Shadow Talk: Anomali’s AJ Nash on Building Threat Intel Teams, The Chief Intelligence Officer, and Methods for Cultivating Your Cyber Threat Intelligence Strategy
RICK: Hello, everybody.
Welcome to another special edition of Shadow Talk, Digital Shadows' threat intelligence podcast.
I'm excited.
We have a trio, a trifecta, three of us today.
We're joined with our special guest which I'm very excited to have on the program, AJ Nash from Anomali-- Senior Director of Cyber Intelligence Strategy.
Welcome to Shadow Talk.
AJ NASH: Thanks, Rick.
It's great to be here.
I really appreciate it.
It's going to be a good opportunity.
I'm really looking forward to talking with you and Sean.
RICK: Yeah.
And then of course, we have Sean, as well, who is now our new host of our biweekly US-based Shadow Talk, as we shuffle back and forth between our friends across the pond.
So this should be a really, really-- Listen, if you want to hear an intel talk-- Sometimes we have talks that maybe aren't as intel-focused, but today's will definitely be intel-focused, and you've got three career intel professionals-- in the private sector and public sector, military as well.
So this should be a really, really good one.
AJ, where we always like to start off-- your Marvel superhero or super villain, your choice, but what's your origin story?
AJ NASH: Yeah, that's a good question.
Oh boy-- Superhero or super villain?
That really is subjective, isn't it?
Yeah my background, my origin story-- military, originally.
So I went into the military a little big late, so I started off doing [INAUDIBLE] but I did a little bit of sales before I went in, so I worked for my dad, sold cars and some stuff, so I knew a little business background before I went in.
But military is really when it started.
I came in, thought I was going to be a cop, and I was going to go to law school.
That was the plan, but I ended up doing intelligence work.
And that led me to a career as a linguist, which I wasn't a very good one.
So I became an intel analyst.
RICK: What language?
What language?
AJ NASH: Serbian and Croatian, at the time, was kind of a big deal.
The Balkans was a big deal at the time, but I wasn't very good at it, if I'm going to be very honest.
And we have several good linguists, so when I first got on station at Fort Meade, I was working associate at NSA, and we had a lot of good linguists, and we had a shortage of analysts.
And it was something that really appealed to me.
So I actually worked in the analysis shop, and because I had a linguist background, I was able to do a lot of good work on missions we were doing, but from an analyst perspective.
So that actually filled the gap that we knew we had to, but didn't necessarily know how we were going to fill, which started again, a theme of my entire career, I think-- filling gaps that people knew existed, but didn't know what to do.
So I worked in the intel shop, and I was an analyst and reporter.
And so I did a lot of stuff.
I started with the Balkans, I was doing a lot of different regions.
If you can name a hot spot, I probably spent some time working in it.
Then some counter-terrorism work [INAUDIBLE] [AUDIO OUT] for a while, which is all really interesting stuff.
And then moved into countering threats in cyberspace when I was in the private sector, actually.
So I medically retired, did about nine and change in the Air Force, and then moving to the contracting side.
And ended up in cyber by mistake, as a lot of people do.
I was doing intel work.
Originally, I was in counter ID stuff, and I got recruited into a position that was cyber, and I knew nothing about it.
But what they needed-- they were talking about math, science.
To be honest, halfway through the interview, I literally interrupted the guy interviewing, and said, I think I'm in the wrong room, because everything you're talking about, I know nothing about.
This isn't what I do at all.
So it was a big company, and I thought maybe they just put me in the wrong interview room.
But it wasn't.
What they needed-- They had all these folks that did math and science and operations research, et cetera, and the idea was they wanted to build this program to help with intel analysis, but they needed some intel analysts with appropriate background to be the Guinea pig-- test what the project was going to look like.
Would it be applicable?
Would it be useful?
And so really very, very lucky to be on that contract now, because that was what became what was known as intelligence preparation battlespace, IPB, [AUDIO OUT] environment, [INAUDIBLE]-- RICK: AJ, AJ-- first of all, you did something very unique.
You actually defined the acronym before you used it, which seems to be something that those of us coming from the military background fail to do, because we love to talk about IPB and PIRs and every other acronym out there.
So kudos to you for doing that.
This isn't your first rodeo.
AJ NASH: I do a fair lot of speaking, I did grow up doing a lot of the alphabet soup stuff, and seeing glazed eyes when I described the product, [INAUDIBLE].
But what we were doing was a cyber equivalent, so cyber intelligence brought about preparation of the environment-- CIPE-- was this giant [INAUDIBLE]..
And so I was one of the initial cadre on that.
As it turns out, we wrote the book for it.
Now, nobody remembers CIPE anymore, but everybody knows Kill Chain, and CIPE actually existed before Kill Chain-- it was the forerunner.
So this contract that I accidentally ended up on was a group of people trying to develop an idea of how do we manage the process of adversaries in cyber and get in the middle of that process?
In the traditional military world and in kinetic violence in war, intelligence preparation of the environment is about knowing where everything is, right?
Understand the environments, so you can figure out your war fighting.
I want to take on a city, there's three bridges in the city, I'm going to take two of them out, everybody was on third bridge, [AUDIO OUT] one.
Gruesome, but that's how it works.
You can't do that in cyber.
You can't take out a node to solve the problem, because there's 12,000 nodes.
So the idea was focus on the process instead, and if we can map out the adversary process, and if it seems to be consistent, then we can figure out where in the process we want to knock out [AUDIO OUT] and stop the process.
So everybody knows Kill Chain now.
That's where it advanced to, later on.
I was lucky enough to be at the beginning, and was initial, helped me write the book and teach classes, on what became Kill Chain.
Also-- it's happenstance-- I worked at a time with some really smart folks, I happened to be sitting in the room-- I deserve no credit other than I was there-- sitting in a room while the Dynamo was invented, which was another, how do we solve a problem, how do we communicate this intelligence about cyber to leaders who aren't really that technical, don't understand what we're talking about?
How do we come up with a model that works?
And I was in a room, and there was a lot of people talking, smarter people than myself developed it.
It was not me.
RICK: Was Sergio in this conversation?
AJ NASH: You know, I'll be honest with you, Sergio was probably there.
It's Andy that I actually know and remember there, but Sergio was also probably there.
There were several people I just didn't know, to be honest.
Andy I knew, a little bit.
So I watched that all get developed, and then those guys went and wrote a book on it, wrote a paper, and built a company, did some good things.
So it's like my Forrest Gump moment-- I was there when Kill Chain was invented, I was there when Dynamo was invented.
You know, Gumpian, but again, I didn't do a ton there, necessarily.
