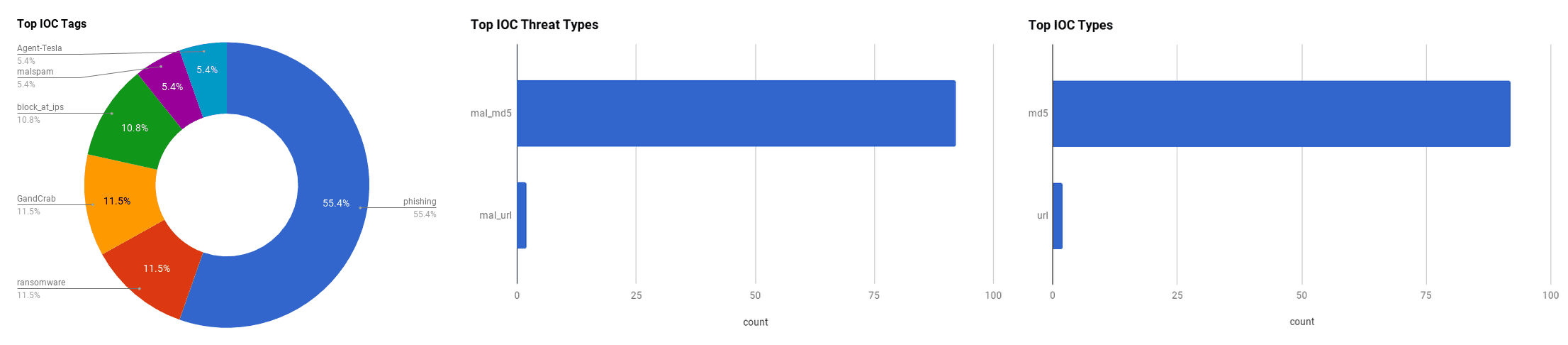

The intelligence in this week’s iteration discuss the following threats: Breach, Cryptojacking, GandCrab, malspam, phishing, Ransomware, targeted attacks and WannaCry. The IOCs related to these stories are attached to the WTB and can be used to check your logs for potential malicious activity.
Trending Threats
Have I Been Pwned: New Sensitive Breach (August 6, 2018)
Adult-FanFiction.org disclosed that they suffered a breach in May 2018. At least 186,000 records were compromised. Data such as names, dates of birth, email addresses and passwords were stored in both MD5 and plain text, which made them easily accessible by threat actors.
Click here for Anomali recommendation
Computer Virus Cripples iPhone Chipmaker TSMC Plants (August 4, 2018)
A computer virus halted production for the company, Taiwan Semiconductor Manufacturing Co., who manufacture parts for the iPhone. The company reported that a number of its fabrication tools were infected. The virus was reportedly contained and the company was able to resume some production, however, several of its factories will not be able to resume production until at least Sunday the 5th of August 2018. The company did not disclose what computer virus affected their organization, though it is speculated that it was a version of WannaCry, or how the virus infected their network, but did say that it was not initiated by a hacker.
Click here for Anomali recommendation
Credit Card Issuer TCM Bank Leaked Applicant Data For 16 Months (August 3, 2018)
TCM Bank released a statement that a due to a third-party vendor's website misconfiguration, names, addresses, dates of birth and Social Security numbers of thousands of people who applied for cards between early March 2017 and mid-July 2018 were exposed. TCM Bank was notified of the breach, and the leak was fixed the next day. TCM Bank stated that fewer than 10,000 consumers who applied for cards were affected in the breach, but they have been notified. While the third-party vendor was not publicly announced, TCM Bank said that they will require the vendor to look at their technologies and procedures to detect and prevent similar issues going forward.
Click here for Anomali recommendation
Alaskan Borough Dusts Off The Typewriters After Ransomware Crims Pwn Entire Network (August 3, 2018)
The Alaskan borough of Matanuska-Susitna or Mat-Su was hit by a ransomware attack that infected nearly all of the local government's servers and network. The attack was spearheaded by the BitPaymer ransomware, but also appears as though another threat actor was able to log into the borough's network to drop other malicious items like the Emotet banking trojan. The threat actors were able to gain Active Directory access which inhibited the controller's ability to reconfigure its security setting. The borough resorted to using typewriters and handwriting receipts to continue conducting business until the systems were cleared and up-and-running again. The local government admitted that the recovery servers were also infected, meaning that data such as email were lost for good unless the decryption key is accessed.
Click here for Anomali recommendation
Web Doc iCliniq Plugs Leaky S3 Bucket Full Of Medical Files (August 3, 2018)
An India-based online medical consultation service left thousands of medical documents and information available to public viewing after it accidentally left them in a public Amazon Simple Storage Service (S3) storage bucket. Their consultation services allow users to ask medical questions in private and they can attach private medical info, to be answered by doctors, which were some of the documents stored in the AWS S3 bucket. The bucket contained over 20,000 medical records. iCliniq failed to double-check their web application's permissions, meaning that users could access anyone's responses to the medical questionnaire by just guessing the ID number related to the question. Once aware of the scale of the breach, iCliniq promptly restricted access to that data and made it private. However, this leaves many patients vulnerable as their confidential medical and personal information could be accessed by unauthorized users.
Click here for Anomali recommendation
DHL-themed Malspam Reveals Embedded Malware In Animated Gif (August 2, 2018)
A phishing campaign to launch malware is parading as a DHL tracking email to evoke users to click on the link. The phishing email is formatted poorly, but can still get users to click on it. If a user clicks the "Track Shipment" link, a zip file is downloaded and directs traffic to an HTTP request that returns an animated GIF that contains malware binaries. This phishing campaign pushes malware using the Agent Tesla keystroke logger.
