MITRE ATT&CK Framework
Well, thanks for stopping by.
Today's show is about the MITRE ATT&CK Framework.
It's an essential knowledge base that you need to be using within your organization to be more secure.
It's essentially a taxonomy of the different ways an adversary is going to come at you so you can be prepared.
You can know the different tactics and techniques, and then all the different data sources that you can pull from in order to be able to start to defend yourself better Otherwise than you'd be able to.
It helps you find the gaps within your own security practice.
It's all open source.
It's free.
I encourage you to use it.
You'll be more secure if you do.
Now, today's episode runs a little bit longer than the average episode.
And that's because our guests do such a fantastic job of explaining all the different nuances of the MITRE ATT&CK Framework.
They walk through some of the tools you can use, and just some of the ways you can think about threat intel in some new ways as well.
Welcome to Threat Actions This Week, the show where we look at the latest threats, tech, and actions your organization can take.
Today's top security talent share their insights with you.
And I'm joined by three individuals who know how to turn the tables on attackers with tactics and techniques.
Say that 10 times.
We've got Katie Nickels.
She is the lead cybersecurity engineer from MITRE.
They are the creators of the ATT&CK Framework that we'll be unpacking today.
She's joining out of the Washington DC area.
Pleasure to have you on board, Katie.
Thanks so much for having me, David.
It's great to be here.
Thank you.
And Travis Farral He is the director of security strategy at Anomali.
He has an infectious passion for the ATT&CK Framework.
He's in the San Francisco area today.
Glad you could join us, Travis.
Yeah, thanks for having me, David.
And David Strom.
Too many accomplishments to even list.
So many articles, speeches, books, mentoring, et cetera.
Strom.com, S-T-R-O-M.com.
How you got that five letter domain, must have been early on.
Joining us out of St.
Louis, Missouri.
Thanks for making the time, David.
Thank you, David.
It's a pleasure to be here.
So the MITRE ATT&CK Framework, and the NIST Cybersecurity Framework, and a bunch of other frameworks are coming to the fore and getting a lot of popularity.
I guess first to disambiguate, to separate out the NIST Cybersecurity Framework from the ATT&CK Framework is that the NIST framework kind of works perpendicular, Travis, to the Mitre framework in that when I think about identify, protect, detect, respond, and recover, then I can use that to walk through the different elements of Mitre.
Now, we're going to pull apart the Mitre ATT&CK Framework.
But just to kind of separate those two out.
I know some listeners might be thinking, wait a minute?
Yet another framework?
How do I think about all these different elements?
The ATT&CK Framework is sort of a common vernacular to use for all the different techniques that you might be looking for or that you might observe, whereas NIST really kind of lays out the how of how you should be doing things, and a list of recommendations of how you should be defending your environment.
I have a little bit different look at it.
I would say the ATT&CK Framework is actually useful in your day to day operations.
I think one of the key things as we created ATT&CK is that we wanted it to be useful and actionable.
So NIST and other security guidelines are useful at a different level sometimes.
People are planning.
But we wanted ATT&CK to be actionable for especially defenders.
So we based it on what adversaries are doing in the real world.
So that's kind of a key differentiator and way to think about it.
And so Katie, when you think about ATT&CK, there's a number of use cases, right?
It provides this common language for communicating with different individuals in your organization, or across other organizations.
It helps you assess some of the capability gaps in your defenses, even to prioritize some of the security investments in the organization as well.
And that really it's a progression from the Lockheed Martin kill chain.
So how do you take this massive knowledge base and distill it simply for organizations to understand?
Yeah.
It's definitely a challenge.
When we talk about ATT&CK there are a few pieces of it.
The one that most people are familiar with is ATT&CK for Enterprise, which is how the adversaries get into your network, and then what they do post exploit, focusing on Windows, Linux, and Mac.
And it can be really overwhelming, because right now there are 11 tactics, which are the adversary goals, and 219 total techniques just how they achieve those goals.
So it's overwhelming for people when they first look at it.
Something that I like to recommend-- I come from a threat intelligence background.
So we have a bunch of examples on our website of how different groups have used ATT&CK techniques.
One thing I like to say is that if there's a specific group you're concerned about, go to the website.
See if they're already mapped there.
And look at what they've done in the past.
It gives you a way to start prioritizing based on the actor group that you might be most concerned about.
And you've mentioned a bunch of other ways ATT&CK can be used, whether it's mapping your detections.
It can be used to help your red and blue teams communicate, all those use cases.
And I think I forgot to mention that it's an acronym.
So it's the Adversarial Tactics, techniques, and Common Knowledge.
Yeah.
That's kind of a mouthful.
So if you just say ATT&CK, we know what you mean.
So the thing I like about the ATT&CK Framework is that it gives some common ground you can use between different aspects of your defense.
So if you've got, as Katie mentioned, threat intelligence folks that are looking into the actual actors, and you have an instant response group that's dealing with actual seeing these tactics used inside the environment, it gives you that ability to sort of marry those two things together so that instant response sees these things happen.
Threat intelligence can then look and see, hey, that maps up against these actors that we've seen in the past, or ones that are known publicly or whatever.
The other thing too that I think is really cool about it is, it gives you a little bit of focus.
From a defensive perspective when things are happening all the time, and you get phishing attacks, things happening on public facing websites, this gives you kind of a road map of things to look into from a defensive perspective.
