The Purpose of a Threat Intelligence Platform (TIP)
A threat intelligence program is all about gathering data and turning it into operational intelligence.
A threat intelligence platform, also known as a TIP, is really about enabling a threat intelligence program.
So what it does is it gathers all the information into one centralized location, allows the analyst to take that information, process it, and make it actionable for the company.
So every organization and enterprise has different environments and different uses of the CTI platform.
Primarily, it is to be that single pane of glass for intelligence.
So you can have different sources from ISACs or security groups, from commercial feeds, from open source feeds.
And I suppose it is taking that workload off having to try and source, and look at different platforms and panels to have it in one view.
A threat intelligence platform is something that you're able to handle the threat intelligence data with.
And it's able to consolidate it and normalize it.
So what it has is you've got all your different threat intelligence sources, and each one speaks through a language about what type of threat it is, how malicious it is, how active it's been, maybe if it's inactive.
But if you can bring that all onto the one platform and map them correctly, you can translate that into a common language.
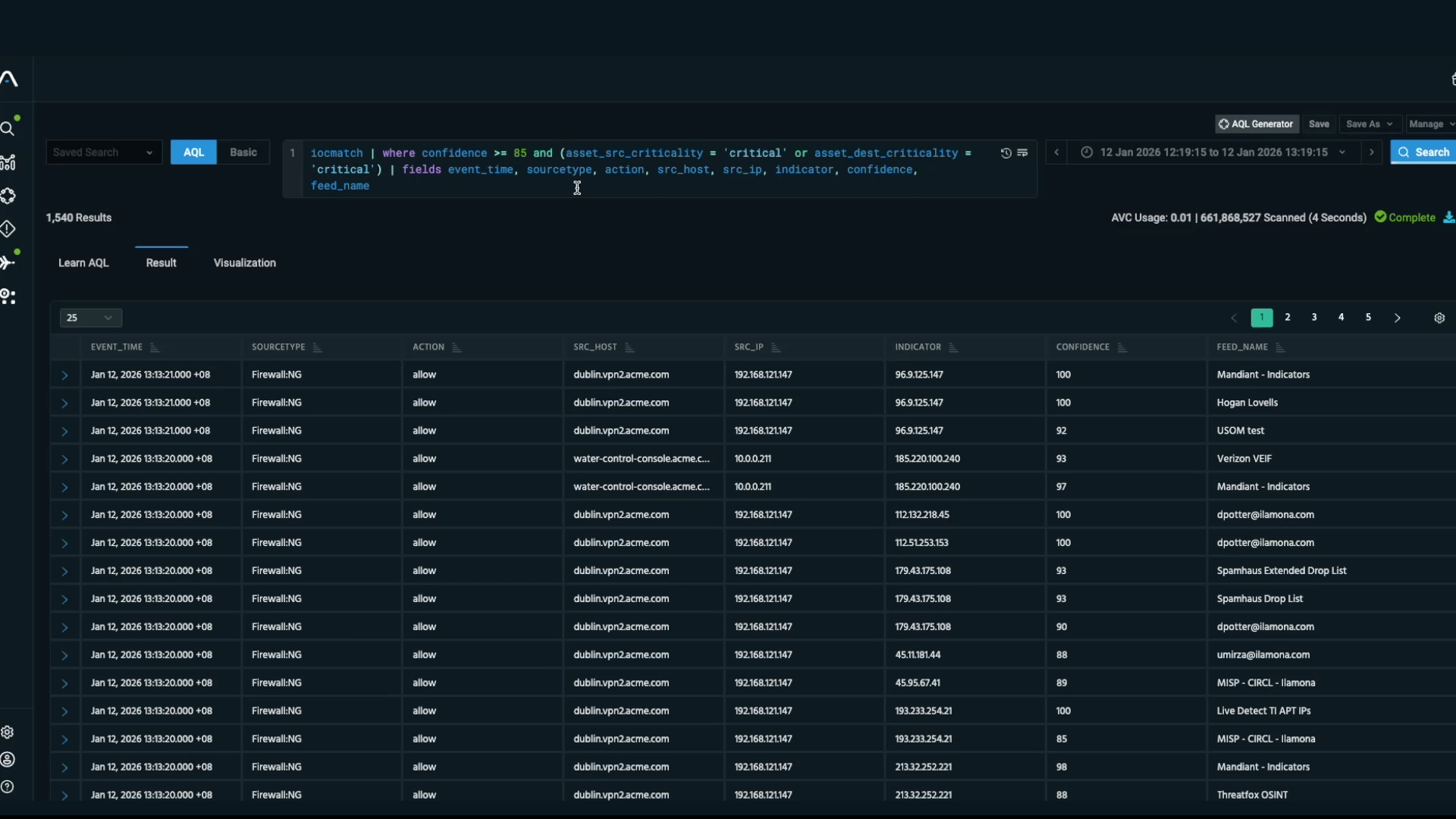
If you know the threat actor, or you know the hacker, or you know the bad guy, whatever term you're going to use, you can identify them with an email address.
You can identify them with an IP address.
And those very technical details are called indicators of compromise.
Once you have that into a centralized location, you essentially have an encyclopedia on threat data.
Probably the biggest challenge that we see is the volume of data.
There's obviously so many different incidents happening on a daily basis.
There is a staff shortage as well, across industry.
So it's trying to manage the ever-increasing events and information that's coming up to the desk of the analyst.
So the other key element to a TIP is the scalability.
So imagine if you have one analyst that has to go out and get the data, bring the data in, process it.
