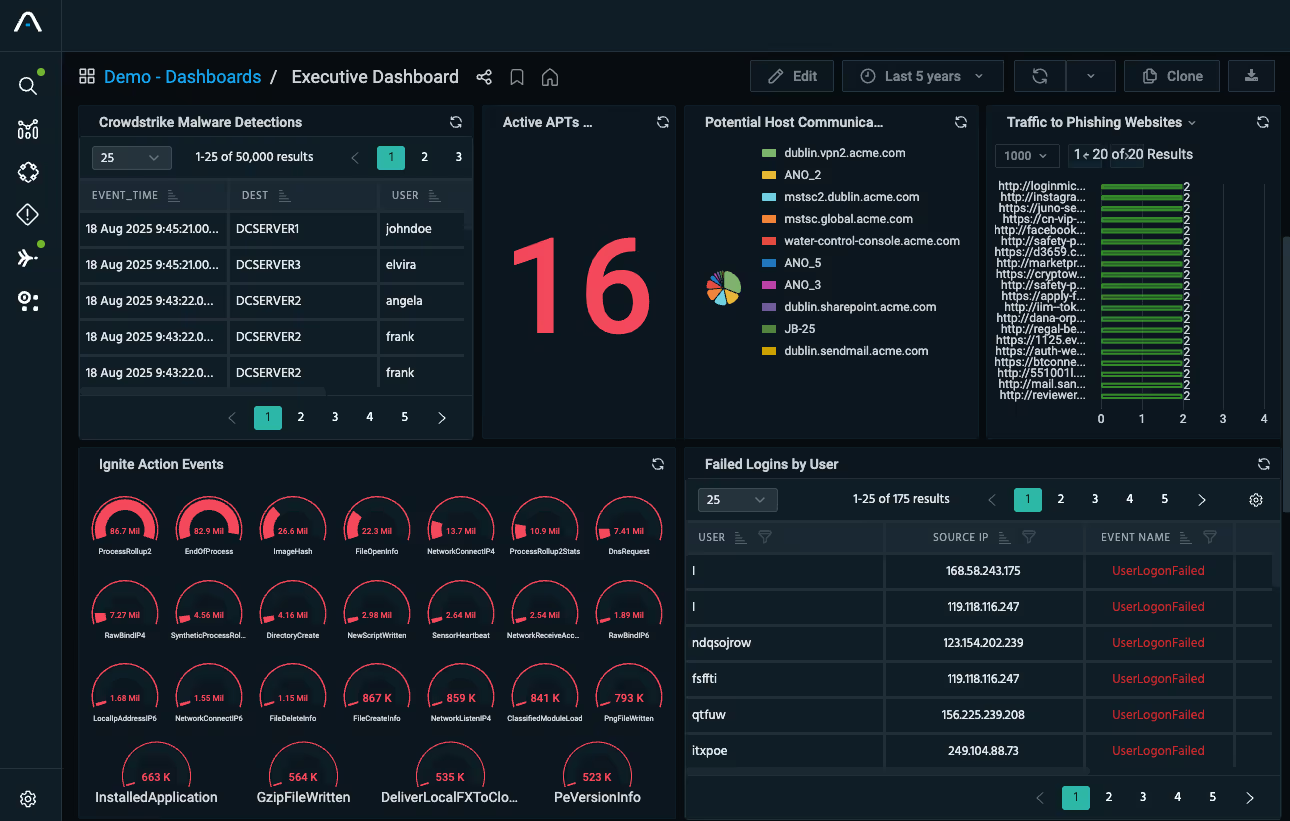
Automate and Orchestrate Your Security
Share integrated data, intelligence, and insights across your security ecosystem. Elevate the efficacy of your security controls and orchestrate the distribution of relevant intelligence across your network.
Maximize Your Security Investments with Integrated Intelligence
Operationalized Threat Intelligence
Empower security teams with actionable intelligence on IoCs, IoAs, and TTPs to identify and address points of vulnerability while there’s still time to prevent a breach.
Multi-Destination Distribution
Anomali Integrator enriches and automatically distributes threat intelligence across your entire security ecosystem. It includes out-of-the-box integrations with common endpoints, SIEMs, firewalls, proxies, DNS, ISACs, and more.
Executive-Ready Intelligence
Auto-generate clear, contextual reports that translate technical findings into business language for leadership and decision-makers.
KEY CAPABILITIES
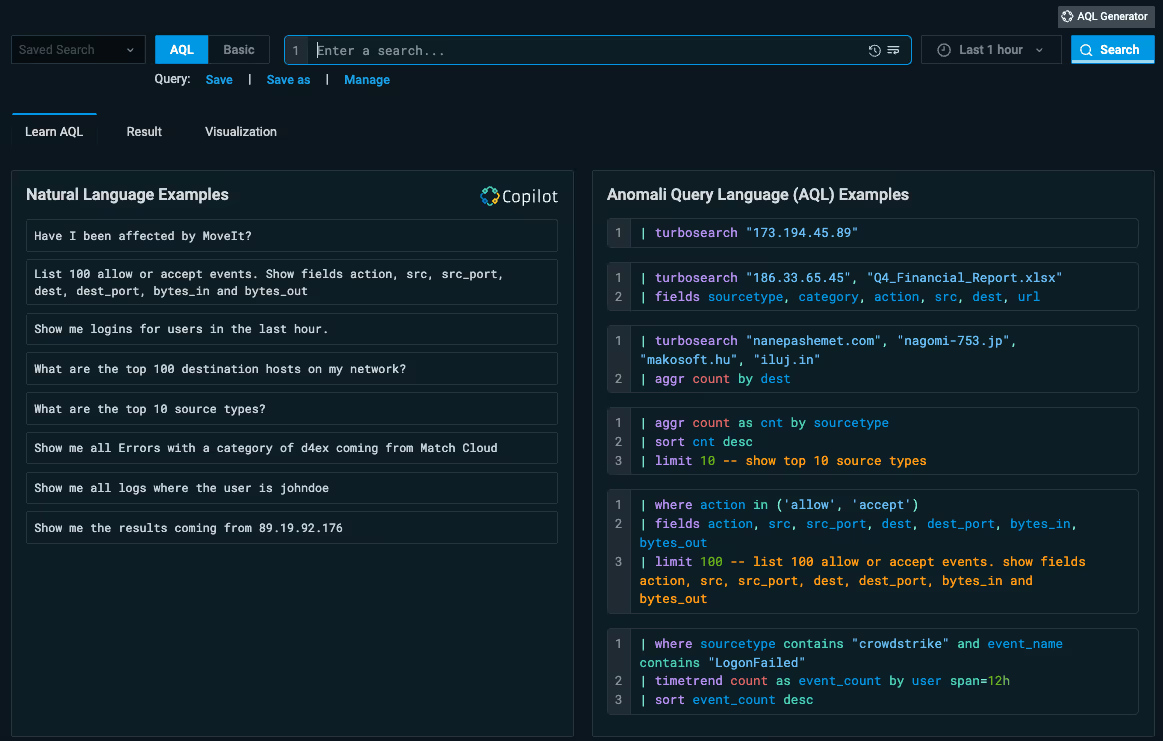