And it kind of spells out things that you can be doing mitigation wise, detection wise, based on sort of the knowledge around those different techniques.
So I love that all of this is stored in one database.
And it just makes it a lot easier from a defender's perspective.
And so, David, how do you start to cut through it?
Because it's a roadmap, but I'm thinking of spreading out and unfolding this massive map of all the roads in the United States, and trying to say, OK, go on a trip.
It does give me this ability to have this complete view of the environment.
But at the same time, there's a lot of things.
So especially if I'm a smaller organization, I might be thinking, OK, well, where do I start with all this?
I think the difference between what we're trying to do as defenders and driving your car across country on the highway system is we have an intuitive knowledge of if we go on the interstates, we're going to go 75 miles an hour.
We're not going to have too much in the way of delays, unless you're driving through Illinois, cause that's where there's a lot of road construction.
You sort of figure that out intuitively because of the knowledge that you gain from driving a car.
Well, defenders don't necessarily have that intuitive knowledge, especially as attackers and criminals try to break into their infrastructure, and are constantly changing their techniques, and constantly adding blended threats, and producing very complex attacks methodologies.
And so what's really great about the MITRE ATT&CK system, or framework, whatever you want to call it, is that it gives you that organizing structure.
And it gives you sort of a leg up on how to develop that intuition.
And also, we talked about blue and red teams.
And I think it's important to understand what is a red team?
Cause a lot of companies don't have them.
They just have people that are trying to prevent bad guys from getting into their network.
And they're looking at logs, and doing whatever they're doing with various firewalls and other tools.
And what you're purposely trying to do with a red team is to create a simulation of what an attacker does, only in a safe environment so that you're not going to actually compromise your data and spread it out across the internet.
And by using the similar tactics that these guys do, you can have a better understanding of what they're trying to do, and try to defend it better.
A lot of small organizations may not want to have their own red team.
They may not be able to afford it.
Or they just don't necessarily have the expertise to get involved in it.
So in that case, they may look for open source tools like the ATT&CK collections from various vendors.
Or they're going to hire a consultant, or a managed service provider, or a security operations center for hire.
They're going to do something outside of their organization.
So in that case, still having the knowledge of ATT&CK is useful, because you can at least talk to these people in a coherent way.
So you've raised a number of really interesting points that I definitely want to circle back to around what red team exercises might look like, what are some of the tools that organizations may want to consider, and what are some of the outsourcing options, or what are just some of the options that they've got available if they don't have their own SOC, Security Operation Center, or what have you.
I love what David was pointing out there.
I think one of the cool things with the ATT&CK Framework is that even if you don't have a red team, to sort of extend what he was saying, and let's say, as part of your compliance issues, you have to have a penetration test every year.
It makes a lot of sense to have those penetration tests where it's basically doing adversarial simulation of one or more actor groups that you think might be targeting your organization, and have them follow the ATT&CK Framework as they go through so that you can now see areas where you have gaps.
Here's the steps that the penetration testers took as they followed this mapping of this particular adversarial group.
And here's the areas where we're able to see activity.
Here's the areas where we were not able to see activity.
And being able to dig into the information that's available about those techniques that they used and figure out like how can I close these gaps, what detection strategies, what mitigation strategies should we be pursuing over the next year to try to close those off?
So I find that it's super useful in all kinds of different contexts from a defensive perspective.
That's a great point, Travis.
And one thing to add on the adversary emulation piece is my MITRE teammates, like Cody Thomas and Chris Corbyn, worked on an APT3 adversary emulation plan they released a couple months ago that's on the website that anyone can use.
It gets down to the command line level and what commands you would run to try to emulate APT3, especially using ATT&CK techniques.
So that's one resource that even a newer red team or a penetration testing team could try out.
Katie, when you think about who is using ATT&CK, is it security pros, security analysts, developers, executives?
How do you find it being used out in the wild?
So one of the things that we think is really powerful about ATT&CK is that you can use at whatever level makes sense for you.
So for an executive level, maybe you just look at those tactics across the top, those adversary goals, lateral movement.
Or maybe you ask your analysts to make you a chart showing what your SOC can detect.
Whereas for the analyst level, [INAUDIBLE] defenders, red and blue team, they might want to get really deep into each of those techniques, and say exactly what are the ways that I can detect credential dumping?
How can I write analytics in my environment to detect that?
So that's one thing that we think is powerful is that you can use it at whatever level you think is useful for your use case.
David, one of the things that's not immediately obvious when you start looking at ATT&CK is the number of people that are actually actively contributing to its use, and its development, and its increasing utility.
It's not just the folks at MITRE.
Although MITRE is the primary caretaker of the thing.
But there are many vendors in the security universe selling both their own tools for profit, as well as contributing open source addon methods that complement the MITRE efforts.
I don't know what the number is, but it's definitely in the dozens.
That's a great point, David.
We've heard from a ton of people who are using it, both vendors who are incorporating it into their products, as well as end user SOCs in a bunch of different sectors.
And some of those people have contributed back ideas for new techniques, or changes to the model, or threat group positions.
Some people haven't.
But yeah.
ATT&CK is free and open to anyone who wants to use it.
If I'm finding that, oh, I want to add this or that, what's the process for doing that?
Absolutely.
Right now it's email us-- attack@mitre.org.
Myself and our lead, Blake Strom, check that mailbox all the time.
And so if you have ideas, we'd love to hear from you.
We're looking for new technique ideas.
As MITRE, we don't have all the answers.
