CISO Series Defense in Depth: The Iran Cybersecurity Threat
DAVID SPARK: The Iran conflict has threatened new retaliations, and we don't know where they're going to come from.
Cyber retaliation is a real possibility.
Who's being threatened and how should we prepare?
WOMAN: You're listening to Defense in Depth.
DAVID SPARK: Welcome to Defense in Depth.
My name is David Spark I am the producer of the CISO Series.
Joining me as always is Alan Alford.
We are available at cisoseries.com.
Our sponsor for today's episode is Anomali.
That is Anomali with an i at the end, Anomali.
We thank them for sponsoring this episode of the podcast.
So the reason we're talking about this is a lot of companies are showing a lot of concern.
Vendors that I have spoken to say they're getting flooded with calls from customers asking what do we do.
So Alan set us up.
ALAN ALFORD: This is a timely topic.
But honestly one that should be on our minds far more often than just when such an extreme and specific incident occurs.
Right?
DAVID SPARK: Yes.
ALAN ALFORD: We chose this topic now because of how many folks are out there churning at the moment, but I think it's something we need to focus on all the time.
Some vendors are ignoring, others are exploiting the situation, it's the usual some vendors adopt the flight approach.
Practitioners reactions are all over the map and a lot of folks have a lot of questions.
So we're hoping to dive into this and get into it a little more.
DAVID SPARK: And by the way I'm going to give a major qualifier for this episode before we really jump in.
Like you would see on a medical website, don't assume that the advice that's been given out here is prescriptive.
Consult your security consultant or whoever you speak to, your local ceaser or whatever it is, for advice in your specific situation.
We're going to be talking about in some cases generalities, what certain industries do.
So I don't want people to take everything that is being said or anything specific as prescriptive as you must do this now.
Are we on the same page with that Alan?
ALAN ALFORD: Sounds good to me.
DAVID SPARK: All right.
Now I want to bring in on our sponsored guest, who is perfect for this subject because, well, heck, he is looking at threats all the time not just when everybody's ears are perked up.
It is Nicholas Hayden he is the global head of threat intelligence for Anomali.
Nicholas, thank you so much for joining us.
NICHOLAS HAYDEN: Thank you for having me, David.
I'm happy to be here.
Where do we begin?
DAVID SPARK: Christoph DeLong of Conquest Federal summarized the US department of Homeland Security's CISO cyber cybersecurity advice and I looked through it and it seemed like just general good cyber security, bur not necessarily tied specifically to Iranian attacks.
And MWD Robbins, a contractor at Booz Allen Hamilton said, quote, I personally do not see any difference because in my opinion both cyber threats and cyber warfare have become 100% transnational dealing with organized criminal networks.
This will kind of teasing what you said at the onset Alan.
Everything we're hearing is just sort of, do the basics like you should be doing ALAN ALFORD: I think it's a little more than that.
But to MWD Robin's point, it's a fair point.
North Korea has shown us that the difference between nation state attacks and criminal attacks can be non-existent.
They can be one and the same.
So that peace is there for certain.
And as far as what the CSA advised, you're correct.
Chris's advice if you look through it, and again he was just summarizing the report, it's what I call the fundamentals.
Harden your systems, disable and data and protocols, patch monitor backup, etc.
These are all the activities that should be ongoing part and parcel and not just things that arise when incidents arise.
DAVID SPARK: Very, very good point.
I'm going to take this to you Nicholas.
Is it just basic advice keep doing what you're doing or when issues like this come up, is there a heightened need to do more?
NICHOLAS HAYDEN: So, yeah, I would have to echo what Mr.
Robins and Alan are both saying is, yeah, it is business as usual at this point.
We have attacks coming from all different avenues, all different perspectives.
There is a match between the different threat actors, whether it be nation, state or criminal.
They're both coming at you.
They're both using the same tactics and techniques.
And in fact, now within the threat intelligence base we're actually seeing the attribution cross pollinating so that they can cause false flags, which is the perception of one act of threat act to group that is utilizing tactics and techniques of another threat act to group in order to hide their tracks, so to speak.
So, yes, this is business as usual.
The one advice that I would give is that now is a good time to start practicing your incident response plans in your disaster recovery because as it's been stated time and time again it is not a matter of if, it is a matter of when.
