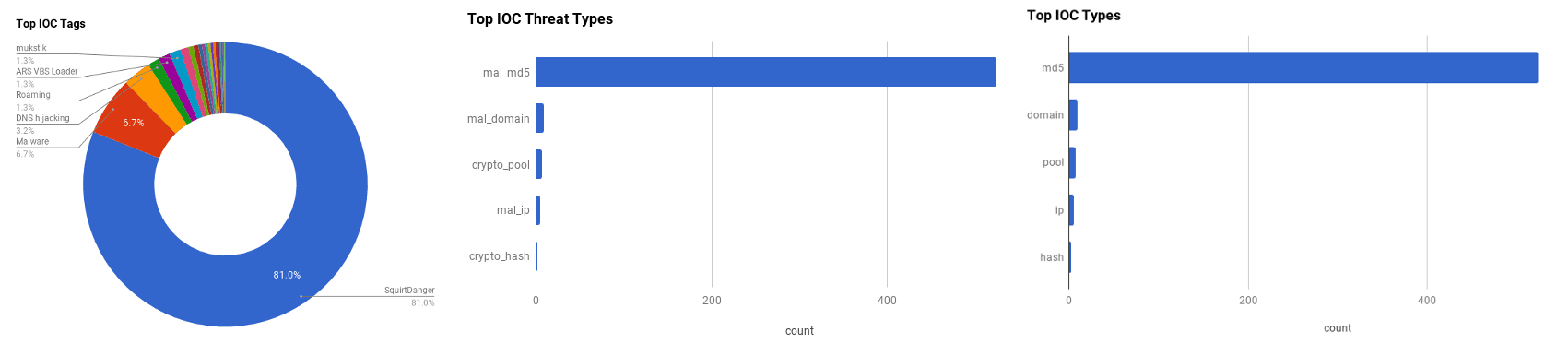

The intelligence in this week's iteration discuss the following threats: Adblocker Malware, APT28, ARS VBS Loader, Desert Scorpion, DNS Hijacking, Mukstik, PBot, Roaming Mantis, SquirtDanger, Stresspaint, and XiaoBa. The IOCs related to these stories are attached to the WTB and can be used to check your logs for potential malicious activity.
Trending Threats
Energetic Bear/Crouching Yeti: attacks on servers (April 23, 2018)
Due to recent advisories by both the United States Computer Emergency Readiness Team (US-CERT) and the United Kingdom National Cyber Security Centre (NCSC), Kaspersky Labs have released information detailing servers that have been compromised and used as attack platforms by the group. The targeted countries include Germany, Greece, Russia, Turkey, Ukraine, United Kingdom, and the United States of America. The compromised servers range across many different industries, and were either used for watering hole attacks in order to reach their main targets, auxiliary purposes, or for hosting malware and logs. The watering hole servers infected targets by having an injected link in the webpage or a JavaScript file. The link would direct to an IP address using "file://", which initiates a request to fetch the resource over Server Message Block (SMB), which allows APT28 to harvest the victims IP, username, domain name, and NTLM hash of the victim's password. Other servers were used for platforms to conduct scanning attacks using tools such as Nmap, Sqlmap, and Commix. It appears that the scanning attacks were conducted to further expand APT28's water hole hosting infrastructure.
Click here for Anomali recommendation
Botnet Muhstik is Actively Exploiting Drupal CVE-2018-7600 in a Worm Style (April 20, 2018)
After the public announcement of a remote code execution vulnerability, registered as "CVE-2018-7600," for the "Drupal" Content Management System (CMS), a large number of scans against the internet have been detected trying to exploit this vulnerability. After noticing worm-like propagation behaviour, NetLab researchers have named the "botnet" responsible for the attacks as"Mukstik," after a word that appears in its binary file and Internet Relay Chat (IRC) channel. The botnet tries to infect servers by scanning TCP ports 80, 8080, 7001, 2004, and attempts to use seven different exploit payloads on each. When an exploit is successful, it will report back to a "Command and Control" (C2) server, ready to receive commands.
Click here for Anomali recommendation
SSH Worming CryptoMiner Targets Vulnerable WebLogic Instances (April 19, 2018)
Attackers have created a "Cryptominer" script that exploits "CVE-2017-10271" to infect vulnerable "WebLogic" instances, then tries to propagate via Secure Shell (SSH) according to Alert Logic researchers. After infecting a vulnerable WebLogic instance and installing a modified "XMRig" miner, the script attempts to identify every SSH key on the host by checking the ".ssh" directory and looking for directly referenced SSH certs in all users bash history. The script also checks for recently accessed SSH hosts and netstat to identify potential targets. The attacker iterates across all discovered users, keys, and target hosts and attempts to install the worm onto the target machine. A tactic that the attacker employs is to change the landing page that delivers the malware to an FBI takedown notice, this is to make incident responders believe that the site has been neutered.
Click here for Anomali recommendation
Over 20 Million Users Installed Malicious Ad Blockers From Chrome Store (April 19, 2018)
Five malicious "ad blocker" extensions have been discovered on the "Google Chrome Store" that have been installed by over 20 million people. The extensions allowed the creators to steal information that victims entered into any website they visit, which could include usernames, passwords, and card details. All the extensions were copycat versions of legitimate Ad-blockers. The creators used popular keywords in the names and descriptions in order to rank their position higher in search results.