And we don't claim to.
It's really important that we bring the community's perspective, what kind of behaviors is everyone seeing from attackers?
So yeah.
You can just email us.
And we actually have a document that I should be tweeting out in the next few days explaining the types of contributions we're looking for in particular.
Sorry, David.
I cut you off.
I was just going to say, despite Blake's excellent last name, we're not related.
[LAUGHTER] Important clarification.
Appreciate that.
So David, you started to talk earlier about some of the tools that I can use in order to be able to bring the ATT&CK Framework to life within my organization.
And you did some analysis of some of the tools that are out there.
What did you find?
So I looked at four of them for CSO online.
MITRE has its own thing called Caldera, which is maintained separately from the framework, but obviously is intimately tied into it.
Red Canary has their product called Atomic Red.
Uber has developed an open source tool called Meta that they use in their infrastructure.
You would think it's interesting that a company that is a ride sharing company is using it, but, again, that's a testimonial to its extensiveness.
And then Endgame has something called red team automations.
And each of these tools, they're all free, by the way.
Each of them does something slightly different.
And they work a little bit.
Some of them are harder to use.
Some of them are easier to use.
They all don't necessarily support the same attack scenarios.
So that's kind of annoying.
You have to look and see the way that they work.
Some of them are useful for scripting purposes, so you can do automated testing of your products, like the Endgame product.
They developed it to show how effective the endpoint detection tools are.
So if you've got a project where you're looking to get a new ADR in a solution into your company, you may want to get up to speed on something like that.
Travis, what do you think?
I mean, I hate to use marketing-ese.
I'm at loss for a better term, but that's the single pane of glass if you will.
How do you see that evolving in the market?
So being knowledgeable about these different tools that David mentioned.
I love the fact that you're seeing all these different approaches to using the ATT&CK Framework, and sort of using this same model of different techniques that maps back to the ATT&CK Framework so that defenders can, again, have that singular way of referring to things that could happen, that adversaries could be doing in their environment.
And I'm really excited that because there's differences in these tools, and because they kind of approached different problems, and they are applied differently, I fully expect that we'll see a lot more energy into this going forward, and probably lots more open source tools coming out.
And I think also on the commercial side, maybe to get some more of what you were talking about with the single pain of glass, as commercial vendors start to get involved in this, I know that there's some of the adversarial simulation companies out there, like Verodin and so on, are fully trying to adopt the ATT&CK model as far as being able to map the adversarial techniques that their platforms do inside the environment to the framework.
So, again, having this common language, I think it's really going to make things a lot more simple.
Even though the framework's really big, it's better to at least have some of these specific targets to talk about, and say, hey, we really suck at detecting DDE exploitation, for instance.
Anybody that's familiar with the framework will know exactly what you're talking about.
And I think everything's heading in a very good direction all because this framework exists.
So actually, can we take it back just one step.
And I know it's the middle of the show.
We're kind of jumping back a little bit.
But maybe just review some of the top tactics.
Because I know we kind of went right into the middle and started to explain some of the value of it, and some of the tools around it, and some of the use cases.
But maybe for someone who's just a little bit unaware of some of the things that the ATT&CK Framework can do, maybe just review some of the tactics, Katie, from your perspective.
So I'll go over ATT&CK for Enterprise first.
I mentioned that's covering how the adversaries gain access, and what they do after they've entered your network.
So those tactics, which we describe as the adversary's goal are initial access, execution, persistence, privilege escalation, defense evasion, credential access, discovery lateral movement, collection exfiltration, and command and control.
And a question we get really often is, are they in the order that you list them?
Is there some kind of order to this?
Is it like the kill chain?
Not exactly.
They're sort of roughly in order.
You can see initial access we usually put on the left, command and control on the right.
But we don't want to tie that order to a specific way, because adversaries will move back and forth.
They might persist, and then they might move laterally and exfiltrate.
Then they might go back and make sure they're persisting still.
So that's one clarification we get quite a bit.
I should mention that I just described tactics for Enterprise ATT&CK.
We also have Pre ATT&CK, which focuses on what adversaries are doing before they get in your network, and then Mobile ATT&CK.
So there are separate tactics for each of those.
I like the point that you started to make around it not being a chain.
In other words, that I follow from one to the next, to the next.
Now, you can follow it I think, as Travis and David were indicating as well, kind of like a roadmap in a sense, just so you have some order to the operations you're going to do within your organization.
But when you're thinking about it from the adversary's point of view, you're not necessarily thinking about it in a particular order, cause really, as you're saying Katie, they can go anywhere they want at any point in time.
Yep.
Exactly.
I think someone asked that on Twitter recently.
Like adversaries don't think linearly.
So why is ATT&CK displayed in a matrix?
Something like that.
For simplicity's sake, we display it usually as that matrix view.
But adversaries don't care about that.
They're going to move around to wherever they want to.
So where do I start?
Yeah.
So I mentioned, one thing I like to do is pull up the group examples that we have on our website.
If there's a group you're really concerned about, look at the techniques they use.
Another thing I like to recommend doing, and you can do this via the STIX TAXII API, we have for each technique a list of data sources that you would need to detect that technique.
So what you could do is, hey, let's say I can collect registry information.
If I have registry information, what out of all of the ATT&CK techniques can I detect?
And from there you can start to say, hey, I already have this data.
So let me write analytics.
Let me write some kind of detection for those techniques that I already have the data for.
