Weekly Threat Briefing: Watch Out for Game of Thrones Phishing Scams as the Final Season Arrives
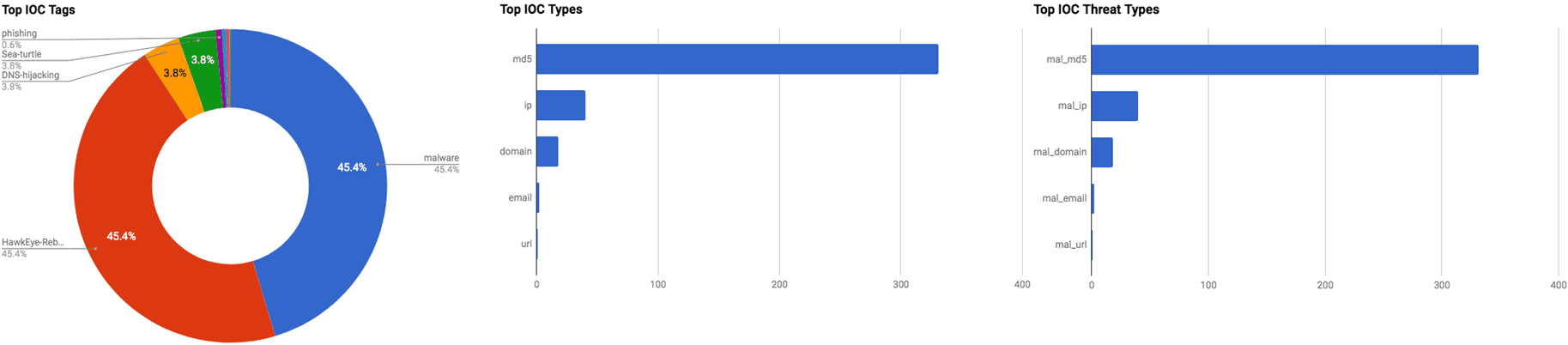

The intelligence in this week’s iteration discuss the following threats: Brute force, Data breach, Data theft, Phishing, Personally Identifiable Information, Ransomware, Threat group, Vulnerabilities, and Zero-day. The IOCs related to these stories are attached to the Community Threat Briefing and can be used to check your logs for potential malicious activity.
Trending Threats
Watch Out for Game of Thrones Phishing Scams As The Final Season Arrives (April 22, 2019)
Check Point researchers have identified a phishing campaign themed after the HBO series “Game of Thrones,” with the campaign’s objective being the theft of user data. The emails attempt to direct recipients to Game of Thrones websites that purport to be fan pages, gaming sites, and online shopping stores. Some of the websites are designed to steal user data such as email addresses and phone numbers to be used in additional spam campaigns. The other types of websites, such as the online stores, are designed to steal a user’s credit or debit card information.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] User Execution (T1204) | [MITRE ATT&CK] Spearphishing Link (T1192)
Easter Attack Affects Half a Billion Apple iOS Users via Chrome Bug (April 18, 2019)
The threat group called “eGobbler” is believed to be responsible for conducting one of “the top three massive malvertising [malicious advertising] campaigns” observed in the past 18 months that has impacted 500 million user sessions, according to Confiant researchers. Clicking upon one these malvertisements or pop-ups will begin the downloading process for a malicious payload that is used hijack user sessions. This campaign is exploiting an unpatched bug in the Google Chrome browser for iOS that can allow the actors to hijack user sessions. eGobbler’s objective is to utilize the session hijacking to redirect mobile web browser users to another site or used to display a pop-up that cannot be exited out of. Researchers observed that 35% of all the advertisements “are served through sandboxed cross-origin iframes” and that the actors are primarily using the “.world” top level domain, the latter which could help identify this campaign. eGobbler is primarily targeting users in the US with this campaign beginning on April 6 and composed of eight separate campaigns with the malvertisements lifespan lasting 24-48 hours.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] User Execution (T1204)
Oracle Issues Nearly 300 Patches in Quarterly Update (April 18, 2019)
In the latest Critical Update Patch, Oracle has issued security updates for 297 vulnerabilities. The patches were issued for 110 products on April 16. Some of the products that contained vulnerabilities include the following: Fusion Middleware product set with 42 vulnerabilities. Other products affected are Oracle Communications Applications with 26 security fixes, and the Oracle E-Business Suite, with 35 security fixes, with the majority for remotely exploitable bugs. Oracle Retail Applications received 24 security fixes, with 20 open to potential remote exploitation without authentication.
