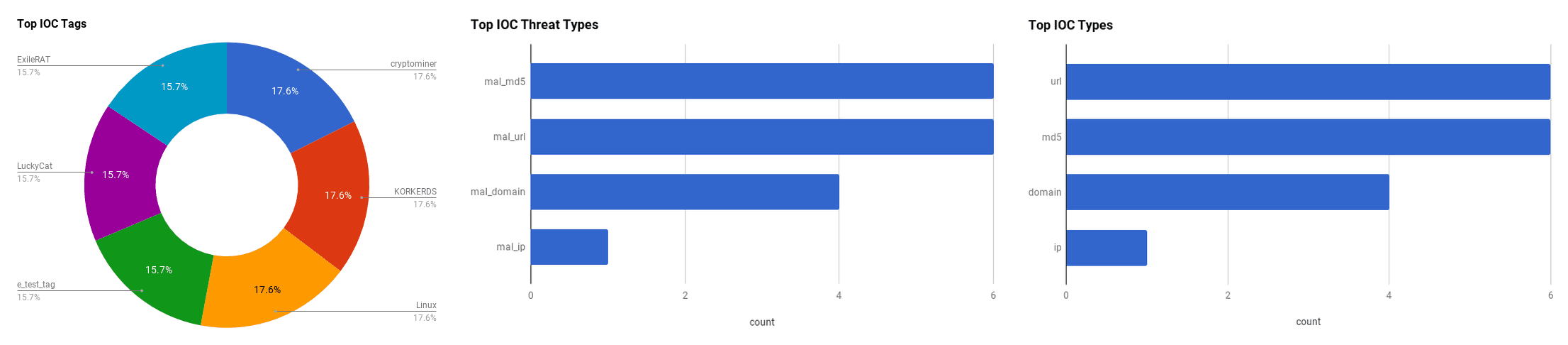

The intelligence in this weekís iteration discuss the following threats: Cryptominers, Data breach, ExileRAT, Malware, NanoCore, RATs, Remote code execution, Spear phishing, and Vulnerabilities. The IOCs related to these stories are attached to the Community Threat Briefing and can be used to check your logs for potential malicious activity.
Trending Threats
Mumsnet Data Leak Baffled Parents As Cloud Migration Exposed Users' Personal Data (February 10, 2019)
The parenting forum website, "Mumsnet," suffered a data breach following migrating their services to the cloud. Between 2 pm on February 5 and 9 am on February 7, 2019, users that attempted to log into the website could have accessed another user's account information if two users were logging into the site simultaneously. Because of the software change that was occurring at that time, users could view the details of other users including account details, email addresses, personal messages, and posting history. Mumsnet was notified by a user to the issue, and they promptly fixed the issue.
Click here for Anomali recommendation
Linux Coin Miner Copied Scripts From KORKERDS, Removes All Other Malware and Miners (February 8, 2019)
Researchers from Trend Micro found a script on one of their honeypots that was downloading and installing a cryptocurrency mining malware onto a Linux system. The script is capable of killing and/or deleting a number of known Linux malware, cryptominers, and connections to other miner services and ports, and after installing its own malware, it implants itself into the machine's system to survive rebooting and deletion. The script appears to be similar to the "KORKERDS" malware, but is notably different in that this malware does not install a rootkit or uninstall antivirus software, as well as this new malware has KORKERDS in its kill list. The observed script downloads a modified version of the "XMR-Stak" cryptominer that mines for Cryptonight cryptocurrency. The infection source appears to have started from some IP cameras and web services via TCP port 8161.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Uncommonly Used Port (T1065)
Google Spots Attacks Exploiting iOS Zero-Day Flaws (February 8, 2019)
Apple released a new software update to their iOS that addressed four vulnerabilities, including two privilege escalation vulnerabilities observed to be exploited in the wild. The first vulnerability patched in this update, registered as "CVE-2019-7286," affects the Foundation component in iOS and could potentially allow a malicious application elevated privileges. The other vulnerability observed in the wild that has been patched, "CVE-2019-7287," impacts the IOKit and could potentially allow a malicious application to execute arbitrary code with kernel-level privileges. The other two vulnerabilities addressed in the new software update, fix the flaws that are related to the FaceTime bug that allowed the caller to see the recipient before they accepted the phone call.
Click here for Anomali recommendation
Opening This Image File Grants Hackers Access to your Android Phone (February 7, 2019)
Google noted a critical vulnerability in the Android operating system framework that could allow a threat actor to execute arbitrary code and obtain privileged access. To exploit this vulnerability, a threat actor would need to send a malicious Portable Network Graphic (.PNG) file to a user's Android device, and would be triggered upon opening the file. This vulnerability has not been observed in the wild yet. Android versions 7.0 to 9.0 are affected.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Attachment (T1193)
Phishers Leveraging Google Translate to Target Google and Facebook Users (February 7, 2019)
Larry Cashdollar, a member of Akamai's Security Intelligence Response Team (SIRT), received a phishing email that said his Google account had been accessed on an unknown Windows device. The email's content appeared very similar to a legitimate Google notification, however, the email purported to be from "facebook_secur@hotmail[dot]com." If the target clicked the "view activity" button, they were redirected to a fake Google login that used Google Translate to load the malicious domain to trick users into thinking the domain was legitimate, though the domain being translated in the search bar was completely different from a Google page. This phishing attack had two phishing attempts as if a user did enter in their Google account information, they would then be redirected to a Facebook page in an attempt to also steal those credentials.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Link (T1192)
Microsoft Confirms Serious ëPrivExchange' Vulnerability (February 6, 2019)
A high-severity privilege escalation flaw in Microsoft's Exchange Server has been confirmed to exist by the company. Both Microsoft and the US-CERT released official warnings regarding the flaw, called "PrivExchange." The flaw is a result of the default setting in the Microsoft Exchange Server and the mail and calendar server that could allow a threat actor with a basic mailbox account to execute a Man-in-the-Middle (MITM) attack utilising one of two python-based tools: "privexchange.py" and "ntlmrelayx.py." These tools would forward an authentication request to a Microsoft Exchange Server that could allow impersonation of another Exchange user, and allow the threat actor to obtain domain administrator privileges. Domain administrator privileges allow the user access to the full Exchange Server and the ability to perform almost any task on the server. Only users with "OnPrem" deployments are at risk; Exchange Online is not affected. Microsoft is currently developing a patch.