So that's one way that people can get started.
I know it can be a little overwhelming.
So we're also working on a blog series to help people pull the string on these use cases a little bit.
I think from my perspective, David, what ATT&CK makes you realize is that malware creators or attackers are putting together these various building blocks out of these different components that Katie mentioned.
And they're not necessarily doing it in any organized fashion.
They're just piling things on so that it makes it harder to find, it makes it harder to stop.
And it makes it more effective and lethal on our network.
And you're a defender, you can say, OK, I got compromised by a piece of ransomware, or I got compromised by a phishing email, or something.
And that's a singular moment in your time, your work day, because your network went from working fine to being all messed up because of this event.
But what ATT&CK makes you start thinking about is that piece of ransomware got through an email filter.
It got clicked on by a user who wasn't paying attention.
And it downloaded a file, this piece of malware that's exploiting a PowerShell environment, which some anti-malware tools don't pick up on.
So there's this whole sequence of things that happens.
And a good way of looking at this, at Palo Alto Networks, their Unit 42 research operation, they have put together a playbook for the oil rig malware, which is a pretty infamous piece of malware.
And there are 19 different ATT&CK techniques, and 100 different ways that you can detect this thing.
So it's a very, very complicated piece of malware, even though you just say, well, that's just one malware.
So I think understanding sort of the infrastructure, the dependencies, the way that the kill chain is constructed, the particular obfuscation techniques, all those things are really helpful if you're going to try to defend yourself in this.
So Travis, as an adversary, I only need to find one entry point, but similarly, as a defender, you only need one indicator, don't you?
In order to be able to catch me as the bad guy?
I mean, that's true.
But it has to elevate itself to the right status.
Having the indicator buried amongst millions of other indicators and it gets overlooked isn't so useful to a defender.
But knowing that that particular indicator is maybe an indication that there's something really nasty in their environment, if that knowledge can be applied, then it does become very useful.
And I think this is one of the things that the ATT&CK Framework really helps us do.
Because I really want to piggyback on what David was making a very good point about.
At the end of the day, defense is all about, man, we got this phishing attack this morning.
And it came.
We think it was a Necurs botnet and it was LokiBot.
And unfortunately, some people clicked on it, and we had to clean up some mess as a result of that.
So this is like day to day in a defender's world.
What the ATT&CK Framework helps us do is go back into that event, and be able to determine like why did this malware, as David pointed out, get through our spam filter.
What technique is it using to get past there?
And then document that.
And the whole thing, all the way through to the click, to the command and control, document all those things, apply to which techniques from the ATT&CK framework were used by this particular attack, and which ones were we good at detecting?
Which ones did we suck at detecting?
And how can we go back and, to Katie's earlier point, apply some analytics with the tools we already have in our environment to try to detect that stuff in the future, or even mitigate it if we can.
This is really kind of, I think, the magic that the ATT&CK framework brings to defense is it gives them sort of this roadmap and already like a good starting place, for as they determine it was this technique.
You could look that up in the framework, and it stalls out.
Like here are some strategies you can apply to try to detect this.
Yeah.
And to build on what Travis was saying, I think we've seen a shift in the past few years to where people are actually looking inside their networks with the assumption that adversaries are already in.
When I started in this field nine years ago, it used to be, let's lock down the perimeter.
Let's lock down our firewalls.
They'll never get in.
People are realizing, OK.
They're going to get in.
And I think that's where Enterprise ATT&CK can really help is that, OK, let's assume that the adversaries have gotten in.
We really need to focus on how you catch the ones that have gotten into your network.
And I think that we've seen a lot of progress in this area in the past few years, especially with the rise of EDR products to help out with that.
And so what are some of the best practices around documenting basically what, Travis, you're talking about, and Katie and David as well?
What are some of the ways, maybe some of the tools that I might want to use?
I think so it depends on what you're trying to do.
For initial incident response, whatever tools you have at your disposal.
I'd say if you're trying to track what techniques adversaries are using, the ATT&CK Navigator, which we have a hosted instance of-- you can see it from our web page, attack@mitre.org.
We have a link.
That's a way you can kind of visualize different technique use.
So if you have an adversary that you're tracking in your environment, and you want to visualize what techniques they use, the ATT&CK Navigator would let you do that pretty well.
I think it's also worth mentioning, security people love to pile on tools.
They need a new tool.
In a lot of cases what you're going to find if you do the analysis with ATT&CK is you've misconfigured a server.
Or you've forgotten about the fact that this guy had admin rights and he left the company two years ago.
You know, stupid stuff like that that has nothing to do with any firewall or intrusion device.
It's just a lack of rigor, or laziness, or stupidity, or all three with how you set up your equipment on your network.
So if you can see that you're having, all of a sudden, this long gone administrator is all over your place, well, that's odd.
That guy's no longer here.
Why are we seeing logins from 13 different servers.
You can correlate events like that a lot easier once you have this framework that gives you a little bit more rigor in your analysis.
Interesting point.
And it starts to raise the question, what's the cost to an organization?
If you're following some of the best practices that you should be already in terms of config, and managing identities, and what have you.
And if you're able to use some of the open source tools as well that you've been talking about, and you're documenting things well, a lot of what might harm you as an organization, you can deal with at a pretty low cost.
How low cost can I use the MITRE ATT&CK Framework within my organization to make myself a little bit more secure?
Well, all the tools that I mentioned were for free.