Click here for Anomali recommendation
PBot: a Python-based adware (April 18, 2018)
Malwarebytes researchers have discovered a Python-based adware, called "PBot" or "PythonBot," that is dropped by the RIG exploit kit. The malware comes under the disguise of software that blocks cryptocurrency miners, but has nothing in common. The malware performs "Man-in-the-Browser" (MITB) attacks and injects scripts into legitimate website pages. PBot is able to control whatever contents are displayed on the browser. Legitimate certificates on sites with HTTPS are replaced with fake certificates. There is a possibility that PBot will be configured in the future, from harmless ads, to display more malicious pages, such as phishing.
Click here for Anomali recommendation
Stresspaint Malware Targeting Facebook Credentials (April 18, 2018)
Radware's research team recently detected malicious activity attributed to a threat group collecting user credentials and payment details from Facebook users worldwide. The group sends phishing emails that download a painting application called "Relieve Stress Paint" that drops a malware dubbed "Stresspaint" in the background. At the time of this writing, the group has infected over 40,000 users. The malware copies the content of Chrome browser cookies and login data files. When saved login credentials or Facebook cookies are found, they are encrypted and sent to the command and control server.
Click here for Anomali recommendation
SquirtDanger: The Swiss Army Knife Malware from Veteran Malware Author TheBottle (April 17, 2018)
Palo Alto Networks Unit 42 researchers have released information on a new malware family, dubbed "SquirtDanger," based on the name of a DLL file used in the attacks. The malware is believed to have been created by the Russian malware author called "TheBottle." SquirtDanger is a botnet malware family written in C#. Once run on a system, it creates a scheduled task to run every minute. It uses raw TCP connections to communicate to a remote Command and Control (C2) server. The malware can take screenshots, exfiltrate files, steal browser passwords, steal cryptocurrency wallets, swap identified wallets in the victim's clipboard, and execute files, among others. The malware is likely delivered via software that has been illegally copied and trojanized with the malware.
Click here for Anomali recommendation
Ransomware XIAOBA Repurposed as File Infector and Cryptocurrency Miner (April 17, 2018)
The "XiaoBa" ransomware has been repurposed to be a File Infector and Cryptocurrency miner, according to Trend Micro researchers. The file infector injects malware binaries to run the malware code. It also injects ".html" and ".htm" files to run the "Coinhive" mining script. Variants have also been found to include the "XMRig" miner. XiaoBa also modifies the "hosts" file to redirect anti-virus and forensics related URLs to localhost. The file infector can infect an executable of any size because there are no limits set. There are also no markers of infected files, which allows it to infect itself multiple times. Once XiaoBa infects a file, the code of the host file will not execute, this could affect critical files, rendering the victim's system unstable.
Click here for Anomali recommendation
RAT Gone Rogue: Meet ARS VBS Loader (April 16, 2018)
A new variant of the malicious loader called "ARS VBS Loader," which is based on the "SafeLoader VBS" loader that was sold and later leaked on Russian underground forums, has added Remote Access Trojan (RAT) feature to its capabilities, according to Flashpoint researchers. The ARS VBS Loader malware is being distributed via malspam emails that are themed around personal banking, package shipments, and toll road notifications. If a malspam recipient interacts with the malicious attachment that contains the loader, a recipient could be infected with multiple different malwares, such as the information-stealing malware "AZORult."
Click here for Anomali recommendation
Advisory: Russian State-Sponsored Cyber Actors Targeting Network Infrastructure Devices (April 16, 2018)
The U.S. Department of Homeland Security (DHS) and Federal Bureau of Investigation (FBI) in coordination with the U.K.'s National Cyber Security Centre (NCSC) have issued a join Technical Alert (TA). This TA discusses how Russian state-sponsored threat actors are targeting network infrastructure devices such as routers, switches, firewall, and Network-based Intrusion Detection System (NIDS) devices. The Russian threat actors are engaging in this activity "to conduct man-in-the-middle attacks to support espionage, extract intellectual property, maintain persistent access to victim networks, and potentially lay a foundation for future offensive operations."
Click here for Anomali recommendation
Roaming Mantis Uses DNS Hijacking to Infect Android Smartphones (April 16, 2018)
Japanese media organization began reporting about DNS hijacking attacks that were targeting routers in Japan which subsequently redirected user to malicious IP addresses in attempts to infect users with banking trojans. Kaspersky Lab researchers looked deeper into these attacks and found malware, dubbed "Roaming Mantis," is behind the DNS hijacking attacks. Once the malware has infected a router it can redirect any user using the router trying to visit a website to one of the actor's choosing. The malicious website, once visited, displays a dialogue box that requests the user update to the latest version of Chrome for a better browsing experience. If this fake update is downloaded, a user will have granted permissions to an Android Application Package (APK) that can conduct additional malicious activity, such as stealing information on an infected device.
Click here for Anomali recommendation
Lookout Finds New Surveillanceware in Google Play with Ties to Known Threat Actor Targeting the Middle East (April 16, 2018)
A new, targeted mobile malware campaign has been observed to be distributing surveillance malware (surveillanceware) via an application in the Google Play Store, according to Lookout researchers. The malware is called "Desert Scorpion" and was able to infect users by hiding in an application called "Dardesh (Unleashed)." Researchers note that the application ties together Desert Scorpion with another surveillanceware called "FrozenCell;" these malwares are believed to be in active development by one threat group dubbed "APT-C-23." The Dardesh application masquerades as a messaging application that itself is being distributed by phishing emails and messages, specifically via Facebook.
Click here for Anomali recommendation
FEATURED RESOURCES