The time that that takes is pretty significant.
Whereas a TIP will automatically go out and get that information via automated services, or community-driven.
So imagine that one analyst becomes an army of analysts bringing that data in.
Ultimately, what that'll do, it will bring that information, that threat data that's released, and it'll make it actionable quicker.
The threat intelligence platform, it takes your security from being reactive into a proactive space.
And so you want to analyze what the common threats are in your area, maybe what's happened to someone else in your industry.
You're able to put in safeguards to try stop something before it happens.
Norsk Hydro, who was hit by a ransomware attack recently that cost them approximately $50 million, the fix.
So if you can prevent that, it's a little bit cheaper.
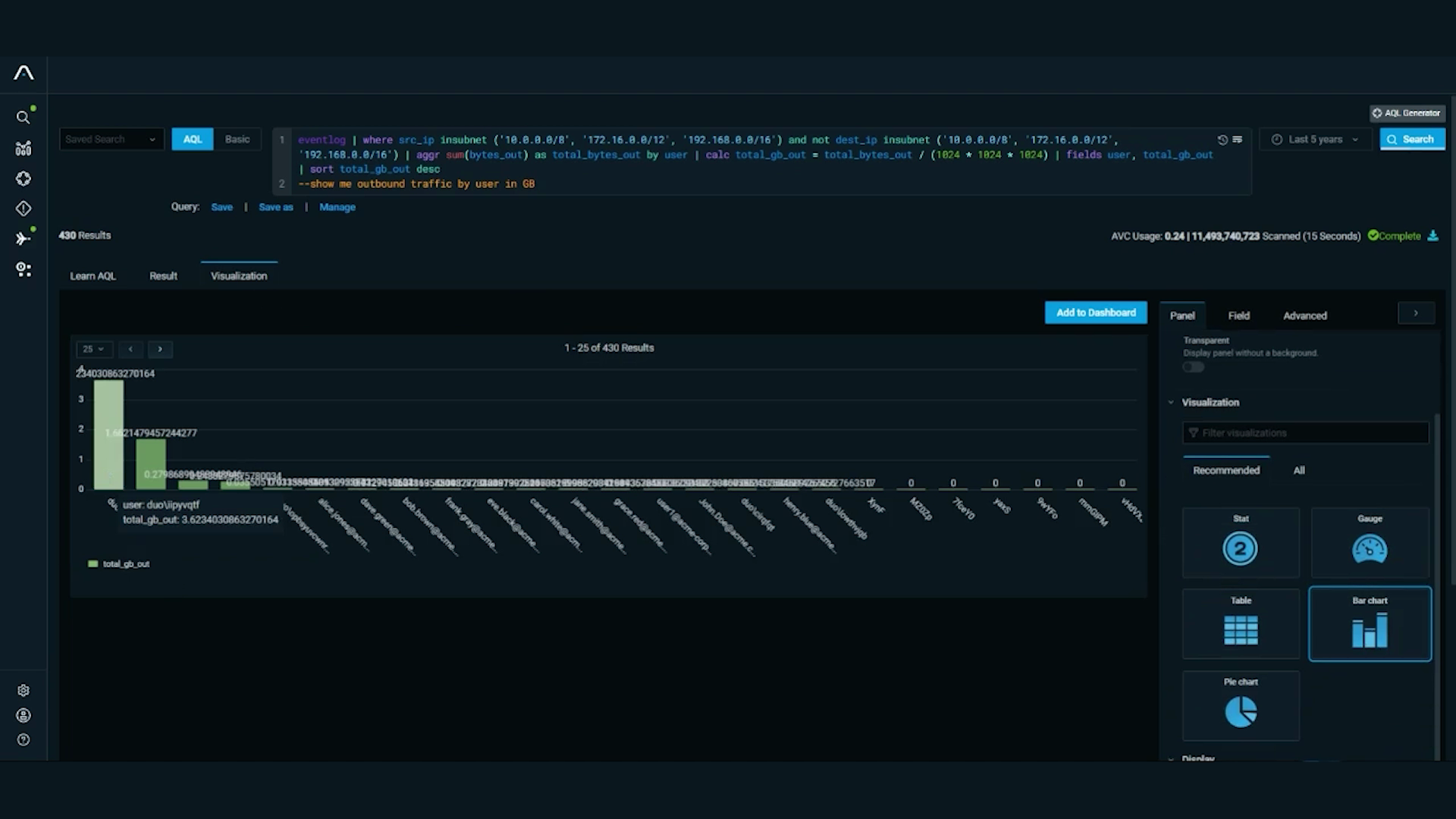
So now that you got the data in, the important thing is getting the data out.
So they're taking it, and they're pushing it down into the firewall to block the adversary immediately.
Or they're taking that data, and they're pushing it to their host endpoint integrations in order to prevent the malware, the phishing email from properly executing.
Another thing it can help with is that, if you want to generate your own threat intelligence and share that within your community, you don't need to set up the infrastructure yourself to help disseminate that.
The platform is built in itself to help facilitate the dissemination of that information.
When a customer is looking at acquiring a threat intelligence platform, the first thing they may want to start off with is a free program, similar to what we have called STAXX.
And that'll kind of get them introduced to what threat intelligence data is, and how to process it.
And then from there, they can grow with Anomali, and they can move into a more robust threat intelligence program.
The cyber threat landscape is constantly evolving, and so they need to be on top of that to proactively prevent breaches, prevent exposures.
And so it's obviously our job to help them and give them that view of what's going on and what's relevant to them.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.