You can download them and install them in a couple of hours to a day or so.
So the actual capital cost to acquire this stuff is pretty minimal.
But if you've got a really sloppy implementation of Active Directory that doesn't reflect the reality or your company, or it reflects the reality years ago when it was first setup, it doesn't matter what you're going to do.
You're going to have a sloppy, bad actor directory implementation that actors can leverage.
And you can spend an infinite amount of money and still not fix the fact that you're [INAUDIBLE] implementation isn't working.
I'm sure, Travis, you've got a few things to say on this question.
Yeah.
I do actually.
Yeah.
This is great discussion.
So lots of things that come to mind.
I mean, first off, you're right.
There are three things.
Like simply just following good security hygiene in terms of keeping things patched, using the least privileged, using two factor authentication and multi-factor where you can, and especially around administrator accounts and broad access accounts.
All these things, they go really a long way to being able to prevent a lot of the bad things the happen in environments.
And just making sure, like David pointed out, maybe test against your own infrastructure sometimes.
And make sure things are still configured properly.
Because maybe they were configured right a few months ago.
But then there was this project, and somebody had to open something up, and they forgot about it, left it open.
This stuff happens.
This is just part of being in an organization doing security, or doing IT.
But in terms of actually using the ATT&CK Framework, as David also pointed out, there's open source tools that you can use to help test your own environment.
But it's not rocket science as far as tracking that stuff.
If you just want to use a spreadsheet that has all the different columns laid out like the ATT&CK Framework, and kind of what's being done in different areas, and things that you now you have gaps in as part of ongoing efforts that you want to engage in to try to clean things up, that's one way to do it.
Another thing you can do with the ATT&CK Framework is, so let's say you're in an enterprise that you've got heavy investment in tools and stuff.
I think the default situation for most enterprises is, you go buy a tool.
You put it in place.
You're like, yay.
And then you're afraid to pull it out assume it's doing something.
But you don't really want to turn it off and be the guy that turned it off, and then it would have detected the breach that happened a month later, right?
But what you can do with the ATT&CK Framework is you can start to assess your tools and figure out what areas does this give me coverage in?
Do I already have tools that give me essentially the same coverage?
So I'm sort of doubling down on this.
But I have other areas where I have gaps.
And figure out what the best tool is.
Maybe drop some tools, use the freed up resources to fill in gaps where you don't have coverage.
That's a great point, Travis.
And we've heard from a lot of organizations who were doing just that.
And on the question of what do you need to implement an attack based approach, I'd say that we talked to organizations of all sizes who were using it.
Sometimes there's just one dedicated analyst on a team who starts going through the techniques, and just figuring out how you can start implementing them in your environment.
So it's free.
It's open for anyone to use.
So you don't need a huge SOC.
Some people have that, and they're very successful in using ATT&CK as a common language to communicate.
But even a couple people, I think, can just start going through ATT&CK.
I've heard from teams who every week, one of their analysts presents on a new ATT&CK technique.
And they talk about how they might detect and mitigate that.
So I think a low barrier for entry, right?
Anyone, even a small team, can use it.
So one of the points I did want to return to that's come up a couple of times is around using attack to determine the confidence level that you have across different techniques, and across different tactics as well.
And wondering where you would suggest an organization starts with that, because when you think about being able to define what your confidence level is, it'll help you to prioritize, in some organizations' case, a very limited budget, and be able to decide, OK, where am I going to put things this year?
Where am I going to direct my resources?
So from determining that confidence level, what are some of the best ways that can do that, and, again, maybe some additional tools that you've seen there? We've talked about a lot of the things you can use to kind of do the testing of what you can detect.
I mentioned the data sources that are on each technique that you can use as a way to jump start what you might be able to detect.
I would say, just start going through one by one, and thinking about, what do I have in my environment that could already detect this?
And then there are a lot of really low barrier for entry things, like the Atomic red team.
You can just choose the tests that you would want to run on specific techniques.
So we also have something coming up pretty soon, a spinoff effort called ATT&CK based evaluations, where the team's going to be evaluating a bunch of different EDR products for what ATT&CK techniques they can detect out of some that we've seen APT3 do.
So those results will be published publicly in the fall.
So that's another way that folks could look at what certain tools are able to detect out of attack.
Well, that's really cool.
So you can kind of see where some of the gaps may be, or just some of the functionality and what it's going to address across ATT&CK.
Is that something that you're going to do certifications around?
Yeah.
We think of this as kind of an articulation of what the tools can do.
So we just announced, I think yesterday actually.
The lead on this effort, my colleague Frank Duff, announced that there are eight vendors participating.
So we're going to look at each of those tools, step through on the APT3 adversary emulation scenario, and then articulate, hey, we ran this technique.
How did the tool respond?
Not making a judgment about the type of detection, whether it was good or bad, but saying, hey, here's what the tool could do and what it could detect or not.
So I'm excited about that.
And those results will be public, openly available in fall.
One of the ways that I learned how to use ATT&CK was I picked two different scenarios, one where I understood how the malware was working, and one where I really didn't.
And so when I saw how ATT&CK worked with the particular technique that I knew, I could understand it better.
And then I could start learning how to use it to teach myself about the things that I knew nothing about.
So that's a good way to sort of bridge your knowledge, because nobody is an expert in everything.
And it's depressing when you look at the whole matrix, cause there is a lot there.
But you just take it cell by cell, as Katie said.
Just knock off one of them at a time.
