
<h2>Background</h2>
<p>Multiple vulnerabilities have recently been identified in the managed file transfer (MFT) software MOVEit developed by Ipswitch, Inc. and produced by Progress Software. These include CVE-2023-34362 <sup>[1]</sup>, CVE-2023-35036 <sup>[2]</sup> and CVE-2023-35708 <sup>[3]</sup>. These vulnerabilities allow adversaries to gain unauthorized access and escalate privileges in the environment.</p>
<p>MOVEit is a popular tool that is used by thousands of organizations around the world. These include organizations in the public, private, and government sectors. The transfer software can be deployed as on-prem, in the MOVEit Cloud, or on any Microsoft Azure server. Due to the nature of handling potentially sensitive information, MOVEit is a lucrative target from a threat actor’s perspective, granting threat actors the ability to add and remove database content, execute arbitrary code, and steal sensitive information.</p>
<h2>What do we know about the exploits?</h2>
<p>While this story is still actively playing out and we will know the final count only in the coming weeks, here's what we know about it thus far. </p>
<p>The CL0p ransomware gang has been actively exploiting this vulnerability and has claimed to compromise over dozens of organizations across different industries and regions. These include oil & gas, news & media, healthcare, financial services, state and federal governments, and more. Anomali’s own assessment has shown that there are thousands of externally exposed MOVEit instances that could potentially be exploited. </p>
<p>Additional public research has revealed that this vulnerability may have been actively exploited even since 2021 <sup>[4]</sup>. More recently, organizations have also released proof of concept (PoC) exploit code for this vulnerability<sup> [5]</sup>, making it likely that other attackers could exploit unpatched systems.<br/>
<br/>
<img alt="" src="https://cdn.filestackcontent.com/YeWMhzJtR5ucMa4vJ0O3" style="width: 800px; height: 401px;"/><br/>
<strong>Anomali MOVEit Vulnerability Dashboard</strong></p>
<p>The Anomali Threat Research team has additionally researched and documented additional details on this vulnerability via Threat Bulletin. The team has also identified over 430 relevant indicators and signatures and several sector specific articles to provide more industry-specific details. The dashboard below highlights some of the insights available to Anomali customers via ThreatStream.</p>
<h2>What can you do about it?</h2>
<p>There are several steps important to reduce the impact of this vulnerability, some of which are also documented in Progress’ knowledge base article <sup>[6]</sup></p>
<p><strong>1. Discover your attack surface.</strong> there are several tools that offer this capability, including Anomali Attack Surface Management <sup>[7]</sup><br/>
<strong>2. Patch the vulnerable systems at the earliest. </strong>The Progress knowledge base <sup>[6] </sup>article captures this in the following steps<br/>
a.Disable HTTP/S traffic to your MOVEit Transfer environment<br/>
b.Patch the vulnerable systems<br/>
c.Enable HTTP/S access to the MOVEit Transfer environment<br/>