So during these times of heightened security that is probably the best time to start practicing and making sure that there are no holes in your processing procedures with regards to instant response in disaster recovery.
DAVID SPARK: And we're going to get into this a little bit more later in the show.
But the reality, and I'm going to ask you again Nicholas, is that sometimes sadly we need these kinds of threat for us to start paying attention to our own security.
ALAN ALFORD: Yes.
NICHOLAS HAYDEN: Absolutely.
As a general rule of thumb, most of the companies that I've ever been a part of or have ever spoken to is they have a documented instant response and disaster recovery plan that should be challenged and executed at least once every 13 months.
But the problem is is that doesn't always happen.
And then when the time comes that you actually need it, that's when you start to find out that there are holes and gaps and some misunderstandings.
WOMAN: How do we handle this?
DAVID SPARK: Paul Callaghan of Data Defense Solutions said, quote, nation state risks need to be considered in a threat profile for any org or agency.
And sort of you were kind of tipping this like look at your incident response situation, Nicholas.
And I also want to mention what Travis Howard of the US Navy office of Legislative Affairs said, quote, investing in threat hunting and dwell time reduction is what it takes to eject an APT.
Facing a state sponsored APT is a different ballgame.
So at that point right they're going to go to you, Nicholas.
Is that what it takes to get rid of an APT?
I mean, like, first of all, we don't know necessarily if we're facing an APT.
Let's start with that, each individual company.
So where should they take this and what does ejection look like?
NICHOLAS HAYDEN: Yeah.
Absolutely.
And you're spot on, David.
You don't always know if you're facing an APT.
I think the point is that you should just assume everything is an apt, always assume the worst case scenarios.
But dwell-- DAVID SPARK: Let me just pause here for a second.
Always assume the worst-- doesn't that get into a DEFCON 5 all the time and people just can't maintain at that level?
Or am I wrong in this thinking?
NICHOLAS HAYDEN: This day and age, I would say that that's not completely accurate.
So you wouldn't go to DEFCON data or unless some of your critical business systems are compromised.
So the DEFCON 5 would come after the fact, after you realized-- DAVID SPARK: OK.
So you're not saying that everyone should be on ludicrous heightened alert all the time.
OK.
Go on.
NICHOLAS HAYDEN: Precisely.
Precisely.
Yeah, absolutely.
And what I mean by saying that you should assume that it's always apt, assume that they're hidden.
Assume that they've migrated their processes, they've hidden themselves, they're only beginning out.
Assume that you have to go above and beyond for the detection capability.
You go into DEFCON when you start hemorrhaging data or your business, your critical business assets have actually been compromised.
DAVID SPARK: All right.
Let me then take this to you, Alan.
At what level, you know, when something like this comes about, do you start obsessing about do I have any PT on our network?
ALAN ALFORD: I'm with Nicholas on this one.
And the reason is you have to assume the worst case scenario.
It used to be that one little event would occur, like I don't know, let's say you find one phishing email.
And you would dismiss it, and contain it, and move on about your business.
These days, you have to assume that a phishing email is part of an attack chain that is part of some sort of intended larger scale effort, that it's part of possible ransomware, whatever it might be.
So I think this idea that everything could be treated as an actual APT, I think is valid.
So I'm there with that.
DAVID SPARK: Let me pause.
Let's just say you get a phishing email, and you say, we have to assume this is part of an attack chain.
What are you then doing at that point, instead of just saying, oh we got the phishing email, it's gone.
What are you doing after the fact?
ALAN ALFORD: So it's going to depend on the circumstances.
But you know, you're looking at IP addresses.
You're looking at domain.
You're looking at sender.
You're scanning all your inboxes to see if similar emails have been sent, anything from the same IP, anything with the same keywords.
You know, you're looking for other presence.
You're then looking through network and firewall logs to determine if those IP addresses were related to anything else for those domains, you know, et cetera.
So you're going to take that one piece of evidence you have and you're going to expand your search around it and look for threats in other areas and nooks and crannies of your business that might tie back to the same source.
DAVID SPARK: So essentially you're going to use that, what you might think is a first attack, as a piece of evidence to do deeper investigation.
ALAN ALFORD: Exactly, exactly.
Now let's be honest though.
My post was created without any acknowledgment of any hard intel on the subject, right?
