Weekly Threat Briefing: Phishers Target Panicking PayPal Users with Fake “Failed Transaction” Emails
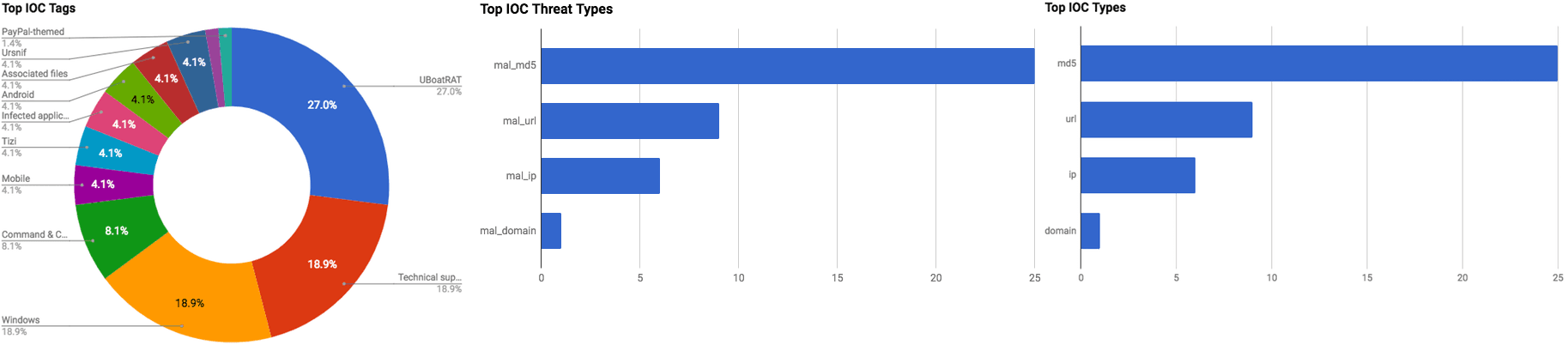

The intelligence in this week’s iteration discuss the following threats: Backdoor, Data breach, Data theft, Malspam, Misconfigured bucket, Phishing, RAT, Spyware, Trackers, and Vulnerabilities. The IOCs related to these stories are attached to the WTB and can be used to check your logs for potential malicious activity.
Trending Threats
PayPal Says 1.6 Million Customer Details Stolen in Breach at Canadian Subsidiary (December 3, 2017)
The American-based online payment company, “PayPal,” has confirmed that a Canadian-based subsidiary suffered a data breach in November 2017. The subsidiary, “TIO Networks,” was purchased by PayPal in July 2017, and is responsible for running a network of over 60,000 utility bills payment kiosks across North America. The unknown threat actors were able to gain access to Personally Identifiable Information (PII) associated with approximately 1.6 million TIO customers and customers of TIO billers. In addition, PayPal stated that some financial details were also likely accessed, however, the specific details of all of the data that was accessed has not yet been released.
Recommendation: The exposure of Personally Identifiable Information (PII) requires affected individuals to take precautionary measure to protect their identity and their finances. Identity theft services can assist in preventing illicit purchases, or applying for financial services from taking place by actors using stolen data. Furthermore, TIO is offering its customers free credit monitoring services, and users should visit TIO’s website (http://www.tionetworks.com/) for additional details.
Tags: Data breach, Data theft, TIO Networks
Phishers Target Panicking PayPal Users with Fake “Failed Transaction” Emails (December 1, 2017)
A new phishing campaign has been discovered to be targeting PayPal customers, according to Malwarebytes researchers. The emails purport that the recipient’s transaction cannot be verified, or that the recipient’s payment process cannot be completed. The text of the email attempts to scare the recipient by claiming that the account password has been changed, or that changes have been identified that are different than the recipient’s typical selling activities. The emails provide a link that directs a recipient to a fake PayPal landing page which then attempts to direct the user to a “resolution center.” The resolution center page requests various data be entered such as city, country, date of birth, mother’s maiden name, name, street address, and zip code. Other requested information includes credit card data such as expiration code, name, number, and security code.
Recommendation: All employees should be educated on the risks of phishing, specifically, how to identify such attempts and whom to contact if a phishing attack is identified. Emails that request that the recipient follow a link that then asks for credentials to be entered is often an indicator of a phishing attack.
Tags: Data breach, PII, National Credit Federation
Credit Crunch: Detailed Financial Histories Exposed for Thousands (November 30, 2017)
On October 3, 2017, UpGuard Director of Cyber Risk Research Chris Vickery, discovered an Amazon Web Services (AWS) S3 bucket cloud storage bucket that contained sensitive information that was configured for public access. The bucket was found to be owned by the United States credit repair service the National Credit Federation (NCF). The data that was publicly available for download consists of addresses, bank account numbers, credit card numbers, credit card reports (from Equifax, Experian, and TransUnion), date of birth, driver’s license image, full names, personalized credit reports, and social security card image. Overall the data consists of 111 gigabytes of data and is believed to be associated to approximately 40,000 individuals.
