TechStrong TV Interviews Anomali
NARRATOR: This is Digital Anachist.
Hey, everyone.
It's Alan Shimel, back here for our next guest on Tech Strong TV.
And our guest right now is AJ Nash and he's from Anomali.
Hey, AJ.
Welcome to Tech Strong TV.
Hey, Alan.
Thanks for having me.
Happy to be here.
Absolutely.
It's our pleasure.
You know, we were talking off camera a bit, and wow what an interesting background you bring to our show today.
Before we jump in to what's happening with Anamoli and so forth, why don't we give people a little bit of idea who's AJ Nash?
Yeah, sure.
Happy to.
So as you mentioned AJ Nash.
So my position right now is on the senior director of cyber intelligence strategy for Anomali.
As far as my background, I came out of traditional intelligence background.
I got about 18 years in the intelligence community.
I was US Air Force for half that time.
And a contractor for the other half.
I focused in traditional intelligence, counter-terrorism, counterinsurgency, counter trafficking and persons.
I chased war criminals for a couple years, which was fun work.
Mostly worked at the executive level-- doing briefings and writing papers for executive leaders, briefing director NSA, things like that.
I spend most of my time at the agency or at Cyber Command.
So I spent all five of-- the last five years were spent counter threats and cyberspace.
And I moved in the private sector and I've been out here now for about five years.
And primarily my role in the private sector has been working with organizations to build Intel programs, or help them mature the programs they have or in a couple occasions I was involved in building programs myself.
Excellent.
Excellent.
What a great-- what a great background, man.
And thanks for all the-- I'm sure you can tell some real war stories if you were allowed to, but what a great experience.
Very cool stuff.
Yeah, I was thankful to have the opportunity.
Yeah.
You know, we're thankful we have people like you out there doing it.
So well, AJ, you know, transitioning from, you know, sort of an NSA or, you know, Intel background to private sector like this.
You know, you deal with some things that are a little more mundane perhaps, perhaps not, right.
Depending on what we're dealing with.
But we've certainly seen over the last, let's say, five years.
You know, the whole threat Intel industry or cottage-- it was a cottage industry at one point.
You know, under the whole cyber umbrella.
And now, it's become much more mainstream, much bigger, much more accepted and everything.
But yet, still-- I don't know if I want to use the word immature or maybe more art than science still, you know?
Talk to me, you know, what are kind of your impressions of how threat Intel is fitting in, how it's being used, where does it fit within these cyber organizations at most companies, versus the general?
You know, beyond cyber the whole business of sea level and what have you.
Sure.
Yeah, no I think-- I mean, not to insult anybody, but I think a mature probably is the right term.
You know, it's been interesting.
Like I said I've been the private sector now for about five years.
So I have seen a growth and maturity.
We're getting there, but intelligence has been a professional skill set in the government space for decades.
So I think we're a long way from catching up to the professionalization that we've seen in the government space.
You know, in the private sector, I think we are moving forward.
I think organizations have gone from, you know, hey, we need Intel.
Now, they're starting to figure out what is intelligence, right.
And one of the challenges that I work with folks on a lot is separating interesting data and information, and intelligence.
And a lot of my job frankly is I'm not trying to invent new things.
It's about bringing the best of breed from the private sector-- or from the government's space I should say into the private sector.
So things like joint publication 2-0 for instance or Intelligence Committee directives.
You know, bringing doctor from the government space to teach the private sector how to do professionalized intelligence.
So I think that's growing.
There was a lot of folks leaving the government who have this background, who were able to get out and teach people how to do it properly because the challenges that we've seen early on, our organizations are starting to get directives from above, from the board or from the sea sweep programs.
But not really defining what that is.
And a lot of times I think you see organizations that take, you know, a really talented person, say, the head of the IR department.
And, you know, who's due for promotion and now they're the director of intelligence.
And they say, great.
And start trying to build this Intel program, but they hire people like themselves.
I mean, a lot of times they build really just another instant response type program.
Something very granular or something very much about atomic indicators, instead of true intelligence.
And they don't end up succeeding.
The other challenge I think we see a lot of times is organizations that want to invest in intelligence, but they put it the wrong place in the organization.