So that led me into cyber, and then I did government, obviously, there, and several contracts and worked in Cyber Command at NSA, et cetera.
And then private sector was also, kind of, a fluke.
A friend of mine convinced me to get on LinkedIn.
I had no social media, I had [INAUDIBLE] decades, cleared, et cetera.
And I got recruited through LinkedIn into the private sector.
So that led me toward the path I am on now, basically.
So I worked at a bank, I worked with Symantec-- large cybersecurity company-- and now of course, I work at Anomali.
And my role in the last several years has been primarily building intel programs, talking about building intel programs, helping people build and mature their programs.
It's really just bringing everything-- you guys have the same background-- everything we learned in the government space about what is proper intel, what are the processes, what are the standards and tradecraft, et cetera, and just applying it.
I'm not inventing anything new, I'm not writing new interesting things.
Most of the time, most what we're doing is just applying things, and just trying to drag the private sector forward into where we need them to be.
I have seen a lot of success over the last 5+ years, but there's a long way to go as you guys know.
RICK: Yeah, what are-- On that one, what are a couple of things that you think work in the private sector?
Because there are a lot from the public sector that does not work in the private sector, but when it comes to building intel programs, what are some things that work for companies that aren't real mature in that area?
AJ NASH: Yeah, it's a good question.
I think the biggest thing-- biggest obstacles, and therefore the things that end up working-- is do you hire people that-- First of all, any background in intel always helps.
I think what's frustrating is, people hire folks who are incident responders, and they become head of intel.
Those are just totally different things.
There's nothing wrong with that.
That person might be brilliant at what they do, but they haven't the mindset for intel.
What ends up working is either hiring somebody who has an intel background in the start up building program.
Probably somebody who spent a little time in the private sector, so it's not a culture shock, or the event you're going to hire somebody with no intel background which can work if they're very open minded and they want to learn, and they understand this is taking on something different.
This is a pivot in your career.
It's not applying everything you know.
There's training to be had, and you can build it forward.
So I've seen organizations do that.
If they're willing to understand that this is different.
This is not what you've been doing before, and take that into account as they start rolling out their programs, I think I've seen some folks be very successful.
Organizations that don't gather that-- they just apply the same technical skills and background that they've been applying for incident response and SOC analysis, and just apply it- I find they met a lot more trouble, generally speaking.
RICK: How have you found on staffing-- We had-- Jeff Stone was our previous guest podcast a couple weeks ago, and he's the editor at CyberScoop, so we talked about journalism and parallels with CTI, there.
When it's come to building blocks of a team-- people is where I would start versus the technology.
Obviously technology's important, but the people-- what do you see work and not work when it comes to the staffing of the people?
AJ NASH: Good question.
So we covered the leader a little bit, right?
And I admit that I'm very biased.
I believe you build a program by hiring somebody with an intel background.
I've been pretty adamant about that for years.
I know some people don't like hearing it.
Generally it's people who didn't spend any time in the intelligence community don't like hearing it.
I'm a believer in that, though.
I think it is hard to catch up.
If you hire somebody whose got 5, 10, space, knows the intel inside and out, understands analytic tradecraft and standards, et cetera, they come from a really good foundation, you can learn all those things, but it's hard to catch up.
But I do believe you start there.
But then what you build for the team, there's no one way to get this right, but I'm a big believer in diversity and not just as a country, we're all talking about diversity now.
But from an intel standpoint, there's value in beyond just the standard that people talk about.
If you hire five people that have the exact same background, you get groupthink.
RICK: Groupthink, yep, 100%.
AJ NASH: --great.
You hire five brilliant intel people who've done nothing but counter-terrorism for 20 years, you're still going to get groupthink.
It's still not the best way to go.
So I believe you need a mix.
I think you have to have some folks who are very technical, especially in this work, and some that probably aren't.
I'm not particularly technical.
We want to have both of those-- there's a technical aspect to what we do.
There's also a political science aspect to what we do.
So I think it helps to have that-- different backgrounds, ages, cultures, genders all matter, because everything comes with a different point of view.
You mentioned journalism.
I've talked to folks about hiring people with journalistic background.
Intelligence-- one of the big pieces of what we do-- intelligence is about communication.
So if you hire a team that's highly technical but none of them can write, you got real problems.
You're not going to be able to communicate that very well.
It helps if somebody knows how to tell the story.
So I often build teams-- and even currently we have-- as I talk to people about, I want researchers who are highly technical, as smart as we can make them, give them freedom to go chase things and do cool stuff.
If they can't write sentences, I don't care.
If they write in bullets and throw it over the wall, that's totally fine, if that's what's comfortable for them, and generally this is not all it's about.
And then on the other side, I need people who can build those puzzles, give me all the pieces, and they can make this story, and make it make sense.
They have to have enough technical knowledge that they understand what they're reading, [INAUDIBLE]..
And they pull out the other end of the story, and then those two sides work together to make sure that the story that was captured is the story that was created to begin with.
Now, there are exceptions.
I know people who can do end-to-end, from reverse engineering all the way to writing papers, and it's kind of brilliant.
But I've seen too many companies try to hire these people, and that's the only thing they want-- these job ratios, that are ridiculously hard to fill, because they want these unicorns.
And there's nine of them in the world-- RICK: Oh my god, so true.
So true.
AJ NASH: Yeah.
And again, it makes sense if you have the right leader to begin with, they get that.
So you just build a team that works, and then I always tell my folks, like, I explain to them as we're building out the team, this is the roles I see, but understand these are not boxes, right?
So the idea is that you get to be doing the thing you're most comfortable with and best at, and you can live in what your passion is, but if you do all of it, do all of it.
There's no requirement to stay in a box.
If you're a researcher who likes to do your own writing, do an end-to-end product, go ahead.
But if you are that researcher who just does bullets and moves on, build all your bullets, you're going to build all your intel together, and hand it over to an analyst reporter-type, let them build the puzzle, right, because they're the ones who imposed [AUDIO OUT] and let them do there piece, right?
So I think that's worked out really well, from what I've seen for myself in the past and for some other teams.
Again, how big you get, where you're going, who you serve, broad backgrounds are always really helpful especially in financial, so you do run into some folks who have some fine background, [AUDIO OUT],, that kind of thing, which can be useful.
But the hardest thing I've seen is organizations who do one of two things.
The one I already mentioned, which is they hire people with no intel background.
And they got that incident responder they hire, and that person hires five more incident responders-- they build an incident response team, essentially.
And they fail as an intel team, even though they might be good at what they normally do.
The other side is-- and this one people talk about less-- is somebody who comes in and hires massive resumes that are all government.
