ANOMALI AGENTIC AI
AI-guided security decisions — powered by complete data and real threat intelligence — across detection, investigation, and response.
Why ThreatStream Next-Gen
Why Anomali Agentic AI
300x Faster detection and investigation
Analysts pivot across years of data and intelligence in seconds.
96% Reduced time for threat investigations
Context-driven prioritization reduces false positives and alert fatigue.
50% analyst time saved with operationAlized intel
Threat intel informs every stage of the SOC workflow, not just reports.
60% reduced siem bill and operational cost
Eliminate SIEM tax and manual effort while scaling data retention.
Built for Security Decisions – Not Just Automation
Most AI security tools focus on automating tasks. Anomali Agentic AI is designed to guide security decisions. It reasons over complete telemetry enriched with threat intelligence to recommend and execute the right actions at the right time.
AI-assisted reasoning
across detection, investigation, and response workflows.
Context-aware decisioning
grounded in real security data.
Human-guided automation
so analysts stay in control.
Actions informed by years
of historical and real-time context.
Core Capabilities
AI-Guided Detection & Prioritization
Combine analytics and intelligence to surface high-confidence threats.
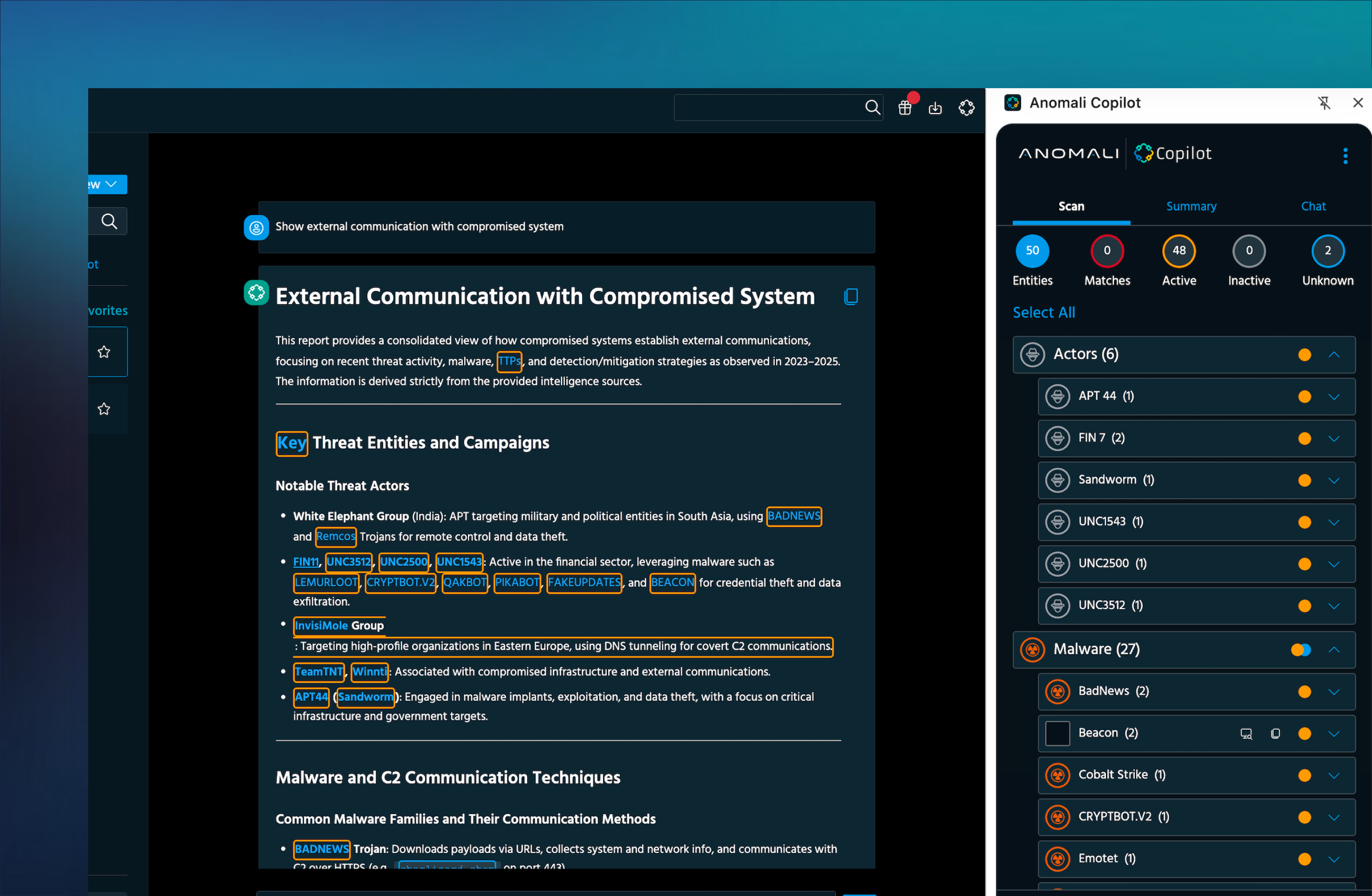
Guided Investigations
AI assists analysts with recommended pivots, context, and next steps.
