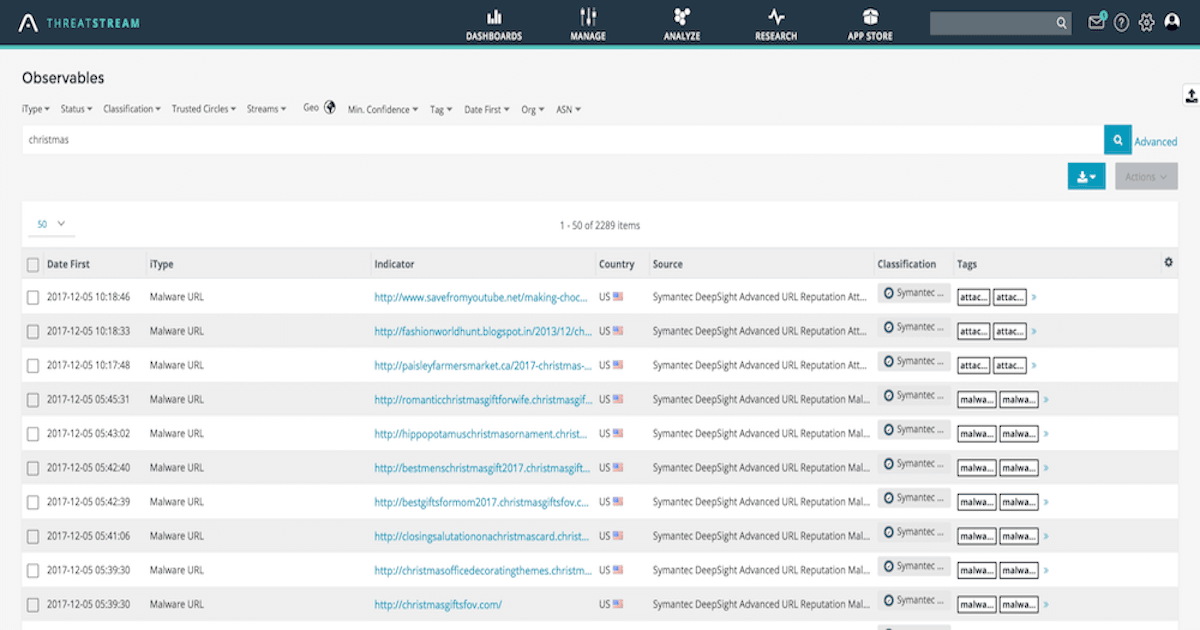

<p><a href="http://news.gallup.com/poll/221060/americans-best-holiday-shopping-mood-years.aspx" target="_blank">In 2017, Americans are projected to spend $906 million on gifts, up from $785 in 2016</a>. A significant chunk of that total will be spent online. As consumers turn to the internet, those looking to exploit them are increasing at a similar rate.</p><p>Over the last 5 years, the festive season has seen actors ramping up Christmas themed campaigns to directly target businesses and consumers. This post outlines a very small number of particularly prolific attacks that have been observed over previous Christmases that will very likely be seen in reworked variants this year.</p><h2>FastPOS</h2><h2><img alt="" src="https://cdn.filestackcontent.com/Zcf5PmQTCqQbYCEQFmRA"/></h2><p><strong>View details in ThreatStream</strong>: <a href="https://ui.threatstream.com/search?status=active&multiSearchResults=true&value__re=.*fastpos.*" target="_blank">https://ui.threatstream.com/search?status=active&multiSearchResults=true&value__re=.*fastpos.*</a></p><p>Despite the increase in ecommerce transactions, in-person retail sales still account for the largest share of the market. Many consumers don't think twice when they swipe their credit card or enter their PIN when buying that must-have gift. Unfortunately, some of these people might receive unwelcome expenses on their credit card statements come January if they've fallen victim to using a point-of-sale (POS) device infected with malware.</p><p>First seen in June 2016, FastPOS is just one piece of malware that targets POS devices. FastPOS, as it is called, is much like other POS families in that it will capture credit data, Track2 and log keystrokes on the infected machine. Notably, the malware communicates with its command and control (C&C) via unencrypted HTTP session. The POS malware establishes persistence much like other malware by creating an auto run key in the Windows registry.</p><p>Previously, <a href="https://www.scmagazineuk.com/fastpos-malware-becomes-stealthier-ahead-of-festive-credit-card-spree/article/547646/" target="_blank">FastPOS has taken advantage of the increased retail transaction volume in the run-up to Christmas</a>. Various iterations of the FastPOS and other malware families targeting POS systems are likely to follow suit during the 2017 holiday season.</p><p>Protip for retailers: <a href="https://ui.threatstream.com/search?status=active&tags=retail" target="_blank">search for indicators of compromise (IOCs) tagged with "retail" in ThreatStream to uncover threats to your operations over Christmas</a>.</p><h2>Lizard Squad</h2><p><img alt="" src="https://cdn.filestackcontent.com/ulNy2GNgQSuKFHTlLIdP"/></p><p><strong>View details in ThreatStream</strong>: <a href="https://ui.threatstream.com/search?status=active&multiSearchResults=true&value__re=.*lizard%20squad.*" target="_blank">https://ui.threatstream.com/search?status=active&multiSearchResults=true&value__re=.*lizard%20squad.*</a></p><p>In 2014, <a href="https://www.theguardian.com/technology/2014/dec/26/xbox-live-and-psn-attack-christmas-ruined-for-millions-of-gamers" target="_blank">Lizard Squad performed a distributed denial-of-service (DDoS) attack against the Xbox Live and Sony Playstation networks over Christmas</a>. As millions (including myself) attempted to play the games they'd just received as gifts they were met with errors. This occurred for the duration of the attack. </p><p><img alt="" src="https://cdn.filestackcontent.com/SkNy7OECSRq6ZUfFqDHU"/></p><p>Looking through ThreatStream, Lizard Squad are responsible for a number of attacks, with DDoS being their preferred method. Since the group's inception they have developed increasingly more sophisticated DDoS capabilities and are now using variations of the botnet malware GafGyt.