And so you've got five or six of these-- FBI, Secret Service, NSA, CIA, wow, massive resumes-- none of them understand the private sector, none of them understand business, they don't understand the culture sh0ck that goes with that.
They can be very, very rigid, even, so they can be in a position where they offend others around them.
If you're going to be an intel org inside of a big company, you've also got to build relationships, right?
You can't come in and just stomp around like a bull in a China shop.
And I've seen that happen too, and they look amazing on paper, and, wow, they've built this amazing team, but they've just pissed everybody off, essentially.
And they can't get things done, and intel is a business of communication and service.
So you have to be able to build those relationships-- RICK: That's a good quote.
"Intel is a business of communication and service." Did I get it right?
AJ NASH: Yip, yip.
And that's-- To me, those are things you really have to focus on, so you also want to make sure you find people that can communicate.
Not everybody on the team has to.
I get people on my team that never want to be on camera, never want to be behind a microphone, probably never want to talk to anybody outside of their house, and that's perfectly fine.
You're brilliant, you do what you do.
But you do want to have people who also have the ability to bridge those gaps and to build those relationships, because when you start building an intel team, that's the hardest part, is getting out there, letting people know what we're trying to accomplish.
And how we can make your job easier.
My job is to help the other folks in the organization by building an intel team-- it's to make the other jobs easier.
We're not telling you how to do your job, we're not telling you we're smarter than you.
We have the opportunity and the time and the access to look at things you don't have the opportunity to see, and to bring it back to you, so you can make your job better and easier.
Our job is to make other people rock stars.
RICK: That's a good quote, too.
SEAN: Yeah, definitely, AJ NASH: You can take all of these.
RICK: Good, good soundbites.
AJ NASH: I talk a lot, so you get a lot of quotes out of me that way.
RICK: What about something else with-- especially going back to the unicorn bit, right?
There's not enough of them, and even if-- You don't have the salary to pay for-- maybe you can get one, right?
That's it.
What's your guidance for people listening to Shadow Talk today, about training and leveling the skill sets up, because as we all know, some of the training opportunities out there-- quite expensive.
You know, SANS is not-- I mean, I co-chair the SANS CTI Summit, so I'm definitely aligned with SANS, there, but SANS is not cheap.
So how do you level up the skill sets on these CTI teams that you're building out?
AJ NASH: That's a really good question, and we have the same challenges, right?
So, you know, ideally I try to hire a couple folks who can mentor, which helps.
If you can hire a couple people who you'll-- you may even overpay them, to be honest.
But you try to get people as you're building out a team that you know have the really strong skill sets in there as you need.
So I built a team out long ago where we were doing it from scratch, and I was able to hire three people that I knew were all really experts in what they did.
We brought somebody who was an expert researcher, top to bottom one of the best I've worked with, brought in somebody who is an expert analyst and reporter-type, and we brought another guy who was really amazing at briefing.
He was also good at analysis reporting, but he was also a great briefer.
So I knew as we were going to build the team, all of them would be able to mentor other people and teach them to do some-- train the trainer group.
Now admittedly, I also believe in investing in the training.
You talked about SANS.
If somebody isn't coming out of the government space with the skill set-- and of course that's another way to save money, as again, if you're hiring people out of the government, especially if you're hiring people out of military by the way, because they're not even necessarily expensive in some cases-- they come with all that training, so you do speed that up.
You've just to work on the cultural shift.
But I'll pony up the money for SANS, for the GCTI course.
Most of the organizations I've worked with and helped set up, or set up myself, you build these career tracks, and to me it's a requirement-- to get past a certain level, a mid-level-- you either have to have x number of years of experience in the government, or you have to have GCTI.
There's a point where you just have to be able to document that you understand these fundamentals.
And then there's other courses you can look at.
There's other vendors that do things.
Who we got?
Treadstone 71 does some stuff, and there's Cybermerc, I think in Australia, does some stuff.
There's a few orgs out there where you can set up cost-effective classes, because you can do it by volume where you can set up a class for your entire team, or you can do it online and self-paced, so there's some there.
I'm a big believer in that.
And then again, like I said, you do the internal, the mentoring, and the train the trainer, and the brown bags, and teaching people, and there's books they can read.
You can-- I believe if you can do it, set up time on work time to let them get better at these things.
That's another thing-- organizations don't want to do that a lot.
It's, I hired you, I need all the hours out of you, and you get better on your own time if you want to advance.
And I get that, there's a place for that.
But if you can also build it in workflow, people are more likely to do better and get better, and you can still get the work done.
I think if anything, what we've learned through COVID is, listen, if you work 12 or 14 hours in an office, you're not getting any more work done than if you stay home and work five or six, maybe, sometimes.
I know people don't work nine on every day.
I'm certain of it.
I don't count people's hours.
I don't work eight or nine every day.
Some days I work 14, sometimes I work six, but the work gets done, right, and it's the same thing with this.
So I think we can build time and make it fun, and my people have work groups together and study group together and work through some of these books and get smarter.
So there's a lot of different ways to do it.
But the key thing is first, you have to be dedicated to wanting to.
Do you want to grow people?
Do you want to make them smarter?
Are you willing to invest?
RICK: If you want to keep them, you better.
Otherwise-- The worst thing to do is to have someone on your team, a colleague that's been there a couple of years, knows the organization, understands the business critically-- going back to your point earlier about setting people up to be successful in these departments that are intel customers of us-- and then to lose them because you didn't do career pathing, mentoring, and development, and I also think a lot of people will just think, oh, It's all the external stuff at the expense of not doing the internal training, because you have a lot of folks-- Like, just this week, we had some internal training, and we had one of our analysts that's heavily focused on the extortion scene do a training session for some of the analysts and the broader company that's not as focused on the extortion side and leveling it up.
So I think that's a nice opportunity you should take advantage of, because if you don't have for SANS, at least have a path and take some of that great knowledge that we have internally on our various teams.
AJ NASH: Yeah, absolutely.
It does come down to a bit of a culture of investing.
And you pointed it out, people will leave.
I know a lot of companies that think, well, we don't want to put too much money into these folks, because they're going to leave us, and we will invest in them and they'll leave.
And I understand the risk of that, and I'm not a CFO, and I don't handle those things.
So I get some of those pieces are real, but I look at it the opposite way.
If you don't invest, then they're going to leave.
You know, I think especially now as we're seeing-- this, kind of, dips into my passion.
I have a master's in organizational leadership with a focus on servant leadership, so people really are a passion for me.
And trying to figure out how to satisfy them, how to feed people's passions and feed their desires and what they want to do in life.