They build it and put it in a SOC buried under the blue team, something like that.
And they're going to have a hard time with value.
So, you know, I tell people a lot of times, with intelligence the math equation I use is talent times access times time.
So talent being people, obviously.
You need the right people to do the work.
Access means you need to have enough material, the right material.
But then there's always some time factor.
Organizations are going to spend a lot of money on these things, it's a reality.
Talent costs money.
People are hard to get.
Good quality intelligence people, there's a gap there.
Access-- you have tons of vendors willing to sell you a lot of things and you need a pretty broad collection capability.
Much like the intelligence community has 70 agencies, the private sector with a lot of different vendors.
You need to figure out what you need for your specific needs, right.
So when you invest all that money, I don't think it's a great plan to put that buried inside your SOC where it only supports your blue team needs or maybe your red team needs, and maybe purple team, somewhere in that area.
So I'd encourage organizations to look bigger.
Move your Intel organization up.
Have it support your CSO at a minimum, maybe even the C staff.
And you can start having discussions about, you know, the physical security and insider threats, which can also work with HR, right.
You can work in your M&A organization, patch prioritization, obviously, your blue team, your red team, your traditional SOC needs skill.
But now you're getting more value out of intelligence.
You're building more of a strategic approach to intelligence.
So when you spend these hundreds of thousands or possibly millions of dollars, it's easier to get return on investment and be able to document that, especially from a business case.
Yep.
One of the problems that I think we have, and it's not just in the threat Intel space or Intel space, it's in the larger cyber space, which is when we try to go broader beyond the CSO, we don't do a good job of talking their language.
Exactly right.
Yeah, I think one of the things I've been trying to focus on.
And I'll be clear in that I haven't accomplished this yet either.
I think there's two languages when you get into the sort of C-Suite and you get in too the board.
You know, they care about risk and they care about profits.
Those are kind of the two languages I've assessed very often, that there is.
I don't know that anybody yet has been able to measure and marry threat intelligence, or cyber intelligence or intelligence in general with risk.
So to be truthful that one of my projects for this year, is I'm trying to get smarter on risk.
It isn't a background I have a great deal of information on it, compard to the intelligence background.
But I think the solution is going to be how do we measure risk reduction?
How does intelligence measure against that?
And how do you do that in a quantifiable way you can defend, right?
Intelligence right now is still very subjective.
I think a lot of people see it that way.
You know, I've spent a lot of time telling people, you know, you invest in intelligence for the reasons you invest in health insurance or a home security system.
You're not going to necessarily be able to get the ROI measurements you would get out of say a firewall or endpoint protection, where you can do all the bean counting.
This is more about how you set up your risk structure, how you set up your threat structure, you know, how you feel comfortable, right.
But that's not a sustainable way of measuring this.
So I think right now there's a lot of folks, myself included, who are trying to find a way to tie Intel to risk because risk is the language of the board.
And the other piece that goes with that is the business aspect of it.
You know, if we can reduce risk, we can improve profitability, we can improve our brand, you know, things of that nature, So I think ultimately to be successful we've got to get to a point where we can explain to the board why if you spend this much money, there's actually value in doing it.
And right now, that's really, really hard to do.
I mean, most are still looking at it as just straight cost.
And the best argument right now is this is the cost of doing business in an interconnected world.
And then there's a fear driver to that.
You know, you don't want to end up on the list, right.
We all know the list.
There's a lot of large companies on the list that have had major breaches.
It's very easy to look back and say, if you only spent four million on Intel, you could have saved the $90 million cost of the breach.
But long-term, I think we've got to figure out a way to tie this to risk.
And that's one of my pet projects for the year.
And if I'm going to be really honest about it, I'm a little behind frankly.
It's a hard thing to do and I haven't figured it out yet.
It is.
And you're not the first person to bang your head on that wall.
But sooner or later you'll either get a very soft head or you break through the wall.
So I'm not as well versed in, let's say, thread Intel and intelligence.
But I am well versed in trying to convey risk to C-Suites, right, in my past lives.
And I will tell you that even-- there's risk and there's risk, right.
