
Early detection of suspicious activity is preventative rather than reactive. Using a honeypot can keep your data and the people who would be affected by a security event safe. ShockPot collects information that can be used in advance of a devastating ShellShock attack.
Many servers are run on Mac or Linux, which use a program called Bash. Bashbugs were introduced in less than 24 hours after a vulnerability was announced. ShellShock is one of these viruses which exploit a vulnerability in one of the operating computer’s ports and then enters unauthorized commands. This program, which is used to enter commands was discovered in September 2014 to create a port through which hackers can attack. Namely, the computer is made to spread the virus to other networks by creating viral botnets. These commands can be deployed individually by the hacker, making ShellShock more akin to a back door than a wild-running virus. Having more control over the proliferation allows attackers to be stealthier than they were with earlier Trojans.
Once built, botnets can be commanded to drive traffic to a specific network. A deluge of traffic which can cripple a network is known as a distributed denial of service attack. The target of the DDoS is the primary victim, with the others infected with Bashbugs being used as a means to an end. Early reports of this development in malware had come from intelligence gathered via honeypots.
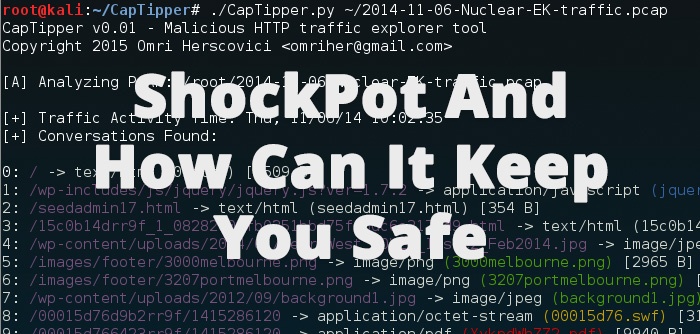
Using a decoy environment, honeypots are security tools which can log traffic sources for investigation and they divert hacking behavior away from actual assets. ShockPot is different from static malware detection programs. Rather than scan for one particular profile independently, it works with the Modern Honey Network.
Information gathered by honeypots is remitted to the MHN, which keeps a list of IP addresses associated with suspicious activity as well as other indicators of compromise (IoC).
Types of warning signs detected:
- Virus signatures
- Outgoing traffic to infected web domains
- Incoming traffic from known bad domains
- New and unusual files or processes
- Activity on decoy or dormant staff logins
- Unauthorized access of or changes to security settings
- Suspicious password resets or unexplained login failures
- Correspondence to an unused email address
- Malware or virus activity
Built on open-source platforms, honeypots are the most affordable means of collecting threat intelligence data. When examined individually these signs are dismissible, but when examined as part of a bigger picture, patterns and trends emerge. All of the data reported from every honeypot on the MHN creates small pieces of a bigger picture which illuminate threats on the horizon.
Respond by leveraging the intelligence from your threat reports. Once properly configured, ShockPot will be able to distinguish firewall activity, antimalware, and other routine legit internal traffic as “noise” which should be excluded from incident reports. Since a honeypot doesn’t have any legitimate traffic, information from all remaining activity should be explored as a possible breach attempt.
The result of hosting and maintaining a honeypot like ShockPot is a reassurance. Knowing what is lurking in the dark will help you to sleep at night.
Download the Security Intelligence and Information Sharing Strategy whitepaper and learn more about the new approach to threat intelligence using trusted collaboration.
FEATURED RESOURCES

Iranian Cyber Operations Enter Most Dangerous Phase: Physical Destruction Without Malware Under Ceasefire Cover