Agentic Response Workflows
Automate enrichment, triage, and response while keeping humans in control.
Intelligence-Driven Decisions
Threat intelligence informs every stage of detection, investigation, and response.
SOC-Native Experience
Designed for analysts — fast, intuitive, and operational.
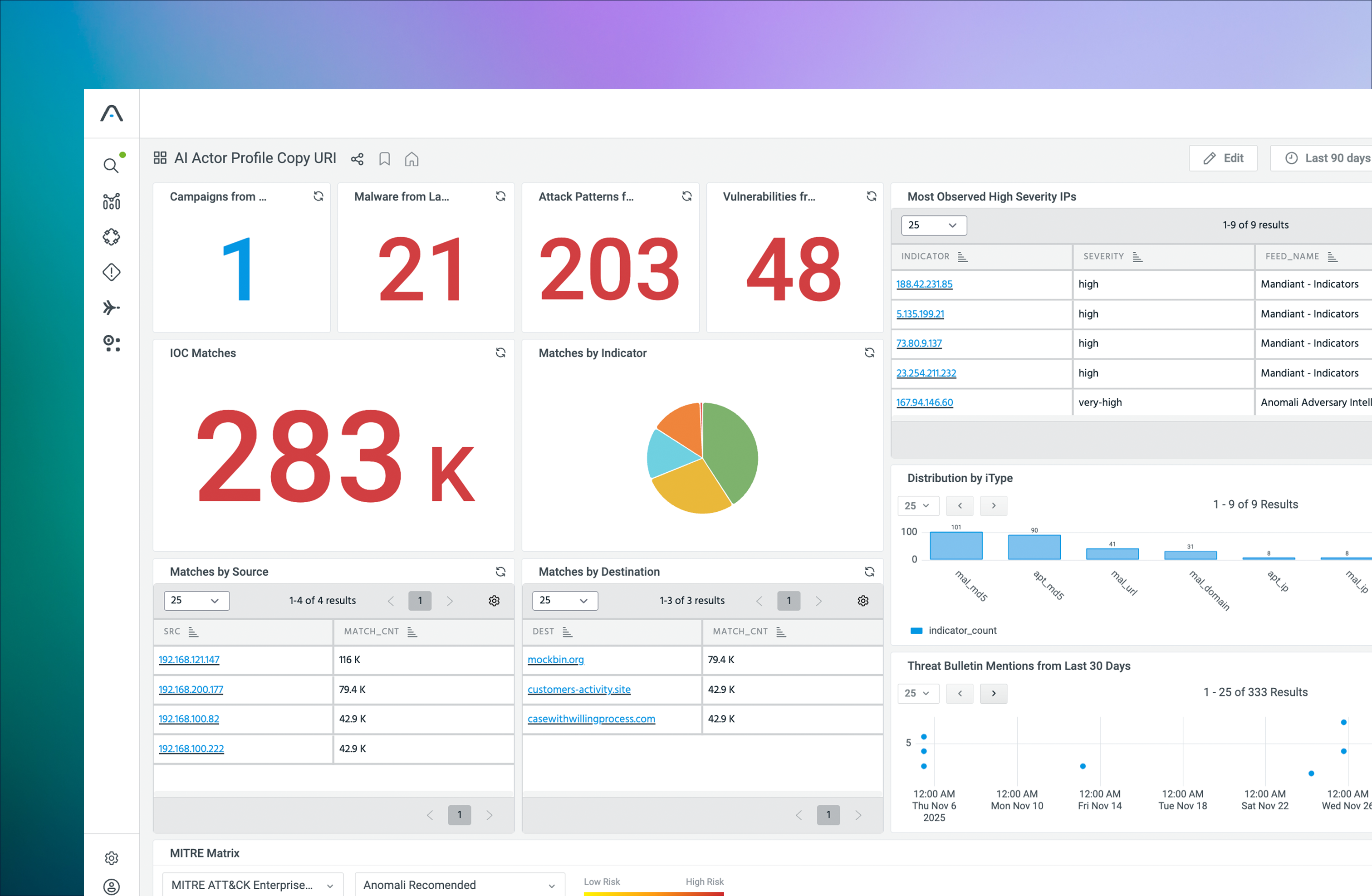
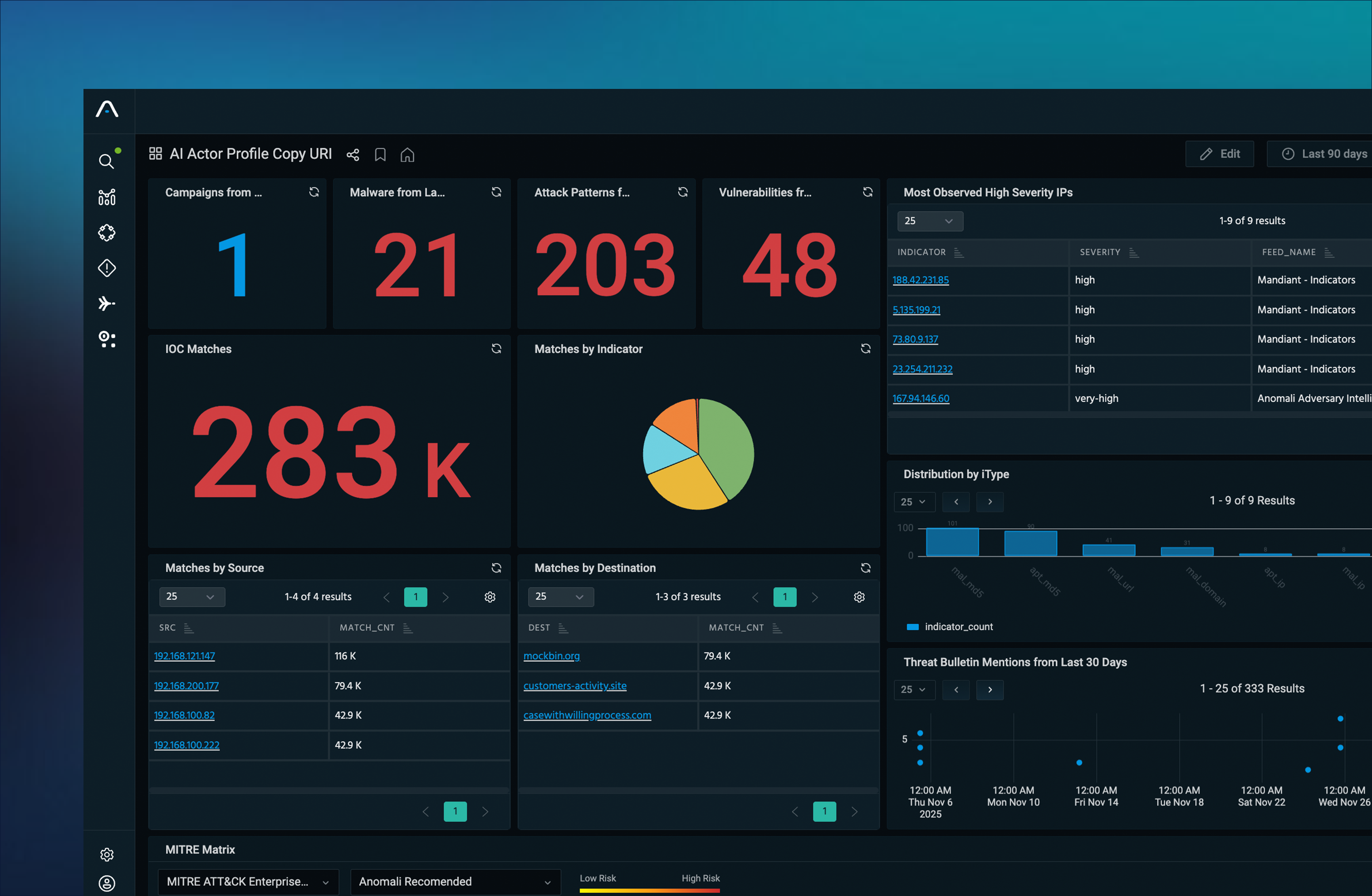
AI-Ready Insights Powered by Complete Data
Act faster, investigate smarter, and respond with confidence.
How it works
1. Detect and Prioritize
Analytics and intelligence identify what matters now.
2. Investigate With Guidance
AI recommends investigative paths using complete context.
3. Respond and Automate
Execute automated or guided actions across your security stack.
3 layers, one operational platform
Three Layers. One Operational System.
Unified Security Data Lake
data foundation
ThreatStream Next-Gen
intelligence and context
Agentic SOC Platform
execution and action
Deploy together or adopt incrementally.
Customer Proof
"Having Copilot is like having another mature analyst. We went from 3-hour IOC collection to 3 minutes"
— SOC Manager, Global Enterprise
Move From Information to Action
Enable AI-assisted security operations built on complete context.