<strong>3. Monitor your environment for any known indicators to identify malicious activities.</strong> The Anomali Threat Bulletin captures over 2200 observables that can be used to monitor for malicious activities via a SIEM, firewall, or other technologies. Proactively distribute these indicators to your security controls (firewalls, proxies, etc.) to monitor for any malicious activity.</p>
<p><img alt="" src="https://cdn.filestackcontent.com/IO9fea1lQRGDhkLZNOC6" style="width: 800px; height: 418px;"/><br/>
<strong>Anomali MOVEit Vulnerability Threat Bulletin</strong></p>
<p><strong>4. Hunt for any attacker footprints.</strong> While monitoring looks forward, hunting allows you to look back in the past for any attacker activity. There are several tools that can help you hunt, including Anomali Match <sup>[8]</sup>. Match can help customers search years of data in seconds to understand if any attacker activity has occurred in the past.<br/>
<strong>5. Look beyond yourself. </strong>Monitor your industry activity for any malicious activities. Your threat intelligence platform, including Anomali ThreatStream <sup>[9]</sup>, should be able to assist you in monitoring industry trends. Participate in ISACs to ensure you are sharing intelligence with industry peers to develop a collective defense posture.<br/>
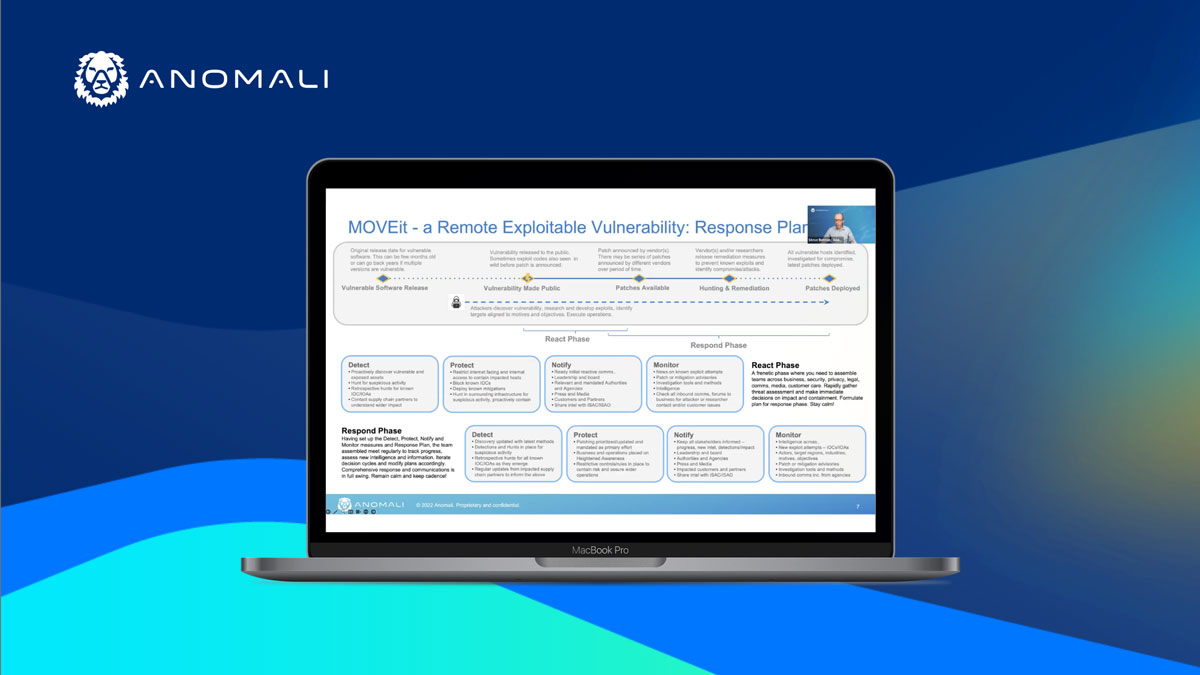
<strong>6. Have a response plan.</strong> Test your response plan, have your communications plans in place, build & test your automated workflows for a timely response.</p>
<h2>Learn More</h2>
<p>Anomali will continue to refine our blogs, bulletins and dashboards as we learn more about MOVEit. </p>
<p>To learn more about this vulnerability, join our threat intelligence experts for a live webinar on June 21, 2023. <a href="{page_6417}">Register here</a> for attending live or to be notified when the on-demand webinar is available. </p>
<p>References</p>
<p>[1] <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-34362">https://nvd.nist.gov/vuln/detail/CVE-2023-34362 </a><br/>
[2] <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-35036">https://nvd.nist.gov/vuln/detail/CVE-2023-35036 </a><br/>
[3] <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-35708">https://nvd.nist.gov/vuln/detail/CVE-2023-35708</a><br/>
[4] <a href="https://www.bleepingcomputer.com/news/security/clop-ransomware-likely-testing-moveit-zero-day-since-2021/">https://www.bleepingcomputer.com/news/security/clop-ransomware-likely-testing-moveit-zero-day-since-2021/</a><br/>
[5] <a href="https://www.helpnetsecurity.com/2023/06/13/cve-2023-34362-exploit/">https://www.helpnetsecurity.com/2023/06/13/cve-2023-34362-exploit/</a><br/>
[6] <a href="https://community.progress.com/s/article/MOVEit-Transfer-Critical-Vulnerability-15June2023">https://community.progress.com/s/article/MOVEit-Transfer-Critical-Vulnerability-15June2023</a><br/>
[7] <a href="{page_6257}">https://www.anomali.com/products/attack-surface-management</a><br/>
[8] <a href="{page_1883}">https://www.anomali.com/products/match</a><br/>
[9] <a href="{page_1882}">https://www.anomali.com/products/threatstream</a><br/>
</pz
FEATURED RESOURCES

Anomali Cyber Watch
Iran's Cyber Arsenal Is Reloading: What CISOs Must Know About the Post-Decapitation Threat Window

Anomali Cyber Watch
Public Sector


