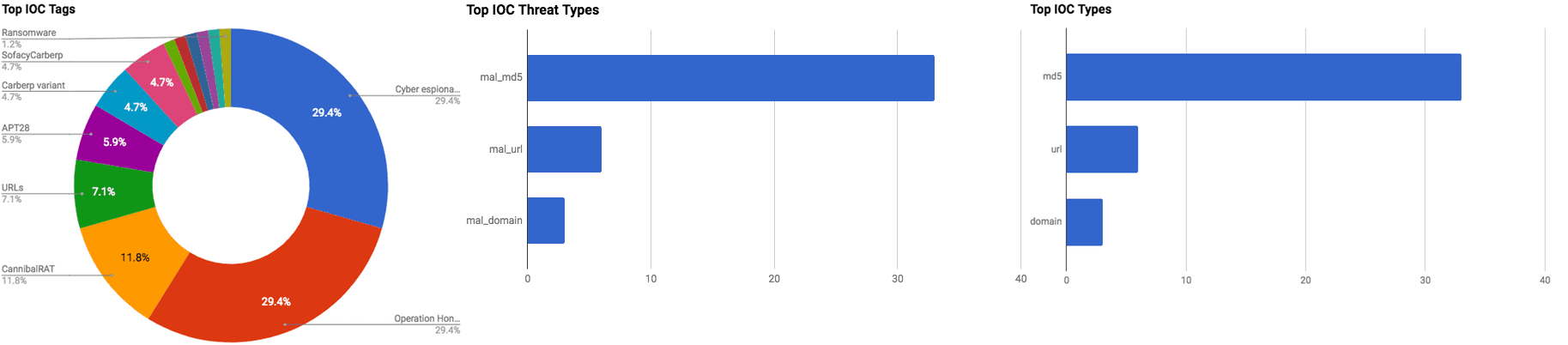

The intelligence in this week’s iteration discuss the following threats: APT, Cyber espionage, Credit and debit card theft, Data breach, Data theft, DDoS attacks, Malicious applications, Misconfigured database, Mobile malware, POS malware, Spear phishing, and Targeted attacks. The IOCs related to these stories are attached to the WTB and can be used to check your logs for potential malicious activity.
Trending Threats
Payment Card Breach Hits Some Applebee’s Restaurants (March 5, 2018)
On Friday, March 2, 2018, an Applebee’s restaurant owner and operator company “RMH Franchise Holdings” (RMH) released a notice in which it confirmed that some of the restaurants it operates were compromised with Point of Sale (POS) malware. RMH became aware of the incident on February 13 and subsequently launched an investigation. This incident is reported to have affected approximately 160 Applebee’s locations throughout 14 states in the U.S. The credit card data-stealing malware was present, in most restaurant’s cases, on POS systems between December 6, 2017 and January 2, 2018. The malware was designed to steal credit and debit card numbers, card verifications codes, and expiration dates. At the time of this writing, RMH has stated that the incident has been contained.
Click here for Anomali recommendation
McAfee Uncovers Operation Honeybee, a Malicious Document Campaign targeting Humanitarian Aid Groups (March 2, 2018)
McAfee Advanced Threat Research analysts have published a report regarding a new malicious campaign, dubbed “Operation Honeybee,” that appears to have first begun in August 2017. The threat group behind this campaign is distributing spear phishing emails that use Word compatibility messages to attempt to trick the recipient into opening them. On January 17, researchers observed the actors behind this campaign distributing Word documents with a malicious Visual Basic macro with the objective to infect individuals with a new variant of the “SYSCON” backdoor. This campaign is targeting humanitarian groups and themes there spear phishing email accordingly.
Click here for Anomali recommendation
GitHub Survived the Biggest DDoS Attack Ever Recorded (March 1, 2018)
GitHub, the web-hosting and information sharing websites, managed to thwart the largest Distributed Denial-of-Service (DDoS) attack that has ever been recorded. The attack took place on Wednesday, March 1, 2018, at around noon (EST) with an astronomical 1.35 terabits per second (Tbps). The threat actors behind the attack used an increasingly popular DDoS method that used “Memcached” servers that were mostly owned by legitimate businesses and organizations. The Memcached servers are used to speed up networks and websites, however, they were not meant to be exposed publicly on the internet where anyone could query and use them. Researchers note that, at the time of this writing, approximately 100,000 Memcached servers are exposed on the internet.
Click here for Anomali recommendation
Equifax finds additional 2.4 million in U.S. impacted by 2017 data breach (March 1, 2018)
The U.S.-based credit reporting agency “Equifax” has issued a statement regarding the total number of individuals who were affected in the 2017 breach, which is considered by many to be largest data breach in history. In the statement, the company said that an additional 2.4 million Americans were affected by the breach. These additional individuals had “less” Personally Identifiable Information (PII) affected with driver license information reported as being not affected. However, credit card information and Social Security Numbers still be affected. Overall, approximately 147.9 million people in the U.S. were affected by last year’s breach.
Click here for Anomali recommendation
French news site L’Express exposed reader data online, weeks before GDPR deadline (March 1, 2018)
Mickey Dimov, an employee of an unnamed major defense contractor, discovered in January 2018 that a server hosting a “MongoDB” database belonging to the Paris-based magazine “L’Express’ was misconfigured. The database was configured in a way that it was publicly accessible to anyone. Dimov contacted the magazine informing them of the status of their database in January, however, it took until late February for the database to be secured. During the time Dimov was aware of the exposed database, he witnessed multiple attempts by threat actors to steal the data in attempts to hold it for ransom; one of which succeeded. The database contained approximately 60 gigabytes of data associated with 693,000 of the magazine’s readers, and other sensitive information regarding the magazine’s online operations.