Click here for Anomali recommendation
CyberInt Reports: Suspected Russian-speaking Threat Actors “TA505” Continues Cybercrime Spree Against Global Retailers and Financial Institutions (April 17, 2019)
CyberInt Research Labs have observed continuing campaigns conducted by the financially-motivated threat group called “TA505.” The group, which has been active since at least 2014, primarily uses spear phishing emails distributed to financial institutions and retail companies to compromise organizations with Remote Access Tools (RATs) such as “Remote Manipulator System” (RMS). Using a legitimate RAT can assist the group in remaining undetected on a network because malicious traffic may appear authentic while actually it is malicious activity conducted by the threat group.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] User Execution (T1204) | [MITRE ATT&CK] Remote Access Tools (T1219)
Over 100 Million Justdial Users’ Personal Data Found Exposed On the Internet (April 17, 2019)
The Indian local search company, “Justdial,” which is India’s largest local search company, was observed to be leaking its customers’ Personally Identifiable Information (PII), according to security researcher Rajshekhar Rajaharia. Rajaharia discovered that Justdial was using an API endpoint that contained a database storing customer data that was publicly accessible since at least mid-2015. The information observed to be stored in the database consists of: address, cell phone number, company name, date of birth, email address, gender, name, occupation, photo, and any other data a user provided to Justdial.
Click here for Anomali recommendation
DNS Hijacking Abuses Trust In Core Internet Service (April 17, 2019)
A new DNS hijacking campaign, dubbed “Sea Turtle,” has been discovered targeting private and public organisations primarily located in the Middle East and North Africa, according to researchers from Cisco Talos. The threat actors behind this campaign initiated the attacks by either exploiting registered vulnerabilities (CVE-2009-1151, CVE-2014-6271, CVE-2017-3881, CVE-2017-6736, CVE-2017-12617, CVE-2018-0296, CVE-2018-7600) or spear phishing emails. Once obtaining initial access, the threat actor would modify the NS records for the target organisations to direct users to a malicious DNS server that provided actor-controlled responses for all DNS queries. They then established a Man-in-the-Middle framework to impersonate legitimate services to steal credentials, and once the threat actor obtained the credentials, they directed the user to the legitimate service to evade detection. The affected industries include energy organisations, information technology firms, intelligence agencies, internet service providers, military organisations, ministries of foreign affairs, registrars, and telecommunications organisations.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Attachment (T1193) | [MITRE ATT&CK] Exploitation for Privilege Escalation (T1068) | [MITRE ATT&CK] Exploitation for Defense Evasion (T1211)
Potential Targeted Attack Uses AutoHotkey and Malicious Script Embedded in Excel File to Avoid Detection (April 17, 2019)
A phishing campaign has been observed by researchers from Trend Micro that contain a macro-enabled document that exploits the legitimate script engine, “AutoHotKey.” AutoHotKey will run a malicious script that establishes a connection to a Command and Control (C2) server which then executes an additional script in response to commands received from the C2. The C2 can also send commands to take screen captures of the infected device, obtain device information, as well as install the Remote Access Tool (RAT), “TeamViewer,” that can give the threat actor remote control over the system.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Remote Access Tools (T1219) | [MITRE ATT&CK] Spearphishing Attachment (T1193) | [MITRE ATT&CK] Scripting (T1064)
Internet Explorer Browser Flaw Threatens All Windows Users (April 17, 2019)
Researcher John Page, known by the alias “hyp3rlinx,” has published Proof-of-Concept (POC) code for a vulnerability in Windows’ “Internet Explorer” (IE) web browser. The vulnerability, which some refer to as a “zero-day vulnerability because it is a known weakness for which there is no patch,” resides in the way IE handles its default web page archiving format, MHTML (MHT) files. A threat actor could distribute a malicious MHT file to a Windows 7, Windows 10, or Windows 12 R2 system because they by default would open them via IE. The MHT file could also contain malicious XML markup to prevent IE from showing a security warning. If opening of the MHT file through IE this takes place, a remote actor could gain the ability the steal Local files and “conduct reconnaissance on locally installed Program version information.” Even on Windows 10, there can be a short setup process that takes place when the machine is booted for the first time, thus potentially leaving all Windows users at risk of this vulnerability, albeit a slight and short timeframe for first-time startup.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] User Execution (T1204)
Wipro Confirms Major Breach Investigation (April 17, 2019)
The Indian IT services giant, “Wipro,” gas announced that they have recently observed suspicious activity in some employee accounts following a phishing campaign targeting users. The company stated that following a comprehensive investigation, they have remediated the incident and attempted to mitigate any impact the breach might have caused. At least eleven or twelve customers of Wipro are affected.
