Anomali Enterprise
Businesses and government agencies face huge new challenges in information security.
Attackers are working around the clock to steal your customer data, proprietary business data, cause business disruptions, and damage your brand.
Companies continue to struggle with limited security staff to get the visibility they need to detect, investigate, and respond to incidents.
They collect vast amounts of log data representing host, user, and network activities.
They also collect an ever-growing amount of threat intelligence data.
These data sets are two sets of fingerprints.
One set used to identify anomalous activities inside your organization.
And the other is evidence of their activities across the internet.
Both data sets contain tens of millions of pieces of information called indicators of compromise.
Security teams attempt to collect, evaluate, and compare these data sets to understand if a security compromise has occurred.
However, traditional tools often fail to scale to make threat intelligence timely and relevant for their organization.
Introducing Anomali Enterprise.
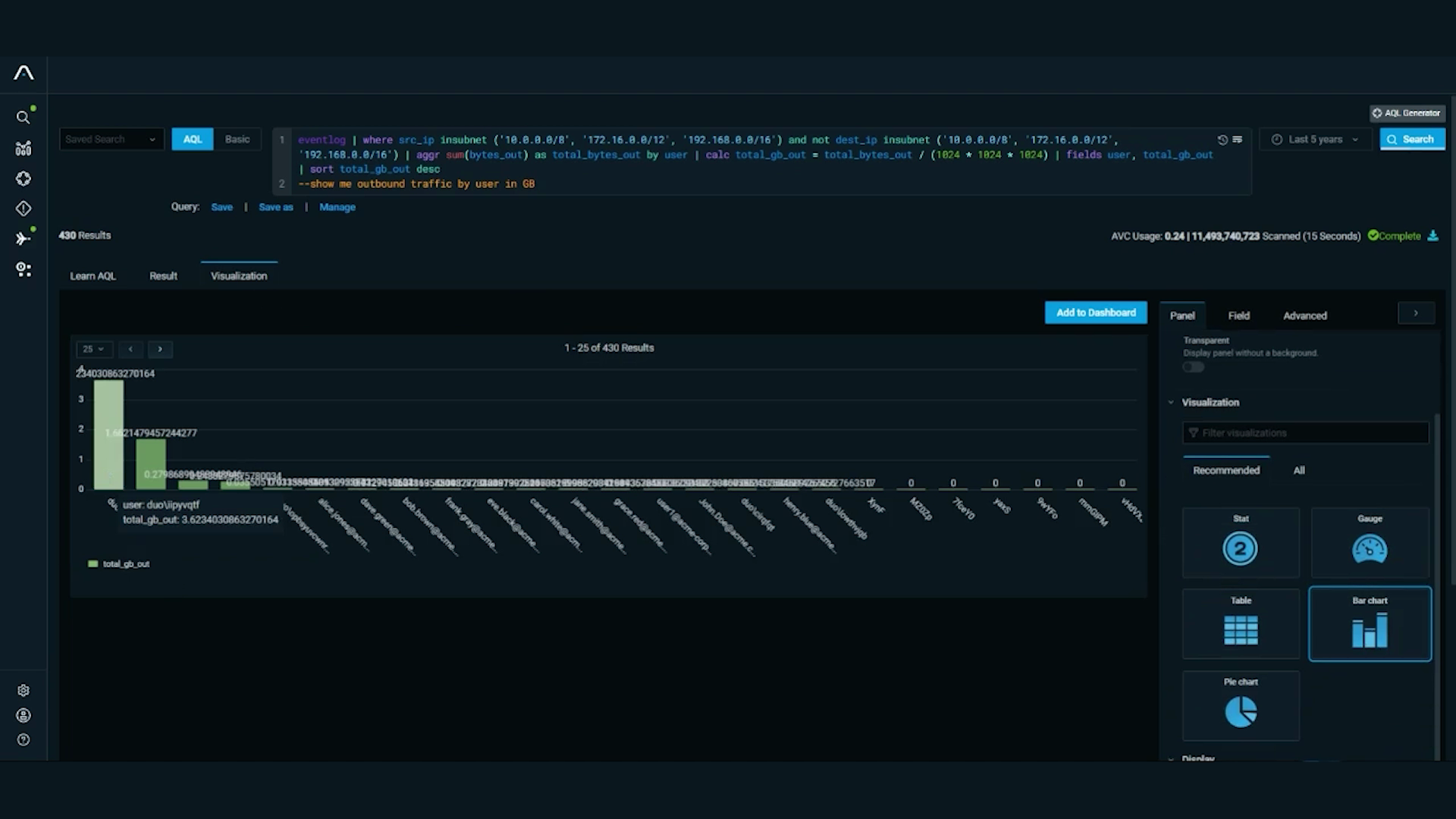
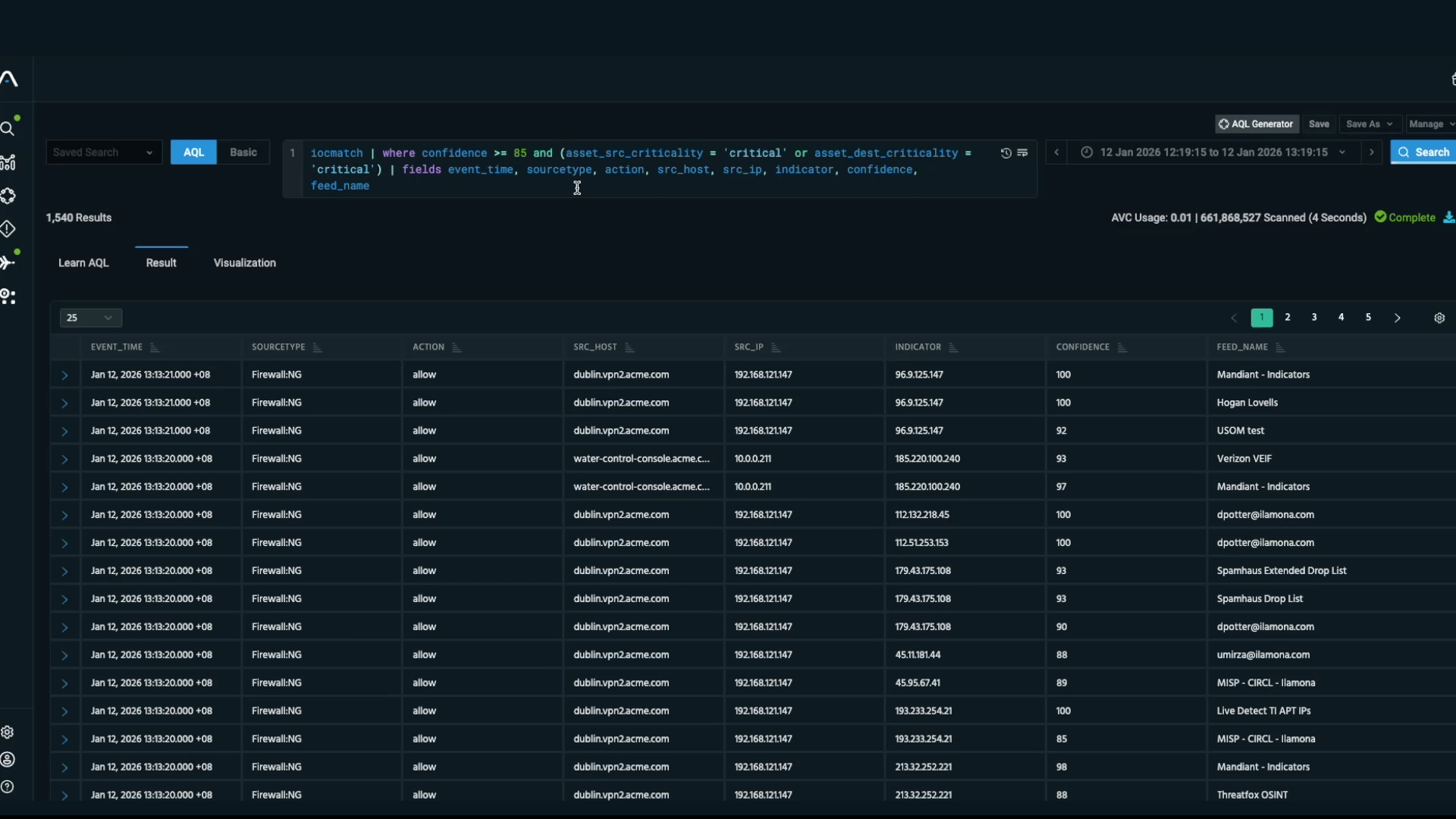
Anomali Enterprise continuously pulls threat indicators from up to a year's worth of your security log data and looks for matches in tens of millions of indicators of compromised and threat intelligence data.
This unique approach creates a security time machine that constantly compares up-to-the-minute threat intelligence data with log data collected as far back as a year ago.
This shatters the 200-plus-day attacker dwell time exposure window often cited in security research reports.
Suddenly, your security team knows what threat intelligence data that is relevant to your organization at any given moment.
Anomali unlocks the hidden value of threat intelligence data for incident responders and security operations personnel.
Want to know if company email addresses are in the hands of attackers, if data exfiltration has occurred, and identify connections to botnets and attacker-infected web sites with a single solution?
Get Anomali.
Intelligence with relevance.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.