Click here for Anomali recommendation
Sofacy Attacks Multiple Government Entities (February 28, 2018)
The Advanced Persistent Threat (APT) group “Sofacy” (APT28, Fancy Bear, Pawn Storm, Strontium, Sednit, Tsar Team) has been conducting a new cyber espionage campaign since at least the beginning of February, according to Palo Alto Unit 42 researchers. Sofacy is targeting Ministries of Foreign Affairs located all around the globe with spear phishing emails with Microsoft Excel file attachments that contain malicious macros. If the macro is enabled, it will begin the infection process of a new variant of the group’s custom backdoor “Carberp” (SofacyCarberp).
Click here for Anomali recommendation
CannibalRAT Targets Brazil (February 28, 2018)
Two versions of a new Remote Access Trojan (RAT), dubbed “CannibalRAT,” have been discovered in the wild, with the newest version (4.0) specifically targeting Brazil, according to Cisco Talos researchers. Version 4.0 of the Python-written RAT is targeting users of the “Instituto Nacional Escola Superior da Administração Pública” (INESAP). The INESAP is a Brazilian public sector management school that also engages in consulting work. The threat actors behind this campaign are distributing CannibalRAT in a Python executable format (py2exe) that is packed with a standard version of UPX, which is an open source executable packer. As of this writing, Talos researchers have not yet identified the initial distribution method. However, they have discovered that upon execution of the Python executable, a user will be presented with a PDF file that attempts to impersonate an authentic INESAP document which opens in the Chrome browser.
Click here for Anomali recommendation
RedDrop: the blackmailing mobile malware family lurking in app stores (February 27, 2018)
A new mobile malware family, dubbed “RedDrop,” has been identified in approximately 53 applications, according to Wandera’s mobile threat team. If downloaded and installed, the malicious applications will ask the user to be granted permissions that allow it to steal information from the affected device. Once a RedDrop infected application is opened on a device, at least seven Android Application Packages (APK) are download to augment additional malicious activity such as stealing audio, contact, files, and other forms of sensitive information. The stolen data is then sent to actor controlled Dropbox accounts. Once the data has been stolen, the actor behind this campaign use it to access other accounts or to extort victims for money to prevent leaking of said data. The RedDrop infected applications are distributed via a large Content Delivery Network (CDN) of domains, malvertisements, and third-party application stores.
Click here for Anomali recommendation
Unsecured AWS led to cryptojacking attack on the LA Times (February 27, 2018)
Bad Packets Report researchers discovered that an AWS bucket used by the L.A. Times had a “Coinhive” Monero cryptocurrency miner served on it. The Amazon bucket was hosting the media outlets “The Homicide Report,” which is an interactive map of city murders. Researchers found that the Coinhive miner was present on the AWS bucket, which was misconfigured to allow public write permission, since February 9. The mining process was restricted to run at a CPU level of 30% in an attempt to conceal the mining activity. Interestingly, researchers found that someone had left a message warning the L.A. Times that the “your AWS S3 bucket settings are wrong.”
Click here for Anomali recommendation
Thanatos Ransomware Is First to Use Bitcoin Cash. Messes Up Encryption (February 26, 2018)
The security researcher known as “MalwareHunterTeam” has discovered a new ransomware family, dubbed “Thanatos,” that is the first ransomware to accept “Bitcoin Cash” as payment. After additional analysis, researcher Francesco Muroni found that Thanatos was created in a way in which it does not appear to be possible to decrypt files even after a ransom payment has been paid. As of this writing, the actors behind this malware are demanding $200 USD in the form of Bitcoin, Bitcoin Cash, and Etherum for the decryption key. However, Muroni also found that it may be feasible to brute force the encryption key for each file that has been encrypted.
Click here for Anomali recommendation
New UpdateChecker Coinminer Package Also Displays Ads to Further Piss You Off (February 26, 2018)
Bleeping Computer researchers have published information regarding a new cryptocurrency miner and adware package called “UpdateChecker.” UpdateChecker is being distributed by threat actors by masquerading as a fake update for Adobe Flash Player. If the “update” is downloaded and installed, it will reach out to a location and download a ZIP file that contains the adware and miner package. The miner was found to mine the “Monero” cryptocurrency. The advertisements were observed to be for adult sites, Chrome extensions, and online stores with a provided link, among others.
Click here for Anomali recommendation
Russian computer hackers in Colorado sold stolen credit card numbers for $3.6 million (February 26, 2018)
Agents from the U.S. Department of Homeland Security in the state of Colorado have uncovered a credit card selling operation. Federal prosecutors in Denver U.S. District Court filed documents in which it was discussed how Russian threat actors instructed clandestine organizations to pay for batches of stolen credit card numbers using Western Union and MoneyGram International. The Russian threat actors operated in Colorado and 15 other states and stole thousands of credit card numbers using data-mining viruses. The stolen data was advertised and sold to Ukrainian actors via the “Rescator” network of underground websites for more than $3.6 million USD.
Click here for Anomali recommendation
FEATURED RESOURCES

Iranian Cyber Operations Enter Most Dangerous Phase: Physical Destruction Without Malware Under Ceasefire Cover