Click here for Anomali recommendation
After Singapore Medical Data Hack, Hong Kong's Department Of Health Becomes Latest Cyber-attack Victim (August 2, 2018)
Three computers belonging to Hong Kong's Infection Control Branch, Clinical Genetic Service and Drug Office were infected with ransomware. The ransomware encrypted the computers' files and gave an email address to contact for a decryption key though no ransom amount was initially declared. According to the department's spokesperson, none of the computers contained sensitive personal information and no data was leaked. An investigation is ongoing into how the attack began and the motive, but officials theorize that it probably was initiated by using unsafe websites or opening links and/or attachments in emails.
Click here fo Anomali recommendation
Mass MikroTik Router Infection – First We Cryptojack Brazil, Then We Take The World? (August 1, 2018)
MikroTik routers in Brazil sustained a mass infection, utilizing CoinHive to mine for cryptocurrency. The infection took advantage of a vulnerability in the devices that target Winbox allowing the attacker full remote administrative access to the files on the device. While this vulnerability was immediately patched by MikroTik, numerous devices were never updated to apply the fix. The attacker used the device's functionality in order to inject the CoinHive script into every unencrypted HTTP web page that a user visited. This allows the threat actor to covertly miner cryptocurrency over long periods of time and is more difficult to uncover.
Click here for Anomali recommendation
Reddit Got Hacked Thanks To A Woefully Insecure Two-Factor Setup (August 1, 2018)
In a blog post, Reddit notified users that it had suffered a data breach that compromised user emails, source code, and internal files along with all Reddit data from 2007 and earlier. The breach occurred when a threat actor compromised some of Reddit's employee administrative accounts with cloud and source code hosting providers by intercepting text messages two-factor authentication verification codes. Logs from June 3 to June 17, 2018, for the platform's "email digests" also were exposed in the breach. This information could allow threat actors to see the usernames connected to each email address. Reddit stated that all the passwords used for Reddit from 2007 and earlier should be changed to stronger passwords. Text message two-factor authentication (2FA) is known to not be as secure of a 2FA method since threat actors can copy SIM cards to intercept messages.
Click here for Anomali recommendation
Attacks On Industrial Enterprises Using RMS And TeamViewer (August 1, 2018)
Russian-based industrial production companies have been the targets of a recent phishing campaign. The phishing emails pretend to be legitimate finance-based commercial offers to the industrial companies, and each email is intelligently tailored to the target company and the recipient of the email. If the malicious attachment is opened, legitimate remote administration software, either TeamViewer or Remote Manipulator System/Remote Utilities (RMS), is installed onto the machine. The goal of this malware campaign is to steal money from the targeted organization. This specific campaign not only steals money from the target organization, but also searches the correspondence of the employees to then launch attacks on partner companies.
Click here for Anomali recommendation
GandCrab Ransomware Puts The Pinch On Victims (July 31, 2018)
GandCrab is a quickly evolving malware that is currently in its fourth version of development. Threat actors developing this piece of malware has quickly improved its code since its first version, and now is adding comments in it to mock law enforcement, security researchers, as well as "NoMoreRansom.com" which had previously been able to decrypt the GandCrab's encryption keys. The malware uses one of four initial attack vectors: 1. Remote desktop connections that have weak security 2. Phishing emails with malicious links or attachments 3. Legitimate programs that contain malicious trojans with the malware 4. Exploit kits such as RigEK and others The goal of this ransomware it to gain an illicit profit, mainly in the form of the cryptocurrency DASH, though Bitcoin is also used. The newest version of the malware uses Salsa20 to encrypt the infected machine's files instead of RSA and AES. Like many other malwares, this malware checks the machine's operating language, and will not drop the malicious payload if the system operates in Russian or certain former Soviet languages.
Click here for Anomali recommendation
New Crypto-Mining Malware ZombieBoy Exploits Multiple CVEs For Maximum Impact (July 31, 2018)
A new family of crypto-mining malware has been uncovered by a security researcher, dubbed "ZombieBoy." It leverages multiple Windows vulnerabilities to compromise networks and create backdoors. The malware drops a Dynamic Link Library (DLL) file into the system and uses WinEggDrop to infect the systems. The binary is encrypted with Themida and does not run on virtual machines so it is difficult to reverse engineer the malware. Because the malware contains a double-backdoor, it leaves the machine vulnerable to ransomware, keyloggers, and other malicious tools. This "ZombieBoy" toolkit is linked to other Chinese-based malware like IRON TIGER APT.
Click here for Anomali recommendation
NSO Group Infrastructure Linked To Targeting Of Amnesty International And Saudi Dissident (July 31, 2018)
Amnesty International and Saudi activists abroad have been receiving suspicious WhatsApp and text messages since June 2018. Security researchers at The Citizen Lab discovered that these suspicious messages were phishing attempts to infect the target's phone with the "Pegasus" spyware that is linked to the Israeli company, NSO Group. If a target is successfully infected with the Pegasus spyware, a threat actor can spy on their activity by using the camera and microphone, recording calls, logging messages from mobile chat applications, and tracking the device's location. These specific text messages appear to be a part of the NSO Group's infrastructure that has a focus on Saudi Arabia, which coincides with the fact that the newest targets are Saudi Arabian dissidents and an NGO that is focused on human rights' violations.
Click here for Anomali recommendation
FEATURED RESOURCES

Iran's Cyber Arsenal Is Reloading: What CISOs Must Know About the Post-Decapitation Threat Window