I mean, I had a very general post about, hey, what are you thinking about Iran.
And I knew the defense folks and the intel folks and the law enforcement folks would see my post.
And I predicted that they probably wouldn't really do a lot of responding.
And I was right.
And the reason is those folks have got access to a lot harder intel than we have.
But it's not necessarily intel that they can or want to share.
If you've got a pretty good hard detail set on what's exactly coming out of Iran, you're not going to just jump on the internet and publish that.
So I expected it to be sort of radio silence on that end.
So to Travis Howard's point, I think there are real concerns there specific and unique.
And there are hard data there, there is hard data there specific and unique.
But that doesn't mean the rest of us necessarily have it.
DAVID SPARK: I want to mention something that Jesse Lyon of Bizinsure said, quote "a consequence of last week is going to come from China and Russia helping Iran with cyber attacks." So I'm going to ask you, Nicholas, how exactly does China and Russia help Iran with cyber attacks?
NICHOLAS HAYDEN: So whenever we look at cyber, or even the missiles going across and hitting the different bases, it's all based on foreign policy.
So war comes about when foreign policy or foreign negotiations fail.
And so the same thing can be said true with the cyber attacks.
They're very similar to kinetic attacks.
Now one of the things that I think that Iran will utilize is Russia and China's cyber expertise.
It's been known throughout history that Russia has been very good at setting hooks into the different industries.
So for example, there has been proof that Russia has had hooks either in the past or maybe even currently within the electrical sector, their energy sector within the US.
Now if I was in Iran's shoes, one of the things that I would look towards is disrupting the oil and gas industry within the US.
So from a foreign policy perspective, if I was Iran, I would be negotiating with Iraq and some of the other leaders within that industry who supply oil and gas to a good portion of the world and start to disrupt the US based oil and gas industry.
Such that the US needs Iran, that not only disrupts our economy.
So for example, I live in the Middle East, or not in the Middle East.
I live in the Northeast, I apologize.
And so if you start raising my heating and oil expenses, that drastically affects the economy within the Northeast and within those colder areas, also in the northern central areas as well.
So by disrupting that, you're actually disrupting the economy within the US, which is a little scary.
And then it puts Iran in a position of power, because of the oil and natural gas, oil and gas industry that they have control over with regards to selling back to the US.
[MUSIC PLAYING] WOMAN: Why are they behaving this way?
DAVID SPARK: Brian Sander of High Trust said pretty much what Nicholas said just a moment ago, which is this is a great opportunity and/or excuse to evangelize review basic cyber hygiene and security posture.
Tim Vander Mill, C3 technology advisor, said we have a customer whose board member now wants to be a part of some of the conversations we're having.
Which is great, because education is taking place.
It's unfortunate sometimes it takes events like this to spur that action.
So I'm going to throw this again to you, Nicholas.
This is a normal pattern that all of a sudden we become heightened when a big news item like this happens.
But as we know from what Iran is historically done, they may not take action for months or years.
So being heightened now may not necessarily be of any value.
NICHOLAS HAYDEN: That is correct.
So being heightened now, as I mentioned before about the instant response, right, everyone develops a plan and starts a plan and then has the full intention of practicing the plan within the 13 month period.
But as time progresses, we all get sloppy by nature.
Now the one thing I will say that this is an excellent opportunity because of the heightened senses for every CISO to essentially sell to the board on fear.
We have this threat.
This is what we need for resources.
So I would say for, if I was in a CISO position, I would use this opportunity as a selling approach to fill in those missing gaps within your security program that historically speaking you haven't been able to get the funding for.
DAVID SPARK: Let me [INAUDIBLE] check, because we're kind of a little anti-fear on this show, or selling a fear.
And we've talked about how fear is sold by vendors and sold internally, too, as well.
Explain to me how you would settle-- you're not going to come in and go, oh my god, you guys, the walls are crashing in, we've got to spend money right now.
I mean, what is the appropriate selling point here?
NICHOLAS HAYDEN: So the first thing I would do is look at what your security program is and find the gaps.
So for example, maybe you don't have a threat intelligence program that has been implemented.
Or maybe you're missing a certain toolset within your disaster recovery.
Or maybe there is not a good interaction between you and the marketing with regards to the disaster recovery plan.