The language of risk they understand is actually very closely tied to profits.
It's very closely tied to revenue, right, because truthfully they don't give a hoot about their reputation unless you can show how their reputation is going to affect their bottom line, right.
And so, going in there and talking to them about whether we should whitelist or blacklist stuff or, you know, why we need better salmon and log or what have you, to lower risk because it's going to give us a is not the risk they know about, right.
The risk to them is really-- it's financial, right.
And everything gets tied to that language of business and-- Yeah, absolutely.
[INTERPOSING VOICES] In cyber, that we talk-- right, right.
But we talk cyber risk, they talk business risk.
Exactly.
And I think that's a really important point, right.
And perhaps I have a benefit of not being remarkably technical because my background is traditional Intel and personalities and geopolitics, and things like that.
I tend not to fall into that category, right.
So I look at reputational risk, business risk.
And that's a key piece right.
The board does not care about the 22% reduction on the SOC.
You know, based on the salmon.
If you put this Intel in and these alerts, they don't care about that.
They're going to tune that out.
They do care about understanding that there's adversaries that are after our industry or our geography and by making these changes, we shrink our footprint, we lower our risk, and the result is going to be x if you are actually compromised.
They do understand the measurements of back and risk.
Once we've been compromised, how bad will things be?
Like the FAIR model, things of that nature.
[INTERPOSING VOICES] FAIR is perfect example.
Exactly.
We need to do is figure out the front end that goes with that.
FAIR does a great job of telling you if you're compromised, how bad is it going to be, how much will it cost you.
Nobody's figured out the front end to say, how do we reduce the possibly of even getting to the FAIR model, how do we keep from being compromised.
And I think that's why we're working very hard is understanding adversaries that have interests in us, what their capabilities are, what the likelihood of their actually showing up our doorstep is.
And then being able to extrapolate and say, if this happens based on past experiences, this is likely to be the damage that'll be caused.
And this is our reputational damage and as a result you want to avoid that problem, right, because if you're a financial institution for instance, people won't invest in you if you get compromised.
Or if you're a-- god forbid, if you're a cyber security organization and you get compromised, it's pretty bad for your business.
So I think that's the case we need to work more on with the executive level.
And like you said, it's hard.
My head isn't soft yet, but certainly working its way there.
I'm trying at this point to reach out to a few folks.
I know they're really, really smart on risk and see how we can partner together and have more discussions on this because I don't think I'm going to tackle it myself this year.
It's just-- it's hard.
It's tough, it's tough.
I will tell you that originally when the rise of the CSO became a thing, right-- because I've been in security 20 years.
That was part of their mission, was to be the translator.
The nexus, right, between the business C-suite and the security SOC and so forth.
You know what AJ?
I realized-- and off camera I have someone I'd like to introduce to, I think can help you with that.
But, um, let's talk a little bit.
You do work for Anomali and we really didn't talk much about what Anamoli does and how it fits into this.
[INTERPOSING VOICES] --for a little bit.
Yeah, that'd be great.
You know, Anamoli-- you know, full confession, I was a customer.
That's how I came to the company, right.
So I mentioned building Intel programs and talent access timer and all this access.
So if you're going to bring all of these pieces together, all these different collection capabilities from all these amazing vendors, it's too much for people to process.
