What is a Threat Intelligence Ecosystem?
It's the Dark Reading News Desk.
We're here at RSA in San Francisco.
And I'm joined today by Hugh Njemanze, the CEO of Anomali.
Hugh, thanks so much for joining us today.
It's a pleasure.
Last year was a record year for cyber attacks.
Why is it so hard for organizations to stay ahead of these threats?
And maybe more puzzling, why is it so hard for them to know when they're actually under attack?
Great question.
Well, the number of attacks seems to be increasing every year.
So I think we'll see more record years.
And organizations actually tend to already be deploying several tools to help with the various aspects of detecting and mitigating security threats.
However, a lot of these tools don't really integrate with each other in very meaningful ways.
And so one capability that's really needed is a way to have integration between the various components of your security system.
This is something Anomali has been working very hard on over the past year, to actually use threat intelligence as a way to interoperate and integrate between the various tools in a security arsenal.
All right.
I mean, as you say, integration is a big priority for most customers today.
Can you talk about some of the things that Anomali has developed to help facilitate integration, particularly of security systems?
Yeah.
We've been working on a few key strategies.
For one thing, in the past year, we've introduced three separate SDKs.
And these are software development kits.
And the idea of these is to make it easy for the various subcomponents of a system to interoperate.
So one of them is our feeds SDK.
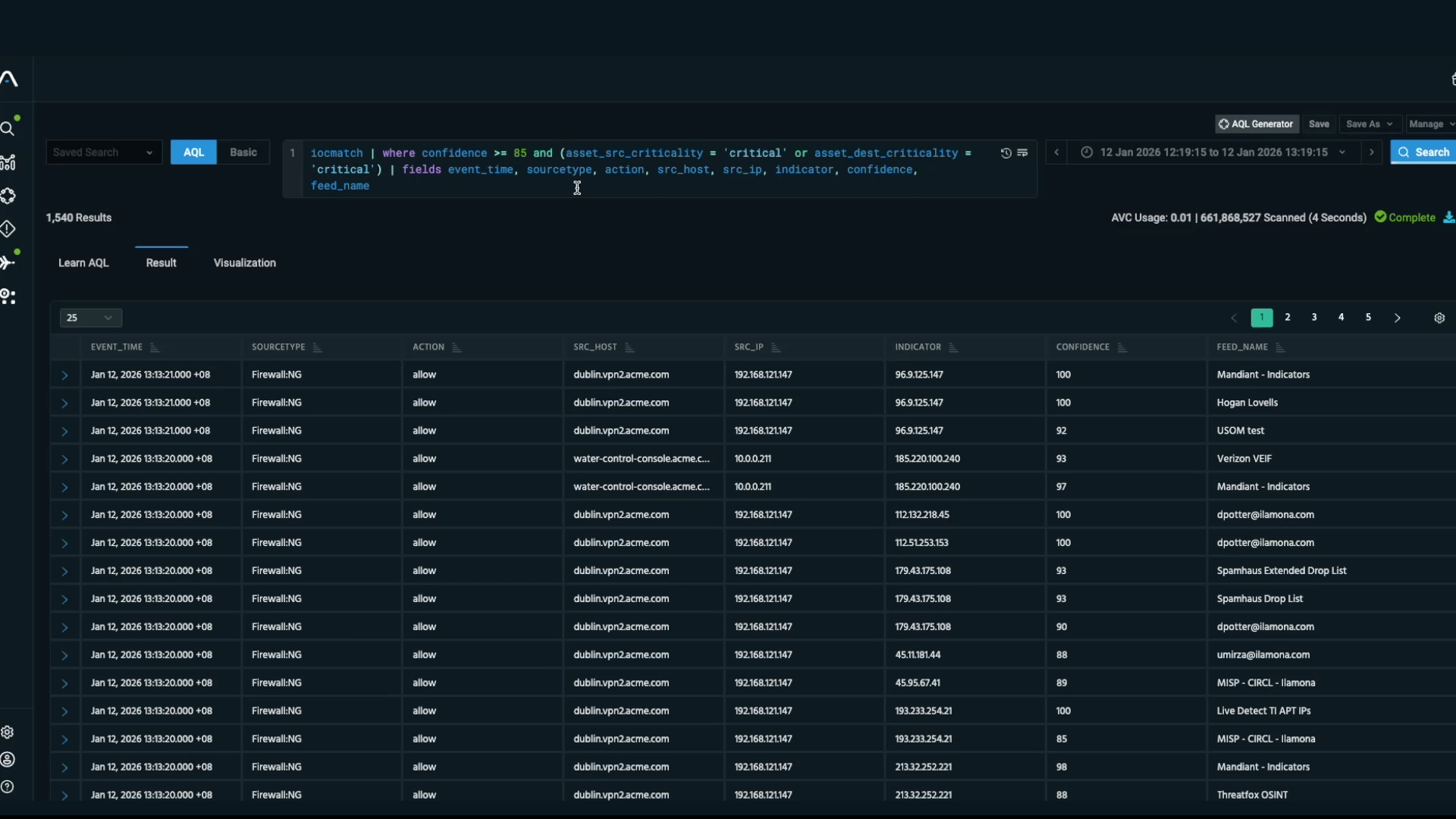
And that's designed to allow organizations and also partners that produce some of these threat intelligence feeds to take literally the best of breed feeds, integrate them into the system.