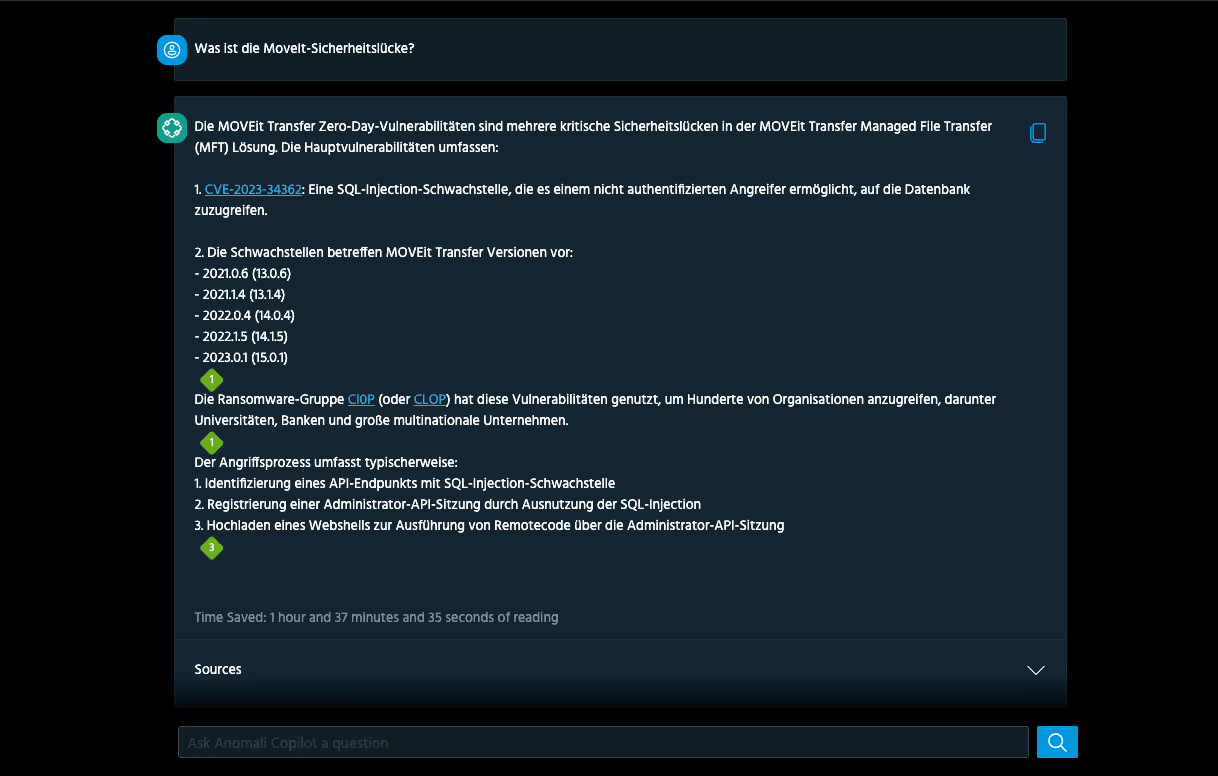
How Anomali COPILOT FITS INTO THE PLATFORM
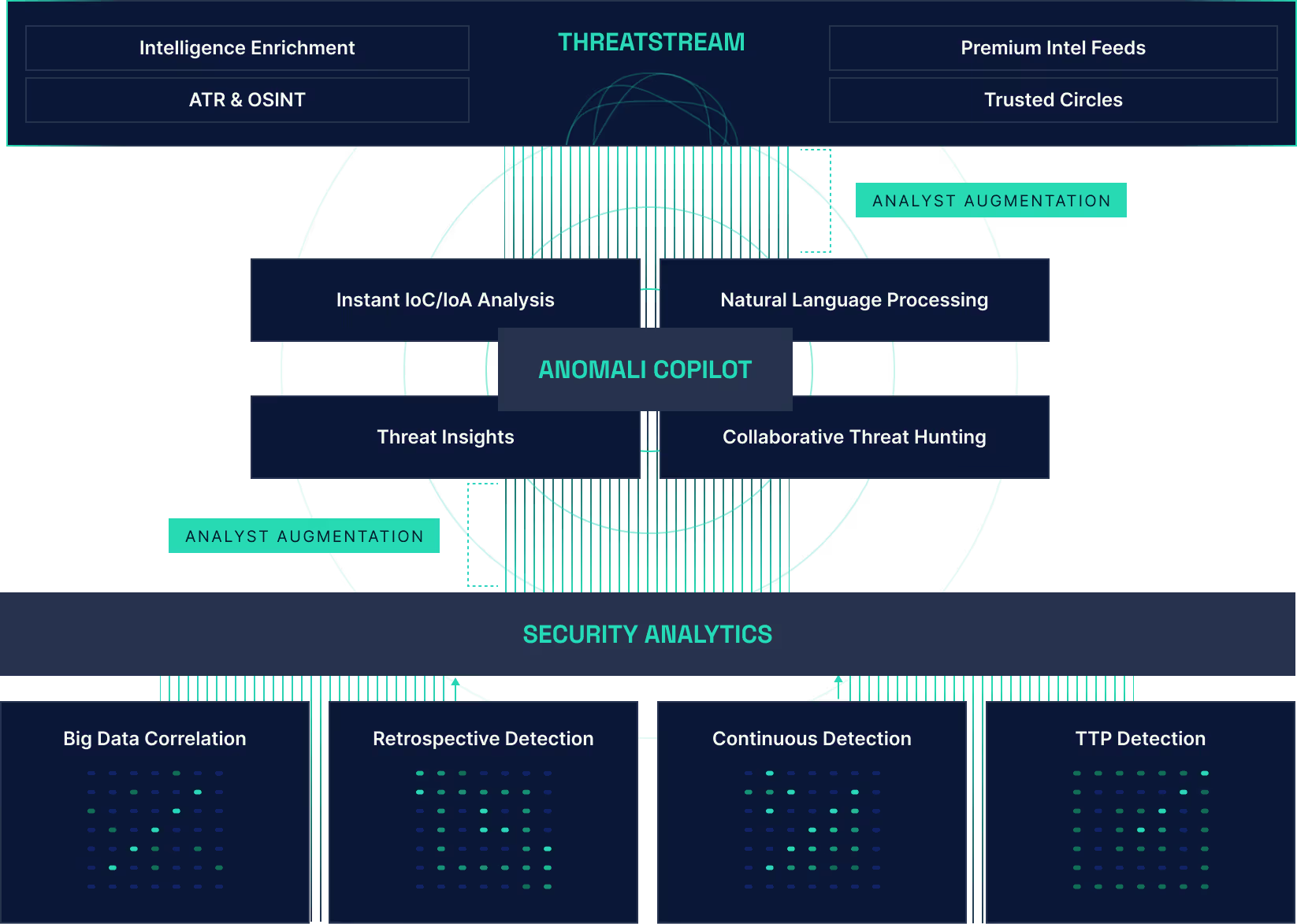
TURBOCHARGE YOUR THREAT INTEL PROGRAM
Find threat intelligence relevant to your organization in the Anomali Marketplace. Feeds from OSINT sources and leading vendors are included in every ThreatStream subscription.

The Real Threat Intelligence Gap Is Execution

Introducing ThreatStream Next-Gen: New AI-Powered Capabilities to Sharpen Your Intelligence Operations
Anomali Named SC Awards Finalist x2: What the Recognition Reflects About Where Security Operations Is Headed

SEE THE PLATFORM IN ACTION

.png)






















.png)