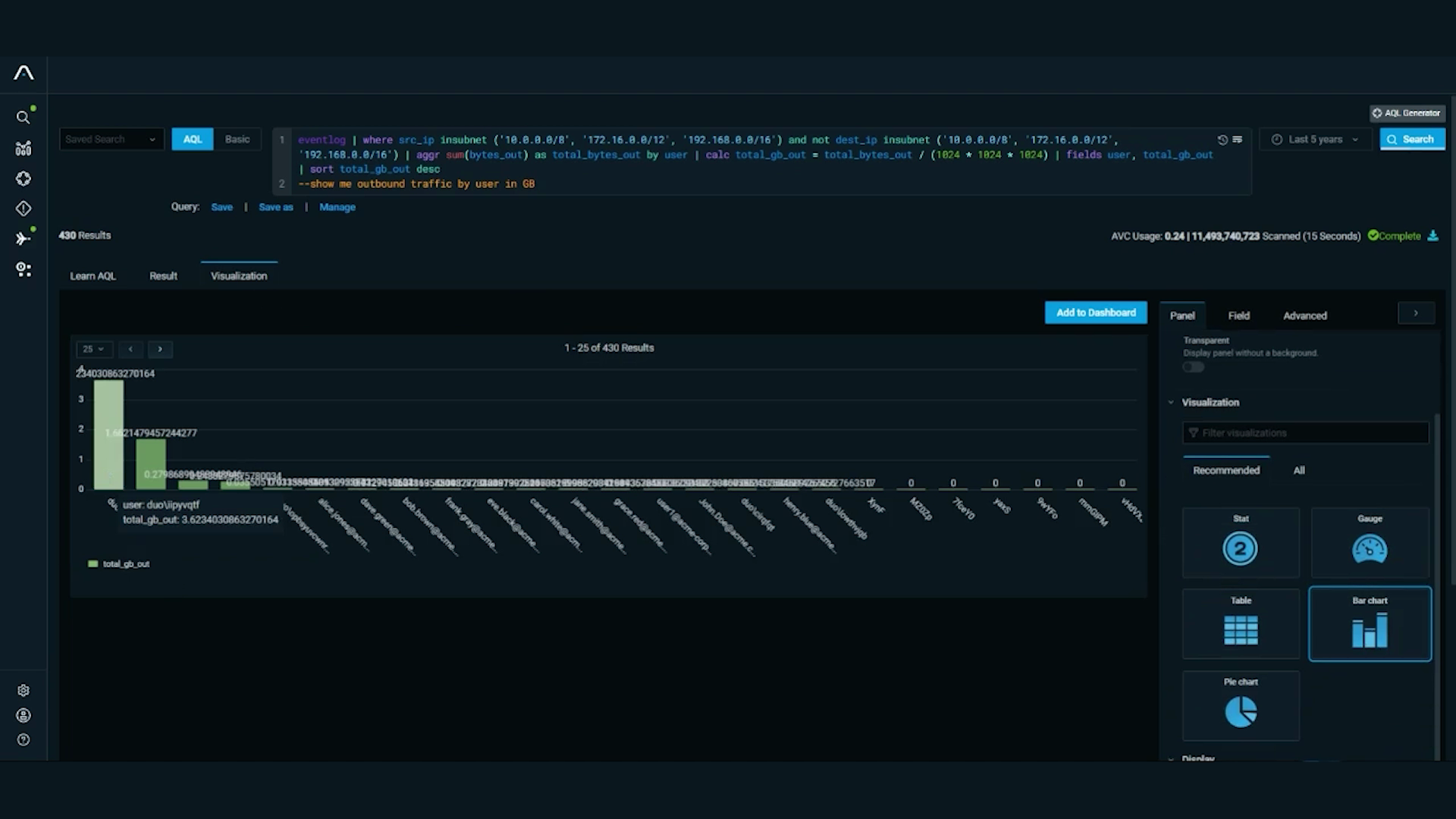
So I was looking for what was known as a threat intelligence platform, which Anamoli, we have one it's called ThreatStream.
And it's the flagship product of the company, right.
So I POCed several different platforms.
And I love choosing Anamoli as the company I went with, right.
So with a threat intelligence platform like ThreatStream, you're able to take all of these various sources of data and information, and in some case intelligence, bring them together with a machine learning algorithm that dedupes these bits of information, that adds context to them, that can add some contents to it.
So, the idea is to give an analyst more opportunity to succeed.
I can't go through millions and millions of articles, right.
So the technology makes it easier for me to work with.
You know, beyond that we also a couple other products in the suite.
We do have Anamoli Lens.
And Lens is a natural language processing tool we have that's really, really cool.
There's a couple of very cool things.
From an analyst standpoint, it makes your analyst smarter or faster.
You know, in simple terms, the ability to be browsing all the different sources we all read on a daily basis and have context brought directly to my screens so I understand.
You know, what is this CVD without having to go back and look for it or who is this adversary because I can't keep track of everything in real time and make sense of that.