And the point of that is, if all the feeds can talk to one system, then each new feed that gets integrated can be distributed to all of the downstream systems that want to take the intelligence and make use of it.
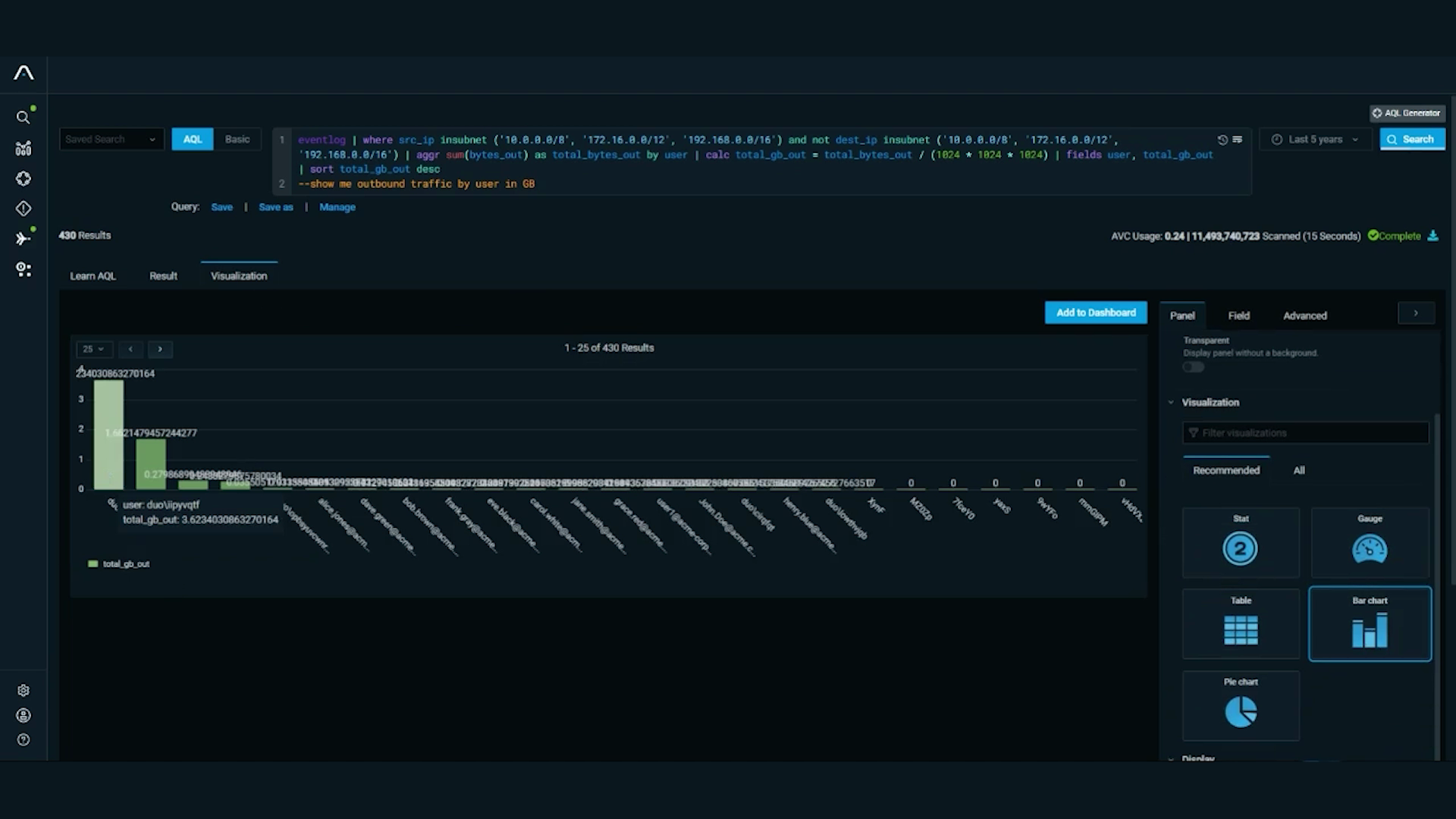
And so that's where our second SDK comes in, which is an SDK that makes it easy to do integrations with downstream consumers of threat intel, like SIEMs, products like Splunk, ArcSight, IBM's QRadar, et cetera.
