Dark Reading News Desk: Time to Get Smarter About Threat Intel
Welcome back to the Dark Reading News Desk, coming to you live from Black Hat USA.
I'm Terry Sweeney.
Our next guest today is Joakim Kennedy, Threat Intel Manager, from Anomali.
Joakim, thank you so much for making some time to talk to us today.
Thank you.
Appreciate it.
Let's get really zen, let's get really basic, and let's start with the essential question.
What is threat intelligence?
JOAKIM KENNEDY: So depending on who you ask you can kind of get different answers of what is threat intelligence.
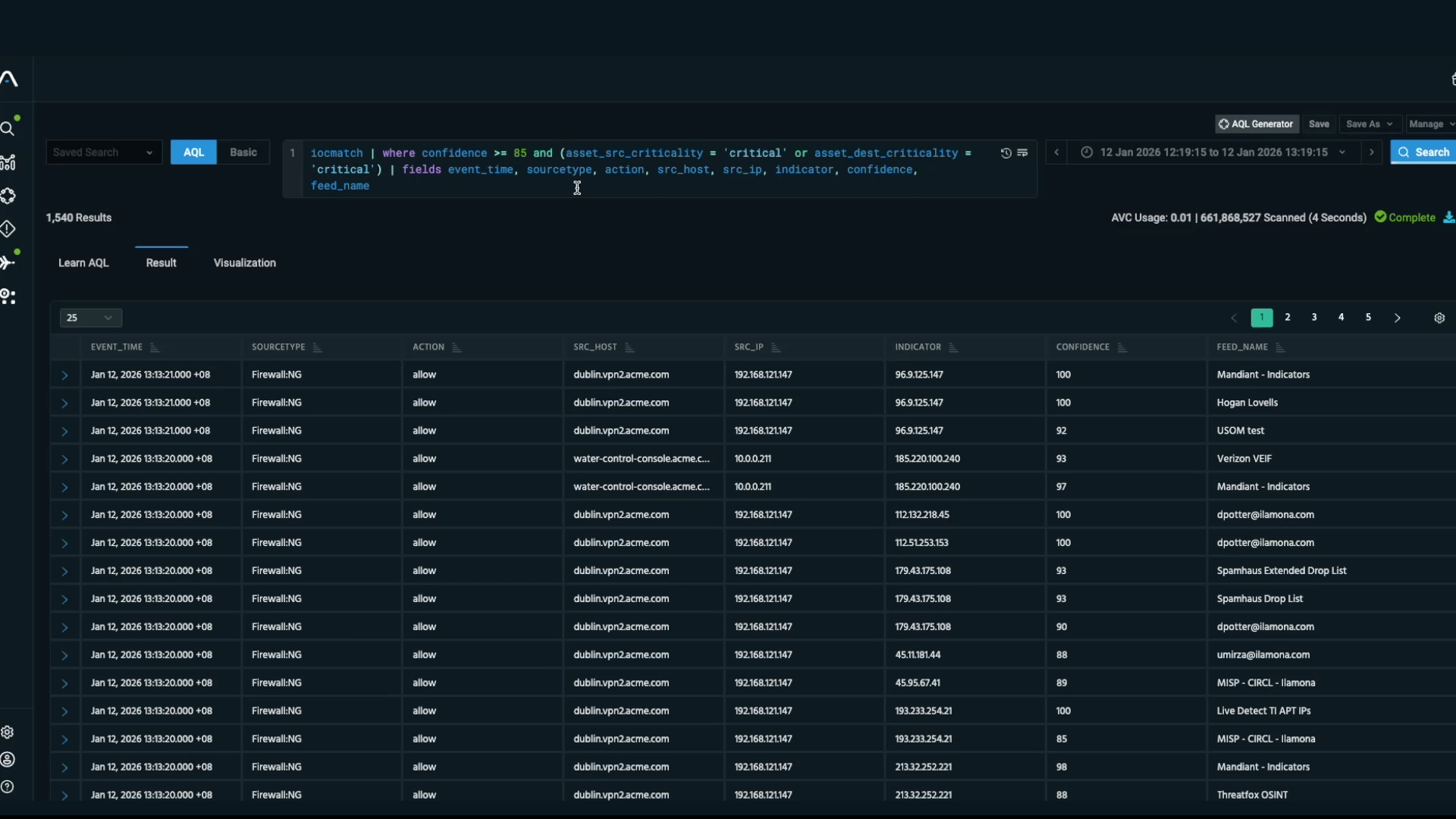
So the way we define it is, it's actionable information that you can use to either protect against a future threat or against-- you can use it to find previous sort of a threats that have been against you.