And so I get the what, and I get some of the who.
And I get a little bit of the where.
How does an organization start to think about the when?
Because you just have no idea when given attacks might occur.
Is it just, you're always vigilant, always prepared?
Or how do I deal with the when aspect?
Yeah.
So that's the big unknown, right?
I think the key is making sure you have kind of that defense in depth so that you would detect adversaries at a bunch of different points.
One thing from that threat intel side, I think David already mentioned Unit 42's adversary playbooks.
One thing I like is that they're mapping group and malware techniques and behaviors to different attack techniques.
And they're doing that based on time.
So last year this group focused on these techniques.
This year, this group is focusing on different techniques.
And that's one way that using threat intel.
You can kind of track over time how the adversaries have changed, and what they're using most recently, which gives you the best chance of finding them, I would say.
What are some of the other areas, some of the other features that I might be able to expect as an organization moving forward?
Yeah.
So the next couple months are pretty busy for the attack team.
I think in the September time frame we should have a new website coming out.
All the MediaWiki fans will be really distressed about this, but it'll be a lot easier to use, a nicer graphic interface, as well as a STIX TAXII based website, which we think will make it easier for people to pull information in a structured way.
Other things we're looking at, and based on community feedback, we know that there are some gaps.
So we're looking at how we could introduce new techniques or new content to detect impact or effect type techniques, things like ransomware behavior, destruction of data, things like that.
We're also looking at-- pretty exciting-- opening up the governance structure of ATT&CK.
In the next year or so, we'll be announcing information about how we're going to be pushing this towards the community with the idea that we don't just want MITRE to maintain this, but we want to have a community committee deciding on the future of ATT&CK and what gets incorporated.
So you can look for some exciting news on that in the next few months.
A lot going on.
I think MITRE has done a really excellent job putting this together.
I mean, yeah, they can add more categories.
They've got several hundred already.
Sure.
Pile on some more.
I think the important thing is widening the ecosystem.
I like the fact that they're trying to get the governance aspect down, because it was basically a couple people's pet project up until relatively recently.
It's great that these other security vendors are recognizing that this is a great way to look at things.
Prior to this, all we had was a CVE number, which was kind of useless to really organize our thoughts and understand what's going on.
So I think the more standardization and the more rigor that we can apply to understanding how attackers think is all great [INAUDIBLE].
Yeah.
So Travis, one of the questions that comes to mind is that, especially when we start to go outside of the purview of the security analysts, security pro, and we go into say the world of the developer, or maybe even executive or what have you, it strikes me that, on the one hand, we can try and educate individuals to know more about tactics, and understand what the techniques are, and really get inside the minds of the adversary in some respects.
But on the other side of the equation is automation, and trying to root out a lot of the problems before they become issues.
And when I think about the amount that we're asking certain individuals to do, in particular the developer, as security winds up becoming more a part of what they need to do, do you find that automation may be equally, if not more important than education?
Or would you say, no, no.
I'm always going to start with trying to make them smarter, and then we'll go to the automation piece?
I think education is a requirement.
You have to understand sort of how these things are happening underlying things.
So when there's a problem with automation, because there inevitably would be at some point, you still have this underlying understanding on what's happening so that you could fall back on maybe some other ideas until you get the automation working again, whatever the situation is.
But I think that, talking in specifics around the ATT&CK Framework, I'm a big fan of using sort of education and automation together, iterating through different techniques over and over again within your own environment so that you can see what visibility do you have into those.
If you make a tweak, if you go in and set auditing on this registry key, and it's now logging certain things, are you now able to see this technique attempting to be escalated, or whatever the situation is, and just continuing?
So that's kind of a blend of being able to use automation with the understanding that comes from education together to try to improve defenses.
One of the points I want to make about automation, and why companies like Uber and Netflix are developing these tools now that are useful for other practitioners is that these are very intensive digital businesses that are constantly changing their environment.
They're upgrading their software every other minute it seems.
And if you have to try to rely on manual discreet methods to test that, to see if those apps are still secure or if they've introduced new vulnerabilities, you'll drive yourself crazy.
You have to have some kind of automated thing to be able to check and balance your development team, otherwise they're going to go crazy, and your organization is going to be wide open.
So for those businesses that aren't as intensively digital, they haven't quite gotten yet the message that this is going to have to be necessary.
All good points.
And we've come a long way in a very short period of time, unpacking the massiveness of the MITRE ATT&CK Framework.
There is a lot in there, and a lot of useful information, a knowledge base, as Katie would indicate, for your organization to be able to use to be able to understand how the adversary might come after your company so that you can be prepared.
Let's look at some final actions that each of you have for organizations to take away this week.
David, starting with you, what do you have for organizations to take away this week?
I start with the MITRE web page and the blog.
Katie has done some excellent job blogging there, as well as some of our other colleagues.
See if you can just pick one or two things up from there that you've always wanted to know something about a favorite or infamous piece of malware, or a particular method.
And just learn what you can about it from that.
And then see if that intrigues you, and you get motivated to want to really do more with one of the tools that use ATT&CK.
And is the best way for listeners to get a hold of you through S-T-R-O-M, Strom.com? or is there somewhere else that people should go look for you?
Could also email me David@Strom.com as well.
My Twitter is @DStrom.
Perfect.
And any conferences you're going to be speaking at?
I know you write prolifically.
So Google your name and you're going to be coming up with all sorts of great articles.