So utilize this as an opportunity to fill in those gaps in order to strengthen your defense in depth strategy.
DAVID SPARK: All right, Alan, let me take this to you.
So what would be your sort of advice?
It's like, all right, I'm going to use this situation for my benefit here.
But I don't want to sell fear too hard.
How would you approach this?
ALAN ALFORD: I guess first of all, I want to comment on Bryan Sanders' comment about reviewing the basic cyber hygiene.
Ever since [INAUDIBLE] [?
Levi ?] was on the show, I'm a big believer in I don't call it basic anymore, I call it fundamental.
And the reason for that is basic makes it sound like it's easy.
Fundamental is the same definition, but doesn't have that implication that it's easy to do.
Fundamentals are the fundamentals.
They're the building blocks.
But it may take a while to lay those building blocks.
So if the board comes to me, or the CEO comes to me, and says, hey, this Iran business, what are we doing about it.
I'm going to have a good answer that says, we're exercising the fundamentals.
Maybe to Nicholas' point, we're going to run an IR cycle, a trial run, you know desktop.
Maybe we're going to test our BCP, whatever it might be, that is normal part and parcel, but maybe you accelerate the schedule.
And if there's truly a gap in my program, if I truly feel like there's tools I don't have or people I don't have or whatever, I might bring it up if they bring it up.
But I'm not going to go knocking down their door and screaming the sky is falling, gimme, gimme, gimme.
But I expect them to come to me on this kind of event anyway.
And we'll have an honest and open conversation.
I'm feeling pretty darn prepared here.
And I've got this and that and the other, but you know, it would be nice if we had this, there is a slight risk of that.
And keep it, you know, keep it as a risk based conversation.
But I would wait for them to come to me.
DAVID SPARK: You don't have to give any specifics, but I got to assume there has been talk in your companies about this subject, yes, Alan?
ALAN ALFORD: Well, sure.
Folks have asked.
Folks have brought up questions and, you know, conversations have been had for sure.
DAVID SPARK: Are they at a hysteria level?
Like is it just more confusion?
Where are they?
ALAN ALFORD: I think it's more confusion.
I haven't seen any hysteria.
But again, when you've got the fundamentals under control and you know you have the fundamentals under control, there's no reason to panic.
DAVID SPARK: So let me ask the same question to you, Nicholas.
Like I'm assuming this topic has come up already.
Is it at a point of confusion?
Is it a point of are we susceptible?
Where are they when concerned customers or potential customers come to you?
NICHOLAS HAYDEN: Yes, it is hysteria.
That's what we're seeing.
DAVID SPARK: Oh, OK, NICHOLAS HAYDEN: We get constant requests.
Now keep in mind that threat intelligence is risks based.
It's fear.
That's the basis of what it is.
You're afraid of something's going to happen.
So you're going to try to find out as much information as you possibly can.
So, but yes, we're getting requests that look like, show me and give me everything that is related to Iran that could possibly be a threat to us.
When you do threat intelligence or threat collections, it's really not that simple.
There is an assumption that is going on that individuals or companies are collecting everything about everyone and know every bit of detail about everyone.
So at a push of a finger, you can just deliver that information.
DAVID SPARK: Push of a button, I'm assuming you're trying to say.
Use a finger to do the pushing.
NICHOLAS HAYDEN: Yeah, yeah.
Absolutely.
But yeah, so there is some mass hysteria on it.
And you know, from our perspective, it's a matter of grounding people and letting people know that it really is business as usual.
We will supply threat intel reports based on what we have from Iran.
But as a general rule of thumb, you're probably not going to get every bit of information around the world of every possible situation, of every possible scenario that Iran could be scaling up.
[MUSIC PLAYING] WOMAN: If you look at the problem this way.
DAVID SPARK: Rob Earl of Avira offers some advice that was originally produced by the British government in 1939.
He said, and that's keep calm and carry on.
Should it be situation normal and just do what you're regularly doing, which we've essentially touched upon at this point.
And David Sterling at CISO at Zions Bank Corporation said, there is a lot of tension initially while this is in the news, but the biggest challenge will be maintaining vigilance for weeks and months ahead, as we had mentioned earlier.
You can't ask your lay colleagues to be on heightened alert for months on end.