Click here for Anomali recommendation
NamPoHyu Virus' Ransomware Targets Remote Samba Servers (April 16, 2019)
A new ransomware family, “NamPoHyu Virus” or “MegaLocker Virus,” has been observed infecting users via vulnerable Samba servers. The ransomware searches for accessible servers, and attempts to brute force the passwords. If it successfully brute forces the device, it then remotely encrypts the files on the server and displays a ransom note. Users are instructed to email a provided address for payment instructions, which are $250 USD in Bitcoin for individual users or $1000 USD in Bitcoin for companies.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Brute Force (T1110)
A Hacker Has Dumped Nearly One Billion User Records Over the Past Two Months (April 15, 2019)
A threat actor by the name of “Gnosticplayers” has breached over 44 companies and stolen almost one billion records. The actor has put up approximately 932 million records across five different release rounds, selling them on various Dark Web marketplaces for Bitcoin. The most recent companies to have their data published by the threat actor include Evite, iCracked, Mindjolt, Moda Operandi, Wanelo, and Yanolja.
Click here for Anomali recommendation
New HawkEye Reborn Variant Emerges Following Ownership Change (April 15, 2019)
Researchers from Cisco Talos have observed a new variant, “Reborn v9, Version 9.0.1.6,” of the keylogger and information-stealing malware, “HawkEye,” being distributed via phishing emails to various organisations. The emails are themed around invoice documents, bills, statements, order confirmations, or other corporate functions, and contain an attached Excel spreadsheet that contains a macro-enabled document. The malicious spreadsheet exploits registered vulnerability, “CVE-2017-11882,” that allows for arbitrary code execution in Microsoft Office and executes shellcode. Upon execution, the HawkEye keylogger is installed on the infected machine and steals information such as system information, passwords from common web browsers and Minecraft, clipboard content, and can take screenshots from the desktop and webcam.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Remote Access Tools (T1219) | [MITRE ATT&CK] Spearphishing Attachment (T1193) | [MITRE ATT&CK] PowerShell (T1086) | [MITRE ATT&CK] Obfuscated Files or Information (T1027)
New Zero-day Vulnerability CVE-2019-0859 in win32k.sys (April 15, 2019)
A new zero-day vulnerability, registered as “CVE-2019-0859,” in Windows’ “win32k.sys” has been discovered by researchers from Kaspersky Lab. The vulnerability is a use-after-free flaw that lies in the “CreateWindowEx” function, specifically the “WM_NCCREATE” callback. A threat actor could exploit the callback flaw which could then allow them control over the free memory block and then execute PowerShell code that ultimately makes an HTTP reverse shell to gain access to the entire infected system.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] PowerShell (T1086) | [MITRE ATT&CK] Hooking (T1179) | [MITRE ATT&CK] Scripting (T1064)
FEATURED RESOURCES

Iran Declares Ceasefire Over: Cyber Retaliation Window Opens for Critical Infrastructure



