Resources
Resource Center
Browse our library of upcoming and on-demand webinars, brochures and datasheets, industry reports and white papers, case studies, and more.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.



.png)

.png)






















































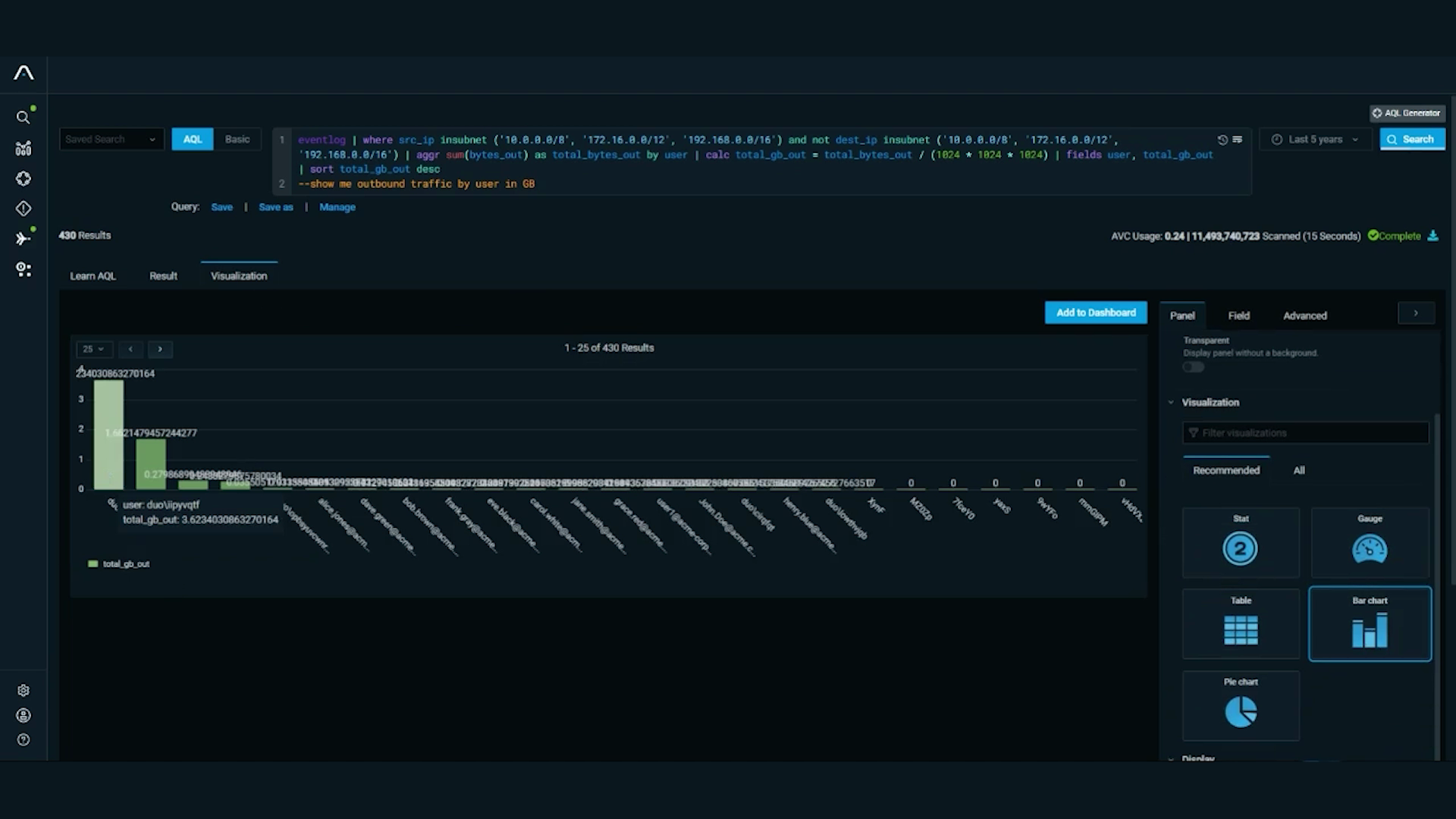
.jpeg)