Again, we reference this.
So Andrew Garcia of Entity also asked, do you ask your team to do an extra good job, better than what they have been doing in the past.
Part of the problem could be hysteria and fear we are creating ourselves.
So I'll start with you, Alan.
People think they should do something differently.
What do you tell them at this point?
ALAN ALFORD: Yeah, so I wanted to point out one thing.
We were earlier talking about DEFCON.
And it's actually DEFCON 1 is the highest alert stage.
DAVID SPARK: Oh, so I had it completely wrong.
ALAN ALFORD: The scale goes backwards.
But if you look at what DEFCON 1 is from the military perspective, right, what is the military doing when it's DEFCON 1?
Certain folks are working longer shifts.
More people are put on different tasks.
There's an upping and ramping up of resources when DEFCON 1 hits.
In the private sector and in most companies, we don't necessarily have that luxury.
In other words, oh, Iran happened.
Let's hire eight more threat intel guys real quick.
Let's deploy another million dollars worth of hardware real quick just for the duration of the conflict.
And after it's over, you know, we'll somehow magically send those people home and unspend the million dollars.
It doesn't work that way in the real world.
So it's trickier.
To say you're on heightened alert, I challenge that whole concept.
What is heightened alert?
Look at your average hospital.
Look at your average small bank.
Look at your company that manufactures t-shirts for a living.
What is high alert?
What is heightened awareness?
There's not going to be a whole lot that they're going to be able to do to extend or stretch their capabilities.
And so it really once again boils down to that fundamentals conversation.
If you've got everything in place and you're doing the right things already, you shouldn't need quote unquote "heightened alert".
And that's where I come down on this.
And to Andrew Garcia's comment, you know, hysteria and fear, you can churn the waters and you can stir people up.
But at the end of the day, what are they actually going to do differently if they're already doing all the right things?
Now to the earlier conversation, if they're not doing all the right things, this is that time to go upstairs and have that conversation.
DAVID SPARK: So I'll ask you pretty much the same question, Nicholas.
Do people have to do an extra good job at this time?
And do you believe that we're forming the hysteria?
I mean, again, if you are just doing threat profiling as a normal course, this would be part of your regular course of business.
NICHOLAS HAYDEN: Correct.
You know, there's not a lot I can add to that Alan hasn't already said on this topic, with the exception of you may change your intel collection requirements a little bit to maybe gear towards Iran as a potential threat.
DAVID SPARK: That's a good point.
And again, I'm assuming this is all dependent on what industry, whether you'd be a target or not.
NICHOLAS HAYDEN: Correct.
The other thing is, I would be very hesitant to say to any of my team, or if I'm a CISO, especially if I'm a CISO, to say, I want you to do an extra good job.
It comes off as a little condescending, an assumption that they're not already experts.
They're not already doing what they're supposed to be doing.
So I would be very careful about saying that.
But yeah, from an intel perspective, the only real thing that I could add is just you may add an intel collection requirement that is geared a little bit more towards collecting information with regards to the capabilities that the Iranian government has and making sure that you're not seeing them within your network.
DAVID SPARK: Well, I think the headline here or the summary of this entire episode is, you should just be doing the right thing in the first place.
You don't need Iran to get you all hot and bothered.
Yes?
NICHOLAS HAYDEN: Absolutely.
ALAN ALFORD: Sounds right to me.
DAVID SPARK: All right, well I want to conclude today's episode and thank Nicholas profusely for your help and your advice on essentially an issue that has been coming up and we had to actually talk about it.
And I appreciate actually you guys, Anomali, approaching us and saying, hey, let's do an episode on this very subject.
And so we said all right, you're right.
We should.
Because even if much of the advice is do what you should be doing, but be aware of your specific situation, your specific threat profiles, people sort of need to I guess sort of have that sensible conversation.
And I think they appreciate you, Nicholas, and you, Alan, getting their head straight.
Because there is, as you guys both mentioned, confusion and hysteria going on depending on who you are.
I want to thank Anomali again for sponsoring this episode.
Nicholas, I let you have the last word.
Alan, anything you'd like to say?
ALAN ALFORD: I want to thank Nicholas for coming out.
I want to thank Anomali for sponsoring the show again.
Threat intel is a really fascinating subject for me.
I'm always poking around that world.