And then we have a third software development kit that makes it easy for customers to actually enrich the threat intel data.
So once there is something that's of interest, you can basically add contextual information about that particular threat or actor.
Yeah.
So that's one area.
And the second area that we find very interesting in this context is the notion of analyzing the tools, techniques, and practices of our adversaries.
And so we've integrated with frameworks like the MITRE ATT&CK framework, which basically makes it much easier to see the context of what the bad guys are doing and how.
We're hearing a lot about threat intelligence and threat intelligence ecosystems here at RSA.
Help us better understand what those terms mean.
Sure.
Well, it's hard for a threat intel to solve problems by just interfacing with one tool.
And so it's important to build integrations into all the other parts of that ecosystem.
So tools like firewalls, SIEMs, which are our security information and event management systems, endpoint protection tools.
There is also tools like email security gateways, and similarly with cloud infrastructure.
And so the idea is to be able to integrate into all of those tools and provide a full contextual picture to coordinate the intelligence flowing through those systems.
OK.
Some end users are pushing back, saying that they've already bought security tools, that they already have some automation in place.
What's missing from the equation that allows threats like phishing to still be a problem?
Yeah.
Well, being able to operationalize threat intelligence, it requires, number one, the integration between those tools, but also analytical capabilities, so that when we see, for example, efficient attack, you can take the context where it started from in the email chain, look at the various actors that are connected to the source, and essentially do the kind of analysis that a human would do by looking at multiple tools.
We've actually worked on being able to automate a lot of those steps.
And that requires talking to all the different tools in the chain.
OK.
You mentioned this phrase, "operationalizing threat intelligence." Is that analytics at work?
Or are some other sets of processes in place there?
Yeah.
There's a lot of pieces involved, depending on how you look at it.
But it starts with being able to integrate the intelligence into tools that can consume it.
It also basically means looking at what's the threat model-- essentially, what steps is your adversary trying to take?
And so when you combine that analysis, you essentially want to look at how a human researcher would reach conclusions and provide tools that reduce the number of steps it takes to do that.
As more organizations have come to believe they need to safeguard data, do you see any resistance to sharing threat intelligence?
And if so, what do you advise customers there?
Yeah.
We have seen resistance, especially in the earlier days of threat intel.
So this field is not that old-- five or six years old.
So when I say "early days," I'm not talking about that long ago.
But organizations, essentially, have a hard time sharing threat information with each other for several reasons.
One reason is sometimes they're just shy.
They're worried that maybe the intelligence they're sharing is not as amazing or unique or high quality as maybe other peers.
And so they're worried about, if I share this, will I look bad?
They're also worried about exposing internal linen-- basically, dirty laundry.
And that could undermine the confidence of customers, for example.
They're also concerned about their own legal department, thinking this is leaking of corporate IP to a competitor, because if you're a bank, you're going to share with another bank.
But then that's also a competitor.
So there is many sort of cultural barriers.
We see things getting a lot better.
One of the areas we've focused on is on building tools that make it easy for organizations to essentially share information in a structured way that proves that they're collaborating on something for the good of the entire industry, as opposed to sharing proprietary IP.
And we've also worked extensively with information sharing organizations, like ISACs and ISAOs, as they're known, to provide tools and infrastructure to literally make it technologically easier to do something that's actually culturally challenging.
Anything else that Anomali is involved in that helps encourage that sort of information sharing?
Yeah.
We've worked with organizations, like for example, the most multi-state ISAC, Colorado ISAC, several other ISACs.
There's usually an ISAC for each vertical.
What we've found is that in the US, the notion of an ISAC is a fairly well-developed concept.
In other parts of the world, not every country has ISACs covering all the verticals like we do here.
And we've actually been fortunate to be able to help organizations in various countries around the world to start launching, creating, and running their own ISACs.
All right.
Any other resources that you can recommend to our viewers for places to go to find out more about threat intel?
Well, a good place to start would be anomali.com.
And that's spelled with an I.
And you can go there and learn about threat intelligence, threat intel platforms, and also how to get started on building your own thread intel ecosystem.
That's great, Hugh.
Thank you.
Thank you.
This is Terry Sweeney for the Dark Reading News Desk.
We've been talking with Hugh Njemanze, the CEO of Anomali.
Thanks for tuning in today.
Discover More About Anomali
Check out some of our other great resources covering the latest cybersecurity trends, threat intelligence, security and IT operations, and Anomali product updates.