TERRY SWEENEY: OK.
And it usually comes in sort of two parts.
You have a data point that can be an IP or a domain, and then you have some sort of a context that gives you what it means and things like that.
So bad IPs on its own is not threat intelligence.
TERRY SWEENEY: OK.
You need the whole thing.
And it's the same thing with just context.
It's not threat intelligence, that's just information.
You need sort of both of it for it to be actionable.
TERRY SWEENEY: So you need data and context.
Yes, correct.
TERRY SWEENEY: Handling threat intelligence is obviously crucial for trained IT staff.
Having a trained IT staff is also essential.
The staffing challenges in both info security and IT in general are well documented.
Any sense of what we can do to get more people interested or excited about this particular field?
Yeah.
I don't think there's directly one silver bullet for it.
But what we should start looking into is to look for the future employment.
So if we can provide and get younger generation more interested into it.
And so one option could be to open up and give access to tooling and stuff like that that's being used in the industry.
So that's kind of why we are releasing an open source tool here at Black Hat that we're showing off at the arsenal.
All right.
Thanks.
It feels like we've got a couple of dynamics though that the security industry itself is juggling.
The lack of sufficient candidates for cybersecurity jobs, but also an ongoing struggle for more budget dollars for both hiring, training and retaining these same employees.
Any sense of which of those challenges is easier for companies to deal with?
It's a hard-- both of them are really, really hard to solve.
So the fact that you can't find any suitable candidates means that you have to go and look into to find new candidates that you're willing to train and also they are willing to actually learn.
And for that you need that budget.
But on top of that, that budget should be there already because it's important that you are actually training your cybersecurity team because you need them to stay current.
And it is something that probably would be what we should actually focus on solving, is to make sure that that is actually what's happening.
So is the subtext to this are we really talking about the politics of security?
Yeah.
I mean it always comes down, more money you have the easier it is to solve the problem.
TERRY SWEENEY: Right.
Thank you.
How do we evolve skills from just collecting from threat intelligence feeds from a wide range of sources to identify and act upon attacks that really pose a threat to the environment?
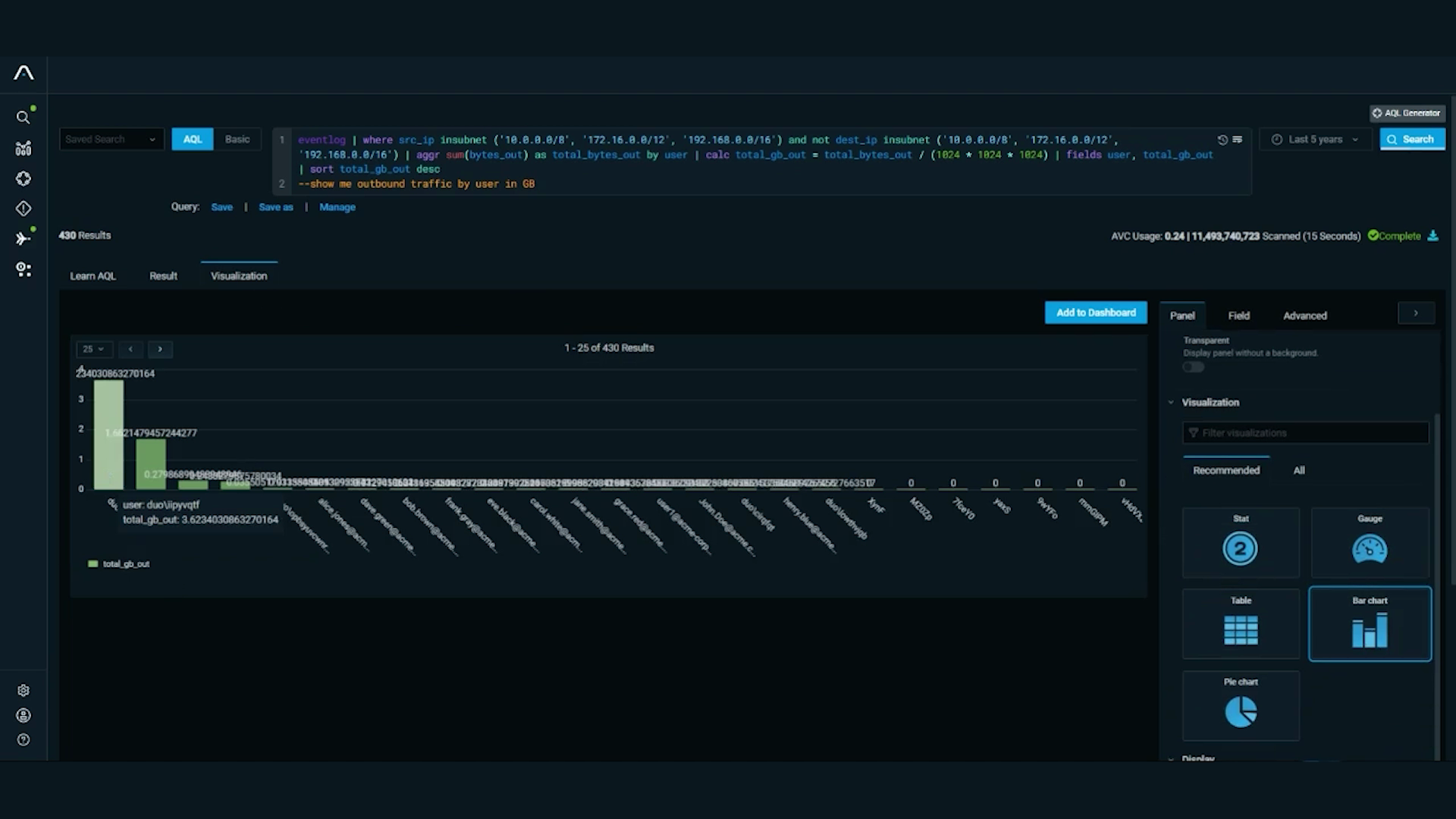
So threat intelligence that came in as some sort of feed and stuff like that has been a really, really great way of integrating and actually get organizations onto using threat intelligence.
Now it's sort of coming to a point where we have to change how it's been used.
The threats nowadays move so fast that by the time it actually hits an event or a feed the adversary has already moved on.
So it's not solving the same problem it used to do where you could use it to block future threats.
Where it still sort of serves a purpose is that you can use it to find have I been breached.
But it's the historical look up.
Instead what needs to be pushed on is to get that moving to actually use finished intel and use that knowledge to sort of prepare for protection.