Recommendation: The exposure of Personally Identifiable Information (PII) requires affected individuals to take precautionary measure to protect their identity and their finances. Identity theft services can assist in preventing illicit purchases, or applying for financial services from taking place by actors using stolen data. As of this writing, it is unknown if threat actors downloaded the data, however, appropriate precautions should be made to assist in mitigating the possibly of malicious activity.
Tags: Misconfigured AWS bucket, Data leak, PII
Uber Breach Affected 2.7 Million UK Users (November 30, 2017)
The global transport company, “Uber,” has released additional information regarding a security breach that took place in late-2016. Uber only just confirmed that a breach had occurred in late November 2017. After the breach took place in 2016, Uber reportedly paid the threat actors responsible for the breach, which affected approximately 57 million riders and drivers, $100,000 USD to destroy the stolen data instead of contacting the appropriate authorities. The stolen data consists of email addresses, full names, and phone numbers, in addition to approximately 600,000 Uber driver’s licenses numbers. The new information bodes more bad news for the company as it now states that approximately 2.7 million U.K. residents are also affected by the breach.
Recommendation: At the time of this writing, Uber has not confirmed whether financial data may have been stolen during this incident. However, as Uber has proven, it is not best to rely on a company that does not inform its users of a breach so that they may take steps to protect themselves. Uber users should change their passwords for their accounts as soon as possible, and any other account that uses the same password (every account should use a different password). Furthermore, regular credit card statement monitoring should be common practice to assist in identifying potentially malicious activity.
Tags: Data breach, Data theft, Uber
Fake Windows Troubleshooting Scam Uploads Screen Shots & Uses PayPal (November 29, 2017)
Researchers have discovered a new technical support scam that is targeting Windows operating system users. Threat actors are distributing this scam via a cracked software installer, according to Malwarebytes researcher, Djordje Lukic. The scam begins by showing a Windows user a fake Blue Screen of Death (BSOD), followed by displaying an application that purports to be a Troubleshooter for Windows. The “troubleshooter” application will then present a user with a screen that states that the computer cannot be fixed. It will also block the user from using Windows. Lastly, the actors behind this scam will then prompt the user to purchase a program via PayPal for $25 USD to fix the “issues” that were detected.
Recommendation: Technical support scams are common threats facing individuals and companies alike. However, this scam is a screen locker rather than the often observed phone number provided to contact an individual to assist in “fixing” the “issue.” Often times there are research blogs that provide instructions to remove malware related to these type of scams from an infected machine. This story also depicts the potential dangers in downloading software installers. All downloads should be carefully vetted prior to installation, particularly free versions.
Tags: Tech support scam, Windows
Cisco Releases Security Updates (November 29, 2017)
The United States Computer Emergency Readiness Team (US-CERT) has issued an alert regarding vulnerabilities in Cisco’s online meeting software “WebEx.” Specifically, in WebEx Network Recording Players for Advanced Recording Format (ARF) and Recording Format (WRF). The US-CERT states that a remote threat actor could exploit these vulnerabilities to take control of an affected system.
Recommendation: The US-CERT recommends that WebEx users and administrators visit Cisco’s security advisory located at “https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20171129-webex-players” and apply the necessary updates.
Tags: Alert, Vulnerabilities, Cisco
UBoatRAT Navigates East Asia (November 28, 2017)
Palo Alto Networks Unit 42 researchers have identified attacks in which actors are using a new, custom Remote Access Trojan (RAT) dubbed “UBoatRAT.” The first discovery of UBoatRAT occurred in May 2017, and in this iteration the actors behind the malware have added new malicious features. This variant is distributed via links that direct to a Google Drive, followed by executables masquerading as a folder, a Microsoft Excel spread sheet, or Microsoft Word files. While researchers have not yet been able to pinpoint specific targets for this malware, they have discovered that individuals and organizations that are targeted typically are associated to South Korea or the video games industry.
Recommendation: Malware authors are always implementing different methods of communicating back to the control servers. Always practice Defense in Depth (do not rely on single security mechanisms - security measures should be layered, redundant, and failsafe).
Tags: Malware, RAT, UBoatRAT, Google Drive
Newly Observed Ursnif Variant Employs Malicious TLS Callback Technique to Achieve Process Injection (November 28, 2017)
A newly observed Ursnif variant has been observed employing Thread Local Storage (TLS) callbacks in an attempt to avoid sandbox and analyst detection. TLS allows Microsoft Windows to define data objects that are not placed on the stack. It is stored in the PE header. Ursnif has TLS callback functions which initialize and clear TLS data, executing code before the “start” of the program to unpack DLL files stealthily. The malware is delivered by spear phishing emails containing a link which downloads the malware from a compromised Sharepoint account.
Recommendation: Always be on high alert while reading email, in particular when it has attachments, attempts to redirect to a URL, comes with an urgent label. As shown in this story, if the email suggests you access a resource that is meant to be viewed through the browser, but downloads a file instead, delete the file immediately. If the message appears to come from a person within the company, check with them first to make sure they sent the email. Employ email signing techniques for authentication. This technique is meant to evade sandboxes and signatures, use up-to-date anti-spam and antivirus protection.
