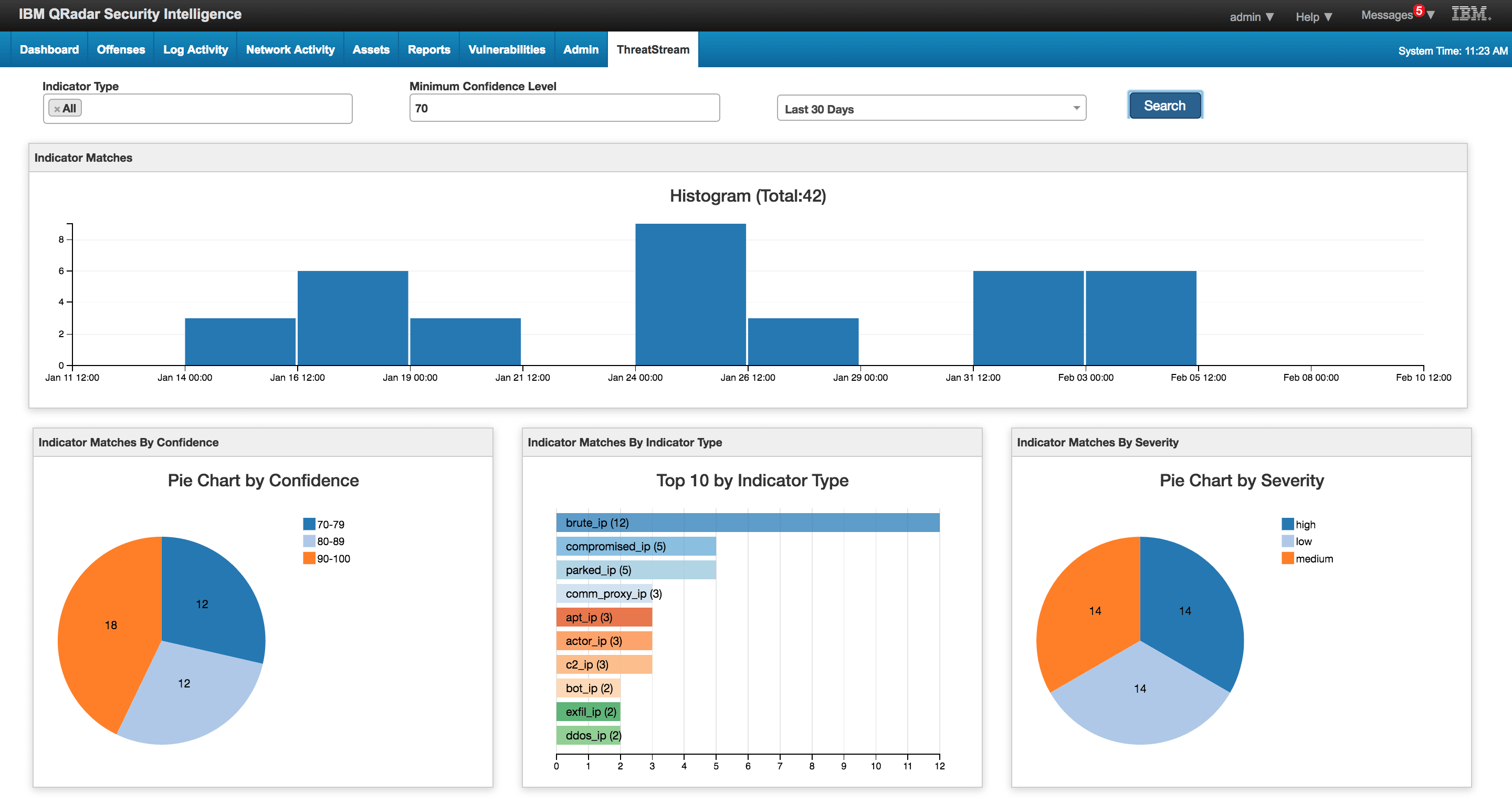

<p>Here at Anomali we have over 30 out-of-the box integrations, from SIEMs to endpoints and everything in between. Our QRadar integration is one of our most popular.</p><p>The QRadar app and Content Pack available to ThreatStream customers provide security analysts visibility into threats within their network by matching and enriching log data to known indicators of compromise through interactive dashboards.</p><p>We recently shared the latest version of the app (v1.0.4) with the IBM QRadar team who have blessed it with their certification (given to only a handful of apps in the XForce exchange).</p><p>In the latest release, we've added some new features that improve the workflow for threat hunting and SOC teams. Here's a brief introduction to some of them...</p><h2>Submit observables from QRadar</h2><h2><img alt="" src="https://cdn.filestackcontent.com/YZpiK9MVTJynyurEuse7" style="width: 600px; height: 393px;"/></h2><p>As you work through offenses in QRadar, it is very likely you'll identify new threats not already reported to ThreatStream during an investigation. With this in mind, we decided to make it easier to submit new observables to ThreatStream from QRadar in a matter of clicks.</p><p><img alt="" src="https://cdn.filestackcontent.com/Sun9JqeCT0ytwS6YGkM9" style="width: 600px; height: 287px;"/></p><p>Once submitted, you can then explore and edit the indicator in the ThreatStream interface. The new indicator of compromise will also be available for matching to new logs in QRadar using the ThreatStream rules included in the Content Pack.</p><h2>Submit false positives</h2><h2><img alt="" src="https://cdn.filestackcontent.com/N8PvdWd5RRCuqBJgJkIL" style="width: 600px; height: 173px;"/></h2><p>Depending on the feeds you're subscribed to, it is likely you might discover events deemed to be malicious that are in fact benign. In such cases, users can mark the indicator as a false positive in ThreatStream so that it does not subsequently flag up as a match in QRadar.</p><h2>Where can I download the latest release?</h2><p>ThreatStream customers can get a copy of the app and Content Pack on the IBM XForce Exchange:</p><ul><li><a href="https://exchange.xforce.ibmcloud.com/hub/extension/70ab618ddc1859b71ff95abe5e0a1eec">App download</a>.</li><li><a href="https://exchange.xforce.ibmcloud.com/hub/extension/67f7718840621bd79739e1beae33482b">Content Pack download</a>.</li></ul><p>If you're not already a ThreatStream customer, <a href="https://ui.threatstream.com/registration">sign up for a free trial today</a>.</p><p><em>Finally a big thank you to Declan Wilson, Ryan Gribben, Gavin McDaid, Sean Creen, and Jagdeep Chabra who worked on this release here at Anomali.</em></p>
FEATURED RESOURCES

Anomali Cyber Watch
Iran Declares Ceasefire Over: Cyber Retaliation Window Opens for Critical Infrastructure

Anomali Cyber Watch
Public Sector


