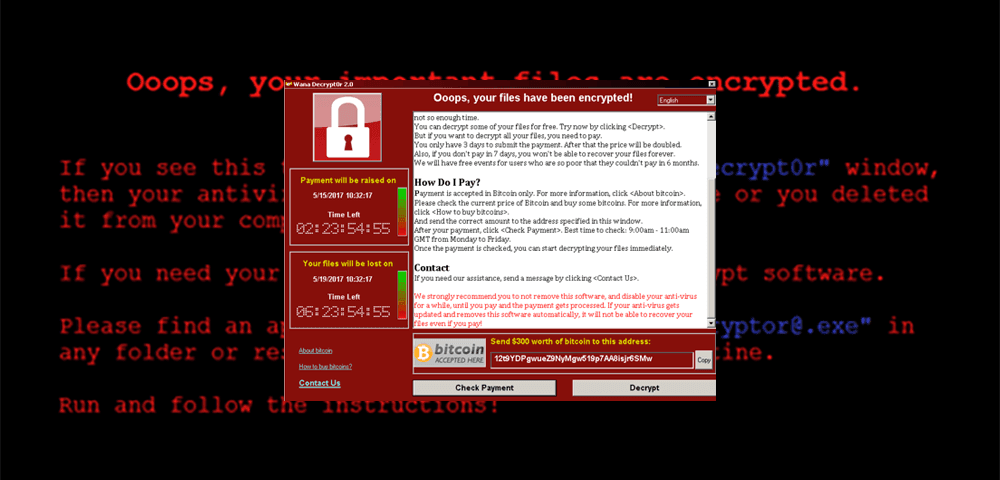

<p>NOTE: Anomali is continuing to investigate and monitor the WanaCry worm and will update this page as we have more information to share. Visit <a href="http://www.anomali.com/wanacry" target="_blank">www.anomali.com/wanacry</a> for the latest.</p><p>On the morning of Friday May 12th a new ransomware threat emerged infecting tens of thousands of computers across the globe at an alarming rate.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/MZKZyYKxS3iAy4jLyi0k"/> <img alt="" src="https://cdn.filestackcontent.com/cGYZtAQsQsWnr1NRATnn"/></p><p style="text-align: center;"><em>Figure 1 - WanaDecrypt0r 2.0 Pop up window and splash screen.</em></p><p>Named “Wana Decrypt0r 2.0” (a.k.a “WannaCry”, "WCry"), the ransomware was unique in that it appeared to be one of the first to have the ability to spread to other (Windows) computers on its own, similar to malware of the past like <a href="https://en.wikipedia.org/wiki/Conficker" target="_blank">Conficker</a>. This was starting to look like the first case of worm functionality being integrated into ransomware and indeed it was, sort of.</p><p>It was later determined that the ransomware was spreading on its own by scanning for systems vulnerable to <a href="https://technet.microsoft.com/library/security/MS17-010" target="_blank">MS17-010</a>, exploiting them and then using a <a href="https://arstechnica.com/security/2017/04/10000-windows-computers-may-be-infected-by-advanced-nsa-backdoor/" target="_blank">recently leaked NSA backdoor</a> to install the ransomware on the system.</p><p>A lot of the hype surrounding the spreading component of the ransomware was due to the fact it was using an exploit against MS17-010, a vulnerability in Microsoft’s SMB protocol that resulted in continued spread of the ransomware. It is also a big deal because the exploits used by the malware came from the recent <a href="https://github.com/misterch0c/shadowbroker/" target="_blank">“Lost In Translation” dump</a> leaked by the infamous Shadow Brokers, which included cyber-attack tools developed by the NSA. In this case, ETERNALBLUE was the name of the exploit included in the dump by the Shadow Brokers.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/S6Ii4vkFRrG4QhxFoQLw"/> <img alt="" src="https://cdn.filestackcontent.com/PK5ebPDSTByTCykNJSMU"/></p><p style="text-align: center;"><em>Figure 2 – FuzzBunch exploitation framework containing exploit targeting MS17-010, leaked by the Shadow Brokers.</em></p><p>While the security community at large is still investigating the worm, ransomware and the initial infection vector, details have begun to emerge giving us more insight into how the malware works and what can be done to stop it.</p><h2>Worm Gives Birth</h2><p>Although it was not clear at first, there were 2 malware components involved in the infections. The first being the main malware binary that drops the ransomware. The sample we looked at had md5 <a href="https://www.virustotal.com/en/file/24d004a104d4d54034dbcffc2a4b19a11f39008a575aa614ea04703480b1022c/analysis/" target="_blank">DB349B97C37D22F5EA1D1841E3C89EB4</a>. Time stamp [4CE78ECC] - Nov 20, 2010 9:03:08</p><p>This is the malware binary that will call out to the domain “iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea[.]com” to see if it gets a response and determine if it should continue execution or not. Fortunately, the domain was sinkhole’d the same day it was discovered effectively stopping further ransomware infections since the malware would just exit as soon as it got a response from that domain. This was not the ransomware component, it was the dropper.</p><p>Using the tool ResourceHacker you can see actually see and extract the resource section containing the malware payload for closer analysis.</p><p>The first one is the actual WanaDecrypt0r 2.0 ransomware</p><p>MD5: <a href="https://www.virustotal.com/en/file/ed01ebfbc9eb5bbea545af4d01bf5f1071661840480439c6e5babe8e080e41aa/analysis/" target="_blank">84C82835A5D21BBCF75A61706D8AB549</a><br/> Time stamp [4CE78F41] - Nov 20, 2010 9:05:05</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/MO0PK7seRciS0xVlAx2R"/></p><p style="text-align: center;"><em>Figure 4a – File header of the ransomware hidden inside the worm.</em></p><p>The next resource section of interest comes from the ransomware binary, it holds a password protected .zip containing additional files used by the ransomware. The zip file has md5 B576ADA3366908875E5CE4CB3DA6153A.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/qpotSOdtRWKG2pCoqgVQ"/></p><p style="text-align: center;"><em>Figure 4b – “PK” File header visible in resource section of main malware binary.</em></p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/v1wbhMTBe8lNnQyiAZ2g"/></p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/FbwkQfRQyy8yX1nglxtg"/></p><p style="text-align: center;"><em>Figure 5 – Zip password “WNcry@2ol7” was clearly visible during analysis.