What Are STIX/TAXII?
STIX is a framework.
Think of it as a model of threat intelligence data.
And TAXII is the process in which somebody acquires or sends that information.
Think of the TAXII server as the one that is serving out the information or receiving it, and what it's serving and receiving is a STIX package.
STIX is basically just a common language for intelligence.
So everyone in the world, whether or not English or whatever is their first language, it just creates a foundation for everyone to know what is happening and what this means.
Years ago, the intelligence industry determined that we need some tool, some container, essentially some vehicle for taking this information that is being tossed around, and to be able to take that and push it out to anyone who wants to receive it.
And so from there, that's where STIX and TAXII was born.
So they're free, because from an industry perspective, we want everyone to be able to share this information freely.
And so it's important that that standard remains free.
Imagine that the FBI wants to put out an all-points bulletin to everyone in the United States.
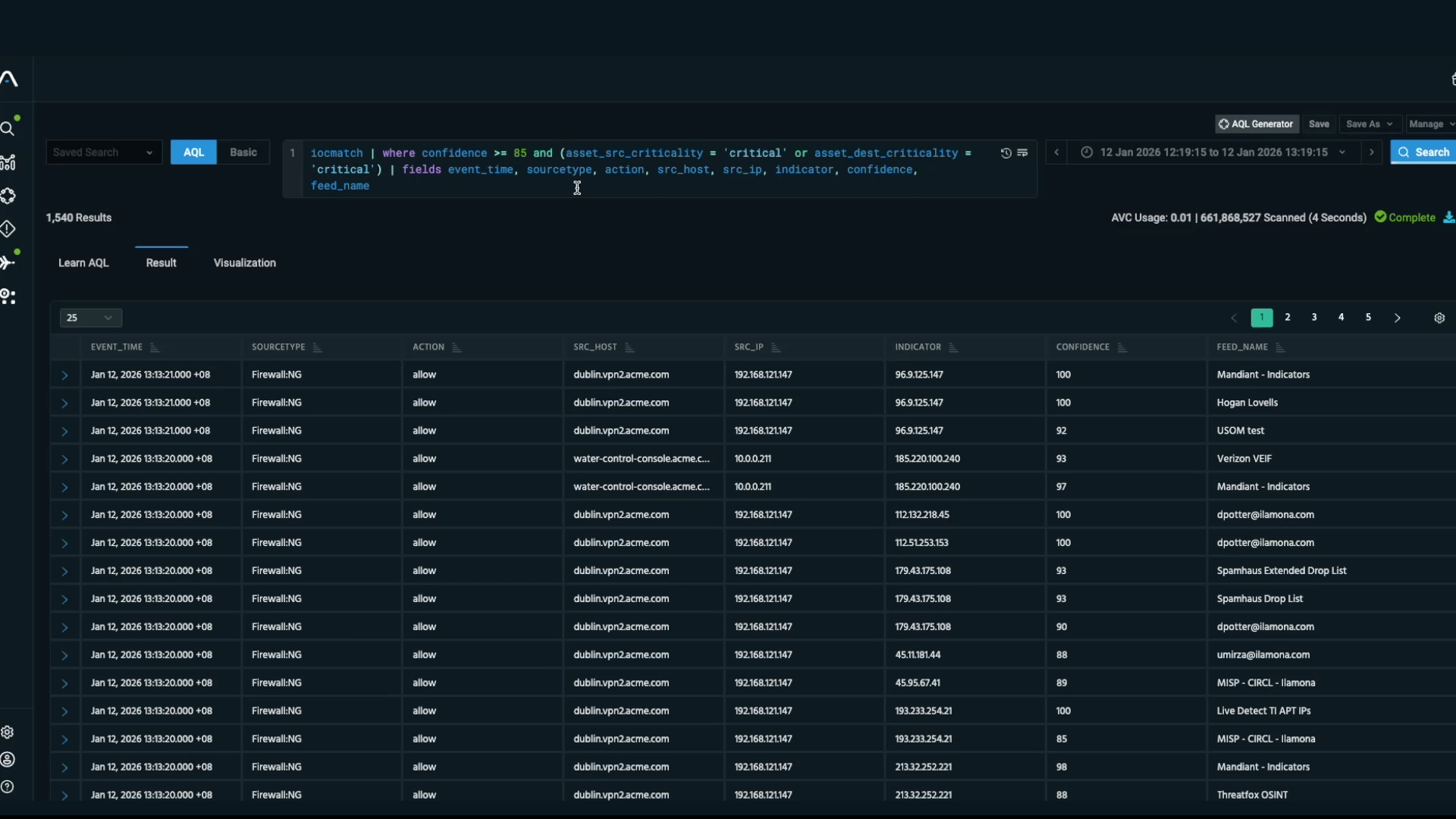
They can push that out as a STIX package, and immediately if a company is using a TAXII server, they can pull that in and they can immediately operationalize it.
So it normally uses STIX for both platforms that we have, so whether it's ThreatStream, which is the subscription-based TIP, or STAXX, which is more of the free kind of general TIP.
