
[updated 6/28/2017 1:29pm ET] We will be updating this page with additional information. Please check back for the latest.
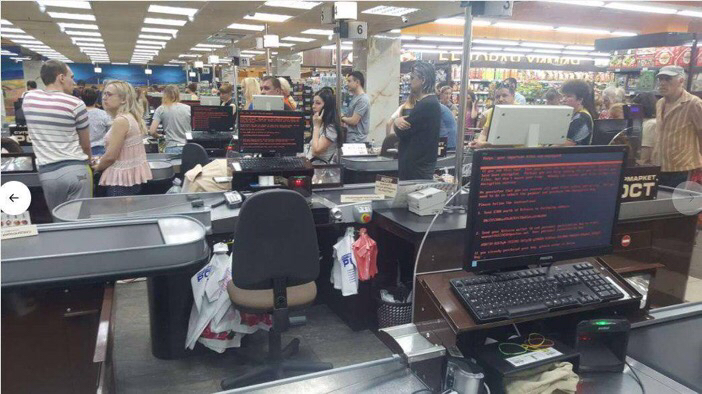
While initial reports have only centered on the Ukraine being hit by a new stream of ransomware known as Petya, this is a global attack. Just like WannaCry, this might be leveraging EternalBlue, which attacks SMB file-sharing services, locking organizations out of their networks and demanding a fee to decrypt files. Bitcoin payments are currently already at $2,000+ already. But it’s essential that victims understand that payment may not actually allow them to access their data, and may just fund hackers to commit further crimes.
The exact measures organizations can implement to mitigate risk depends on the kind of system being protected but there are fundamental actions such as backing up data in the Cloud and on an external hard drive, updating system and patch vulnerabilities, and ensuring everyone is watching where their click. While collaboration across organizations and individuals is also a highly effective method of prevention and mitigation. Sharing experience or research on various types of ransomware helps to dilute their effectiveness.
Petya-Based Ransomware Attack
- Targets hit around the world include but not limited too, Saint-Gobain, Evraz, Rosneft, WPP, Rosneft, Maersk, Ukrainian Central Bank, with Ukraine being particularly hard hit.
- Identified Target Verticals: Harbour terminals, Airports, Electricity grids, Banks, Factories, Insurance companies, Military
- Kaspersky reports that Ukraine and Russia top the list of affected countries so far
- The Petya ransomware variant currently spreading utilizes a single bitcoin payment address for ransom payments and currently has seen 45 payments totally just under 4 BTC ($10,200) - [https://blockchain.info/address/1Mz7153HMuxXTuR2R1t78mGSdzaAtNbBWX]
- Infection spreads via MS17-010 (ETERNALBLUE) just as WannaCry did - also includes support for spreading via PsExec and WMIC however
- This malware can use authentication reuse to spread laterally meaning it can reuse the logged-in user’s credentials from infected systems and spread to other systems those credentials have access to so even if a system is fully patched, infection can still happen
- Adds a scheduled task to reboot the computer some period of time after the system is first infected. Encryption happens after reboot as a fake “chkdisk” screen message appears. Before the reboot, files can be safely backed up if infection is suspected.
- According to Dave Kennedy of TrustedSec, the ransomware spreads very fast - 5k computers in under 10 minutes inside one organization
- Email provider Posteo has blocked the email address used to notify the malware authors that payment has been made. Making a payment to get the files back is definitely not going to be fruitful.
- Reports are that the initial infection came via a compromised update server at Ukrainian accounting software manufacturer, MeDoc, which pushed the malware down when systems checked in for updates. The ransomware spreads rapidly internally once inside an organization. It is unknown at this time how organizations not running MeDoc have become infected.
- The encryption routine encrypts the Master Boot Record of the infected system upon reboot after infection if the user has admin rights on the machine. If the user does not have admin rights, the individual files the user has access to are encrypted and not the Master Boot Record.
- The malware includes several evasion techniques including long sleeps to avoid analysis by researchers
- Creating a file named, "C:Windowsperfc.dat" and setting it to read-only will prevent infection even on systems that would otherwise be vulnerable. This is an onerous task to be done on very single system but organizations can leverage tools like Group Policy (as suggested by Binary Defense) to automate deployment to prevent infection by this Petya variant.
- A researcher at Kaspersky reported that additional infection vectors included the use of at least one watering hole domain in Ukraine
FEATURED RESOURCES

Iranian Cyber Retaliation Imminent: Ceasefire Collapse and Critical VPN Vulnerability Create Perfect Storm