Tags: Malware, Ursnif variant
Pro Tip: You Can Log Into macOS High Sierra as Root With No Password (November 28, 2017)
Developer Lemi Orhan Ergin has released information via Twitter regarding a security issue that affects macOS High Sierra. The issue can be exploited by anyone who has physical access to the machine. An individual simply needs to navigate to System Preferences, Users & Groups, click the lock to make changes, and then use “root” as the username while leaving the password field blank. After clicking “Unlock” several times an individual can gain administrator rights to that machine.
Recommendation: Researchers note that this vulnerability cannot be exploited in High Sierra if a user has set a root password for the machine. Users who have not set a root passwords are vulnerable. It is crucial that your company has policies in place in regards to administrator accounts. All work-related machines should have complex root passwords in place. In addition, employees should be in the habit of putting their work machines into sleep mode when not in use to prevent unauthorized access to potentially sensitive data. Furthermore, Apple has a released a patch for this vulnerability that should be applied as soon as possible if it has not been already.
Tags: Vulnerability, macOS, High Sierra
No Patch Available for RCE Bug Affecting Half of the Internet’s Email Servers (November 28, 2017)
The team behind “Exim,” a Mail Transfer Agent (MTA), has issued an alert on their website warning that its product contains two vulnerabilities. The vulnerabilities reside in Exim’s most recent versions in 4.88 and 4.89. The critical vulnerability, registered as “CVE-2017-16943,” is a “use-after-free” (attempt to access memory after it has been freed) vulnerability and can be exploited to allow arbitrary code execution on affected servers. Security researchers believe that as many as 400,000 email servers may be affected.
Recommendation: The Exim team have released a patch that addresses both these vulnerabilities. Immediately update to version 4.89.1 or apply the teams workaround to block an attack from being performed; in the main section of the Exim configuration, set “chunking_advertise_hosts=”. The empty value disables advertising the ESMTP Chunking extension, thus allowing an attacker apply the logic. According to a survey conducted in March 2017, 56% of the entire Internet’s email servers run Exim. Furthermore, a public proof-of-concept code for this exploit has been released which increases the likelihood that threat actors will attempt to exploit this vulnerability.
Tags: Vulnerability, RCE, Email servers, Exim
Researchers Identify 44 Trackers in More Than 300 Android Apps (November 28, 2017)
Researchers from Yale Privacy Club and Exodus Privacy have released information from their collaborative report regarding third-party tracking in Android mobile applications. The two teams identified tracking scripts in both popular and less popular Android applications, which sometimes track a user without his/her consent. Overall it was discovered that over 300 Android applications contain 44 different forms of trackers. Researchers note that some of application’s trackers contain trackers that only collect application crash reports, such as Google’s CrashLytics, while other trackers collect application usage information of which some was noted to be sensitive in nature.
Recommendation: Always keep your mobile phone fully patched with the latest security updates. Use the Google Play Store to obtain your software, and avoid downloading applications, even if they appear legitimate, from third-party stores. In addition, it is important to review the permission the application will request and comments from others who have downloaded the application. Furthermore, it is paramount that mobile devices be kept up-to-date with the latest security patches and employ trusted antivirus software.
Tags: Android, Mobile, Trackers, Applications
Phishing Scam Cashing in on Water Refunds (November 28, 2017)
A phishing campaign is targeting customers of the Irish water services company “Irish Water,” according to ESET researchers. The actors behind this campaign are attempting to generate illicit revenue by using phishing emails that purport to be Irish Water requesting the recipient to perform account maintenance. The email provides a link for the recipient to “log in” to their Irish Water account. If the link is followed, a prompt will appear that requests a user to “update” their credit and debit card information.
Recommendation: Impersonation of legitimate entities is a commonly used tactic by threat actors in malspam and phishing campaigns. It is important to educate your employees on the risks of opening attachments from unknown senders. Anti-spam and antivirus applications provided from trusted vendors should also be employed. Emails that are received from unknown senders should be carefully avoided, and attachments from such senders should not be opened.
Tags: Phishing, Theft, Irish Water
Tizi: Detecting and Blocking Socially Engineered Spyware on Android (November 27, 2017)
The Google Play Protect security team has discovered a new form of Android malware, dubbed “Tizi,” which was first found in September 2017. Tizi is a fully featured backdoor that is used by threat actors to install other malware designed to steal sensitive information from popular social media applications. Additionally, Tizi is also capable of exploiting multiple vulnerabilities to root a device. Worryingly, researchers also found that the malware goes back until at least October 2015, indicating that some users could have been infected with Tizi for nearly two years. The Tizi creator also created a website and social media accounts to advertise malicious applications. This malware primarily targets African countries, specifically Kenya, however other countries such as the U.S. were also found to have Tizi infections.
Recommendation: Google has since disabled Tizi-infected applications, and have stated that they have also notified users of all known affected devices. Users should carefully review all permission that application will request prior to installation. In addition, applications should be downloaded from official locations to better avoid potentially malicious applications.
Tags: Android, Mobile, Spyware, Malware, Backdoor, Tizi
FEATURED RESOURCES

Iran Declares Ceasefire Over: Cyber Retaliation Window Opens for Critical Infrastructure