STIX is used so it structures it in a way that you understand what the itypes are, what malware, whether it's a malicious IP false positive malicious domain, it structures it in a way that everyone can understand it.
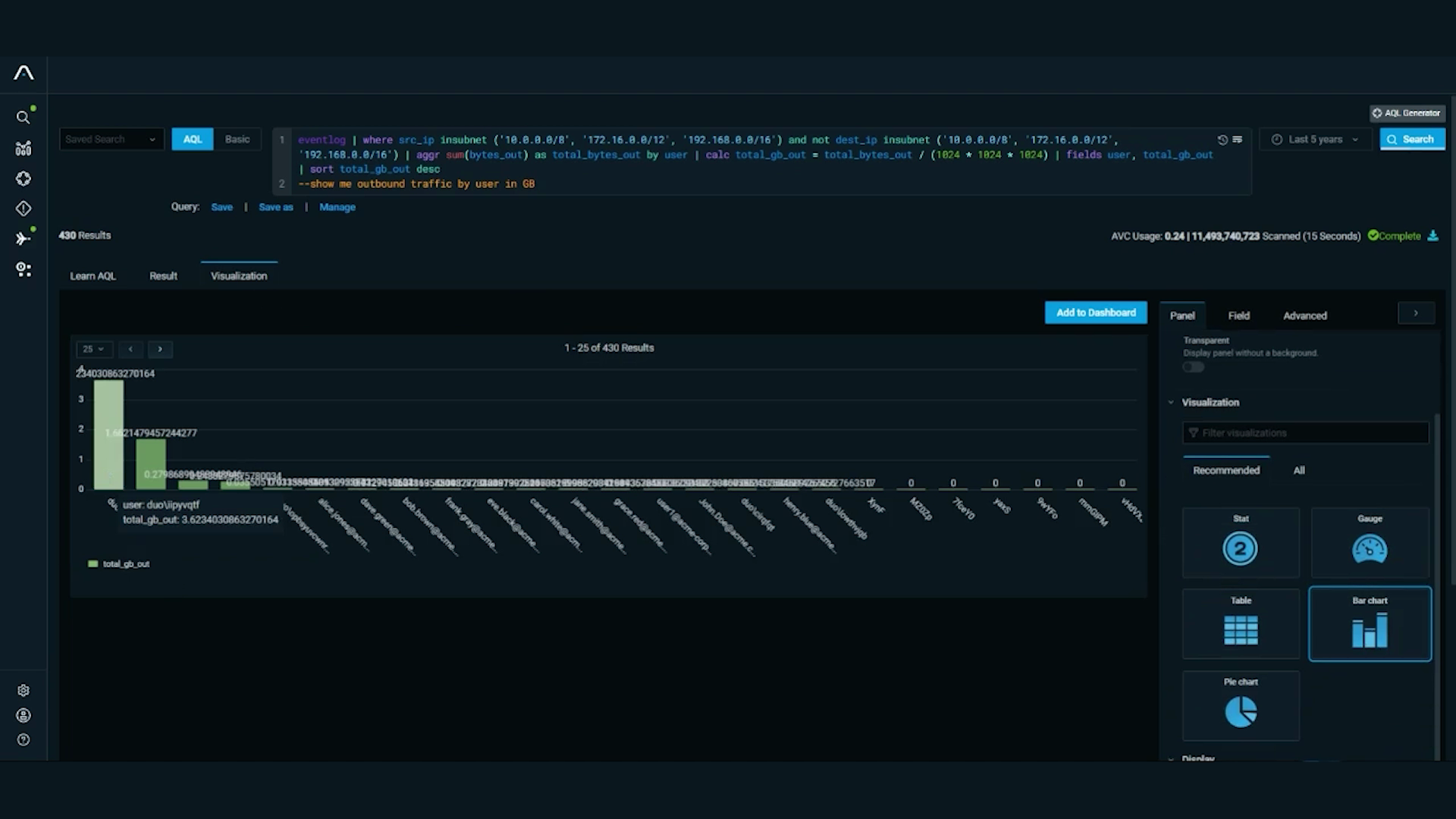
Anomali uses it in a couple ways.
First of all, we have a free-to-use STIX taxi virtual machine client, called STAXX.
Basically what it does, it's able to pull down data from STIX TAXII service and consolidate and normalize that data.
That's pretty much it.
Then it has an API, which you can access that data.
How our Anomali threat platform uses it is that you're able to export both indicators and threat model intelligence into STIX format in multiple versions.
So STAXX is a free version of ThreatStream.
And what it does is it allows users to basically dip their toes in to kind of get a better understanding of threat intelligence information sharing.
So they can utilize STAXX to use it on a very general basis, and then as their needs evolve, as they get larger, as they are kind of the threats change, then they can then switch to ThreatStream which is much more comprehensive.
So ultimately, if you're trying to serve this information out to maybe some local endpoints or maybe some other individuals who want to share and collaborate that information, Anomali's TIP allows you to be able to freely do that and ease of use of just clicking a button and sending that information out.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.