Click here for Anomali recommendation
Researcher Reveals Data Leak at South Africa's Main Electricity Provider (February 6, 2019)
The South African, state-owned electricity company, "Eskom," appears to have suffered a data breach due to their billing software database being left exposed, without having a password to protect the database. Cybersecurity researcher Devin Stokes publicly tweeted screenshots of the customer and service-related information that was accessible on the database including: account IDs, meter information, and start and end service dates. The breach appeared to have escalated when Stokes found that some database entries also contained financial data of customers such as CVV numbers, names, payment card types, and partial payment card numbers. This issue appears to have been further exacerbated by an unnamed employee possibly accidentally installing a trojan onto the corporate machines by downloading a fake "SIMS 4" gaming installer. Despite Eskom remaining fairly quiet on the matter, they did state that they "investigated the potential trojan infection and have taken necessary actions."
Click here for Anomali recommendation
Severe RCE Flaw Disclosed in Popular LibreOffice and OpenOffice Software (February 5, 2019)
Security researcher, Alex Inf¸hr, discovered a severe Remote Code Execution (RCE) vulnerability in open-source office suites "LibreOffice" and "Apache OpenOffice." This vulnerability could be triggered by opening a malicious OpenDocument Text (ODT) file and exploiting a directory traversal flaw, "CVE-2018-16858," that executes a specific python library in the software. The python file "pydoc.py," that is included in LibreOffice's python interpreter, will accept arbitrary commands that allows a threat actor to trick the interpreter into executing a malicious payload. This vulnerability affects both Windows and Linux operating systems.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Attachment (T1193)
Sophisticated New Phishing Campaign Targets the C-Suite (February 5, 2019)
A new phishing campaign attempting to steal login credentials has been observed to be specifically targeting C-levels and executives in organisations, according to researchers from GreatHorn. The phishing emails appeared as requests to reschedule a meeting and provides a URL link to a page that looks similar to a "Doodle" poll site to then rearrange for a suitable time. The webpage is a phishing site designed to steal Office 365 credentials. Interestingly, if the phishing email is viewed on a mobile device, the sender of the email is changed to "Note to Self" which is a new feature in Microsoft Outlook that activates when a person emails their self something. Because of this, the likelihood of the user falling victim to the attempt increases. Depending on the email client used, the phishing email could be filtered and put into the "Spam" folder, though this does not inhibit users from continuing to interact with the email.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Link (T1192) | [MITRE ATT&CK] Trusted Relationship (T1199)
Hackers Now Exploit Google Sheets To Spread CSV Malware (February 5, 2019)
Threat actors have been observed utilising Google Sheets to distribute malware. Researcher Marco Ramilli received a phishing email that bypassed Google's spam filters by using a Google Sheets document, and found "a series of empty fields preceding a final and fake formula piping a CMD.exe command. By using the bitsadmin technique the attacker downloads a file called now.exe and stores it into a temporary system folder for later execution." This then installs a variant of the "NanoCore" Remote Access Trojan (RAT). The malware is able to install itself onto the device whether it is opened in Google Sheets or downloaded and opened locally in Microsoft Excel.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Attachment (T1193) | [MITRE ATT&CK] Remote Access Tools (T1219)
ExileRAT Shares C2 with LuckyCat, Targets Tibet (February 4, 2019)
Researchers from Cisco Talos discovered a spear phishing campaign targeting individuals in Tibet that installs the "ExileRAT" Android Remote Access Trojan. The phishing email targets subscribers to the organisation, "Central Tibetan Administration," which represents the Tibetan government-in-exile, and uses a malicious attachment pretending to be the document "Tibet-was-never-a-part-of-China" to trick users into opening it. The installation process begins by first by exploiting a registered Microsoft Office code execution vulnerability, "CVE-2017-0199," and then establishing a connection to the Command and Control (C2) server. The C2 then delivers a script that downloads the payload that install the RAT. The RAT is capable of obtaining system information including computer name, listing drives, network adapter, process name, and username, as well as using get/push files and execute/terminate processes. The C2 infrastructure is similar to that of the malware, "LuckyCat," that has been observed to target Tibetan activists in the past and is attributed to Chinese threat groups.
Click here for Anomali recommendation
MITRE ATT&CK: [MITRE ATT&CK] Spearphishing Attachment (T1193) | [MITRE ATT&CK] Remote Access Tools (T1219)
FEATURED RESOURCES

Iran's Cyber Arsenal Is Reloading: What CISOs Must Know About the Post-Decapitation Threat Window