And even connect that back to my environment.
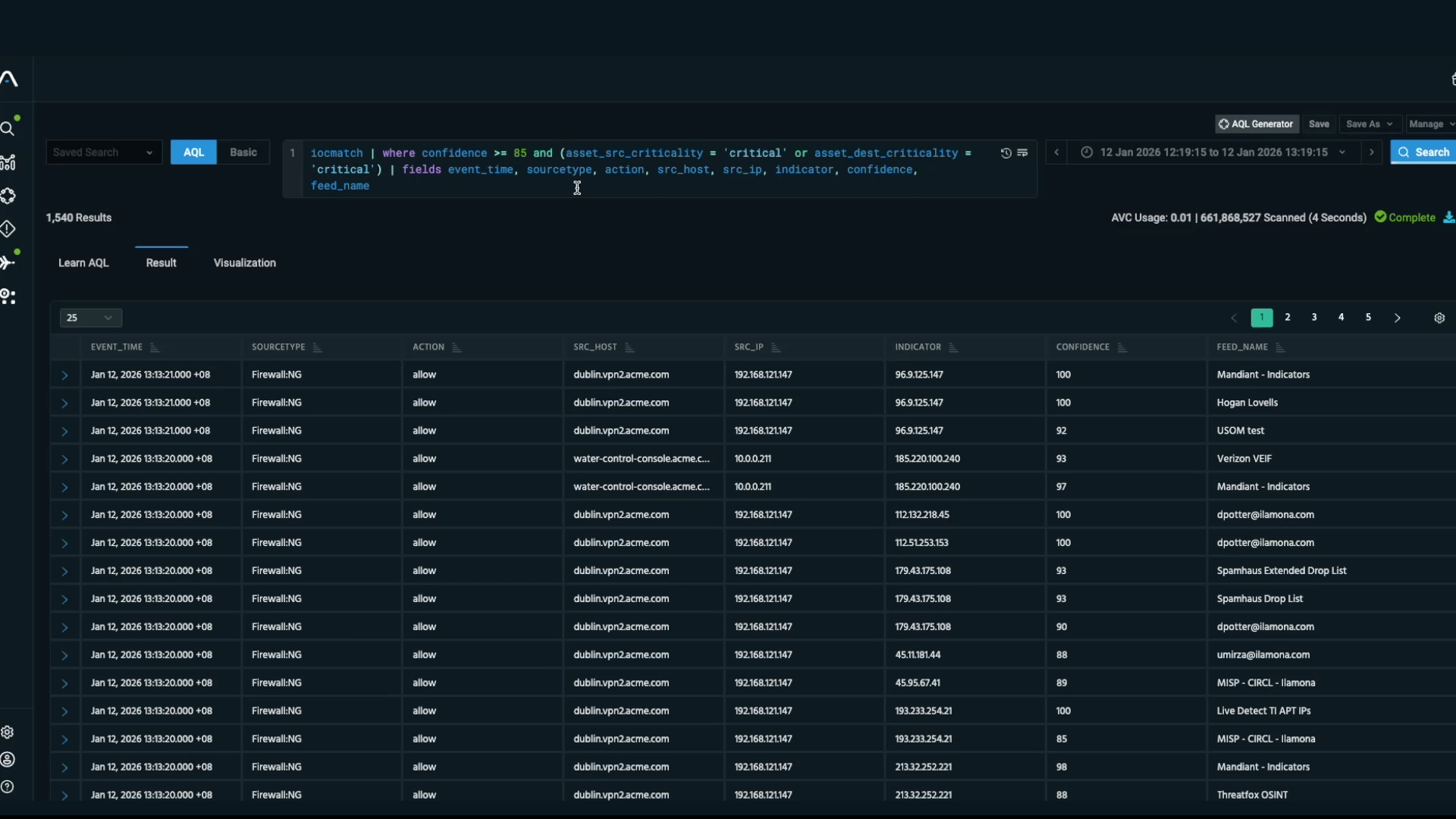
And the third product we have is known as Anamoli Match.
And what Anamoli Match does, is-- I tell people I think it completes the promise of the SIM.