And if you do that, they're more likely to stay and be happy and give you more productivity.
And this is part of that, is taking the time to say, where do you want to go?
Where do you want to be?
How does it fit where we're going?
How can I feed that?
How can we get you what you need?
And recognizing that that's a good investment.
Yeah, there's risk, sure.
Somebody you're going invest in will leave.
It happens.
But you're taking good care of people, you have a-- RICK: You'll keep them longer.
You'll keep them longer than you would have otherwise.
I always tell-- AJ NASH: Especially now.
RICK: Oh yeah, especially now.
AJ NASH: Especially now.
I mean, if you talk about the millennials, and Gen Y-- and whatever labels you want to put on who's coming up, right-- the younger generations care more about this.
They all know the days of are long over.
Loyalty to companies is, kind of, a dead concept, because companies weren't loyal to people for the most part.
They care more about, hey what's my life going to be like?
Am I doing something I care about, do I believe in my company and the culture of the company?
And are we doing good work?
Are we ruining the world or making the world a better place?
Do they care about me, personally?
And I believe in all of those things, so it works out nicely, but there's a whole generation of people in management leadership who don't, and there's a clash there and they're going to age out, thankfully.
Because that's what's important now is, take care of the people, and they'll take care of the mission almost always.
Yeah, the outliers won't-- RICK: That's another good one, by the way.
Take care of the people that take care of the mission.
AJ NASH: Yeah, well the challenge is some folks-- I hate to put in an age sense, but a different generation of leadership looks at it as they take the outliers, the problem.
Well, we spent a lot of money on this person then they left, and they ignore the fact that that's really the outlier.
You're going to have some of those, but most people-- you take the time and energy, you put in, you invest in them, and you show that you actually care about them personally and professionally-- they don't want to leave.
You know, they care more about that, and they won't leave for five grand or ten grand or a few percentage points.
They'll stay because they know the value, right?
Yeah, if you're paying them terribly, they're going to leave, because the gap's enough so that they can buy them off.
But that's also an investment that saved us.
I read years ago-- and I know the numbers have probably changed-- but years ago, the cost to replace somebody just in terms of recruiting and all that stuff, it was like five to ten grand.
And companies don't think about that part either.
You throw a couple of thousand in the training on this person-- it's actually still a much better investment than the risk of losing them.
RICK: Oh, yeah.
AJ NASH: It keeps continuity, it builds better teams, there's just so many good reasons to do it.
But you always have to fight for it.
And I get it.
I don't want to bag on CFOs and the people who count the money.
They have a hard job, and they're the ones who keep us all in business, because if they don't do it, we all go broke.
But it's hard to sell, and you have to find that balance of why there's value here, what it does for us-- it makes us better, and it makes us stable, and it makes us safer, and we build better teams this way.
And you build a reputation as well as a place people want to work.
People want to work for people or with people that care about them.
So I think those all come into play, and you build that reputation.
And then, yeah, you don't have a problem with recruiting, because there's always somebody throwing resumes saying, hey man, I heard-- RICK: Especially in this market.
AJ NASH: And it's so competitive.
I mean, you and I-- all of us, I'm sure-- know somebody you'd never work with again.
You wouldn't recommend somebody else work with or for them.
You won't go out and spread their name around, but if their name comes up, I'd be like, yeah, I don't know man.
I don't think it's a place I'd want to go, right?
We all know those.
And we all know the opposite places that you'd just love to work for or with, and if opportunities come up, you recommend people all the time, oh, you should work with those guys, they're great.
That spreads.
It's a small industry.
And if you build that reputation one way or the other, it's going to stick with you.
And it'll stick with you if you change companies-- you hire the wrong person as a manager at a new company or a leader, because you didn't know what their reputation was-- that's also a big mistake.
So going back to that question of how you build teams, if you're going to hire somebody to start building a team, hire a leader, do a lot of background.
And make sure you know.
Intel people know each other.
And also don't hire that hot resume, the guy who says, well I can't tell you what I did.
It's all classified, it's all spooky-- red flag, huge red flag.
The guy who has to do that, or gals-- run away from them.
It's bull.
There's always a way to explain something about what they did.
The intel community is so small, like, you can find-- I'm sure any one of us could probably in six degrees find almost anybody.
You'll find out.
People have these resumes that say they did great things, and you dig in and find out, no they watched other people do great things.
They were just in the office.
Or they were, I led a team, I managed this, and you find out, well, that was a lieutenant.
Literally, you-- RICK: You cleaned-- You cleaned latrines in that unit.
You didn't do any actual work.
AJ NASH: You didn't do the actual work.
RICK: One of the-- You mentioned leader, and I know Sean is interested in a blog that you did recently, but it's related to the leader of the intel org, so I don't know-- Sean, you want to transition to that topic?
SEAN: Yeah, so I think one of the things that, kind of, got the wheels turning was the whole idea of a Chief Intelligence Officer.
It's really funny, because I had almost like a visceral reaction to this blog in a lot of ways.
Like, if you were basically my English teacher at a boarding school, I would have stood on my desk and said, oh captain, my captain.
Once I got about halfway through, just seeing the roles and responsibilities of a CINO-- it's just a really interesting concept, and for the people out there that have not had a chance to dive into the blog, what would we, I guess, expect seeing a chief intelligence officer, somewhere?
AJ NASH: Yeah, so first of all, thanks.
I mean, there are not better compliments than hearing that you responded that way to it, and you liked it.
Especially somebody with the background.
You get intel, right?
I'll be really honest, it's something I've been kicking around in my head for a couple of years and hadn't really gotten on to writing.
And then-- US Cybersecurity Magazine is where that was originally published.
So they asked me if I'd write an article-- I'd written for them before-- and I said, yeah, and I didn't really tell them what I was going to write.
So I had an idea, and I kind of put that together, and they liked it a lot thankfully and published it, and apparently other people have to.
So for those that haven't read it, the basic concept is, I've been working down this path-- Years ago, CTI is still a really common [AUDIO OUT] cyber threat intelligence.
I hate it.
I'm not a fan of that term at all.
I've written articles in the past that said, CTI is dead.
Threat is a subset of intelligence, so I don't think CTI in itself is a good term, so I moved to cyber intelligence a few years back.
And much to the chagrin of some others.
I know there's people who disagree mostly just because CTI is the term people understand, and they want to stick with something comfortable.
But I moved to cyber intelligence, and even then I think we're not doing ourselves a service.