But any conferences you're going to be speaking at coming up?
I'm not going to be speaking.
But I will be next month at the RSA Net Witness Archer Conference in Nashville.
Travis Farral, what actions do you have for organizations to take away this week?
I really whole heartedly agree with what now David suggested.
Just get in and start looking through the framework, and understand some of the different techniques that are listed there.
Some of them, you'll probably notice, look like stuff that people would do inside the environment, like mapping a network drive, and those type of things.
But understanding that this activity could sometimes represent activity that's happening from an adversary as well, especially when you see other bits of techniques being used in conjunction with that on the same host, or in the same environment, and things like that.
One other thing that sort of jumps out as well is that the different elements of visibility that are required to be able to detect these things that happen inside the environment, it becomes, to me, obvious very quickly that you really need to have good visibility into the endpoint at some point to be able to even know that a lot of this stuff is happening.
But just familiarizing yourself with the framework, understanding like what types of things, and what types of logs and visibility that you need to be able to detect that I think is a great place to understand how this applies to the defenses you have in your own environment.
Yeah.
We could spend an entire show on visibility.
And how can listeners reach you, and anything that you've got coming up that people might want to attend or read?
Yeah.
I'm pretty easy to get a hold of.
I'm just Travis@anomali.com.
That's Anomali with an I.
I'm @Mivyx on Twitter, M-I-V-Y-X.
I will be speaking in Singapore next week at the FS-ISAC AP Summit there.