And it's something that's coming with just sort of the maturity, both the maturity of the industry but also the maturity of the consumers of threat intelligence.
So if I can torture your analogy a little bit, it feels a little bit like threat intel is a bit like weather data but the bigger picture is you need something that's going to tell you like specifically when it rained and for how long-- Yeah I mean where you can look up though is-- the thing with finished threat intelligence is that it may not directly seem applicable from whatever the report you're looking at.
So one of the training things you have to focus on is to see how is this report that's coming out how can I use what that information is that to actually protect my organization.
There's parts here that I can actually utilize.
It's not just that doesn't seem to apply, what's next.
You know there's always information you can learn from it.
You seem to be alluding to I'll call it an effectiveness gap in threat intelligence.
JOAKIM KENNEDY: Yes.
Is that accurate?
Yeah.
I would say there is an effectiveness gap in it.
I mean earlier-- what it comes down to is the use of threat intelligence in the private sector is still a young or new sort of area.
And I mean earlier this year there was the Ponemon report, sort of highlighted how companies can address the effectiveness.
And one of the key things coming out of that is that the importance of actually having a dedicated team that is actually focused on just some threat intelligence.
And then on top, sort of going back to the previous budget, that you actually are allocating a specific budget for this work.
Other things to sort of solve the effectiveness is coming down to it's good to participate in all this sort of the sharing community.
So whatever exit that you have for your vertical.
And then also when you're getting threat intelligence you need to be able to disseminate and send it out to whatever your integrations have if it's firewalls or endpoints.
And that's kind of where we sit for the anomalies to facilitate that.
But in general, it comes down to you need to know who might be your particular adversary, what are they after, and what are their methods.
You want to be prepared when they come knocking on the door essentially.
OK.
Picking up on a comment you made a few minutes ago, I'm curious what your sense of the importance of training is in making a difference in this entire equation.
So training is very, very important.
It's a very-- the industry moves quickly so you always have to stay current.
You don't want your team to apply the last generation's methods to protect against the new generation that's being used by the adversaries.
On top of that also, the more you know, the better you are as a defender.
You need that strong base to stand on and sort of help them work from there.
And the good thing is the security industry is a wide field.
You don't have to come from a technical background.
It does help, but in the same sense if you're a technical person and you know other stuff, for example around policies and other things that are less technical, you're a better sort of candidate and better sort of person when it's security.
So whatever knowledge you can achieve it is useful.
So training is very important.
All right.
Thanks for this.
This was really insightful.
I appreciate you taking some time to talk with us at the Dark Reading News Desk.
Thank you.
We've been talking with Joakim Kennedy of Anomali.
Don't go away.
There's more News Desk coming right up.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.