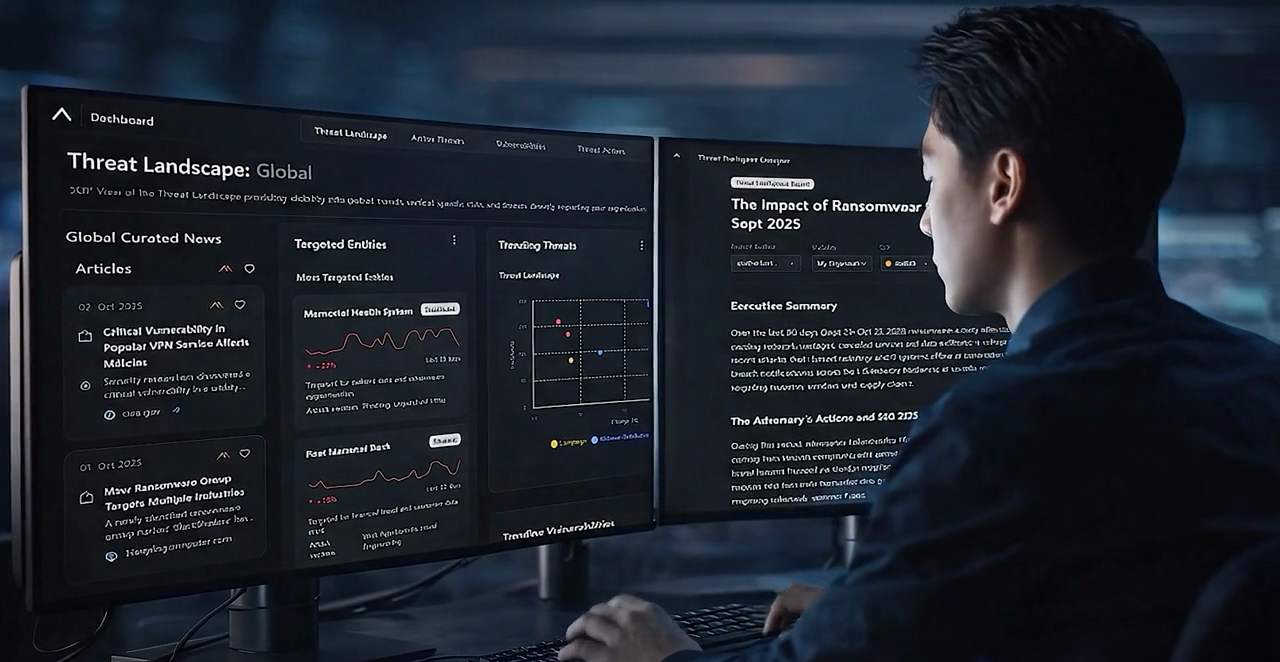
So right now, we build these CTI programs inside the SOC buried underneath the SOC Manager, the director of defensive cyber operations, somebody like that.
And so they're just going to be focused-- almost entirely-- on the tactical, technical needs of the SOC, which is a real under-utilisation of what it takes to build these teams and in terms of the talent and in terms of the technology and the access as an all expense.
So I've been arguing that that should be moved up.
I think those programs-- cyber intelligence programs-- should probably report to the CISO, and we've started to see some moves in that area.
You see things like fusion centers, right, where you start seeing that concept and that tends to report higher up.
And you just get a wider aperture to do the work.
So now the same accesses and talent and time and money on technology and all those things we spent money on-- it costs a few million dollars to build a good team-- instead of just focused on the SOC and defensive operations, or even the SOC and blue and red team and a couple of things in there, you start elevating up, and now you're doing everything that the CISO cares about, and that gets you into government's risk and compliance, and some of these other things.
And maybe they're a CSO and not just a CISO, so you get physical security, insider threat, and executive protection.
But the truth is, even now, as that's starting to pick up, that's not what I believe it needs to be.
I think you need to have a chief intelligence officer.
I really think we need to move to the point where we have somebody in the C-suite which-- parallel to the rest of the C-suite-- reports to the CEO and is, sort of, a consiglieri.
So there's a chart that went along with the article I wrote-- and I'm sure we can get it to folks, post it on your blog or someplace-- that, sort of, lays out how I thought this worked, which is you've got an operational side, which is your CISO on that side a couple of the other C-Suiters, and then you've got a consulting side, which is your consiglieri-- which is the term I keep using-- for the CEO which is, sort of, your chief legal officer and your chief intelligence officer.
And now you've really reach that enterprise level-- where you're getting the full value of everything you're buying, because now you're also getting into business intelligence risk.
You're talking about what the entire enterprise really needs.
And again, you're using the exact same resources.
You're spending the same money.
It may cost you a little bit more at that level, but my belief is you do that, and then you reach into all these other organizations.
And again, it's a service.
We're raising it up, so that we're able to do this at an executive level.
I think of it, sort of, like the government space.
You've got the Office of the Director of National Intelligence, and then, of course, the Director of National Intelligence runs it.
That was invented not all that long ago, historically, either.
And that was the single person that reported to the president and brought all the intelligence together and explained it to the president, right?
Back to the unification of everything.
And we can do that in our private sector spaces, and then you have the ability to reach out to all of these organizations throughout the entire enterprise.
It gets you to things like mergers and acquisitions that a lot of folks don't do much of anything with intelligence to.
Physical security, again, we talk about some insider, but M&A is, kind of, a big one people talk about.
HR is another one which can lead into some insider pieces.
You know, M&A for most companies is, does this fit with our portfolio?
Is their bottom line good?
Do they have any legal responsibility we need to worry about?
They don't take into account things like, have they been compromised before?
What are the risks?
How's their security posture set up?
RICK: You're going to inherit-- you're going to inherit their adversaries, right?
SEAN: Absolutely.
AJ NASH: You inherit all their problems-- their third parties, who are the hiring, where are those people sitting?
What risks have they taken on we haven't paid attention to?
SEAN: Shadow IT is a huge one, too.
AJ NASH: Exactly.
And there's nobody covering that, right now.
There's no way to cover that.
So organizations buy this, and then they get it in, they're going, wow, we've inherited a lot of problems.
And that becomes the CISO's problem, right?
Oh, good luck.
Stitch all these networks together, fix all these problems, that's yours, now.
And it just gets handed off for someone else to take care of when it could have been prevented, or maybe it could have changed the cost, or you bought that company for a lot less-- you're able to negotiate a different cost, because you know you have work to do to get it right.
There's a lot that can be done there that just isn't.
And you can get into business intelligence, and you really bring everything together into that intel picture to help the CEO and the entire E-staff, and even the board make better strategic decisions.
So I'm a big believer of this.
Like I said, I've been pushing it for a while.
Slowly but surely.
I'm sure some might consider this self-serving.