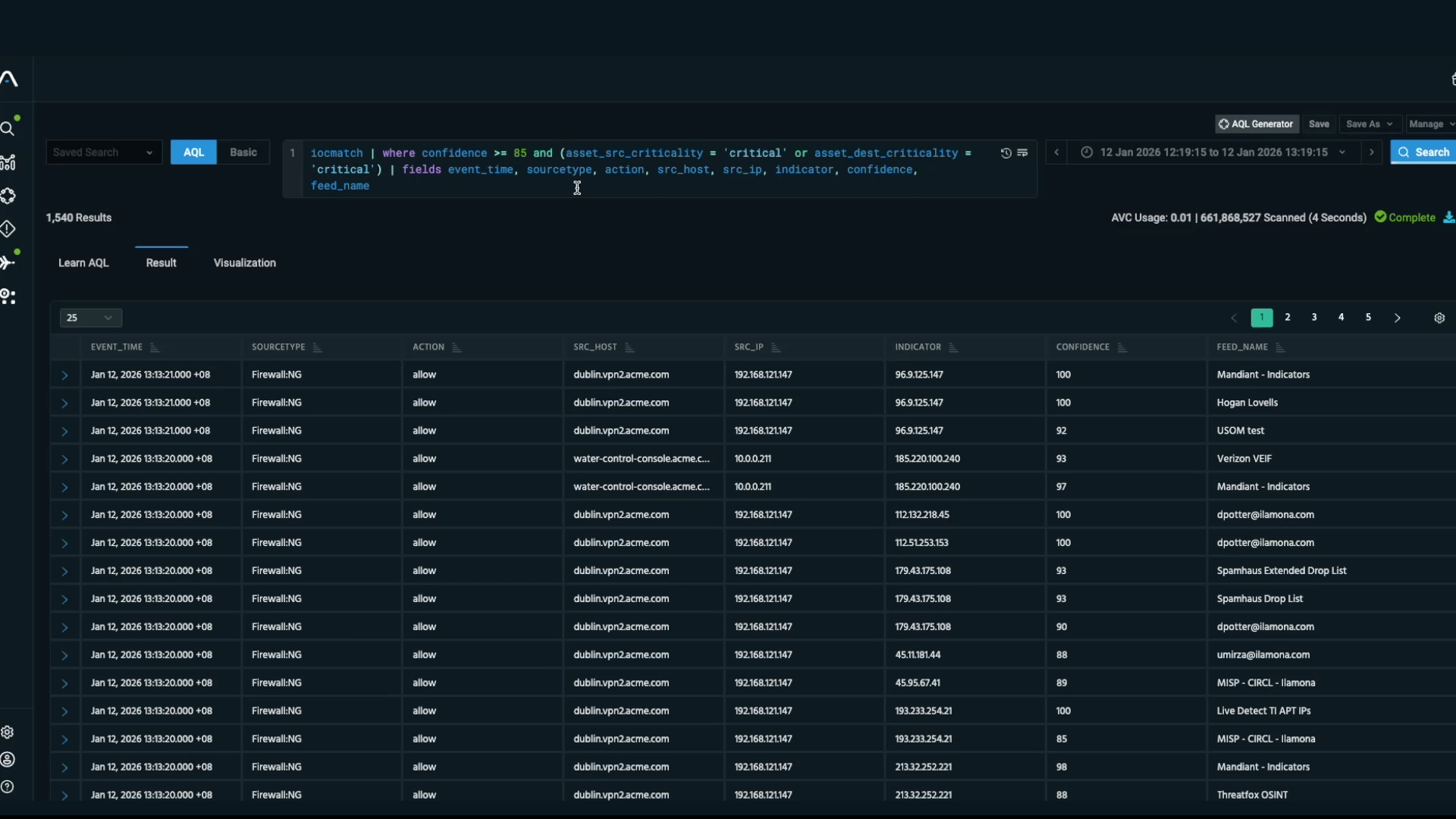
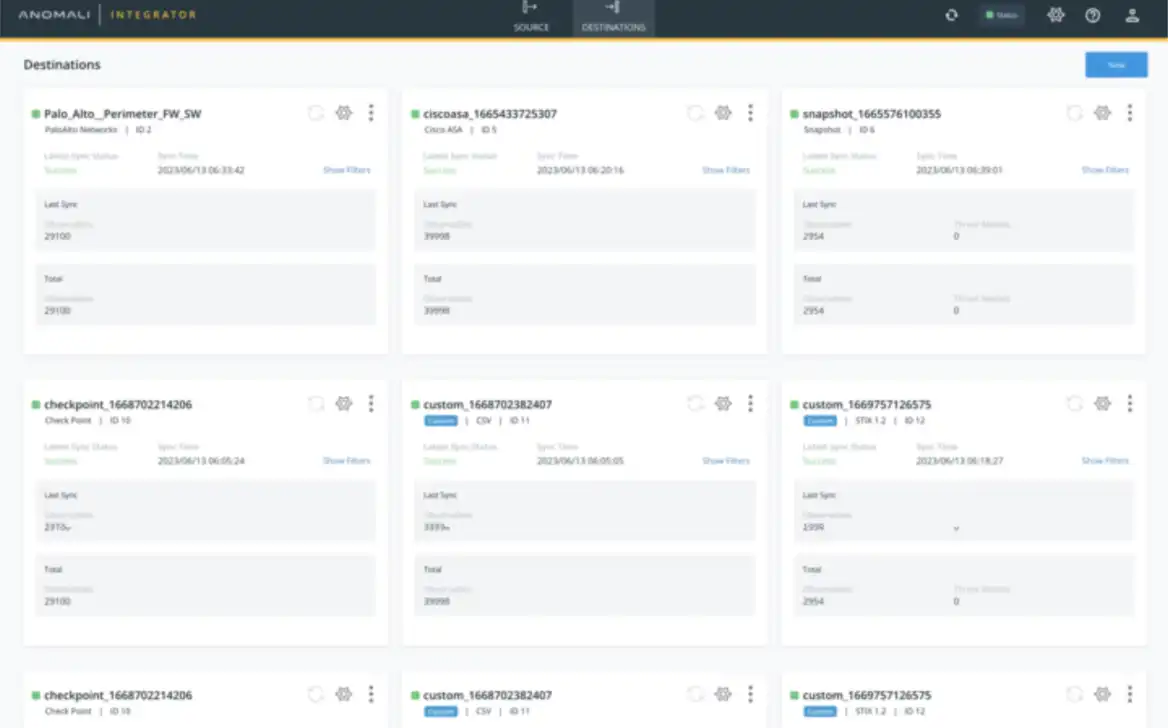
.jpeg)