</p><p>Protip for gaming companies: <a href="https://ui.threatstream.com/search?status=active&tags=gaming">sync indicators of compromise (IOCs) from ThreatStream with your SIEM to automatically match known threats to your l</a><a href="https://www.anomali.com/community/anomali-splunk-app">ogs, and alert when a match has been found</a>.</p><h2>Merry X-Mas</h2><p><img alt="" src="https://cdn.filestackcontent.com/NR58cokwT2GZInH98aw0"/></p><p><strong>View details in ThreatStream:</strong> <a href="https://ui.threatstream.com/search?status=active&multiSearchResults=true&value__re=.*Merry%20Christmas%20Ransomware.*" target="_blank">https://ui.threatstream.com/search?status=active&multiSearchResults=true&value__re=.*Merry%20Christmas%20Ransomware.*</a></p><p>2017 has been the year of ransomware. From <a href="https://www.anomali.com/blog/wanacry">Wanacry</a> to <a href="https://www.anomali.com/blog/petya-notpetya-petrwrap" target="_blank">Petya</a> and everything else in between, ransomware has brought havoc to companies around the world. <a href="https://www.theregister.co.uk/2017/08/16/notpetya_ransomware_attack_cost_us_300m_says_shipping_giant_maersk/" target="_blank">The NotPetya ransomware will reportedly cost shipping giant, Maersk, $300 million alone</a>!</p><p>The Merry Christmas (or Merry X-Mas) ransomware was spotted for the first time by security researchers in early January 2017, when the malware was distributed through spam campaigns. According to researchers, the latest strains of the ransomware have been delivered together with other pieces of malware, namely DiamondFox, which is used to steal sensitive information from victims’ systems.</p><p>Protip for SecOps teams: <a href="https://www.anomali.com/products/match">be immediately alerted when the latest malware hashes or suspect domain generated algorithms are seen inside your network (including on mobile devices) using Anomali Match</a>.</p><h2>Phishing for gifts</h2><p><img alt="" src="https://cdn.filestackcontent.com/neQ3LAz9RQSFPpwAeJ8A"/></p><p><strong>View search in ThreatStream</strong>: <a href="https://ui.threatstream.com/tip/9476">https://ui.threatstream.com/search?value__re=.*christmas.*</a></p><p>A quick search for malicious domains in ThreatStream turns up hundreds of IOCs with the word "christmas." Phishing campaigns often ramp up over the festive period, taking advantage of the fact people are spending more money in December. I've seen campaigns spoofing retailers and financial institutions in greater number this year than in any previous year I can recall.</p><p>Protip for everyone: never click a link in an email. For SecOps teams, <a href="https://www.anomali.com/products/match">monitor emails from compromised addresses or with links to known malicious domains before they're clicked using Anomali Match</a>.</p><h2>A few free Christmas gifts from Anomali</h2><p>STAXX gives you an easy way to access any STIX/TAXII feed and is a great tool for those starting to incorporate threat intelligence into their security strategies. </p><p><a href="https://www.anomali.com/community/staxx">You can download STAXX for free here</a> -- our gift to you this Christmas.</p><p>Understand your security risk posture with a free customized Recon Report from Anomali Labs. Simply sign up for a free Anomali Match Trial in the month of December.</p>
FEATURED RESOURCES

Anomali Cyber Watch
Iran's Cyber Arsenal Is Reloading: What CISOs Must Know About the Post-Decapitation Threat Window

Anomali Cyber Watch
Public Sector