I work in the intel space, and I'm trying to move intel from being buried under the defensive cyber operations guy in the SOC, all the way up to be a C level.
Well, that's a great way to move your career forward.
But this isn't about me.
There's a couple of folks out there who are brilliant, who I think will be the first CINOs when we finally get there.
It won't be me.
But I think we're going to see large enterprise will get there.
We've been mimicking the government space as we're building intel in the private sector.
So why not get to the logical conclusion, which is eventually getting it to the executive level-- reporting to the highest levels to the right people and a holistic look.
And frankly, as much as I don't like seeing them, things like the Colonial Pipeline attack and SolarWinds-- that moves us closer to this.
Every time those things happen, and we see these big events, and what we end up seeing is organizations who are supposedly mature and spending money and doing the right things still don't completely know what they're doing.
And sometimes the leadership has very little idea, depending on who it is.
And it just tells us we have a lot more work to do on this holistic approach.
And if you want to do what intel's designed to do, which is prevent things-- you know, it's great to report on what happened, it's great to talk about the after effects, and cut down on your response time, and remediation, but that's all post attack.
Prevention requires effort and investment, but it requires a bigger picture.
Are you going to look at the China five year plan and take the time to figure out, hey, China's five year plan that is really big on health care and credit and insurance.
If we're in those industries, we need to take a look how that affects us, as China runs that five year plan like a playbook right down the line on how they handle their cyber operations.
I think most companies don't pay any attention to it.
They don't realize it, because if you try to tell them, we want to do this, they go, no, no, no, I need to know how to fix the problem in my SOC, today.
I need to work on patch prioritization, I need to work on this really technical stuff.
And as long as we keep intel teams buried, that's what will happen.
The teaming that works in the SOC, for the defensive cyber operations director, or senior director, whatever, the SOC manager-- to me-- and the intel people will get this reference better than non-intel people-- that's like taking NSA and putting it under Central Command.
For those who don't know the military or the government, Centcom handles the Middle East.
If you took NSA and put it under that, all you're going to get is intel about the Middle East.
You'll never see what's going on in China and Europe and whatever area you want to look at-- Africa-- you'll never get it.
You'll just get nothing but the Middle East.
It's a waste.
So yeah, I'm a big I'm a big proponent of this.
I'm thrilled to hear that you were that excited about it, because whenever you write something that's, kind of, you want to think it's new or novel at some level, you don't know how it's going to be received.
I put it out there hoping people would think the way I did and fearing that people would cast me off on an island someplace, and I'd be thought of as a guy who has no idea what he's talking about, it would be the last time-- SEAN: A pariah in the space.
AJ NASH: And there's always that possibility, right?
This guy is-- this guy's loony.
He's nuts, he has no idea what he's doing.
Don't listen to that quack anymore, and suddenly I don't have a future of having these discussions.
But to me, it's the natural evolution of things.
I just want to push it forward and make it-- RICK: How do you one-- especially as a CISO myself, I'm like, oh man, I don't want a competing person-- just kidding-- there, but if you want to-- For those that are out there listening and are like, no way this would happen in our org.
I mean, you mentioned for the big FS, very likely to be-- if anywhere was going to do this, it would be there.
But let's-- If you peel it back past the CINO component to it, your part about getting beyond just the SOC and the IOC land is really, really critical.
If our listeners are trying to take the first step of many steps to get more strategic, to work with the other lines of business M&A, human resources, physical security, what are a couple of practical things that you would recommend folks do to move in that direction?
AJ NASH: Yeah, so it's a good question, right?
The CINO-- this is the pinnacle, right?
This is the ultimate we want to get to it, but it's miles and miles and miles away from a lot of folks.
So what you're asking is the right question, which is what do we do today?
Right?
How do we start building there?
The old story about, how do you eat an elephant?
It's one bite at a time.
So the first bites here, to me, are intel requirements.
So this is where a lot of organizations really struggle, I think.
If you think about the intel cycle-- and we talk about standards all the time, right-- to me, if anyone's listening as never heard "the intel cycle", Google it, please.
It's a really easy graphic.
It's very important in my opinion, and you can build almost your entire program off of just the intel cycle-- RICK: Sean has that tattoo, actually.
SEAN: Yeah.
Yeah.
AJ NASH: Where?
Do I want to know?
[LAUGHS] Don't show me.
SEAN: After a couple of beers.
RICK: After-- Yeah.
[AUDIO OUT] AJ NASH: To me, it's planning and direction, right?
That's the first step of the intel cycle.
And what we see is organizations don't have intel and then they say, we're going to build intel, and they jump right to collection.
They jump right to buying stuff.
And believe me, there's never an endless-- there's an endless supply of vendors happy to take your money and sell you all sorts of stuff whether you're ready for it.
But to me, it starts with planning and direction, and that starts with identifying your stakeholders, and then doing your intel requirements-- understanding what they're going to be.
So the best example-- when I was at the bank, we went through this, and it went really well-- was the bank had seven lines of business.
Think it was seven, might be eight, but I think it was seven.
So each one had their own information security officer, and the company had never really done intel requirements up until this whole exercise.
So as I said before, intel is about communication, right?
It's a service business.
So I just set up a meeting with all the ISOs, and just sat down.
And you don't walk into the room and say, hey, what are your intel requirements?
I promise you, the answer is going to be, I don't know.
That's your job.
And you've already started off on the wrong foot.
They don't think you know what you're doing.
That's a bad place to go.
Better to sit down and just say, hey, I just want to talk about what you guys do.
Like, just fill me in.
I've got credit cards and I've got mortgages and I've got car payments.
I get the mechanics of business.
But talk to me about what you do.
What's your job, right?
And people love to talk about their jobs.
So they'll be happy to tell you everything to do, and some more often than others will tell you how brilliant they are.
But the key pieces I want to figure out are, what are your business processes?
What are the core processes that you have to be able to complete to survive, what technologies do you depend on to go with those, what data are you protecting, what's the crown jewels that if you lose, you're done, and what technology is tied to that?
Talk to me about your communication, what technology is used to communicate with one another?
Talk about how you consume things, right now.
Are you a reader, are you somebody who listens to podcasts on the way to work?
Are you visual, you like pictures and graphics, et cetera.
So if you're able to do that with whoever you identify as your stakeholders and you bring all those together, then I believe you come back after you-- You can take that, and you should be able to craft some kind of intelligence requirements.
And for organizations, start from scratch.
Be simple.
This does have to be these giant books like we had in the milt- don't bother with that.
Like, you need a plan.
Very simple.
At the bank I said, we're going to have three tiers.