And it's always good to hear from the experts about threat intel perspective when issues arise.
So Nicholas, thank you very much for coming out.
DAVID SPARK: And Nicholas, if anything you'd like to plug about Anomali, please go right ahead and do that.
And I want to also apologize to my security audience for so screwing up the DEFCON numbering system.
Because I know I'm going to get a lot of hate mail or something like, you buffoon, how could you have not known that.
But Nicholas, go ahead.
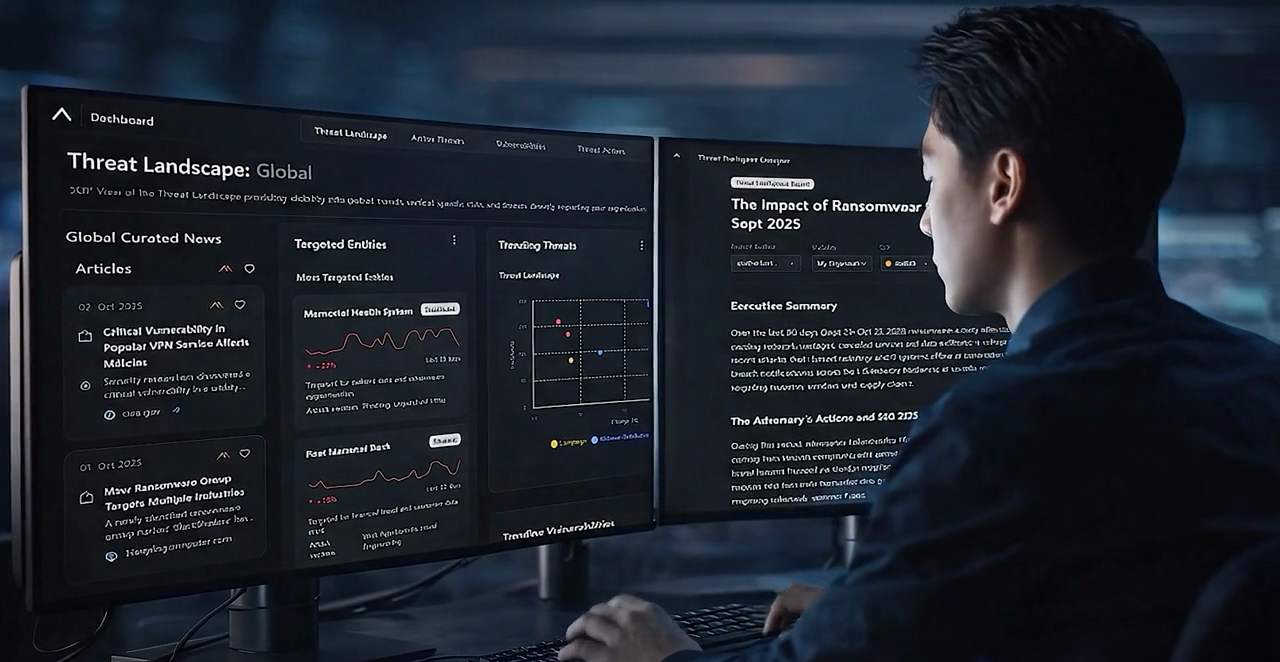
NICHOLAS HAYDEN: Yeah, so at Anomali, we have one of the world's leading and threat intelligence platform, as well as supplying threat intelligence.
So you know, go to Anomali.com for more information.
And thank you for having me.
DAVID SPARK: Well, we're thrilled to have you, and we greatly appreciate your advice and sensibility on this very episode.
And I want to thank our audience for participating in the discussions as always.
I mean, we greatly, greatly appreciate it.
As you can see, I couldn't sort of steer this show if it wasn't for your great contribution.
So thank you again.
And thank you for listening to Defense in Depth.
WOMAN: We've reached the end of Defense in Depth.
Make sure to subscribe, so you don't miss yet another hot topic in cyber security.
This show thrives on your contributions.
Please write a review, leave a comment on LinkedIn or on our site, CISOSeries.com, where you'll also see plenty of ways to participate, including recording a question or a comment for the show.
If you're interested in sponsoring the podcast, contact David Spark directly at david@CISOSeries.com.
Thank you for listening to Defense in Depth.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.