, same function for generating a “UserID” for an infected system, some Dridex and FriedEx samples have the same compilation date, among others. FriedEx is distributed “via an RDP (Remote Desktop Protocol) brute force attack.”
Click here for Anomali recommendation
Dutch Banks, Tax, Agency Under DDoS Attacks a Week After Big Russian Hack Reveal (January 30, 2018)
On January 29, 2018, multiple Dutch entities reported being targeted with Distributed Denial-of-Service (DDoS) attacks. Entities that reported such attacks include three Dutch banks in “ABN AMRO,” “Rabobank,” and “ING Bank.” In addition, the Dutch Taxation Authority, “Belastingdienst,” also reported to have been targeted. These attacks took place between January 27 and January 29. The DDoS attacks reached a peak of 40 gigabits-per-second (Gbps). These attacks prevented users from being able to login to the financial institutions and Taxation Authority web portals. Researchers believe that these attacks may be in response to Dutch intelligence services having compromised a machine operated by the Russian Advanced Persistent Threat (APT) group “Cozy Bear.” The Dutch intelligence services shared information gathered from said machine with the U.S. government regarding Russian malicious activity conducted during the U.S. presidential election.
Click here for Anomali recommendation
Cisco Adaptive Security Appliance Remote Code Execution and Denial of Service Vulnerability (January 29, 2018)
Cisco has issued a security advisory regarding a vulnerability, registered as “CVE-2018-0101,” that affects the “Secure Socket Layer (SSL) VPN functionality of the Cisco Adaptive Security Appliance (ASA) Software. The vulnerability could be exploited by a threat actor to allow a reload of the affected or to execute remote code. Cisco notes that there is no workaround for this vulnerability, and the company has issued a patch in response to address the vulnerability that affects 10 Cisco products.
Click here for Anomali recommendation
Three Days of Seamless Campaign Rig EK Pushing GandCrab Ransomware (January 29, 2018)
Security researchers have observed the “Seamless” malvertising campaign is distributing a ransomware dubbed “GandCrab” via the Rig Exploit Kit (EK). The ransomware distribution was observed to have begun on January 26, 2018. If a user clicks on a malicious advertisement associated with this campaign, they will be redirected to a landing page that hosts the Rig EK. Researchers identified that Rig was using an Adobe Flash exploit, as is common with exploit kits, to infect user with the GandCrab ransomware.
Click here for Anomali recommendation
Hacking Group Spies on Android Users in India Using PoriewSpy (January 29, 2018)
An unnamed threat group, believed to have targeted and victimized government officials in the past, is conducting an espionage campaign targeting Android users in India, according to Trend Micro researchers. The actors are conducting their data-theft activities via malicious applications dubbed “PoriewSpy” that were found in the Google Play store. Researchers believe that the actors created malicious apps with “DroidJack” or “SandroRAT” based similarities on their Command and Control (C2) server. PoriewSpy is capable of stealing information from an infected device such as call logs, contact lists, and SMS messages, among others. DroidJack is even capable of fully taking over an Android device if installed.
Click here for Anomali recommendation
Observed Threats
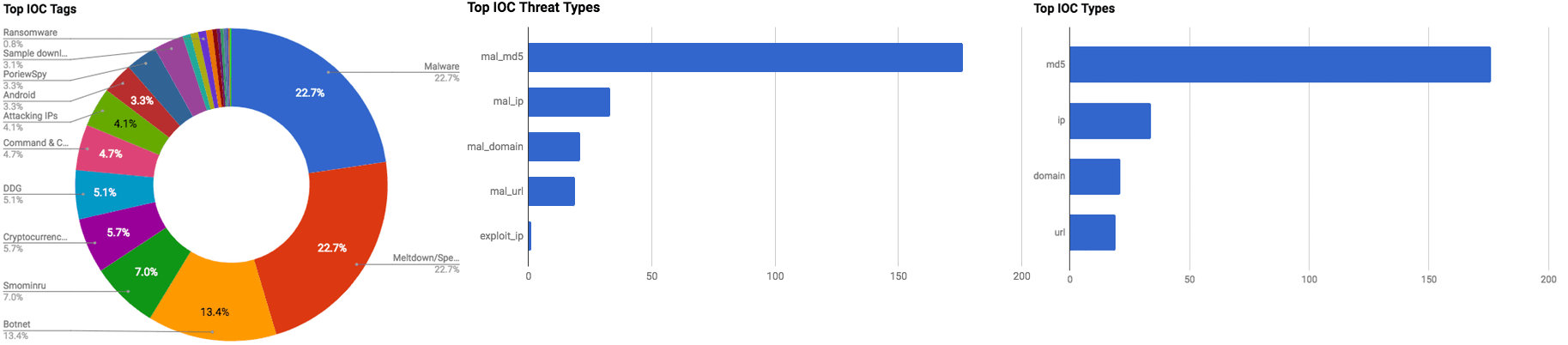
This section includes the top threats observed from the Anomali Community user base as well as sensors deployed by Anomali Labs. A ThreatStream account is required to view this section. Click here to request a trial.
RIG exploit kit Tool Tip
The RIG exploit kit is a framework used to exploit client side vulnerabilities in web browsers. The RIG exploit kit takes advantage of vulnerabilities in Internet Explorer, Adobe flash, Java and Microsoft Silverlight. The RIG exploit kit was first observed in early 2014. The RIG exploit kit's objective is to upload malicious code to the target system. The RIG exploit kit is known to distribute ransomware, spambots and backdoors. Victims are redirected to the RIG exploit kit with a landing page coming from malvertising or compromised sites.
Tags: RIG, exploitkit
FEATURED RESOURCES

Iranian Cyber Retaliation Imminent: Ceasefire Collapse and Critical VPN Vulnerability Create Perfect Storm