Don't do granular, hey, this is our top requirement, second part changes too much, too hard to do.
But I said, well the tier one, tier two, tier three-- each one has no more than five questions in it.
That's it.
That'll be our total for starting, right?
And so we took all these groups.
And there's a lot of overlap.
Like, groups use the same stuff, so it's easy to say what was more or less important just by volume.
And so we have these tiers of requirements, and we go back, and follow up and say, hey, based on our discussion, this is what it looks like-- These are questions that you would like to get answers to that would help you.
It'll make your job easier, make you more successful.
Have I captured that correctly?
Have more communication, and make sure we get acceptance on it.
Then you can start figuring out answers.
Then we can figure out, what vendor should we talk to, what things should we buy, what technology do we need to be more successful?
And you've already built a relationship, because later on you're going to start sending intel to these people.
If You haven't done this first, it's just going to come out of nowhere to them.
And now it's just noise, it's waste.
Even if it's brilliant, it doesn't matter.
They don't know why you're sending it to them.
It's a waste of their time to sit and read it, and then they read a product that doesn't matter to them personally, and they just tune you out, because you just missed the mark on that one.
Whereas if you go through this process, you make sure the right intel is delivered to the right people, because different orgs have different needs.
You can follow up and do feedback and make sure we're doing it properly.
If they're not getting what they need, we can change the intel and change the requirements, but now it's a team.
Now we're in it together.
We built the relationship-- they know why I'm sending them stuff.
And so when we send it they should want to read it.
And we built it in a structure that matters to them.
There was a really smart guy.
He runs the intel program at Capital One now.
I work with him.
It's coincidental we work in the same place.
And he said something I thought was really insightful.
Intel doesn't matter if nobody reads it.
Which sounds simple, but he made a great point about developing products that also are appealing to your eyes, to your senses, making sure you know what people are looking for.
They do really pretty products-- really beautiful stuff.
Good intel, but it's also something that's good to read.
It's not just a bunch of words on paper over and over again.
So make sure you know what they're looking for.
But again, it's starts with the requirements-- stakeholder engagement, understanding who your stakeholders are, build your requirements, get acceptance on those requirements, and then you have a much better chance of getting people to want to read what you're writing and understand why you're doing it.
And then the other thing I would say goes with that is the third piece, is building out a product catalog, was something I learned the hard way, frankly.
If you don't have a product catalog, the questions you're going to get almost always are going to be, tell me everything you know about x.
You've told people you're great, you built this program, they think you guys are geniuses and wizards, and now they're going to ask boil the ocean questions.
And they want it in 12 minutes, that's normal.
So what you have to do is go and sit down and say, hey, let's build a menu.
All right?
So this is what is achievable within these time frames.
So this is the menu I use there, it could be different.
But I had flashes and highlights, and we had summaries and reports and studies, that was our five levels.
And we have profiles, which are, kind of, ongoing.
And then you just-- it really is a menu.
The flash is going to be 1 to 2 pages you can have it in zero to four hours, there'll be no editing.
It's going to be tons of caveats.
You can't put a lot of confidence on it, and you've got to forgive me if there's a typo in there, because you wanted it quick.
But we can get back to you.
Highlight is going to be-- I don't know what it was now.
They change because you can set it however you want.
But it was, like, three days, and it was up to four pages, and be able to-- at least it had to have a peer review to it.
The caveat language should be a little stronger.
If you get to a report, they you're talking about the full process, right?
Ten days, multiple peer reviews, analysts review.
Listen, you shouldn't excuse any errors in typing on that one.
If we have a typo, go ahead and rake me over the coals.
We should've done a better job, et cetera, that stuff can go to anybody in the world.
But when we were able to build that out, I knew we were successful when our leadership stopped asking for, tell me everything about x.
And would start saying, hey, I need a flash on this.
I got three hours to a meeting, and I need a Flash on this, I need a highlight on that.
And you can stack them.
All right, I'm going to do a flash, for now, but we'll keep working on it.
We'll get to a highlight, we'll get to a summary, we'll get to a report, whatever your name your stuff, right?
We'll give you a flash, first, to get started.
We'll keep working on it, but you can get iterations as you're going.
And again, when they started asking for questions in our terminology, we knew we'd hit home.
We knew we were on the same page on what they needed and wanted.
Otherwise you're still going to fail.
Even if you have requirements and it's going the right direction, they're going to ask for something, and you're not going to meet the mark.
They're asking for something that's unrealistic, and you're having a hard time figuring out how deep they need it.
Or the opposite happens.
They ask for something, you do boil the ocean.
You're giving this in two days, because your team just worked nonstop, and the boss wanted that so he can answer one question from the board that was going take 30 seconds.
All that time and energy on building this amazing paper that was totally way beyond what they needed.
Or [INTERPOSING VOICES] Oh, yeah, that was a meeting yesterday.
I forgot all about that, don't worry, we don't need that.
RICK: I have a question.
[INTERPOSING VOICES] AJ, that just came recently in a conversation.
What-- what did you do for feedback loop on your intel products?
AJ NASH: Oh God, feedback's hard, man.
So I will say-- I'll caveat by saying I haven't solved this well.
I don't know anybody that has.
The intelligence community hasn't either, so I feel better about it.
My entire career, I doubt I had feedback on more than half a dozen things I wrote.
If I didn't deliver it in person, I never had feedback.
But what I have talked to people about trying to do, at least-- and we've seen some success-- so first of all, again-- communication.
You build these relationships.
You should be able to have a discussion with your stakeholders and say, hey, we've been doing this a little while, I want to sit down and talk to you about what your feeling is.
But from a metric standpoint, what I'd like to do, and I haven't succeeded in doing this to be honest, but every product should have a mechanism for feedback built into it.
Something as simple as three questions with a 0 to 10 scale, right?
Was it timely, was it accurate, was it relevant?
That's a great place to start-- timely, accurate, relevant.
For anybody who's done intel, we all know that that's the major measurement of intelligence, right?
But we want to know what the customer thinks.
If I have a customer who says, oh, this was always timely, but it's never relevant.
It tells me we're good on our timing but our requirements don't match theirs.
Yeah, we didn't think that was accurate.
Well, I really want to dig into that know why.
You guys are great on relevance, but you're always super late.
Well we've got to discuss what we're doing for our timelines, right?
So something as simple as that.
I have talked to organizations, and we had some dreams that haven't come through, yet to be honest, about if you build a dissemination model on a website for instance, you can have that tied to it.
Somebody downloads the product, they read it, and before they close it they're required to answer these questions.
You can build it into surveys, et cetera.
