Threat Intelligence Sharing—Cybersecurity's Secret Weapon
Cyber threat intelligence sharing is really important.
By sharing relevant, timely and actionable intelligence with your peers and groups, you have a real benefit of knowing proactively what is happening in your environment, and therefore taking them steps back internally to prevent breaches or prevent exposures.
If one bank is seeing an attack, there's a high probability that another bank will see that same type of attack.
And how we thwart the bad guys from getting in is through that sharing of information.
If one individual or one group shares intelligence then that potentially can provide detection and prevention at scale across a whole industry or a whole vertical.
That's the beauty of threat intelligence, is you can share a variety of information, and something is going to be useful to someone else.
You might not find it useful, but the whole point of information sharing is sharing it.
You might have a benign IP that used to be active, or just might be a bit iffy.
It might be benign, but that eventually could actually turn into someone's domain is actually using that to install malware or something.
You never know.
A huge part of efficiency and effectiveness is definitely joining your local or regional security interest group, and through discussions and meet-ups you're building trust with organizations and individuals to know what's happening and potentially know what's around the corner, and so be proactive to stop incidents coming at your door.
If a company is getting attacked, or sees a network-based attack coming at them, there is information that they're going to collect.
Well, some of that information is business-critical.
For example, what type of business system are they attacking?
Information like names, domain names, stuff like that.
That's not information that you want to share out or have publicly available.
So it's making sure that you can declassify, so to speak, the information so that you can still share the relevant information and the context behind it.
People think that, oh, I have to share our secrets for us to actually participate in threat intelligence.
But you don't.
And a lot of major organizations and industries utilize information sharing as a basis to create resilience and longevity for everyone.
It's critical that small and medium businesses participate in threat information sharing because the whole point of sharing is it's a community.
It's about trusting each other.