Sim Technologies are incredibly powerful and very used one.
And really needed in most SOCs.
But we've run into some challenges with SIMs.
You know, they're overwhelmed by a lot of the data.
Sometimes they tip over.
If you want to do a retrospective search, you want to get to patient zero during an incident response, in most cases you're not going to make it.
You know, it takes six, eight months of back research to find that.
And most things will tip over if you try to go that far back.
More people end up having to pick and choose what they even run through their SIMs.
A lot of organizations don't even run their-- you know, their email.
Traffic doesn't actually go through the SIM because it's too cumbersome.
And that's where a lot of your problems are going to be.
So we have this platform that actually works with the SIM and does real time matching of intelligence.
So in the real time you can actually get context on all the alerts coming in.
The thousands and thousands of alerts, you know what to prioritize and look for.
But also, in retrospective-- we do a retrospective search for months or years and it takes a milliseconds to get accomplished.
It's because we're only using the metadata.
So what we can do is put people in a position where we can do a really, really quick search on that.
And literally measure milliseconds to seconds and tell you where patient zero was, it was this end point, the state, this time.
Then you can go reach back and pull that full log, you know exactly which one to go pull and look for.
So the instant responses where you have 15 minute calls or hourly calls and the CSO's upset, and everybody's chewing on your neck.
And it's really hard and stressful.
And you're saying, well, we're waiting on the SIM to come back with an answer for us.
We're still trying to find it.
Those first calls-- those first couple of calls are really productive.
So when you put that all together it's a really great platform as a whole.
It's a unified suite of products.
It allows you to work with both the SOC and the Intel analysts, connect all those things together and give you some really solid solutions.
So I'm really excited about it.
I love working with our team and with our customers.
And now, part of my role is-- in the product office, I actually work with our Intel team to help make these products better because we represent sort of our customer base.
So we're bringing that information back in and we're also testing things in advanced to say, would this work in the environment, is this an improvement, is this good enough.
So it's a really exciting time for us.
Very cool.
And Anamoli is A-N-A-M-O-L-I?
That's correct.
Yeah.
.com?
Yeah.
Anamoli.com We're based out of Redwood City.
We're right there with all the tech giants out there.
It's a fun place to be.
It's a really good team.
I'm really excited about it and I'll put a quick plug-in.
You know, as far as our credibility and our CEO is, you know, he founded ArcSight.
So he's the godfather of SIM to begin with.
And then we essentially founded the threat Intel platform space as well.
So a lot of smart people.
A lot people better than myself, obviously.
So I'm just excited to get a chance to work here.
Very cool, man.
So tell truth, do you ever do you ever miss being back in sort of human Intel and government, and that stuff?
Yeah.
You know, it's funny.
It comes and goes.
There's a lot of things about the government space I don't miss.
But every once in a while, I get a little wistful.
You know, true confession.
I just started catching up on the show Jack Ryan.
And I watched only a few episodes of that to go, god-- Season 1 or season 2?
I finished both now.
Thanks to COVID, I'm home.
So I get to binge watch a lot of things.
Yeah, you and me both.
Yeah.
But you know, it brought up some memories and I chatted with some folks I used to work with and-- Yeah, I miss some of the mission.
I miss some of the service, but we are lucky to be in a position where I work with some good people now, the private sector.
And you know, we work with some folks in the government space.
And I still have friends I get to work with and consult with.
So I miss some of the missions certainly occasionally and some of the camaraderie, but you know, there's a time for everything.
We have good people doing that work now.
I'm real confident in the future for us and I'm happy to be doing what I'm doing right now.
Trying to help some other people.
Very cool, man.
Hey, AJ.
Thanks for joining us on the Tech Strong TV.
[INTERPOSING VOICES] Thanks for having me.
Great conversation.
Say hello to all our friends at Anomali Definitely, yeah.
And thanks for having me.
I appreciate it.
Happy to come back anytime, man.
Absolutely.
We'll have you on.
AJ Nash from Anamoli on Tech Strong TV with me here today.
This is Alan Shimel, we're out right now.
We'll be right back with our next guest.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.