I think those three questions alone, if you can get those three answers on every product, you can build some pretty strong metrics pretty quickly on how you're hitting the mark with folks.
Then beyond that, you've got to do your own digging, unfortunately.
There's still a lot of work to figure out what the real impact was.
So this gets past feedback and actually starts getting into KPIs and ROI, right?
Return on investment and key performance indicators-- to try to keep telling people what the letters mean-- which is the next question that's asked.
Feedback is how do I feel about things, did it help me, and that's great.
It's still somewhat subjective, but eventually somebody in your position, Rick-- CISOs, eventually people who own the budget say, am I spending this money wisely?
Why am I spending this money?
What am I getting?
And that's a tough one, because measurements of intelligence effectiveness are really challenging.
RICK: Not just intelligence, but dare I say, most cybersecurity things-- measuring the ROI on is a challenge.
AJ NASH: Yeah, I mean, if you're doing anything preventative, how do I know what I prevented, because it didn't happen?
You know, it's anecdotal a lot of times.
When I talk to folks about when I worked at Symantec, at one point we had some customers there, and we wrote some intel there-- "we" being the team, I didn't write it, I was just on the team-- but we did some intel and we were able to tell people about BlueKeep which-- some people know what Bluekeep is, some don't, but everybody knows what WannaCry is.
So we had written a product a few months before WannaCry hit.
None of our customers were impacted by WannaCry.
So that's a great anecdote where I can tell people that story and say, listen, if you'd been a customer of ours, how much did you save?
Take a look at the damage done by WannaCry, especially when it first happened, none of our customers were affected by WannaCry, they were all prepared for it and then made the proper changes.
I've got anecdote after anecdote of successes, and those are things I can use with leaders to talk about the value of prevention, because it is hard to measure still, but I also talk about it like banking.
Banks understand the value of intel and security [INAUDIBLE] more than other industries, because I think it's part of their culture.
Banks have been robbed forever.
They've had money, they get robbed.
So the physical security always was there, and they just moved it to cyber.
But banks-- If you walk into any bank-- they've got cameras, and they've got guards, and they've got guns, and they've got all sorts of security, and there's a good chance the bank you walk into has never been robbed even once.
In a cyber world, if you don't get robbed for three years in that environment, they'll be like, why are we spending all this money on security?
We can really cut this budget.
It's all overhead, it's a waste, we should cut all this back.
SEAN: It really is the only place that you get complaints for nothing happening, you know?
Like, you don't call the police department and yell at them because you have gotten broken into or, like, call ADT and be, like, hey, no one's, like, tried to kick in a window, I'm mad at you guys.
Like, security is the only place where that happens, I think.
AJ NASH: You're right, and it's funny you mention it, because I used to talk about my house that way, too right?
I have [AUDIO OUT] ADT, I've got cameras, I've got alarms, I've got a dog.
Nobody's ever robbed my house.
Nobody's ever robbed a house near [AUDIO OUT],, But I always tell people, to me, that's where I consider my security posture.
I travel a lot.
My house is a hard target.
I'm pretty confident it's one of the last on the block that's going to get broken into.
So when you talk about what we do with cyber and prevention and intel, you want to be a hard target, you want to be able to lower your risk-- which meant more risk measurements, and we're working on that-- but you also just have to have an understanding that some of this is an investment that you have to stop thinking about it as things you want to cut as overhead costs.
This is the cost of doing business in an interconnected world.
[INTERPOSING VOICES] SEAN: Well, you know-- maybe to bring it back to your CINO thing, as we wrap up.
Like, elevating intel and those costs to the C-level, right, to help try to communicate these things puts a nice bow-- of course, what we've been talking about for the past-- almost-- hour is very easy to talk about, very difficult to implement.
So I think everybody out there appreciates that.
However, I do think, NJ, in the conversation we've had today, there's been some nice nuggets and suggestions on things that people can practically do with their programs.
For our listeners that want to learn more, we'll put the blog in the show notes for sure, but how can people follow you on the socials?
Do you have anything coming up you'd like to promote?
AJ NASH: Yeah, good question.
So social media-- LinkedIn is probably the best place to find me.
I'm AJ Nash, and I'm with Anomali, I'm not hard to find at all.
I do a fair amount of-- Whatever I do, whether it's a podcast or writing or whatever, it almost always gets republished there, at some point.
It's an easy place to find me.
I'm not on Twitter in the way that you guys talked about or anything.
You know, what do I have coming up?
Let's see.
I've got another couple of pieces for US Cybersecurity Magazine that I need to get written.
Oh, I also-- another thing that might be interesting, SecurityWeek-- I've got a running column in SecurityWeek.
RICK: We'll put that in the show notes, as well.
AJ NASH: Yeah, folks might like that.
But the big thing is if you want to know more, or if you want to talk, just PM me.
Get on LinkedIn, throw me a message.
I'm happy to talk to folks about any of this or anything else.
How do I build programs, how do we work on this stuff?
I am not in sales.
I don't care for your number.
I'm not a commission guy.
You can reach out to me.
I'm not going to turn you over to some guy that's going to sic salespeople on you an try to get money.
I'm happy to just talk.
This is a passion, I like doing it.
And I'm happy to talk to anybody about it.
RICK: Well, we're thrilled that you came and talked to us at Shadow Talk today, about it.
So thanks again for taking the time with us, and then maybe we could do another interview six months, a year from now, something like that.
Or maybe do some joint blog work or something like that together, as we build out the relationship.
AJ NASH: Yeah, I think it'd be great.
I'd love to come back any time.
We should do some joint work.
We should definitely talk about that.
You guys do great work.
Good partners.
And this is just fun.
So anytime you want, man, I'm always happy to do whatever you guys want to do, whether it's talking or doing some joint research, or joint blogs, or whatever it might be, I'm up for all of it.
RICK: Perfect.
Well thanks, everyone, and if you found this interesting, do remember that we do have our weekly episode of Shadow Talk where we go through the top news.
And if I was to imitate my children who love YouTube videos, you know, don't forget to hit, like, subscribe, and hit the notification bell, blah, blah, blah, as YouTube has turned into the main thing that my household apparently likes to-- I do watch the barbecue videos on YouTube, if I'm being honest, myself.
So yeah, if you liked this episode, subscribe to our weekly episode, and we'll talk about the hot things going on.
Today, we recorded our weekly one, and we talked about the new open letter to corporate executives and leadership with respect to ransomware.
So stay tuned for some hot takes on that.
Thanks again, AJ.
Sean, good to have you on as well.
And we'll talk to you.
SEAN: Thanks, AJ.
AJ NASH: Yeah, thanks guys.
Appreciate it.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.