</em></p><h2>Network</h2><p>The malware is designed so that once the system is infected, it will scan the local network and internet for systems that are listening on TCP port 445, these systems will then be checked to ensure the presence of the backdoor, known as DOUBLEPULSAR, through which it will actually send the ransomware to be installed, additional analysis is available <a href="http://blog.talosintelligence.com/2017/05/wannacry.html?m=1" target="_blank">here</a> and <a href="https://blog.malwarebytes.com/threat-analysis/2017/05/the-worm-that-spreads-wanacrypt0r/" target="_blank">here</a>.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/rXWyCJW1R6ehUYRwD9Sj"/></p><p style="text-align: center;"><em>Figure 6 – An infected host scanning for IP’s on TCP 445.</em></p><p>Once the system gets infected with the ransomware, its business as usual with the ransomware pop-up windows and threats of data loss.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/68QyzxKSQ1mAk7JfEA32"/> <img alt="" src="https://cdn.filestackcontent.com/1uEEquWuTuqKXs8IP5S5"/></p><p style="text-align: center;"><em>Figure 7 – WanaDecrypt0r 2.0 on the desktop.</em></p><p>The ransomware will periodically check to see if payment was made, this communication is done using TOR. Since the ransomware uses TOR to communicate, network communication will be encrypted and potentially able to skirt by detection signatures unless specific detections for TOR network traffic are enabled.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/7o6UXWQMTviIRHsBB5nw"/></p><p style="text-align: center;"><em>Figure 8 – Ransomware communicating to TOR nodes on ports 9001, 443 & 80.</em></p><table class="table table-striped" style="width: 250px;"><tbody><tr><td>37.221.162.226</td><td>9001</td></tr><tr><td>62.210.123.24</td><td>443</td></tr><tr><td>81.2.209.10</td><td>80</td></tr><tr><td>94.242.59.147</td><td>9001</td></tr><tr><td>131.188.40.189</td><td>443</td></tr><tr><td>163.172.146.232</td><td>9001</td></tr></tbody></table><p style="text-align: center;"><em>Figure 9 – Example TOR traffic observed</em></p><p>As you might have guessed, blocking TOR communication can help mitigate the threat and is also good hygiene for business networks. Lists of active TOR exit nodes are readily available on the internet as well as from most threat Intelligence platforms, including <a href="https://www.anomali.com/products/threatstream">Anomali ThreatStream</a>.</p><p>Checking your logs for activity to TOR nodes can be helpful in locating hosts that may be infected or using TOR to evade network policy, potentially putting your enterprise at risk.</p><h2>Conclusion</h2><p>If you want to stay one step ahead of threats like WanaCry, it is critical you gauge your exposure levels and put mitigations in place so that infections can be avoided. If not properly protected, these types of attacks can quickly grow out of control and overwhelm security teams, bringing business to a halt (as we saw this past Friday).</p><p>As has been said over and over, vulnerable systems must be patched in order to reduce risk.</p><p>Instead of waiting for infected systems to show up as security alerts, scanning for vulnerable systems on your network ahead of time can help identify potential targets, this can be done with tools like Nessus which will report if the system is vulnerable.</p><p style="text-align: center;"><img alt="" src="https://cdn.filestackcontent.com/PW3oAo8S9GGTCZrDzqmC"/></p><p style="text-align: center;"><em>Figure 10 – Example of Nessus scan results indicating a potentially vulnerable host.</em></p><p>Additionally, ensuring that endpoints are not exposed directly to the Internet is an important general mitigation that would help avoid infection in the case of WanaCry.</p><h2>What's Next</h2><p>Now that weapons-grade cyber attack tools are in the wrong hands, it is clear that tools and techniques previously reserved for use by nation states are being integrated into crimeware for profit. This means you can expect to see more of these exploits and tools leveraged in future attacks, each one likely surpassing the previous in sophistication and stealth as threat actors build on lessons learned from previous attacks. Phishing, exploit kits, and watering holes are all common attack vectors that could potentially leverage these weapons-grade tools in order to continue delivering malicious payloads like WanaCry. There will be new versions of WanaCry that attempt to overcome the weaknesses in what has been observed so far. It will be up to organizations to learn from the security weaknesses that led to this attack and stay abreast of future developments to prevent infection in their environments.</p>
FEATURED RESOURCES

Anomali Cyber Watch
Iran Declares Ceasefire Over: Cyber Retaliation Window Opens for Critical Infrastructure

Anomali Cyber Watch
Public Sector