I've got a number of other things coming up.
Most notably, though, we have our own threat intelligence conference coming up in the DC area in September.
It's called Anomali Detect.
Just do a search for that and find us online.
Perfect.
Thanks so much for that.
And Katie Nickels, what actions do you have for organizations to take away this week?
I think David and Travis covered the key one.
Check out our website, attack.mitre.org.
Tons of resources up there.
David mentioned our blog posts.
So I should mention David's article that he wrote for CSO Online I believe a few months ago.
Great way to get started.
I'd also encourage everyone to check us out on Twitter, or @mitreattack.
And we always retweet and comment on different things people are doing in the community with ATT&CK.
Which there's an essential knowledge base that you can look at, and that's awesome.
But where ATT&CK's power is is in all of the amazing use cases the community is bringing to it.
So we retweet those all the time on Twitter if you check us out there.
And then my personal Twitter is @LiketheCoins.
So you can reach me there on the MITRE ATT&CK Twitter.
Or email us at attack@mitre.org.
Especially once you've looked at the framework and the knowledge base, if you see something missing, reach out to us.
If you have questions, we're always happy to talk.
And I'll be at Hacker Summer Camp in Vegas beginning of August.
So I'm speaking with my colleague, John Wonder, [INAUDIBLE] Las Vegas about ATT&CK.
So if anyone will be in Vegas that week, please reach out.
And I'd be happy to chat with anyone.
Well, there you have it.
Threat Actions This Week for July, the 12th, 2018.
I'm David Senf.
See you again next week.
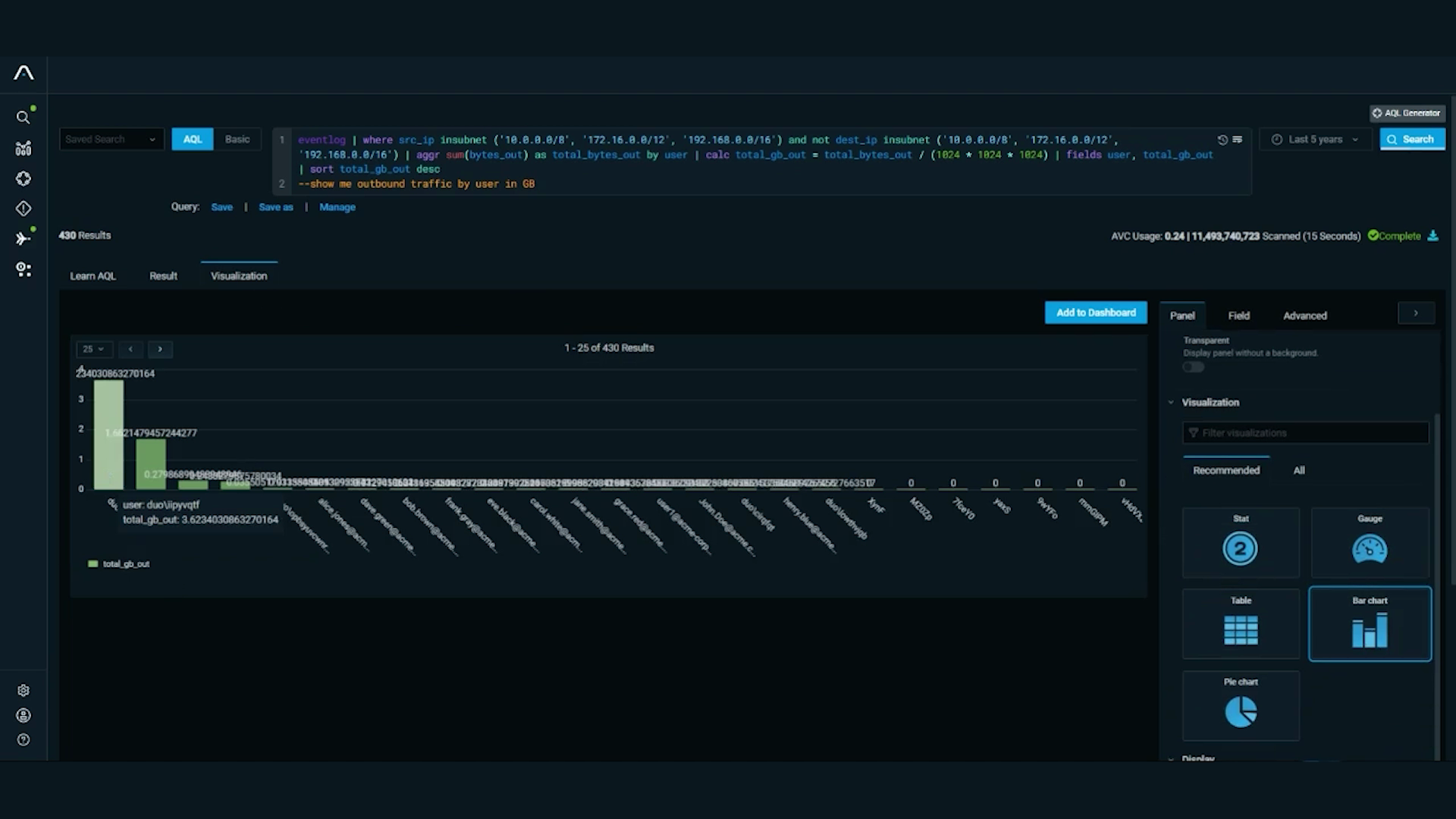
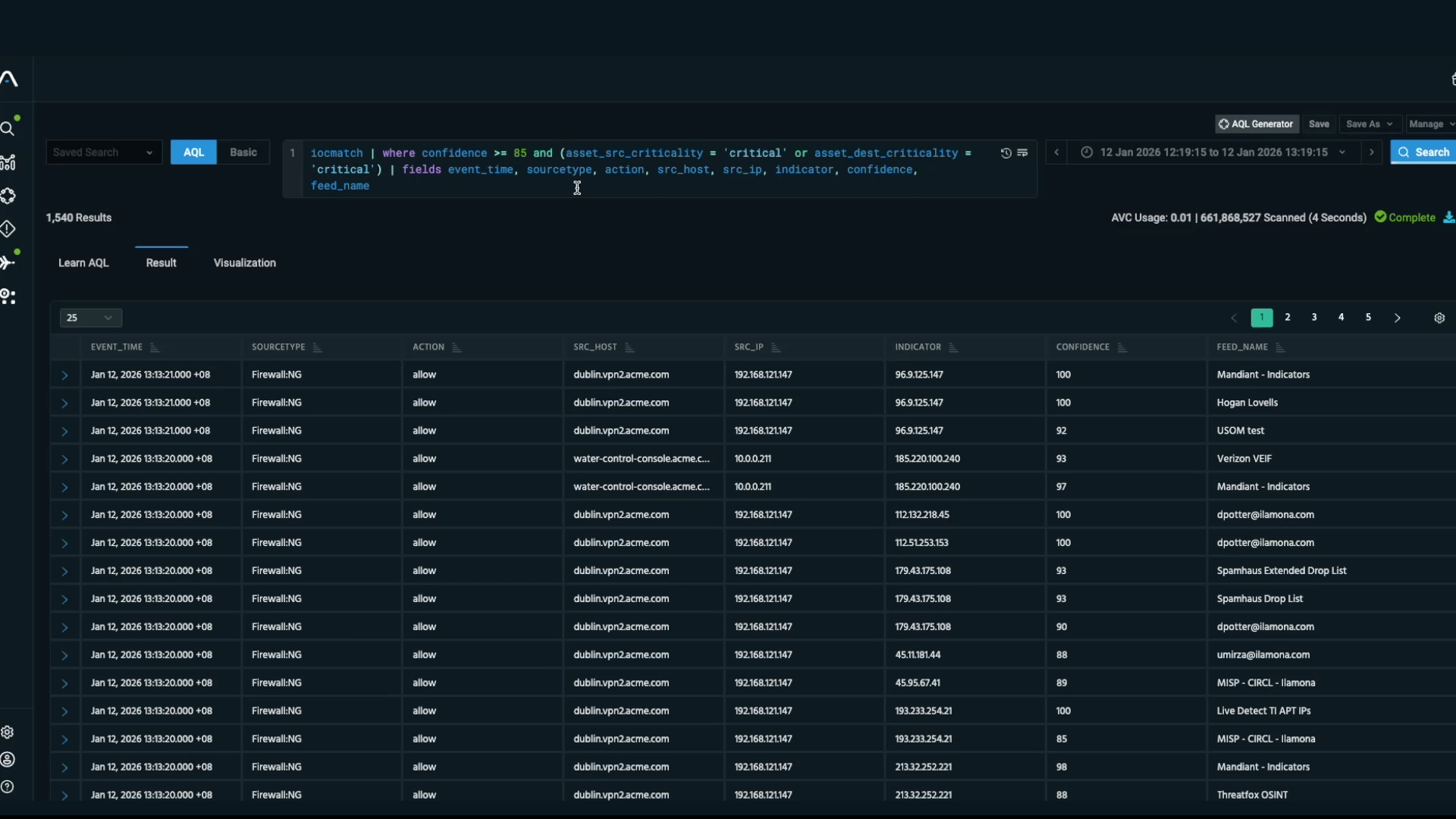
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.