It's about relying on people who may have more expertise in one area than you have.
So if you couple the small businesses, you may have someone who's really good at IT networking, then you may have somebody who is really good at understanding how phishing emails work.
So the value of threat intelligence sharing is that you have that crowdsourced information from that team maybe that has the individual who is exceptional at reversing malware, and that person who's exceptional at network detection, and you you're able to couple those together at no additional cost to the company.
Maybe some small or medium-sized enterprises don't believe they have any information or intelligence to share.
But definitely, I think, there's the greater need for them to contribute to the conversation.
Any information or events of interest they see in their environment should be appropriately passed across.
That one detection on your environment could provide necessary information or intelligence to stop a global or big campaign, hit an entire sector.
So I see threat intelligence sharing becoming speedier in the future.
Faster.
So adding automation into the detection capabilities of an attack, scrubbing it, and getting it out to the community quickly so that other companies are less likely to be compromised.
There is also the possibility of more regulation and perhaps mandating the need for more intel sharing in communities, in enterprising, and governments.
And hopefully that'll be the real incentive.
Almost everyone's vulnerable to being hacked or attacked in some certain way.
To kind of mitigate the severity of those and severity of the risks, you have to participate in intelligence sharing.
Even if it's just the bare minimum and kind of easing into it.
I think a lot more people, and organizations, and even countries I think, which is the hardest industry to kind of change, they're slowly seeing that we kind of need to be collaborative because future success is based on that.
I think more and more as positive use cases and examples come out, then I think there's more buy in.
There surely more growth within the intel sharing community, which is good.
I think there's more realized use cases that it is finding a difference.
It's critical to the success of cybersecurity that we continue to evolve threat and information sharing, and that we continue to accept the responsibility of all of us to share threat information.
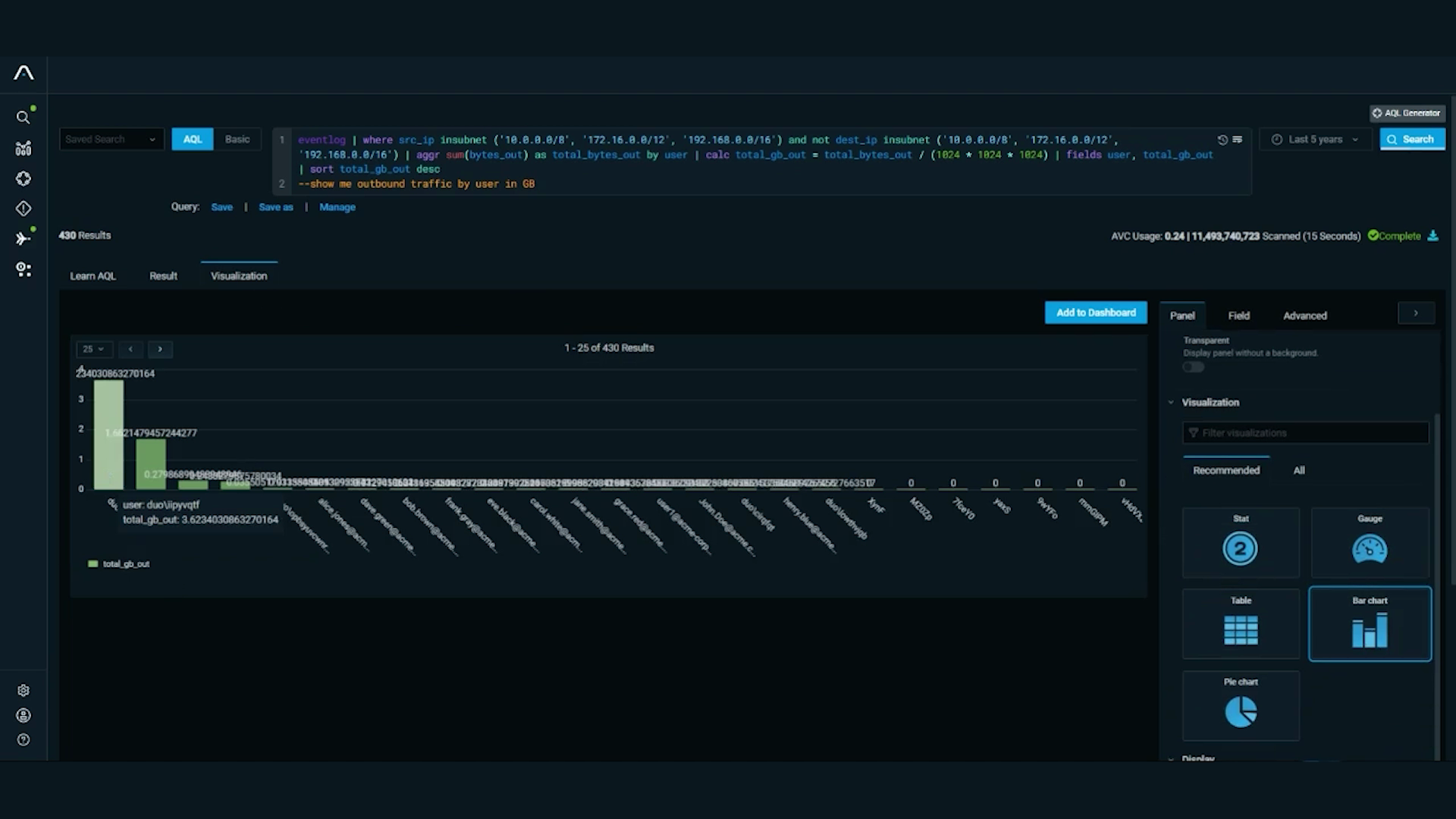
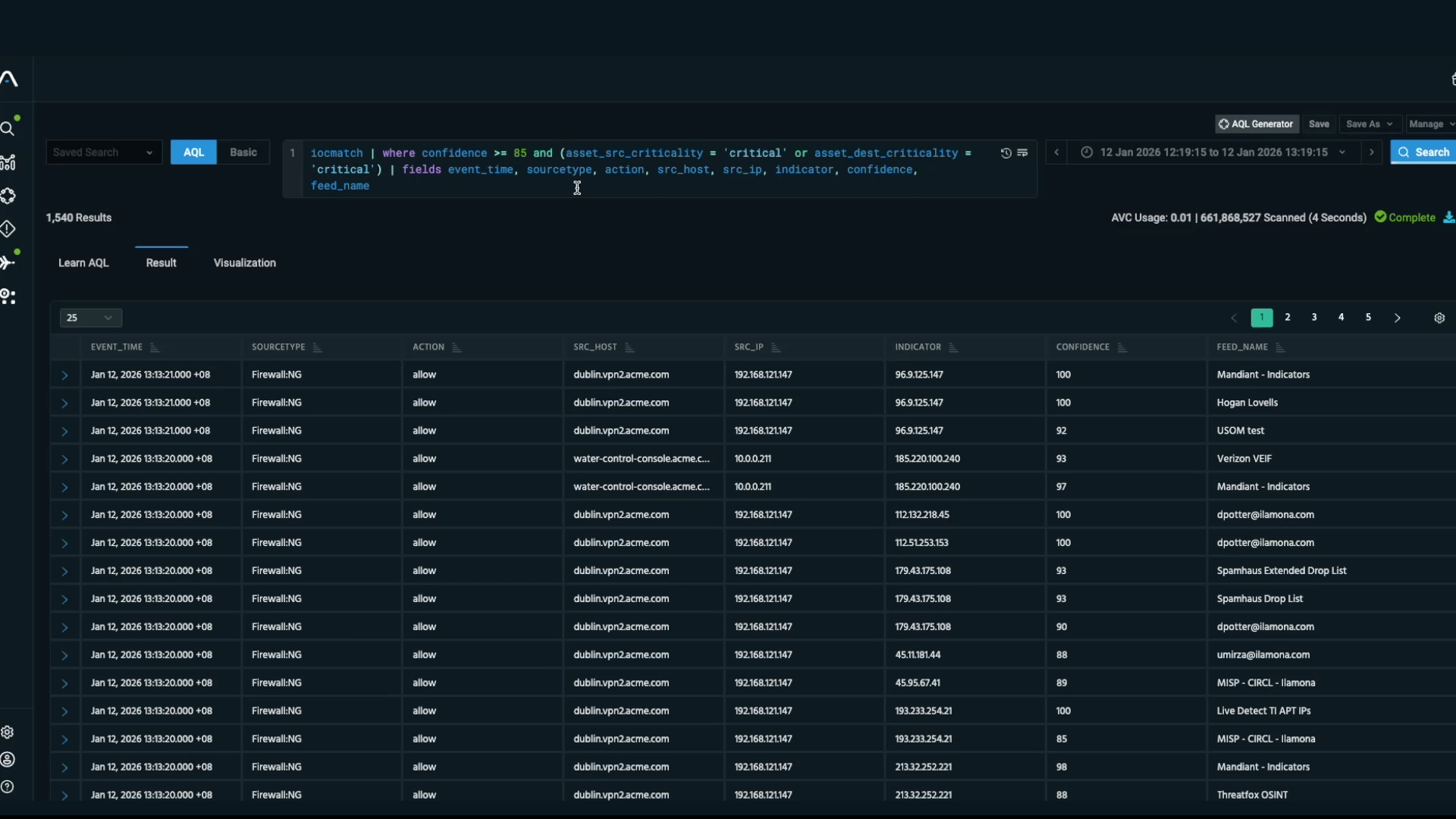
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.